VLANs blocked by Firewall
-
Hello Gents, and Ladies
First post here, need a little help figuring out why are the VLANs being blocked by the firewall.
I'm not new to FreebSD and Networking in general, but my knowledge is at a "layman" level if you will.My box is a Supermicro E200-9B with 4 NIC cards set up as follows,
WAN - igb1
LAN - igb2 - 192.168.3.0/24
OPT1 - igb0 - 172.24.0.0/24
OPT2 - igb3 - 10.70.0.0/24LAN connects to a dummy switch --> Negear Router in AP mode and that's what providing
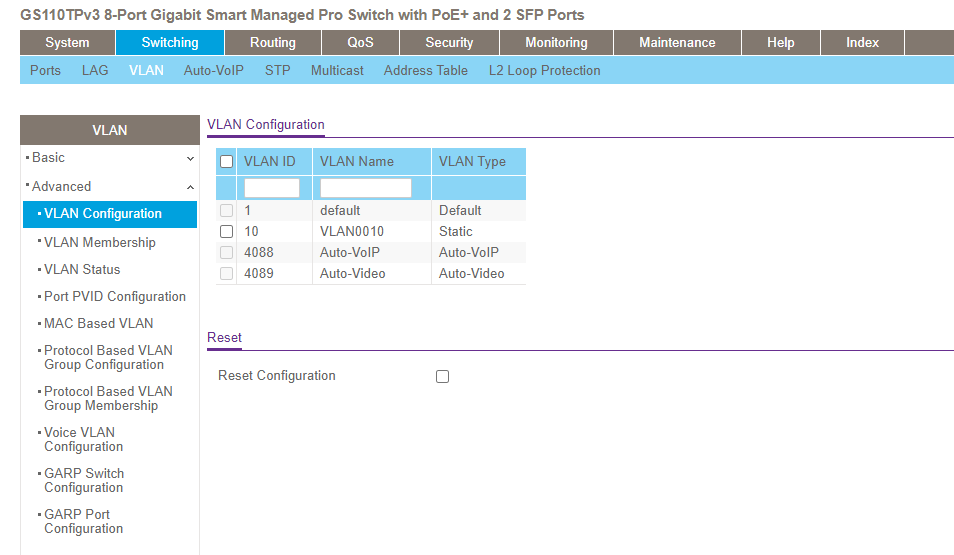
connection to the rest of the house at the moment. Running pfBlockerNG and Snort INLINE without issues.Recently bought a Netgear GS110TPv3 with the intention of subnetting - Kids WIFI, IoT, NAS, etc.- and connected it to OPT2 using a static address. This is an 8 ports swith, I'm using g8 as the trunk and the rest to play with VLANs. At the moment I have only VLAN10 (10.70.10.0/24) for ports g1 and g2, these two Untagged and g8 Tagged as the manual suggests. Also confirmed the correct setup with Netgear's Customer Service.
Did the same in my pfSense box and created the VLAN, Firewall Rules, DCHP Server settings following the manual and this write-up here (https://netosec.com/protect-home-network/). Now, if I connect my laptop to either of those two ports, it cannot pick up the DHCP address from the router. If connected to any of the other ports, g3 -> g7, then it connects to the 10.70.0.0/24 range.
The system log shows APIPA range blocked.
Jan 10 20:43:24 OPT2 Block IPv4 link-local (1000000101) 169.254.199.118:137 169.254.255.255:137 UDPFirewall rules in OPT2 and OPT3 (VLAN10) are simple. One rule to allow access within the subnet, and the second to allow internet access.
I've read a few posts on here and I haven't found the solution yet.
I do appreciate your help in advance.
Thanks, -
@r801248
169.254.x.x it's a link-local address, it's an IP for devices that are unable to obtain a DHCP address from the server
you see the traffic on OPT2 aka igb3 something is wrong on your switch or on your pfSense configuration. we need screenshots of what you have done -
@kiokoman
Thanks for answering. On the switch, IP address is set up as static and the VLAN as follows -
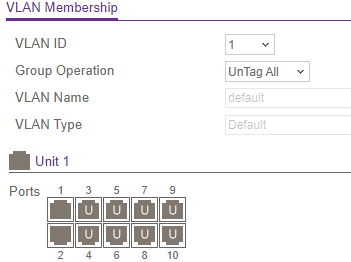
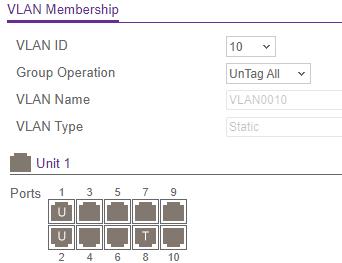
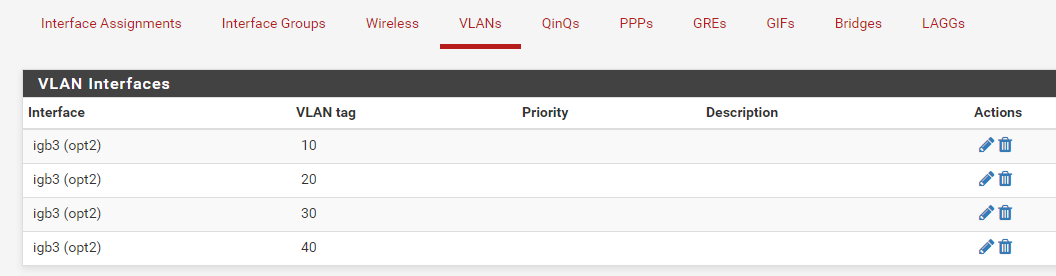
All other settings are set to default values.On the pfSense box -
Interfaces

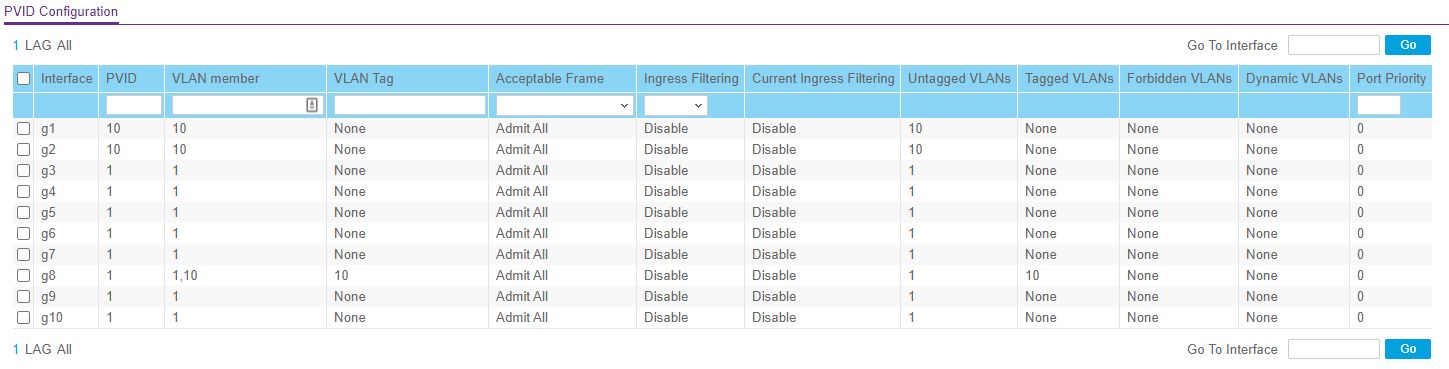
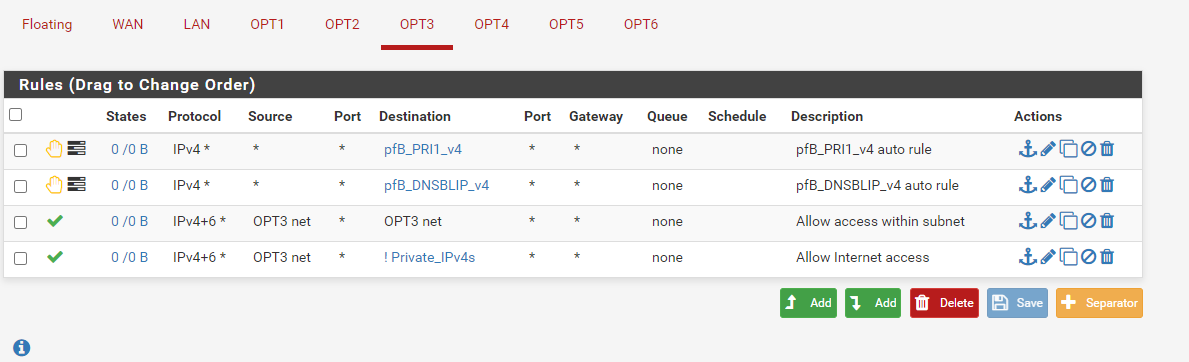
Firewall rules (Similar for OPT3)
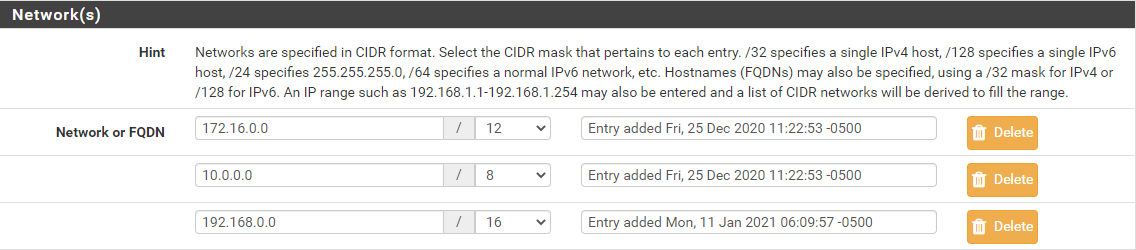
With Private_IPv4 as,
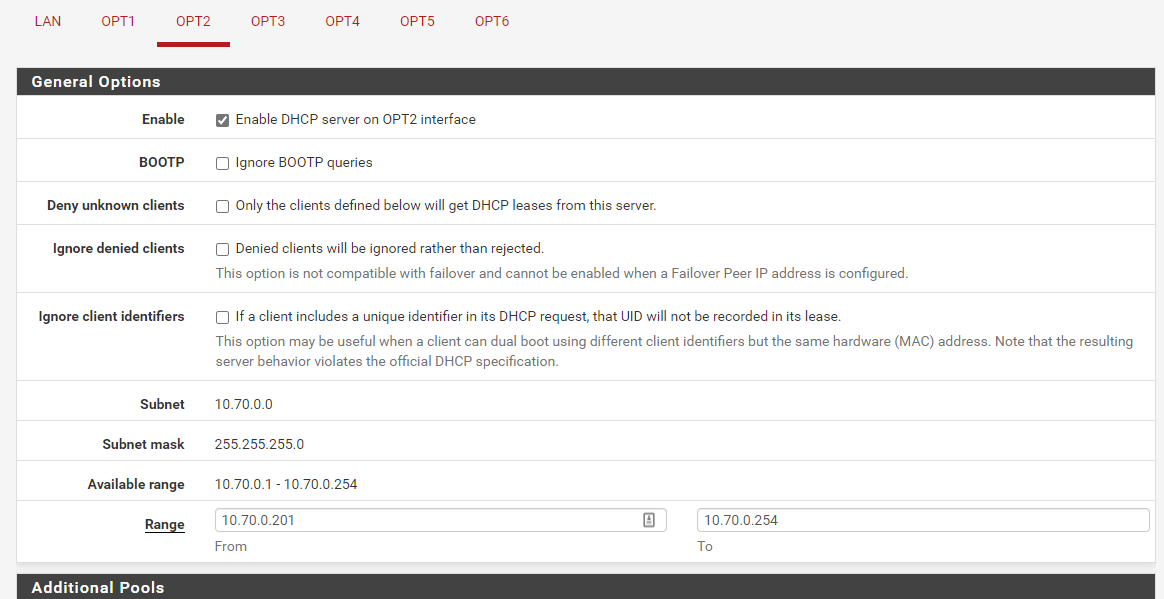
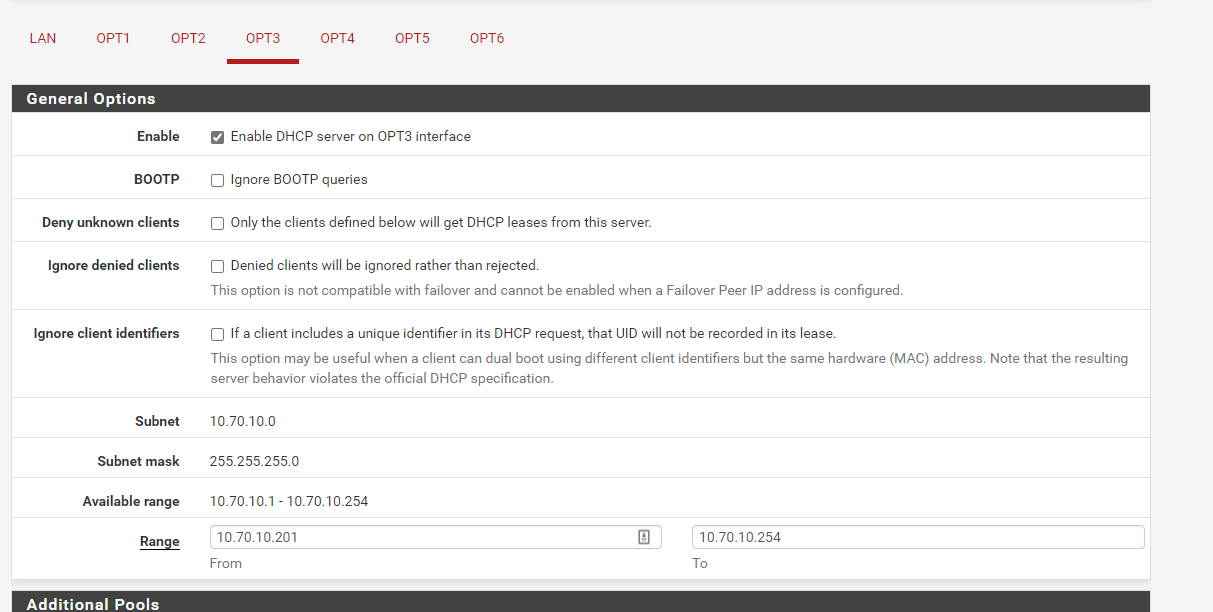
And DHCP (Similar setup for OPT3)
DNS Resolver is used by ALL interfaces, and Outbound NAT as Manual (Tried Hybrid and Auto, same results)
Thanks,
-
@r801248 said in VLANs blocked by Firewall:
it cannot pick up the DHCP address from the router
Did you enable DHCP servers on each VLAN?
-
-
Well, you'll have to do what I often recommend. Start simple and get things working, before you do anything else. Then you can see where the failure occurs. As it is, a firewall will not block a VLAN as VLANs are layer 2 and firewalls work at layer 3. The firewall rules are applied to each LAN or VLAN as required. Just get the basic networks going first and then start adding the rules.
-
@r801248
opt3 is vlan10, i don't see a screenshot for firewall rules and for the dhcp of that interface -
Sorry, here you go. I only set up the switch static address in OPT2, not in the VLAN.
-
@r801248
ok
"opt2 net * opt2 net" and "opt3 net * opt3 net", not a big deal but they are wrong rules, devices on the same subnet talk to each other without the help of pfsense. pfsense does not see traffic when the client talk to each other on the same subneti don't see anything else wrong on pfsense, i don't know how the netgear should be configured.
what i understand is that the vlan tag is not working right on g1/g2/g8
is there an option like vlan port based vs vlan 802.1q or Dot1q on the switch? it should be 802.1q or Dot1q. is the switch configured as layer 2 ? (ip routing should be disabled on the switch)
maybe you can use packet capture on the parent interface to see if traffic is passing with tag and if a dhcp DORA is passing -
@kiokoman IP Routing is disabled on the switch. These are the SWITCHING --> VLAN options available.
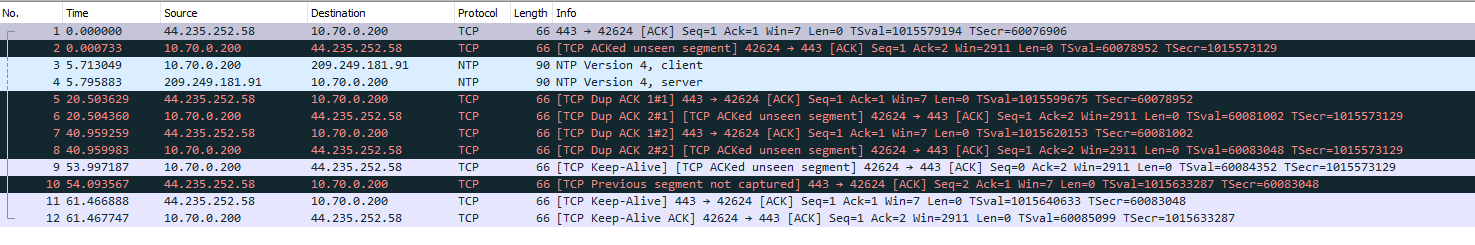
And this is the packet capture on the parent interface (OPT2), where 10.70.0.200 is the static IP of the switch.
-
@r801248
filter for port 67 / 68 and do a release/renew ( or remove and replug the cable) on whatever you have on g1/g2 , i don't see dhcp stuff on that packet capture
there should be something like this
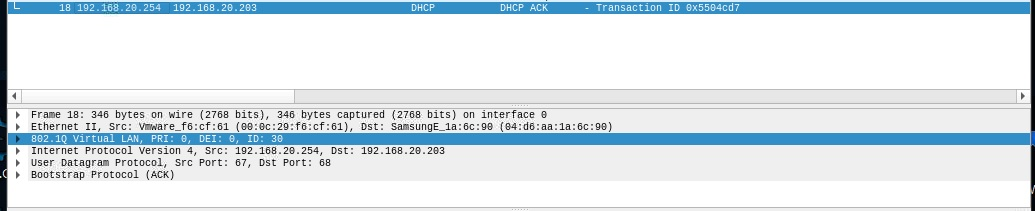
where ID 30 is my vlan 30 -
So, in the Packet Capture screen, you want me to select OPT2 as the interface? I'm assuming Host Address is the Switch's ...
-
@r801248
use opt3, i don't know if youcan do that with packet capture from pfsense, i use wireshark
did you try to reboot pfsense and the switch? -
Both rebooted.
-
@r801248 What is your Port PVID Config look like? ooops that was posted earlier.
What does this look like?

That config looks correct even looking at this ...
https://kb.netgear.com/11673/How-do-I-setup-a-VLAN-trunk-link-between-two-NETGEAR-switches
Also on the switch Select Switching > VLAN > Advanced > VLAN Status. what does that look like?
-
@cburbs Hello,
This is what they look like...

-
And if you plug your laptop into ports 3-7 you mentioned you do get a dhcp from VLAN10 (10.70.10.0/24) ? Can you also get out to the internet on those ports?
Have you tried to add say Port 5 to vlan10 untagged and plug into that to see what happens?
Maybe delete that Vlan 10 from the switch and start over with it?
-
@cburbs
When I plug the laptop into g3-g7 I get a DHCP from the parent interface (10.70.0.0/24) - Yes, I get out to the internet.
Adding any other port (untagged) makes it behave like g1-g2. -
@r801248
did you check if there is a firmware update for that netgear? -
@kiokoman
There is an upgrade. I guess I'll go that route.
Thanks,