Using PfSense as a GeoIP filtering appliance ONLY
-
Hello, can someone point me in the right direction of how to use pfsense to only utilize the GeoIP filtering portion in PFBlockerng. I do not want anything else from the product, only this feature. Trying to build an appliance for this sole purpose to put in front of firewalls. Thank you in advance.
-
-
Using PfSense as a GeoIP filtering
and
an appliance for this sole purpose to put in front of firewalls.
where pfSense is a firewall.
With another firewall in front of it ?A Pi-Hole based appliance ?
Remember : IPv4 Geoip based filtering somewhat works - with many IPv4 networks not defined / assigned to the correct country. You'll be having loads of exceptions. As IPv4 (a are resource) is sold, and sold again. Because of the $$$$ factor.
The upcoming IPv6 : worse.
Thinking that you can 'exclude' IP's based on Geoip info is mostly an urban legend.@azon2111 said in Using PfSense as a GeoIP filtering appliance ONLY:
I do not want anything else from the product, only this feature.
Throw a dozen of full time programmers against a fork of an exiting project (pfSense ?), work on it for a couple of years and - if you still exist - introduce it ?!
-
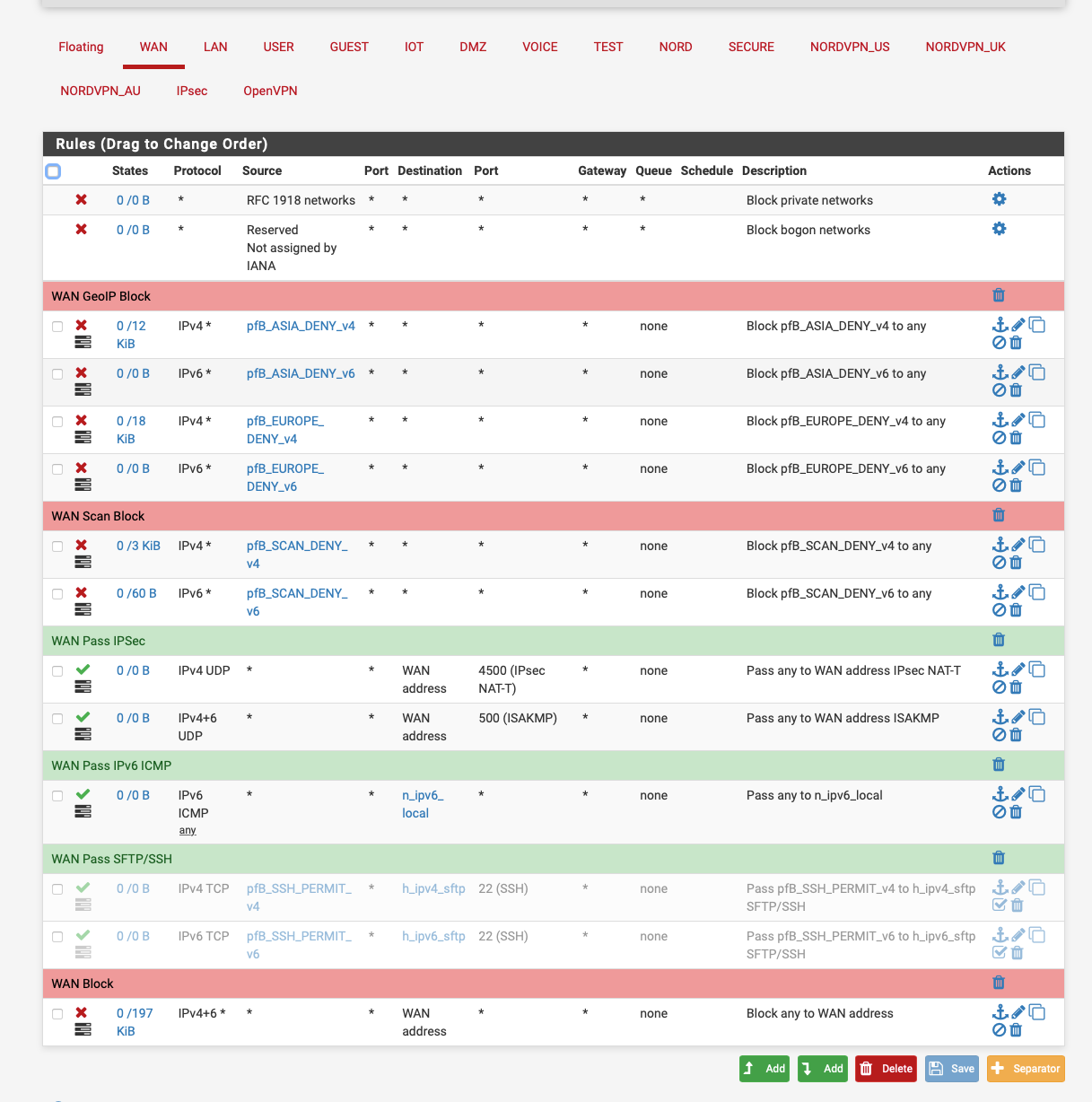
@nogbadthebad by default pfsense blocks everything, this would sit in front of say a ubiquiti or sonic firewall and all traffic would be passed by default except for those rules above for IPv4, IPv6 is not enabled at all at this time.
Would I need to change the default behavior for pfsense somehow to allow for all traffic to flow through except for these rules? Thank you for such a quick reply.
-
What exactly are you trying to filter? You want to stop from going to X, or you want to only allow going to Y and Z?
As mentioned - geoip lists, are far from perfect.. While they might be helpful in saying hey I want to only allow US IPs to talk to something inbound to your IP
For example.. I only allow US IPv4 to talk to my plex server port. But its quite possible that some IP that is NOT in the US is in that list. And it is also quite possible that there are some US IPv4 address that are not in that list.. All of my users are currently in the US, so blocking stuff that is not US, limits the amount of stuff that can talk to my plex server. Now 1 of my users could maybe come from an IP that is not included - but prob unlikely, and they would let me know - hey can not get to plex, and could look up where that IP is listed as being in.
While geoip lists do have some value, and can be used to reduce exposure.. As Gertjan mentions it is not by any means 100% accurate..
So depending on how exactly you plan on using these lists, you may find your self playing wack-a-mole adding and removing IP ranges from the list.. When users complain they can not go here.. They sure are not going to tell you hey, I could get to ABC and I shouldn't be able to ;)
-
@johnpoz Yes sir, just trying to add an extra layer where traffic is dumped thus taking load of IPS/IDS features by dumping that traffic and another reason is self-hosted email where it actually thwarts quite a bit of spam messages by simply dumping smtp traffic where no email from those countries is even needed along with site traffic being dumped too as it would almost all be hacking attempts against hosted sites.
I would prefer to block all traffic except traffic in GeoIP lists like US are allowed. This would result in a smaller footprint for the other firewall to contend with. Hope that makes sense.
-
So you want to use the lists as inbound filtering before traffic even hits your smtp server.
In that context sure that could be useful. But you could find yourself missing emails from company or user xyz.. When the source IP talking to you is mis listed..
Not sure if adding some box, adding a complexity to the setup, most likely another layer of nat. Is worth it. Now if pfsense was just your firewall, leveraging geoip features of pfblocker to your forwarding rules would just be clicky clicky and might be worth it??
Your current firewall does not allow the ability to filter on IP lists? While pfblocker makes it easy for the typical user to work with stuff like.. When it comes down to it, its not really doing anything other than grabbing a list of IP address/ranges and putting them in an alias. Which you use in your rules.
You could grab these list of country based IPs yourself and add them to your existing firewall, if it supports that feature. But simple solution vs adding pfsense, would be to just replace what you have with pfsense.
-
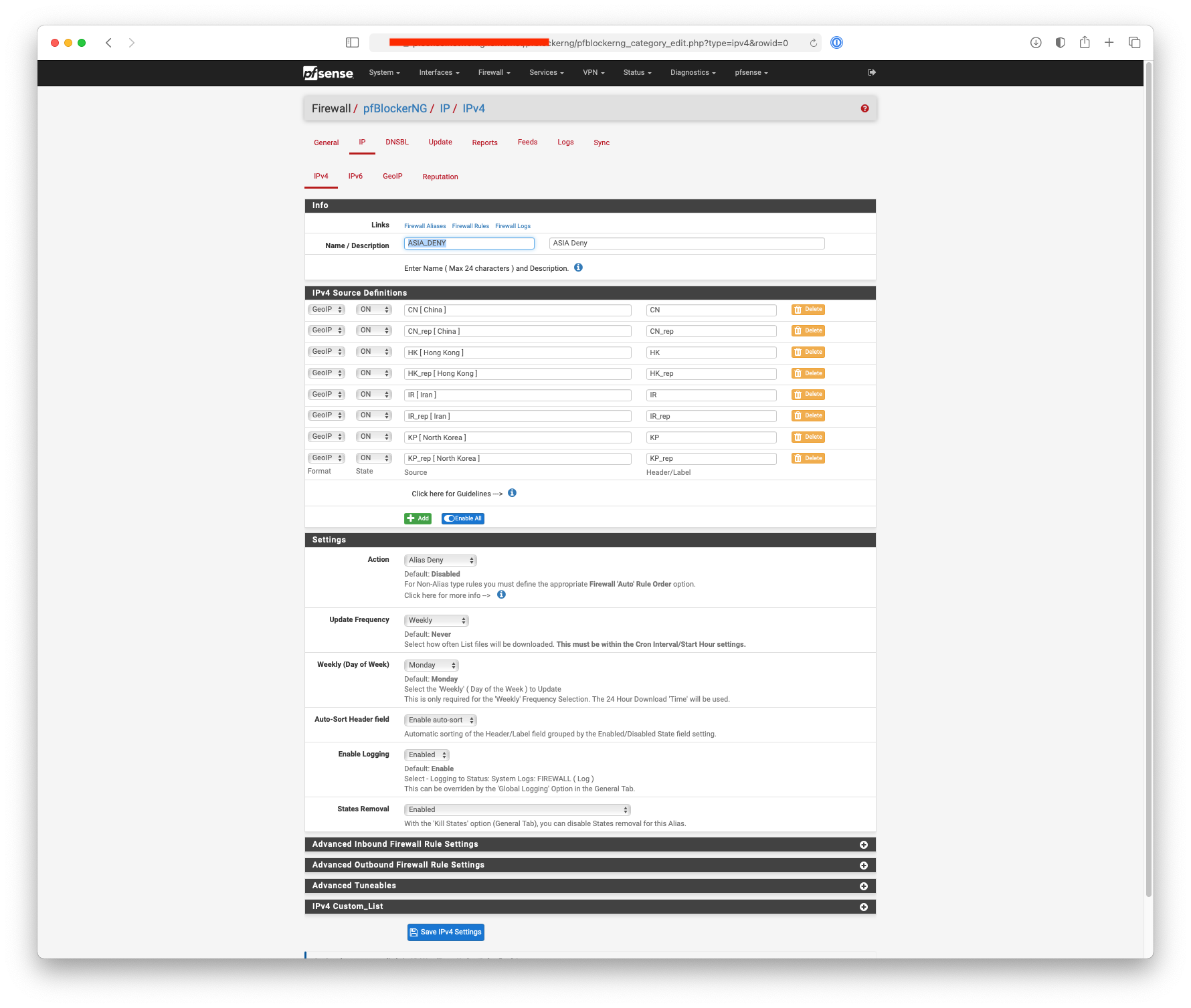
The Deny Alias is used in the reporting in pfBlocker as a label.
I use them block access to my IPsec VPN.
-
Hello!
Maybe...
https://docs.netgate.com/pfsense/en/latest/bridges/index.html#types-of-bridges
https://docs.netgate.com/pfsense/en/latest/bridges/firewall.html
https://duckduckgo.com/?t=ffab&q=pfsense+filter+bridge&ia=webJohn
-
@azon2111 said in Using PfSense as a GeoIP filtering appliance ONLY:
self-hosted email where it actually thwarts quite a bit of spam messages
I know all about that one.
Back, in the 'good old days' I was said ones to myself : want to have my own domain names (private and company (a hotel)) and taking care of my own mails, as using a mail server from some where else binds you to the mail reputation of the host. Shared mails can be great, and the next day you can't mail to gmail, or yahoo, or whatever. Or the other way around : one of the biggest (Belgium) mail suppliers, skynet.be (don't laugh) was often blocked, me not being able to do anything about it.
So I went for the 'do it myself'.What I did : tell postfix to be far more stricter as 'default' : for the incoming mail :
No reverse host name ? => Hang up the phone.
=> You say "Paul' but your reverse lookup says "Jack" >= assign a big penalty to start with (this one has a identity crisis / split personality / other issue )
No SPF ? => assign a big penalty to start with.
No DKIM ? => assign a big penalty to start with.
No DMARC (and IPv6) => assign a big penalty to start with.
Mail with added files that are forbidden, like exe, com, docx, etc etc ? => Drop it.
Then, with the already scored penalties, filter through spamassassin. And amavis - and razor. and more. If the mail is a winner => off to the spam box it goes.We have a guy called fail2ban that analyses the main postfix mail log 24h/24. For every mail that comes in, and the simple server to server transaction 'stinks'or the mail looks like spam, that mail server gets blacklisted at firewall level.
This is the result. And this one to check for the reason why as SSH connects, Apache2 connects etc is also treated. Check out the "Postfix tab for more details.
After more then a decade, me doing close to nothing these days, 80 % of all mail is stopped right at the doorstep - reduced to a line in the mail log :Like : 2021-01-21 16:10:10 postfix : From host a.b.c.d : Hi - and bye.Take note : for me, blocking IPs based on a country is not possible, as our clients are from all over the world.
Example : last month, some agency called Expedia (States based) started to use a bunch of IPv4, formerly known as "from Pakistan ....".
What also happens is : I get mail from Egypt, Cairo. From a fried. LIves in Germany. Who forgot to shut down his VPN (he has a complicated live and many issues with things called "torrents").Geoip IPv6 database will probably never exist as the one wouldn't fit in our galaxy. 25 of all our incoming mail is IPv6. And as aid in another thread this morning : my first IPv6 are already banned.
Btw : I even added some domain names used by friends to my mail server, as I knew they would send and receive a lot of mails. That was just perfect to auto-train my anti spam AI.All this beauty is available of the selves, free, and keeps working over time.
I use a dedicated IPv4 and IPv6 for each domain. This is VERY important.
Also : self-hosted means for me : a 50 $ / month dedicated server in a big data center, as hosting behind an ISP line (our case) is a big no-no.