Snort Blocking IP on Custom Passlist
-
Hello,
I have come across an issue where snort is blocking a specific external IP. I have followed the docs found here:
https://pfsense-docs.readthedocs.io/en/latest/ids-ips/setup-snort-package.html#managing-pass-lists
and created a custom pass list that included the IP that we do not want blocked. I then assigned that custom pass list to External Net as it says in the docs, manually cleared the block, and restarted the interface. I can see that the IP is listed on the list, however snort still blocks it. I am not sure why snort is still blocking the IP.
-
Hello,
I'm not a SNORT expert but I might be able to help. It sounds like you have done all the steps right. When you select the view past list button on your External Net interface is the IP you want to whitelist in the list?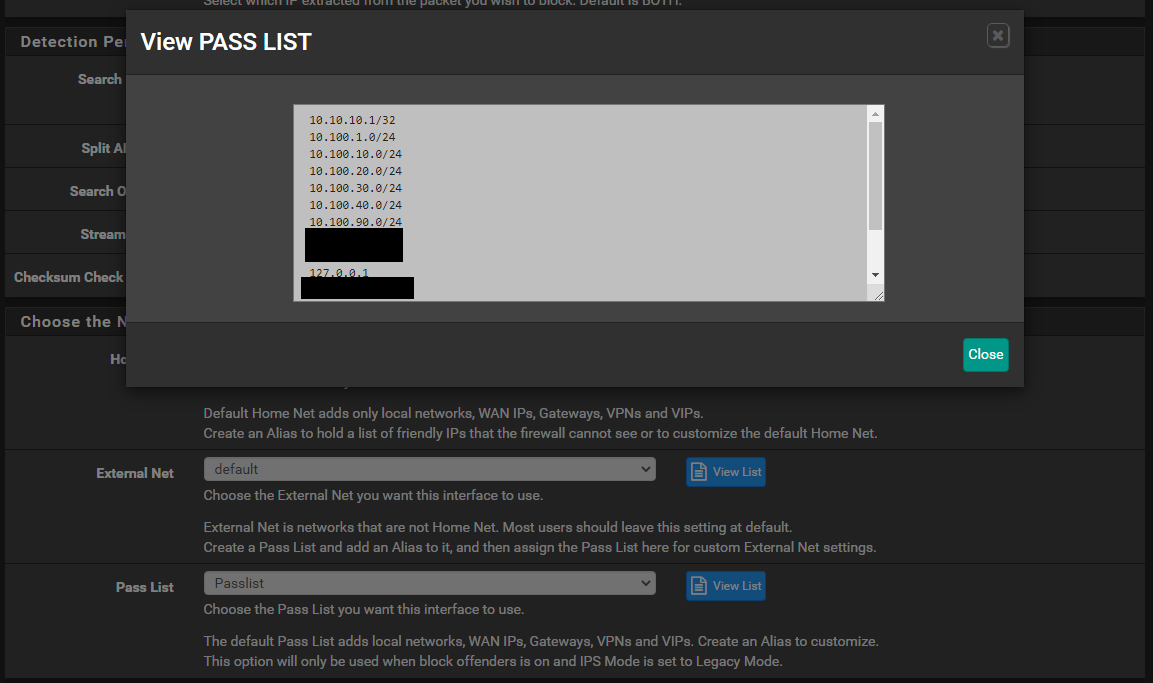
-
@bchok said in Snort Blocking IP on Custom Passlist:
I have followed the docs found here:
Hello!
I think the docs are (still) incorrect.
https://forum.netgate.com/topic/150961/pass-list-documentation?_=1613315390583
John
-
@bchok said in Snort Blocking IP on Custom Passlist:
I then assigned that custom pass list to External Net as it says in the docs
Sorry, last night I misunderstood what you meant by "External Net." I thought you were referring to the SNORT interface in general and not what becomes the $EXTERNAL_NET variable in the rules. If you put the External Net last back to defaults you will see that it is basically !$Home_Net (Not Home Net) which I guess makes sense in most cases, but I can think of exceptions like when you have a DMZ. External Net is supposed to be where the bad guys are. In the pfsense Snort package it looks like if you apply a nondefault pass list to External Net it negates the ! for each of the entries, so it appears Snort becomes useless on that interface. To accomplish what I think you are trying to do I have always used the past list option. Snort will process the packets as normal, write the alert, and then right before it would block it checks this list before it actually blocks. I wish the pass list tab was just the list tab where it had the ability to negate the list so the $EXTERNAL_NET could be modified like you tried.
-
In general you should NEVER monkey with the HOME_NET or EXTERNAL_NET variables in Snort on pfSense. The defaults are fine for almost every case I can think of.
I think sometimes folks make incorrect assumptions about what those variables actually are. HOME_NET is the IP networks or hosts you want to "Protect". They are where your jewels are stored so to speak. EXTERNAL_NET is where the bad guys live. That is assumed to NOT be inside your protected networks. Thus EXTERNAL_NET defaults to !HOME_NET (or all addresses NOT contained in HOME_NET). That is a logical choice.
Do not confuse HOME_NET or EXTERNAL_NET with Pass Lists. Those are completely separate things! Pass Lists are assigned and used to prevent certain hosts from being blocked. That has nothing to do with HOME_NET or EXTERNAL_NET directly.
The only time I can imagine where you might want to monkey with HOME_NET is if you have downstream networks not directly associated with a pfSense interface that you want to mark as "protected". In this case you would need to create a custom HOME_NET, but you would want to be sure that you included the default networks in that list.
The PASS LIST tab is for creating customized lists. And lists created there are usually assigned as Pass Lists, and thus that's how the tab got its name because there is almost never a reason to monkey with HOME_NET or EXTERNAL_NET. However, for the rare time when you may need to monkey with HOME_NET, you would do so by creating an IP list under the PASS LIST tab and then assigning that list name under the HOME_NET drop-down.
HOME_NET and EXTERNAL_NET are special variables used in many of the Snort rules. If you get the wrong IP addresses or networks defined in there, you can totally neuter your Snort traffic inspection. That's why I tell folks not to mess with the defaults unless you are an IDS/IPS admin expert with lots of experience. You need to know exactly what you are doing when messing with either of those two variables.