Log guest users traffic internal IP and destination IP
-
Hi I am currently planing to switch from Zyxel USG to pfsense firewall for my small hotel in France. The french legislation forces me to log the guest traffic up to a certain degree so that in case of some legal issues the user can be tracked down. With Zyxel I had a syslog with following information for the guest VLAN:
Time/Date - Username - Internal IP - Destination IP - Client Mac adress
Is something similar possible with pfsense, what data can I easily log?
Thanks for your help :)
-
@lens it is possible, but using the firewall logs, not the captive portal one
Also, on a side note :
@lens said in Log guest users traffic internal IP and destination IP:
The french legislation forces me to log the guest traffic up to a certain degree
As you said yourself, to a certain degree. Traffic logs are way too detailed here. Plus, they are not really usefull for 2 reasons :
- most websites are nowadays using CDN (akamai, cloudflare, etc).
- the logs will take too much space, meaning retention policy will be way to short. To give you an idea, France impose its keys enterprise ("Operateurs D'Importance Vitale" : banks, energy companies, hospitals, etc) to retain their infra & network logs for at least 6 month.
Instead of logging the TCP traffic, i would suggest you to log the DNS one. DNS + captive portal logs will probably be enough for law enforcment. If you are really worried, you could setup a transparant proxy & also log requests there...through you need to be aware that you won't see much more than DNS logs (nowadays HTTP traffic is mostly made over TLS)
-
Thanks for your input. I do not want to use a proxy. I just need to be able to prove that a certain request at a certain time was not from myself the owner. So if I have the time stamp + internal IP and some sort of destination IP then that should be ok. Can you tell me how the DNS Log looks like to have a better idea.
So I guess if that is sorted I only need to find the right hardware... :).
-
@lens said in Log guest users traffic internal IP and destination IP:
I just need to be able to prove that a certain request at a certain time was not from myself the owner.
Another solution might be : route all the traffic from the captive portal's interface over a VPN.
At least, use the LAN for yourself, and some OPTx interface for the captive portal.Btw : i'm using the captive portal for a hotel, in France. I've abandoned years ago any form of 'extra' logging. Even the MAC addresses that are recorded are fake ones, created just for our captive portal's Wifi (at least, iOS is doing so be default).
What exists today : some IP - my WAN IP, hits some questionable IP address. Traffic content will be complete unknown as it is all TLS these days.
Never had a message from HADOPI (except the day the night auditor decided to use our connection to download some Disney movies ...)These these I have the users share my single Orange VDSL "24 Mbits.sec" connection (the fibre is coming soon).
Also : pfBlockerNG with some feeds that lists famous download peers will help you.
The bandwidth monitoring can also show suspected 'full scale' downloads :
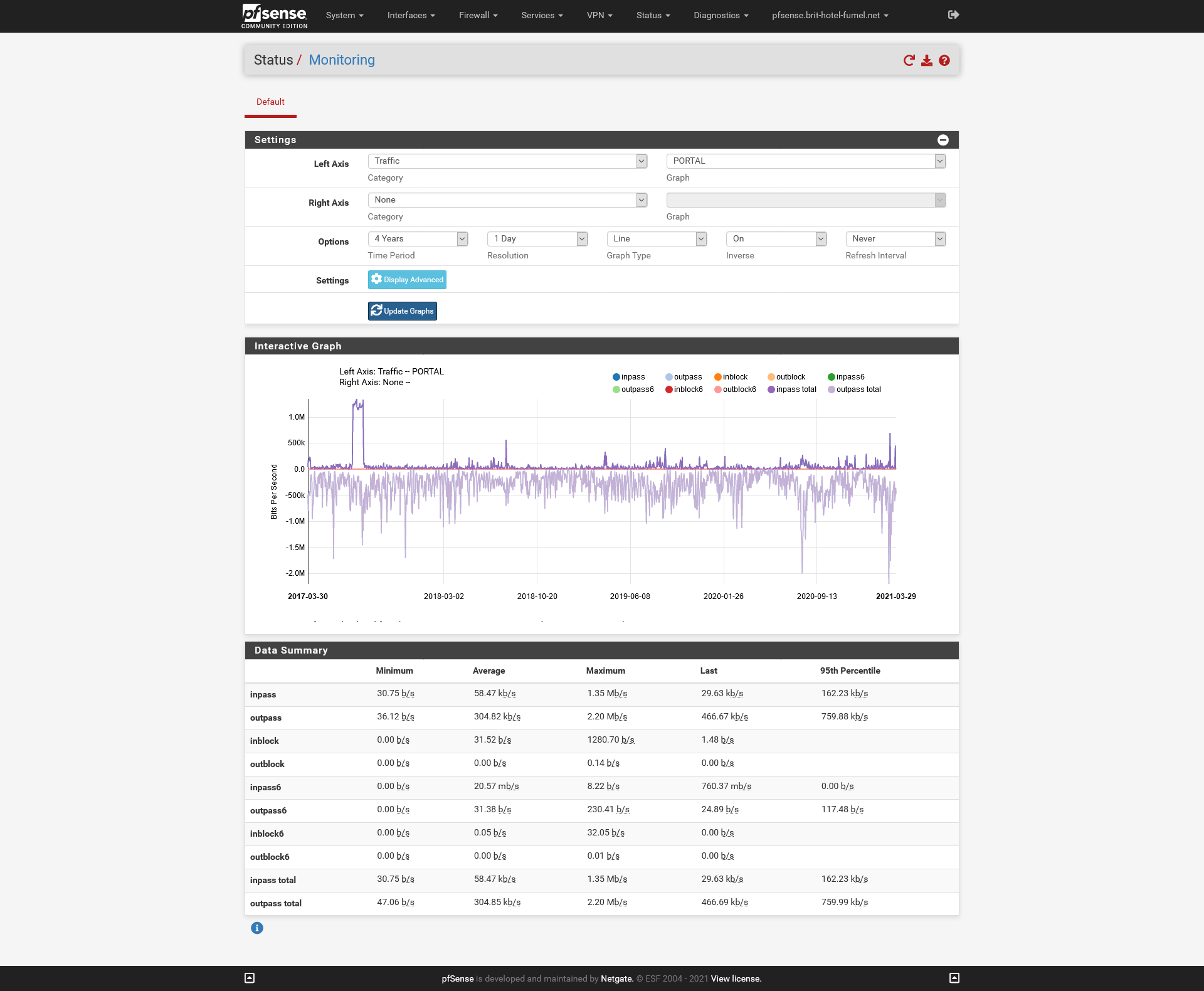
= 4 years of stats.
Keep in mind taht even 'Windows' uses P2P to download the winter edition of windows 10 ^^