Firewall 101
-
@johnpoz said in Firewall 101:
Unless you setup outbound rules on floating?
Nah I removed all my rules from floating and anywhere else, what you see is all my rules.
And I rebooted the device.
-
dot over 853, sure ok use tcp.. But normal dns over 53 can also use tcp..
Its been years and years since played with ipcop or ipfire - but I don't recall them using any outbound rules either. Was always inbound to the interface for rules.
-
@johnpoz said in Firewall 101:
But normal dns over 53 can also use tcp..
Yes that's right but in my case all DNS locally is 53/UDP and it goes out TCP/853 for external look ups.
@johnpoz said in Firewall 101:
Its been years and years since played with ipcop or ipfire - but I don't recall them using any outbound rules either. Was always inbound to the interface for rules.
Yea so you can configure the default behaviour of the firewall in IPFire. So yes by default it allows all out, but in Firewall settings you can set it to default block all out, and then we just choose what we want to allow out.
-
@propercactus said in Firewall 101:
all DNS locally is 53/UDP
That is not always true.. DNS client can switch to tcp when the answer is larger than what udp would allow for. Which use to be 512, with edns that has gotten larger and normally defaults to 4096. But it is not good practice to prevent a client from using tcp over 53, in the event answer to what its looking for exceeds the max size that can be done over udp. And it would have to switch to tcp.
-
@johnpoz said in Firewall 101:
DNS client can switch to tcp when the answer is larger than what udp would allow for
Ok I changed that rule to allow TCP/UDP.
Error still remains tho, I cannot get to any website.
-
Did you look at the firewall log to see if blocking anything - if not logged in pfsense, again your browser error is not always good source of where something prevented you from doing something.
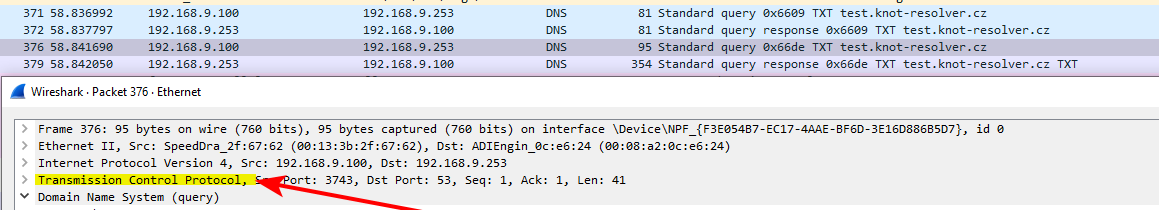
And just to be complete. Here is test showing client switching to TCP over udp doing a test where I turned off edns with +noedns in the query..
dig @192.168.9.253 test.knot-resolver.cz. TXT +noedns
You can see in the sniff client switched to tcp
If pfsense is not logging that it blocked where you were trying to go in the browser - then sniff on pfsense wan (red) and did the traffic get sent?
-
@johnpoz said in Firewall 101:
dig @192.168.9.253 test.knot-resolver.cz. TXT +noedns
I think the floating rules table was gammied up? I added a rule in floating to allow all HTTPS, then I deleted that rule and now it is working.