Any reason to allow multicast on WAN?
-
I see traffic from the WAN address to the multicast address (224.0.0.1) for both ICMP and IGMP traffic. Is there any circumstance where I would want to allow this?
While on the subject of stuff that is blocked by default, is there any reason to allow DHCP traffic from 0.0.0.0 over port 68 to 255.255.255.255 port 67 on a LAN interface? In this case I'm using a DHCP server within the LAN interface and have DHCP disabled on pfsense.
I assume the default rules are fine and I'm not seeing any problems. Just asking for my own education.
-
There are hidden rules that allow dhcp when you enable dhcp server, and on wan for dhcp client, etc.
No there would be no reason to allow for multicast on wan.. It sure not going to go anywhere - and pfsense. If the noise is bothering you in the log, you can just create a rule to block it and not log.
-
@johnpoz said in Any reason to allow multicast on WAN?:
There are hidden rules that allow dhcp when you enable dhcp server, and on wan for dhcp client, etc.
No there would be no reason to allow for multicast on wan.. It sure not going to go anywhere - and pfsense. If the noise is bothering you in the log, you can just create a rule to block it and not log.
Kinda figured, but good to know anyway. Thanks!
-
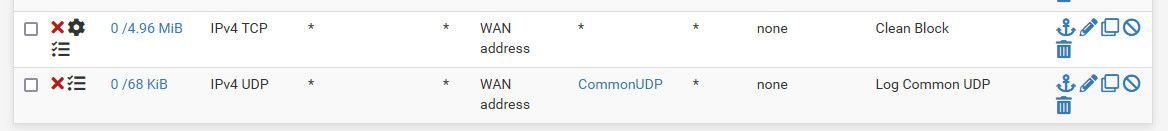
I personally don't like seeing all the noise that default logging produces, so I turn off default logging and just put in my own rule that logs what I want to see which is common udp ports, and tcp traffic with syn set.
-
@johnpoz said in Any reason to allow multicast on WAN?:
No there would be no reason to allow for multicast on wan..
On IPv6, allowing multicast is essential. It won't work without the various multicasts.
-
And what does that have to do with anything?
He is clearly blocking it now anyway.. Pfsense would enable by hidden rule the requirements for IPv6 to function. If it was actually enabled on pfsense.
(224.0.0.1) for both ICMP and IGMP traffic
Is not IPv6, and in what sense is multicast required for IPv6? Where in the rfc does it say that? ICMPv6 yes - multicast where?
-
@johnpoz said in Any reason to allow multicast on WAN?:
multicast where?
Things like router and neighbour solicitation. For example, the all routers multicast, all hosts multicast, etc.. Then there's solicited node multicast, to see if an address is in use. That's just off the top of my head. One other thing to bear in mind is there are no broadcasts with IPv6, with that function provided by all hosts multicast.
-
ICMPv6 to a multicast address.. Say
# IPv6 ICMP is not auxiliary, it is required for operation # See man icmp6(4) # 1 unreach Destination unreachable # 2 toobig Packet too big # 128 echoreq Echo service request # 129 echorep Echo service reply # 133 routersol Router solicitation # 134 routeradv Router advertisement # 135 neighbrsol Neighbor solicitation # 136 neighbradv Neighbor advertisement pass quick inet6 proto ipv6-icmp from any to any icmp6-type {1,2,135,136} tracker 1000000107 keep state # Allow only bare essential icmpv6 packets (NS, NA, and RA, echoreq, echorep) pass out quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type {129,133,134,135,136} tracker 1000000108 keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type {129,133,134,135,136} tracker 1000000109 keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type {128,133,134,135,136} tracker 1000000110 keep state pass in quick inet6 proto ipv6-icmp from ff02::/16 to fe80::/10 icmp6-type {128,133,134,135,136} tracker 1000000111 keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type {128,133,134,135,136} tracker 1000000112 keep state pass in quick inet6 proto ipv6-icmp from :: to ff02::/16 icmp6-type {128,133,134,135,136} tracker 1000000113 keep stateIs not all Multicast - and sure isn't to 224.0.0.1
As I stated if it was required for IPv6 to work, the rules would already be there - hidden.
His blocking of IPv4 multicast noise is not going to break anything..