Microsoft 365 and pfSense
-
@gertjan Yep, I simply pulled the port 25 directly from his list where it seems like the intent is "allow my LAN clients to only do SMTP to the following destinations" (simply wrote it the other way in a default deny)
:) -
Dear All,
Thanks for your kind care and try helping me. As @Gertjan said I'm limiting users for using the internet as I need to open the desired URLs and IPs for my LAN interface using MS 365.
@johnpoz we aren't using IPv6 in our environment.
So, I need to migrate very soon and don't know How I can solve this issue as Microsoft said, I need to allow all the following in their article
https://docs.microsoft.com/en-us/microsoft-365/enterprise/urls-and-ip-address-ranges?view=o365-worldwide
Thank you all and waiting your recommendations
-
@mohkhalifa said in Microsoft 365 and pfSense:
don't know How I can solve this issue as Microsoft said
I gave you all the info you need.. Since your not using IPv6 - you need to allow for the IPv4 ranges listed.. Is that simple.
If your doing any dns filtering.. Allow for those domains to be queried.
fqdn and domains are for dns/proxy use - IP ranges are for firewalls. It is not possible to allow a firewall to to resolve a wildcard domain to IPs. There is no firewall that could do this. A "firewall" doesn't see the dns query.. It only sees traffic to an IP on a port..
For such a thing to work, a UTM would also need to be running the dns. "AND" within the couple of ms since a client did a query for said fqdn, that would have to be put into the firewall rules to allow or not.
-
@johnpoz Thanks for your reply. I will try and let you know
-
@mohkhalifa just to go into a bit more detail on this. Even our big boy/name Multi K $ NG firewalls in our DCs do not support such a function of filtering on DNS name.. Since this is not really how firewalls function. Even though customers do ask for such nonsense quite often..
Proxies do that.. While yes many firewalls allow for aliases based on a fqdn they can query on some sort of timed schedule. And yeah sure many allow for loading a set of IPs or netblocks from some file hosted somewhere that change.
As I went over a wildcard domain would never be possible to use to populate a table of IPs or CIDR.. Since those are impossible to query before hand and get an IP or list of IPs..
When a client wants to go to some site on the public internet - it doesn't send that as a fqdn, it sends that to the gateway as IP:PORT or IP protocol like with icmp, etc.
Now while it "might" be possible for some UTM sort of device where clients as their gateway also use that devices IP as dns, and via some magic this device says ok client X from IP just did a query for sljfdsljsdlf.wildcardallowed.domain.tld which resolve to IP 1.2.3.4 - allow that.. I have never seen such a beast. MS would be having a really hard time getting their stuff to work if that was what was required for anyone running typical firewall..
What happens when the gateway is not the firewall? Most companies that use office365, can almost promise you there is a router internal to the network that clients point to for their gateway, which may or may not firewall internal networks and even external traffic - there is for sure going to be an actual edge firewall.. Many companies the client for sure is not using the firewall as their dns. MS shops for sure - can promise you most of those are pointing to their AD DNS, so how would the edge firewall know where the client actually wanted to go other than IP:Port?
Those fqdn and wildcards are listed for proxy and dns to use, while the cidr are given for firewalls that work based IP... Proxies for example are never really sent an IP, they are sent the fqdn the browser or application want to go.. The proxy then looks up where that fqdn resolves to and the proxy goes there for the client. Sure they can also work if client tries to go to https://1.2.3.4 - but have seen some balk at that sort of url.. Unless IPs are specifically allowed for by the proxy.
That is why proxies can use wildcard domains.. Because they can say oh client is looking for bla.bla.whatever.something.domain.tld, yeah that is allowed by *.domain.tld.. It then looks up bla.bla.whatever.something.domain.tld gets the specific IP for that and then the proxy goes there.. If that IP is allowed by the firewall upstream of the proxy that is ;)
-
Dear All,
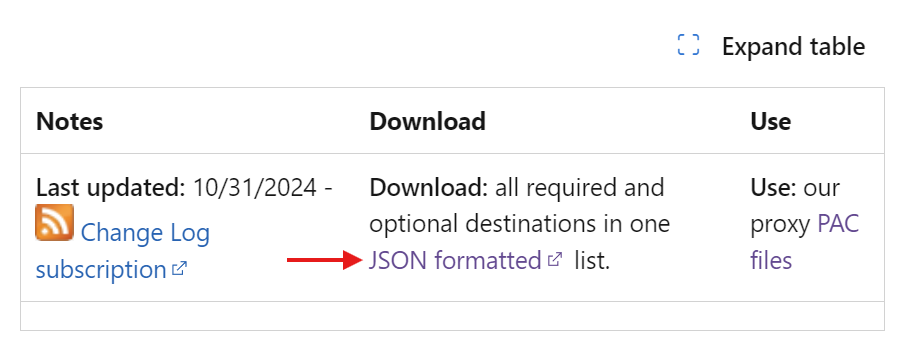
Microsoft created a JSON file includes all M365 firewall rules. Is there any idea to add it to pfSense instead-of creating them manually as they are too much.
Thank you
https://endpoints.office.com/endpoints/worldwide?clientrequestid=b10c5ed1-bad1-445f-b386-b919946339a7
-
@mohkhalifa said in Microsoft 365 and pfSense:
https://endpoints.office.com/endpoints/worldwide?clientrequestid=b10c5ed1-bad1-445f-b386-b919946339a7
you can for sure take all of those networks and put them into a alias and allow..
But those ones that list *.domain.tld are impossible in a L3 firewall.. That ends up being almost infinite amount of IPs that could be resolved.. How could you put those into a list of networks or IPs?
Such listings only make sense for dns or proxy sort of blocking.
Notice says use our proxy PAC file ;)
-
@johnpoz Thanks for your reply. Can you advise with a good Proxy Virtual appliance ?
-
@mohkhalifa there are few proxy users on here, squid could be used like this.
But you can also just whitelist the networks listed.. Unless you were specifically blocking domains, ie already running a proxy - most of the domains they say to whitelist wouldn't be required.
-
@mohkhalifa said in Microsoft 365 and pfSense:
Microsoft created a JSON file includes all M365 firewall rules. Is there any idea to add it to pfSense instead-of creating them manually as they are too much.
Thank you
https://endpoints.office.com/endpoints/worldwide?clientrequestid=b10c5ed1-bad1-445f-b386-b919946339a7
we use pfBlockerNG—specifically its (JSON, yes) parser and floating auto-rule creation functionality—to accomplish outbound IP whitelisting to M365/O365 endpoints.
any domains that may need to be whitelisted would need to be done so manually and depend entirely on what's otherwise DNSBL-blocked (if anything) in your environment.