Block traffic between networks
-
openvpn will create the general openvpn firewall rule either on a server or a client, or many of them
Then rules on the openvpn are applied globally
It comes handy in some occasions
Assigning a specific interface both in client and server scenarios allows for more granular control of firewall rules.
And you can also add the interfaces into traffic monitor and see graphs.
As a rule if you use assigned interfaces you should move rules to specific interface tab. Otherwise it becomes confusing/ -
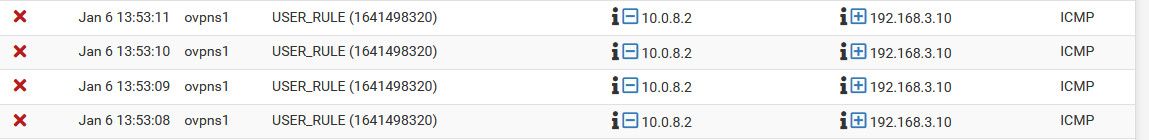
@hfarinha here, I connected via different vpn instance (different port).. And that same openvpn interface and its rules are used.
Notice this block is from different tunnel network 10.0.8 vs 10.0.200 and the "interface" is opvn1 vs 2 in my previous pic
If you want to block only specific clients, just setup the clients to always get the same IP when they connect, etc. This is easy enough to do with the client specific overrides tab in the vpn setup area.
-
my confusion at this point is not how to allow/deny traffic but how I assign an interface for openvpn as suggested.
here's my nic assignment:
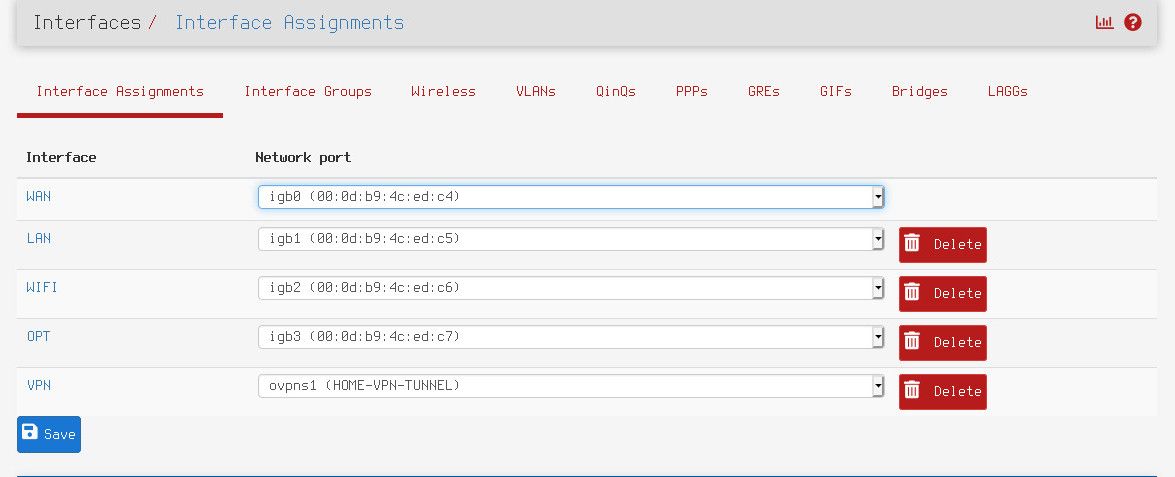
I want to configure all VPN fw rules under the newly assigned 'VPN' nic however I can't get rid of "OpenVPN" under FW rules. I have no rules under VPN nic and vpn traffic still flow as normal so it seems that rules under OpenVPN are still in effect as I'm allowing traffic there.
-
@hfarinha vpns1 is the first openvpnserver, vpns2 the second etc
vpnc1 is the first vpnclient interface vpnc2 the second etc.As simple as that
-
@hfarinha said in Block traffic between networks:
but how I assign an interface for openvpn as suggested.
There is little reason to assign an interface for remote clients connecting to pfsense as server. The global openvpn interface works for your remote access rules, be it you have 1 instance running or multiple instances running.
But you would assign those interfaces here.
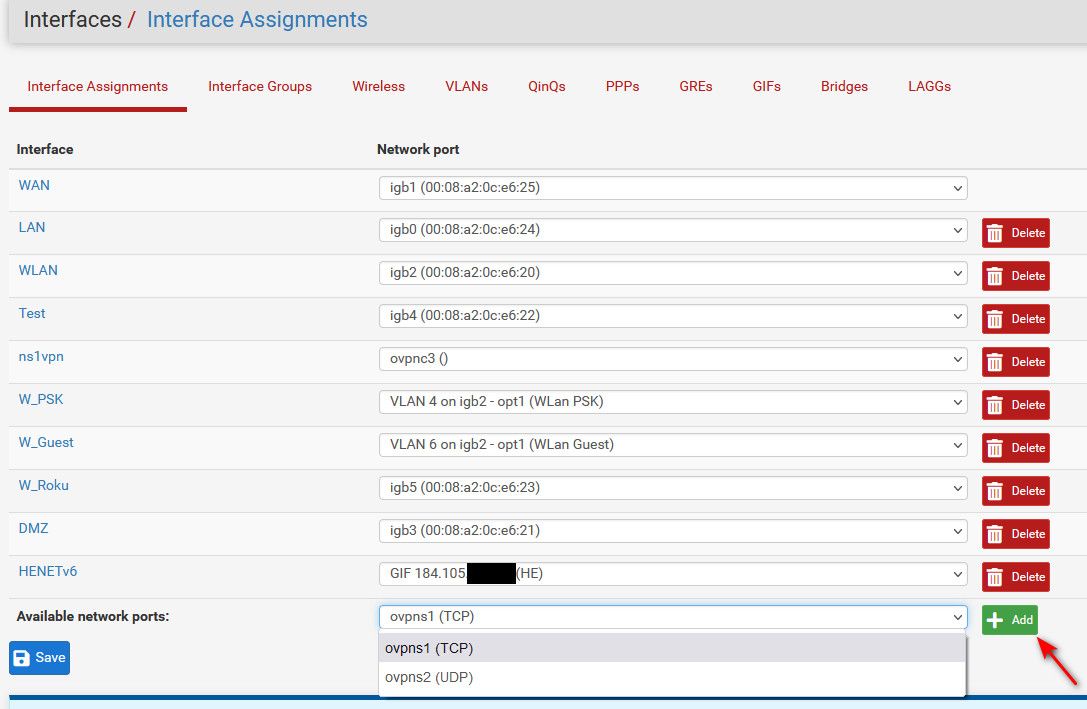
But that really is only something you would do if pfsense is the client to some vpn server/service somewhere.
See above my ns1vpn interface and what its assigned too.
-
I only have one VPN client however I don't see any new interface being created when I establish the tunnel from remote client.
Here's what I did, I assigned interface ovpns1 and called it "VPN" (as explained before).
Then I recreated all the rules I had under "OpenVPN" in "VPN". Then I disabled all rules under "OpenVPN" and now everything works as it was before. This actual fixed a long time issue that I was having with 'DNS resolver' service. Before assigning the new interface I could not enable this service for VPN remote users, so I had to manually push (via openvpn tunnel config) upstream resolvers to the vpn client. Now with the new interface assigned and added to 'DNS resolver' I no longer need to do this. I now have "OpenVPN" with no rules and I don't think I can delete it. -
@hfarinha You cant delete it. Just move the rules and it will be fine
-
@hfarinha said in Block traffic between networks:
new interface being created when I establish the tunnel from remote client.
Who said there would be?
This actual fixed a long time issue that I was having with 'DNS resolver' service
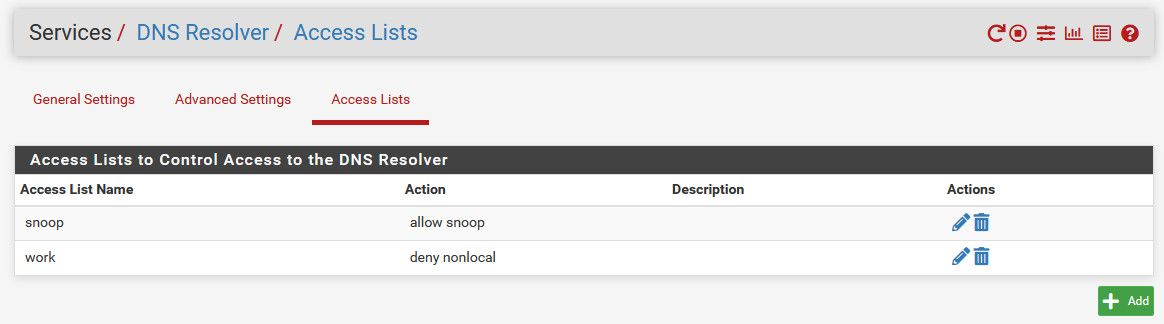
If you want remote vpn users to use unbound running on pfsense, you just need to create a ACL that allows the tunnel network.. Unbound automatically creates ACLs to allow networks its attached to ask unbound for dns. Tunnel networks are not included in these auto acls, so if you want remove vpn uses to ask unbound, you just need to create a ACL in the unbound settings to allow.
-
@johnpoz said in Block traffic between networks:
auto acls
I'm not sure about those "auto acls" from unbound as I don't see them in any place, however I added rules to allow DNS traffic to each of the firewall GW IPs and everything is working as expected.Thank you all!
-
@hfarinha said in Block traffic between networks:
DNS traffic to each of the firewall GW IPs and everything is working as
well you would need to be able to talk to the dns port yes.
The auto created acls are on the unbound advanced page
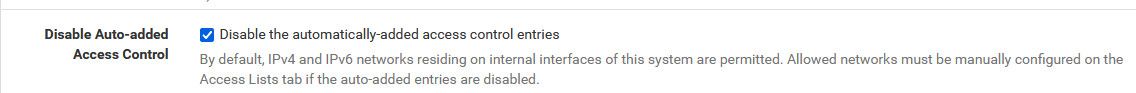
I have mine disabled, and create my own acls
-
@johnpoz The auto option was not enabled under DNS Resolver service however "Services -> DNS Resolver -> Access Lists" was empty. I enabled "Disable Auto-added Access Control" just in case as I want to control this manually. thanks.
-
@hfarinha forgot to mention that I had to add acl's manually as well under DNS resolver otherwise dns resolution does not work.