Snort intercepted "Signal App" traffic as a trojan! Reason to worry?!
-
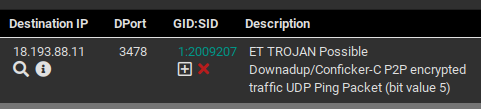
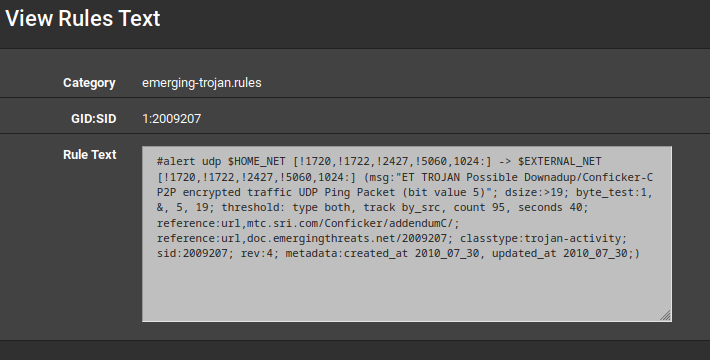
Snort intercepted "Signal App" (android) traffic from WAN interface as a trojan!
Reason to worry?!
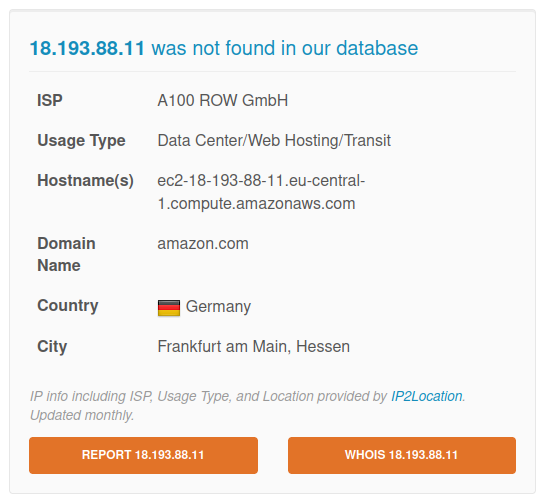
Whois 18.193.88.11
-
If you are 100% certain the origin of the traffic is from a device running the Signal app, and the captured session is from an active Signal session, then I would tend towards ruling it "false positive".
But if there is any doubt, then a thorough virus/malware scan of the machine would be in order to make sure there is no infection. That is an old worm, though. And so far as I know, there never was a mobile app variation of it -- only PC.
Copyright 2025 Rubicon Communications LLC (Netgate). All rights reserved.