Routing Virtual IP traffic through VPN gateway
-
I have a sniproxy[1] set up on a Virtual IP, which works fine. However, I now want to route its WAN traffic through an OpenVPN gateway.
How do I proceed here? I added a LAN rule with a Virtual IP in question in Source and specified the OpenVPN gw, but that did nothing – the WAN gateway is being used still. I suppose I need to NAT it somehow, but have no clue how to proceed here.
Any ideas?
EDIT: Note that I have an identical sniproxy set up on a separate host, and routing its traffic through OpenVPN gw using an identical firewall rule works fine.
[1] Installed using FreeBSD packages. Will migrate to HAProxy once I get it working.
-
Anyone, please? Any hint will be greatly appreciated.
-
@kultigsptrizigfrisch said in Routing Virtual IP traffic through VPN gateway:
[1] Installed using FreeBSD packages. Will migrate to HAProxy once I get it working.
Why are you fighting with an unsupported package as you plan to replace it in the future anyway?
Basically also not clear what you want to do here.
Did you state remote destination device as backend in sniproxy? -
@viragomann said in Routing Virtual IP traffic through VPN gateway:
Why are you fighting with an unsupported package as you plan to replace it in the future anyway?
I am not fighting with it, it works fine, and I don't understand the implication. I'd assume my approach is quite logical: I am migrating a properly-running service from separate host onto pfSense. It's obvious to me to do so by reducing the number unknown variables, i.e. to do the migration one step at a time. So first I want to get the SNIproxy running on the pfSense as is, using the same config as o the separate host, and only then will migrate the configuration to HAProxy
Basically also not clear what you want to do here.
Want to pass the SNIproxy traffic via OpenVPN gateway. SNIproxy is bound to a Virtual IP address, so effectively I want to force the Virtual IP traffic through an OpenVPN gateway. The rule I added seems to do nothing.
Did you state remote destination device as backend in sniproxy?
I can have it bound to a specific IP address, nothing more. The rest has to be done with routing/firewall.
I am stuck trying to get to force that SNIProxy traffic to go through the OpenVPN gateway.
-
This post is deleted! -
Also note that when I say Virtual IP, I have an IP Alias in mind.
-
Seems related:
https://redmine.pfsense.org/issues/5476 -
@kultigsptrizigfrisch said in Routing Virtual IP traffic through VPN gateway:
Basically also not clear what you want to do here.
Want to pass the SNIproxy traffic via OpenVPN gateway. SNIproxy is bound to a Virtual IP address, so effectively I want to force the Virtual IP traffic through an OpenVPN gateway. The rule I added seems to do nothing.
That was not clear to me, cause you mentioned a firewall rule on LAN in regards.
Therefor I assumed, you tried it with policy routing. But this does not work here.I can have it bound to a specific IP address, nothing more. The rest has to be done with routing/firewall.
As mentioned, policy routing cannot work, because that would need an interface to be added to. But behind the proxy the packets are already inside pfSense and don't pass any interface.
You can only direct the traffic to the destination IP at the remote site within the proxy directly. If this is not possible with sniproxy, there would be no way.
HAproxy can do this though. -
@viragomann said in Routing Virtual IP traffic through VPN gateway:
You can only direct the traffic to the destination IP at the remote site within the proxy directly. If this is not possible with sniproxy, there would be no way.
HAproxy can do this though.Thing is, I don't direct that traffic to any particular destination remote site – all the traffic that reaches SNIProxy is meant to be passed over to the intended remote hosts, based on the original TCP session. I don't think HAProxy would be of help here.
-
Also, someone suggested a solution on Reddit, but didn't have time to look into whether it would be applicable to this use case:
-
@kultigsptrizigfrisch said in Routing Virtual IP traffic through VPN gateway:
all the traffic that reaches SNIProxy is meant to be passed over to the intended remote hosts, based on the original TCP session
And how will sniproxy or pfSense know to which IP the packets are "meant"?
-
SNIproxy "Proxies incoming HTTP and TLS connections based on the hostname contained in the initial request of the TCP session. This enables HTTPS name-based virtual hosting to separate backend servers without installing the private key on the proxy machine."
I have it configured to forward the request to the original hostname, thus really just forwarding the original requests as is. Except I want them forwarded over the VPN.
-
@kultigsptrizigfrisch said in Routing Virtual IP traffic through VPN gateway:
I have it configured to forward the request to the original hostname
So this means to me you are forwarding yourdomain.name to yourdomain.name. And I'm wondering how this should work at all.
thus really just forwarding the original requests as is
The hostname is part of the header. The proxy should forward this anyway to the destination server. But in my opinion you have to state the destination IP in the proxy config to get the packets forwarded as you want.
-
@viragomann said in Routing Virtual IP traffic through VPN gateway:
But in my opinion you have to state the destination IP in the proxy config to get the packets forwarded as you want.
I have a wildcard there that forwards to the original destination:
table { .* * }The whole reason I am doing this is to avoid geoblocking of some services. SNIProxy configured as such allows me to specify the DNS overrides in dnsmasq config per domain, wildcarded. This wrks as intended on a separate host, but I want to give up using SNIProxy at all and switch to HAProxy directly on the firewall.
-
@kultigsptrizigfrisch
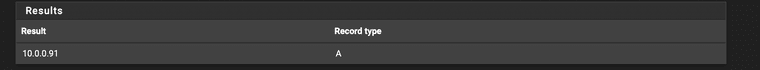
So go to Diagnostics > DNS Lookup and resolve your hostname and you will know where the packets are directed to. -
@viragomann said in Routing Virtual IP traffic through VPN gateway:
Diagnostics > DNS Lookup
Truly don't understand what do you mean. I know that my selected DNS domain queries are directed to SNIProxy by dnsmasq, as I intend, because I can see that in the sniproxy logs. What I now need to do is to have that traffic forwarded by SNIProxy to be routed via the VPN gateway, so that it evades the geoblocking. This is the issue at hand.
-
@kultigsptrizigfrisch said in Routing Virtual IP traffic through VPN gateway:
I know that my selected DNS domain queries are directed to SNIProxy by dnsmasq
The question is, where the traffic is directed to behind the proxy.
-
The question is, where the traffic is directed to behind the proxy.
Still don't follow. Behind the proxy, in this context, is between the sniproxy running on the firewall and the LAN host(s).
-
@kultigsptrizigfrisch
Dude! Simply do what I suggested above to get where the hostname is directed to:
So go to Diagnostics > DNS Lookup and resolve your hostname and you will know where the packets are directed to. -
@viragomann said in Routing Virtual IP traffic through VPN gateway:
@kultigsptrizigfrisch
Dude! Simply do what I suggested above to get where the hostname is directed to:
So go to Diagnostics > DNS Lookup and resolve your hostname and you will know where the packets are directed to.Dude, I am literally telling you that DNS lookups work as intended, i.e. taking an exemplary domain I want to evade the geoblocking for, I see it resolves to sniproxy's Virtual IP, as I already explained, quote:
" I know that my selected DNS domain queries are directed to SNIProxy by dnsmasq, as I intend "
I see the traffic intended for those domains in sniproxy logs, and the websites work just fine, except I can't get it to route through the VPN's gateway and it instead uses the default one.