Rules request
-
I have a thread that a gentleman responded to another commenter that he disabled loging the default deny rule but has a rule in place to log tcp:syn and to log common ports I wanted to talk with him but in his signature he does not want to be chatted or pm'd unless its for mod related. I am very new to writing rules and alias' But would love to get his rules/alias for logging common pots and tcp:syn. So I am guessing that he will respond to this post. or he can email/pm with the details. thanks
-
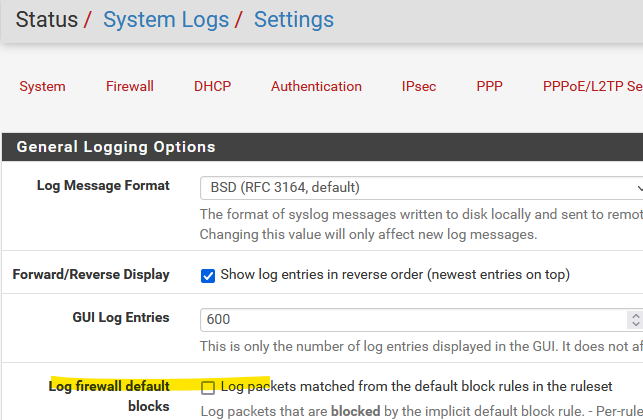
@troysjanda In general, you can uncheck:
...then add a rule near the bottom of your list on LAN (above "allow LAN to any"), something like:block from (LAN IP) to any, port 80
with "Log packets that are handled by this rule" checked...and add rules for any ports you do want blocked, on WAN or LAN.
-
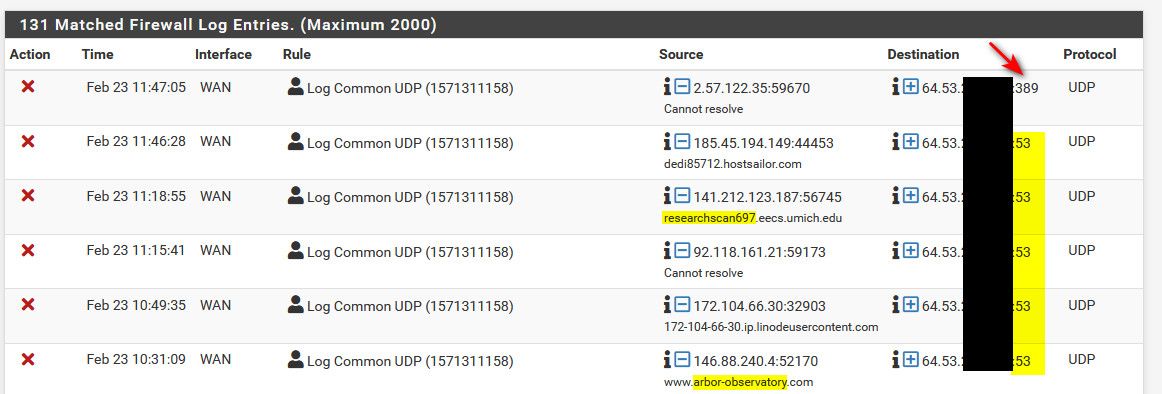
@troysjanda here..
Hope this helps - and thanks for reading the sig and not PM with request for help.. But you could of tagged me in thread..
Happy to help - only reason I don't like direct messages for help, is someone else prob going to have the same question, or would be interested in it.. Not real cost effective doing 1 on 1 sort of help unless something of it is of personal or private nature..
You can do what ever UDP ports you want, I just picked the most common ones - rarely get hits on those to be honest..
That is on my wan interface - very bottom 2 rules. I don't really block anything on my lan, and others have logging of what I block etc..
-
@johnpoz Thank you ill try and interpret that in to the actual rules and ill have to read up on how to use alais'
-
@troysjanda any questions just ask..
-
@johnpoz So to be clear I would
- disable logging default deny rule
- create a clean block rule with logging
- create a alias with the common udp ports
- create rule to log the alias and under extra options advanced select tcp:syn
or is there two rules one for the alias and one for the tcpLsyn?
really sorry but very new to writing rules I have used pfsense for years but just in the deafult state with just the dns redirect to pfsense and blocking external dns.
-
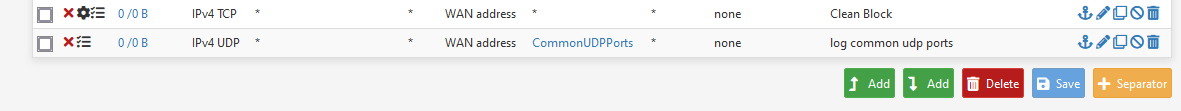
So this is what I did for the rules, and i just used the UDP ports you had in the alias on the port tab. I hope that this is right.
-
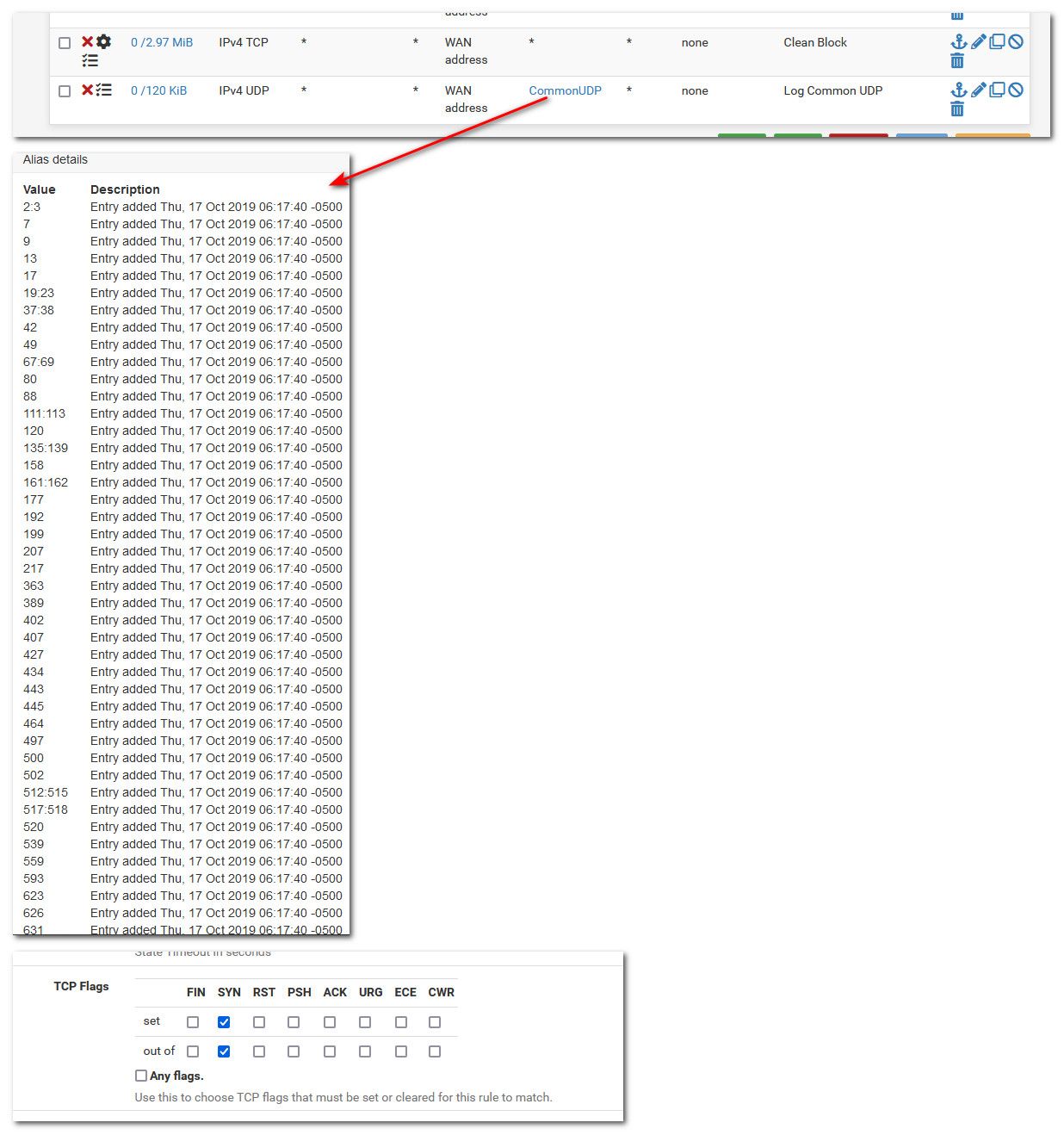
@troysjanda that was only a small fraction of the ports for udp ;)
Here I exported my list - but really should be your list.. What do you want to be logged..
-
@johnpoz Ill use yours as a template, and make changes as I start using it if thats ok? Als odo my rule look right in the screenshot?
-
@troysjanda yeah those rules look fine.. would depend on what you have in front of them if they would be triggered - from what you posted 0/0 means nothing has hit them as of yet.
-
@johnpoz that screen was just after creating them I am getting hits now,
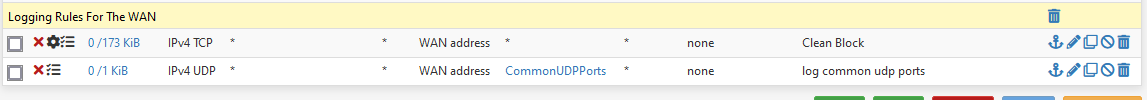
-
@troysjanda there you go.. see UDP is going to be minor hits.. But now you should see interesting stuff - while not blowing out your log with a lot of noise ;)
For example - just interesting is what is the most common hits.. Back awhile ago there was some issues hitting modem/gateways, and seeing lots of traffic on 7547.. I noticed huge upswing on traffic to that port during the issue.. Just interesting is all ;)
I think that was related to Mirai, that was back quite a few years now - 2016 I think... But I normally just look to see what is the top ports being hit, and see if any specific news about that port, etc..
TCP is almost always the most common 1433 (sql), ftp, ssh, telnet.. etc. etc..
UDP is normally quite boring - but the most common hitters are interesting to watch.. here are some of the latest hits.. Couple of those are research related - stuff scanning the internet for open stuff to do research. Some prob nefarious looking for open dns.. That 389 port is a LDAP port..
All ports that are not specifically allowed or forwarded are blocked by the default deny rule - but it can be interesting to see what sort of traffic is out there..
-
@johnpoz Very cool I will watch the logs over the next few days and see what hit me. I have only a few hits already for the commonudp today 137 had a hit and 123 also had a hit. I downloaded the tool you had posted on another topic Tracewrangler going to play with that as well.
thanks again
-
@troysjanda said in Rules request:
Tracewrangler going to play with that as well.
That is good for anonymizing a pcap that you want to post public some where..
-
@johnpoz so since enabling the commonports rule I have had 35 hits, and resolving them its mostly research type stuff that you mentioned
scan-01o.shadowserver.org port 443
zg-0122c-169.stretchoid.com port 161
researchscan704.eecs.umich.edu port 53To name a few.
-
@troysjanda yeah lots of noise ;) it can be interesting if your into that sort of stuff - hehehe
Most users of just your typical soho type router don't see any of this stuff, since their router doesn't show them actual logs, etc. It can be distracting and worrisome for some users new to how much noise is on the internet ;)
-
@johnpoz You can mark this solved if you'd like, not really sure how that works here at the Netgate Forums. I am very appreciative of your time and help. Thank you sir.