Firewall UDP ? Attack !! Or Normal ?
-
@silence said in Firewall UDP ? Attack !! Or Normal ?:
am I under a ddos attack?
A DoS attack is usually much higher volume and I would think be on other ports like 80/443. Normally a DoS attack's goal is to connect to some service (like a web server or DNS server) and make the service respond, to keep the server busy.
I think your ISP needs to answer the questions:
- can they block the traffic?
- was your IP being used by someone else, perhaps a VPN provider?
A similar example is that most phone companies won't immediately re-use a phone number. They wait a while so the new customer doesn't get calls for the old customer.
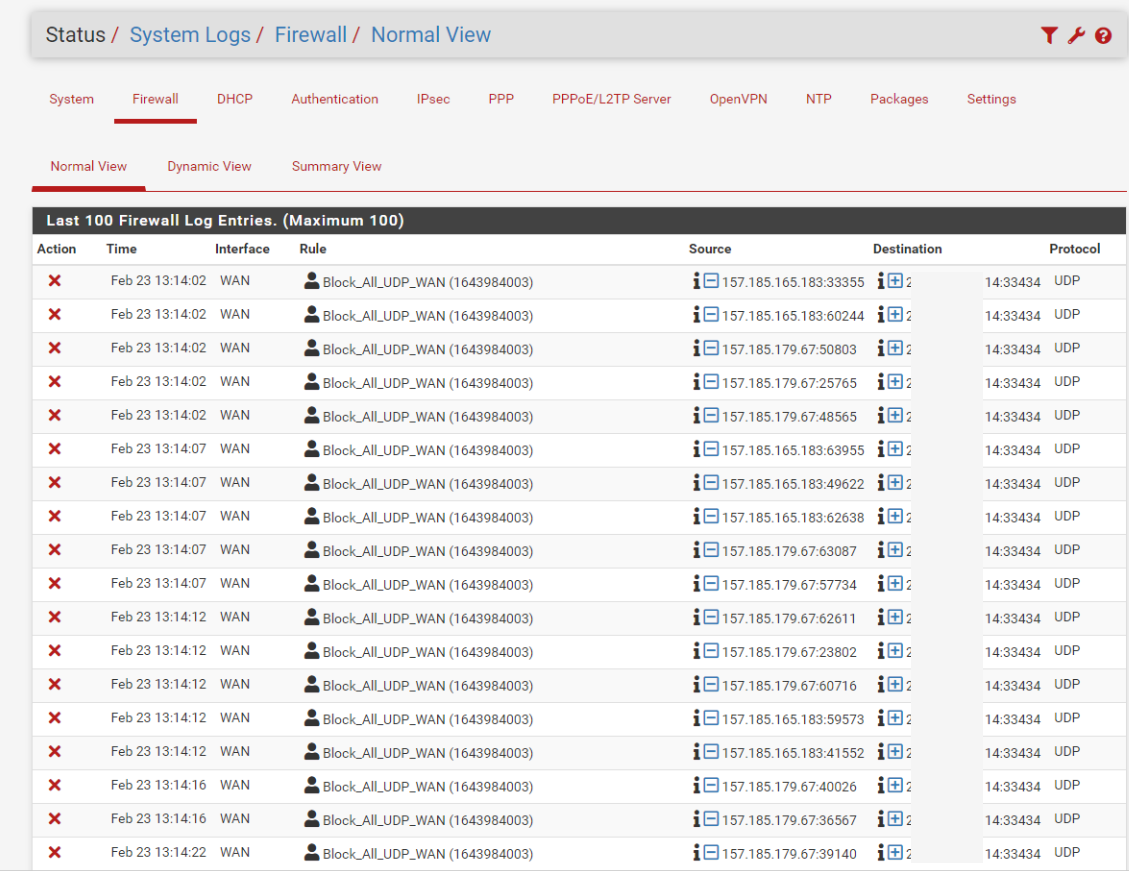
Random traffic probing any IP connected to the Internet is normal; they are scanning all IPs on the Internet looking for servers to exploit. A high volume of traffic coming to one specific port is not normal.
I would definitely not log each packet, that's just unnecessary CPU time and SSD write life wear.
-
@steveits said in Firewall UDP ? Attack !! Or Normal ?:
was your IP being used by someone else, perhaps a VPN provider?
Investigating myself, it seems to me that if the old owner of the IP offered vpn service and apparently all his clients try to connect.
-
@steveits said in Firewall UDP ? Attack !! Or Normal ?:
can they block the traffic?
I am more interested in the case of nslookup
I did the same process with the other ip of my service of /29 and there are only 2 ip of this that show this behavior when I do nslookup
I am sure that if you solve this... I should no longer receive this type of traffic and it is much better than canceling my rule, because I am really interested in registering all types of UDP in my wan
-
@silence The incorrect reverse DNS/PTR record isn't going to hurt you though, it is just incorrect. Unless you have a mail server on your LAN, in which case some/many mail servers on the Internet demand the forward and reverse DNS lookups match, in an effort to block spammers.
To log other UDP, you could make a rule above that rule:
block UDP on WAN:33224, do not log
block UDP on WAN, log -
@silence
Yupp
Something seems a bit fishy with the PTR's
$ host 1.2.3.4 4.3.2.1.in-addr.arpa domain name pointer vpn2.med.com.do. $ host 179.51.66.42 42.66.51.179.in-addr.arpa domain name pointer vpn2.med.com.do. $ host vpn2.med.com.do vpn2.med.com.do has address 179.51.66.42Do you own (use) both of these ip's , i mean primary line vs secondary ?
-
@bingo600 said in Firewall UDP ? Attack !! Or Normal ?:
1.2.3.4
This is my real wan ip can you put 1.2.3.4 please? XD
-
@silence said in Firewall UDP ? Attack !! Or Normal ?:
@bingo600 said in Firewall UDP ? Attack !! Or Normal ?:
1.2.3.4
This is my real wan ip can you put 1.2.3.4 please? XD
Done ...
It wasn't me that posted a tonn of those "real" IP's in the pict here
https://forum.netgate.com/post/1028590 -
@bingo600 said in Firewall UDP ? Attack !! Or Normal ?:
It wasn't me that posted a tonn of those "real" IP's in the pict here
lol sorry, So what else can I do?
-
@silence
I would start by getting the DNS reverse pointer that is in error fixed.
Should your "real ip" reverse resolve to that : vpn2.med.com.do name ?
Else contact theALTICE orTRICOM ISP that controls the PA range you have been assigned , to get that fixed.
That might not stop the noise, as PTR's usually aren't used much But it's still an error, if it's not your domain.Edit: have them fix the .200 PTR too.
And see if the noise is gone.
My guess is that it probably isn't ...
The name it resolves to : vpn2.med.com.do
Might indicate that someone might be trying to connect to the IP address (hardcoded) for vpn usage.If that is what is happening , you should ask the ISP for another /29 range.
-
@bingo600 said in Firewall UDP ? Attack !! Or Normal ?:
Should your "real ip" reverse resolve to that : vpn2.med.com.do name ?
here it should show something like reserved-ipwan-200.tricom.net
-
@silence could you please PM me (send me a private message) Click my avatar and start conversation. With what you actual IP is - I would like to look up the ptr for it, and other info I can glean from this IP. Also are you saying this vpn2.med.com.do is suppose to point to your real IP, and its pointing to some other IP..
I did stop for a few beers tonight with buddy - so that might be my problem, but still confused about your traces and what is suppose to point to what from a fqdn or ptr point of view ;)
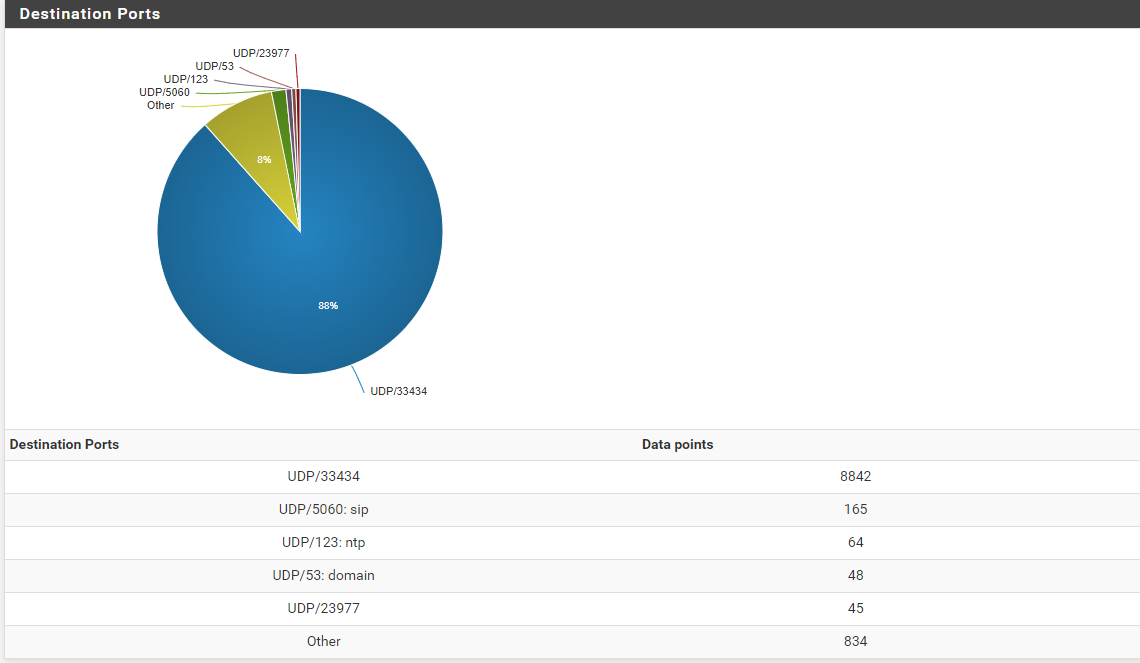
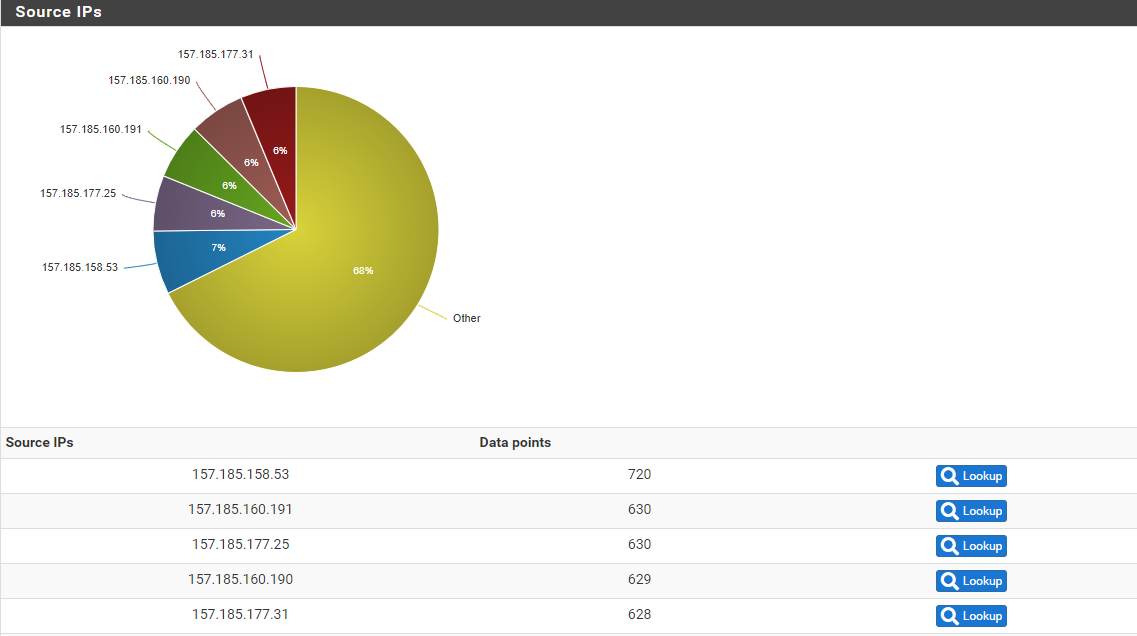
If your seeing 33Mbps to your IP no matter what the port is from just "noise" that seems excessive for sure. But as others have mentioned - when some ISP gives you an IP - it could come with baggage. You don't know what that IP was used for in the past, and you could have other users or companies still trying to hit it, etc. that other port 33224 is that udp or tcp - that is unassigned.. It's not a port actually assigned to anything specific.. So yeah that is odd traffic for sure. But that 200.88 IP is a do (CompañÃa Dominicana de TelÃ
 fonos S. A) IP.. Which at least the region of the world I believe your in.
fonos S. A) IP.. Which at least the region of the world I believe your in. -
@johnpoz said in Firewall UDP ? Attack !! Or Normal ?:
@silence could you please PM me (send me a private message) Click my avatar and start conversation. With what you actual IP is - I would like to look up the ptr for it, and other info I can glean from this IP. Also are you saying this vpn2.med.com.do is suppose to point to your real IP, and its pointing to some other IP..
I did stop for a few beers tonight with buddy - so that might be my problem, but still confused about your traces and what is suppose to point to what from a fqdn or ptr point of view ;)
If your seeing 33Mbps to your IP no matter what the port is from just "noise" that seems excessive for sure. But as others have mentioned - when some ISP gives you an IP - it could come with baggage. You don't know what that IP was used for in the past, and you could have other users or companies still trying to hit it, etc. that other port 33224 is that udp or tcp - that is unassigned.. It's not a port actually assigned to anything specific.. So yeah that is odd traffic for sure. But that 200.88 IP is a do (CompañÃa Dominicana de TelÃ
 fonos S. A) IP.. Which at least the region of the world I believe your in.
fonos S. A) IP.. Which at least the region of the world I believe your in.Done.
-
@silence I do not see how the PTR would be cause of the traffic. What seems likely is they use to have your old IP.. They changed it at some point, but never got the PTR removed..
But they still have something pointing to this old IP (now your IP) vs using the fqdn, if they used the fqdn they would point to what that forward points too
;; ANSWER SECTION:
vpn2.med.com.do. 3150 IN A 179.51.66.42Its prob a good thing that the PTR was not updated, because it gives you a clue to why the traffic is still being sent to your IP.
I would contact the domain owners for med.com.do - they might be able to help get their customers/clients/whoever might be pointing to that old IP (now your ip).
-
@johnpoz said in Firewall UDP ? Attack !! Or Normal ?:
I would contact the domain owners for med.com.do
Done.
-
@silence Or could be when the ISP was changing the PTRs on the IP they F'd it up and put it on yours vs where it was suppose to go..
And this med.com.do never had anything to ever with your IP..
But will be interesting if you hear from them.. Let us know..
-
@johnpoz said in Firewall UDP ? Attack !! Or Normal ?:
Or could be when the ISP was changing the PTRs on the IP they F'd it up and put it on yours vs where it was suppose to go..
And this med.com.do never had anything to ever with your IP..
But will be interesting if you hear from them.. Let us know..Yes, I am trying to get in contact with the owner of med.com.do and with my isp, I will keep this thread informed, because whatever this is it does cause a problem.
-
@silence I do show the current PTR for where that vpn2 fqdn points to be set..
;; QUESTION SECTION:
;42.66.51.179.in-addr.arpa. IN PTR;; ANSWER SECTION:
42.66.51.179.in-addr.arpa. 38400 IN PTR vpn2.med.com.do. -
@silence said in Firewall UDP ? Attack !! Or Normal ?:
@johnpoz said in Firewall UDP ? Attack !! Or Normal ?:
Or could be when the ISP was changing the PTRs on the IP they F'd it up and put it on yours vs where it was suppose to go..
And this med.com.do never had anything to ever with your IP..
But will be interesting if you hear from them.. Let us know..Yes, I am trying to get in contact with the owner of med.com.do and with my isp, I will keep this thread informed, because whatever this is it does cause a problem.
I did a "Who Is" on that domain and it reports them as a banking and finance operation in Santo Domingo, Dominican Republic. Perhaps they changed ISPs or IPs, and still have a misconfigured device trying to establish a site-to-site VPN or something ?? Or perhaps it's a way for their customers to connect with them and someone didn't get the word on a new IP.
-
@bmeeks said in Firewall UDP ? Attack !! Or Normal ?:
them and someone didn't get the word on a new IP.
Yeah you would think this - but clearly that would not be working, so you would think someone would notice something not working ;)
-
@johnpoz said in Firewall UDP ? Attack !! Or Normal ?:
so you would think someone would notice something not working ;)
I keep aiming for an attack, because really, how is it possible for someone to keep trying the same port every day and realize they don't get a response but still continue... unless they want to do it on purpose?