No action on LAN
-
@dhenzler So, now on to your rules that you posted pictures of above. You DO NOT need to add any rules to the LAN interface. If you notice in the screenshot, the rules on LAN, numbers 4-7, have ZERO traffic in them. That's shown clearly in the STATES column, right next to the green check marks. So, that simply means that they are NOT triggering. Your first LAN to any rule, number 2 is catching all the traffic. On a factory reset or defauly installation of pfsense, the allow LAN to any rule is automatically created to allow ANY host on your LAN network to instantly get internet access and access to any additional subnets you create on your firewall. You typically don't need to create anything here on this interface.
DO NOT add any WAN rules for now, get a default factory refresh going, then you can mess around with that stuff. You typically only add WAN rules when you are using services inside your network that you want to expose to the internet. You have to be careful with this interface, and NOT open it up too much to the internet, really really bad stuff lives out there. You don't want that getting into your firewall or into your internal network(s).
-
@akuma1x yeah, I think that's part of the issue here is that @dhenzler might not realize that 100% of the traffic from the LAN going anywhere is approved by the "Default Allow" rule on that interface -- outside ports are only opened to let OUTSIDE traffic in. And as noted earlier outside traffic can come from any port but HTTP/HTTPS traffic will come TO (destination) port 80 or 443. This isn't going to bless inside traffic going out but let anyone on the internet hit https://WAN_IP/ or http://WAN_IP/ without restriction.
-
@akuma1x
It's possible that the Modem is balking at the use of a second port. Although I connected my laptop and set IP & gateway addresses and it worked concurrently with the house network.I HAVE A STATIC IP... no DHCP on the WAN is possible.
Will take your advice, and reconfigure the system once again. I can use the LAN off of the house network for WAN address, and can assign yet another 192.168.1.1 for the LAN.
I use 1.1.1.1 & 1.0.0.1 for DNS... it's faster than Google.
I'll clear all of the rules, but would still like to know how to set specific port rules... Port setting on Source or Destination... or both...
It's supposed to Rain Thursday... good day to spend futzing around with the firewall.
Many thanks to all who have come forward with comments and suggestions. I'm not totally stupid, only untrained. Been a Telecom Engineer for half of my career. But whoever said I was not too good with Firewalls hit the nail on the head. No experience except the Cisco RV-130
Will play as time permits.
-
@dhenzler said in No action on LAN:
Will take your advice, and reconfigure the system once again. I can use the LAN off of the house network for WAN address, and can assign yet another 192.168.1.1 for the LAN.
Be careful with that... you can not have 2 different interfaces using the same IP address space. You say "yet another" and it sounds like you've already got an interface using that 192.168.1.X network. For this exercise, set your LAN network to something like 192.168.8.X or 192.168.9.X, that way, you won't conflict with your WAN port, if it's getting a 192.168.X.X address from your ISP modem/router.
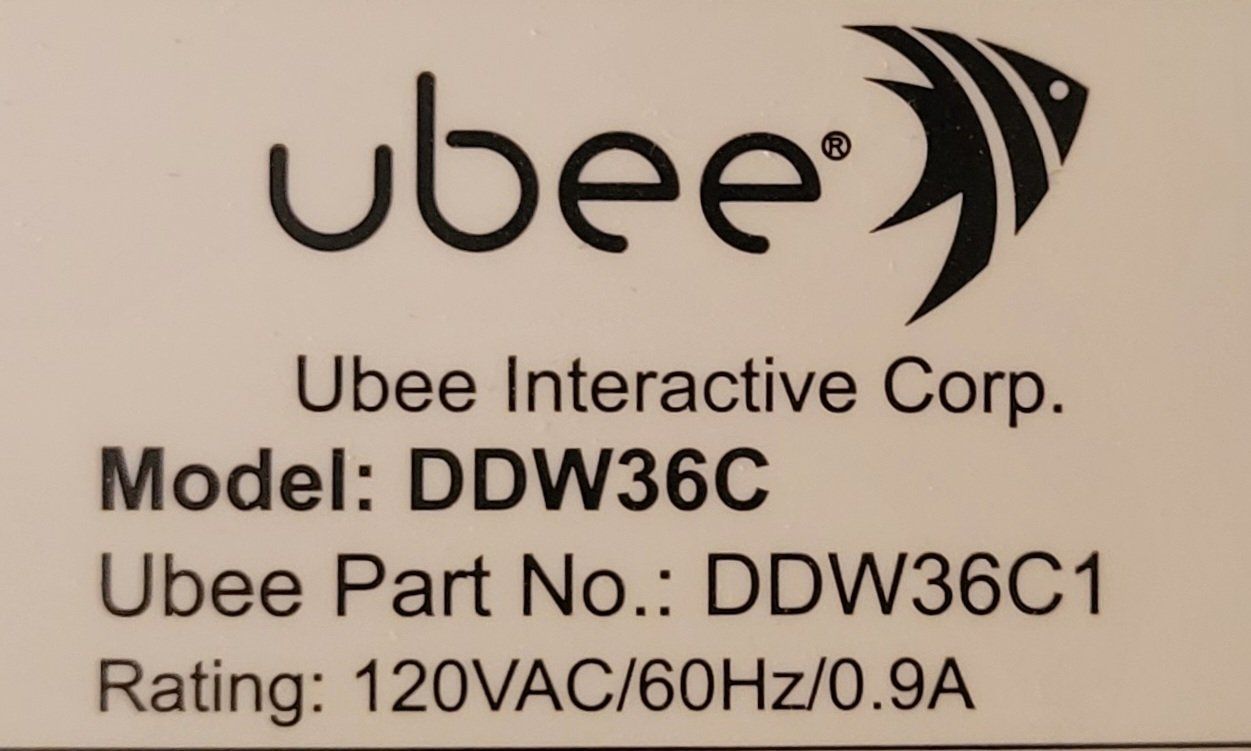
By the way, let's get that question out of the way... what is your ISP modem/router, make and model?
-
@akuma1x
I may be slow, but not stupid !
The LAN address is the same, but totally isolated from the house LAN. Just a CAT5 from pfSense to a computer.I considered that the modem may balk at another device using the same WAN address. However it was tested by connecting my laptop and using the SAME WAN address and Gateway.... worked fine. House network still alive, laptop alive...
Maybe that is insufficient ?
I'll get the modem make & model in a bit...
-
-
@akuma1x
WAN address is 24.172.?.? subnet mask 30 (255.255.255.252)
LAN address is 192.168.?.? subnet mask 24
pfSense is NOT connected to my home network at all.Home network uses the same address ranges. But may as well be on the moon.
I only have one computer connected to the pfSense LAN. It's set for DHCP and connects to the gui configurator.
The modem is in Bridging Mode as the ISP says this is the ONLY way they provide a STATIC IP.
So the connection to the modem is always STATIC. Never DHCP.
-
This post is deleted! -
This post is deleted! -
@akuma1x
Reboot ISP Modem is something I overlooked, but agree it's likely the problem.Well pfSense works well with the default settings and the new IP's assigned. Next will be a late night test... removing the Cisco, Putting pfSense in and rebooting the ISP Modem. See if we have JOY!
If so I imagine I can set up the required Port Forwarding and be on the air..
Thanks again EVERYONE... for the great encouragement and assistance.This was my first time doing Firewall... it's definitely tricky stuff.
-
I successfully migrated my pfSense over to the Cable Modem and my regular LAN IP. However I did have to reboot twice to get operational. I will reconfigure my rack and put it in use in a few days.
The Ubee modem DID need to be rebooted. I have NOT tried hooking up to an unused port now that it's working. Read the manual and apparently even in bridging mode, the extra ports can be active, however they are assigned a different IP, thus unlikely they would get to the Internet.
It's been REAL guys, and I believe much work is ahead of my tweaking the settings to minimize the complaints seen in the log.
-
@dhenzler said in No action on LAN:
The Ubee modem DID need to be rebooted. I have NOT tried hooking up to an unused port now that it's working.
If a single LAN port on the ISP modem works, you should not need to use any of the other ones. Only reason would be to test stuff, off of the pfsense network.
-
@akuma1x
I may try it once more, but only to prove that it doesn't work for the firewall. Funny thing it works for the laptop...I'm anxious to get the Port Forwarding set up for my servers. I have a couple surveillance camera systems and put the video out on the Internet for my remote viewing pleasure. I also built some Reverse Proxy servers to provide SSL access to Emby and other server stuff that I don't want to have man in the middle attacks on. Plus my web servers.
Everything is Virtualized so even if I get hacked I can be back alive in a matter of minutes. One hacker got in a few years ago, and I replaced the virtual machine, and he never came back. Didn't even change the password. I think they realized it was fruitless to try again.The pfSense system should provide a much safer environment. I'll be asking questions here and there when the issues arise.
Thanks again
Dave -
@dhenzler Rebooting between all tests?