Ping to DMZ works without a rule
-
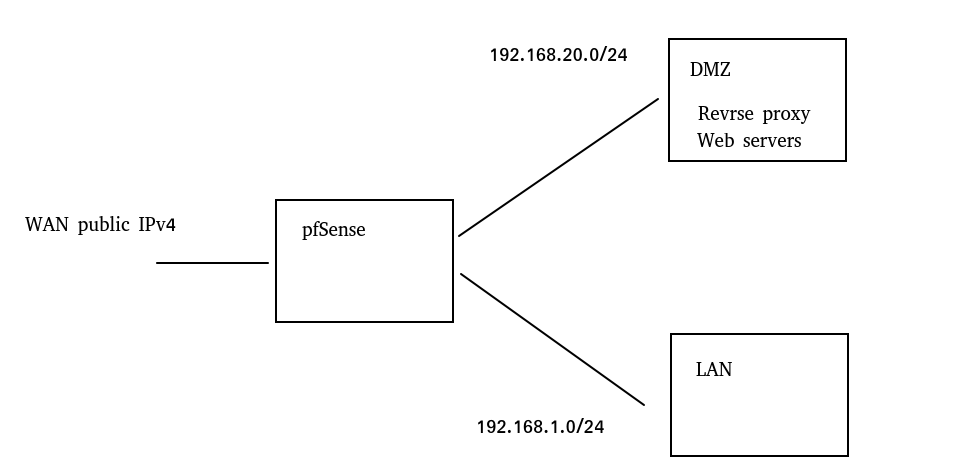
I created a new DMZ network.
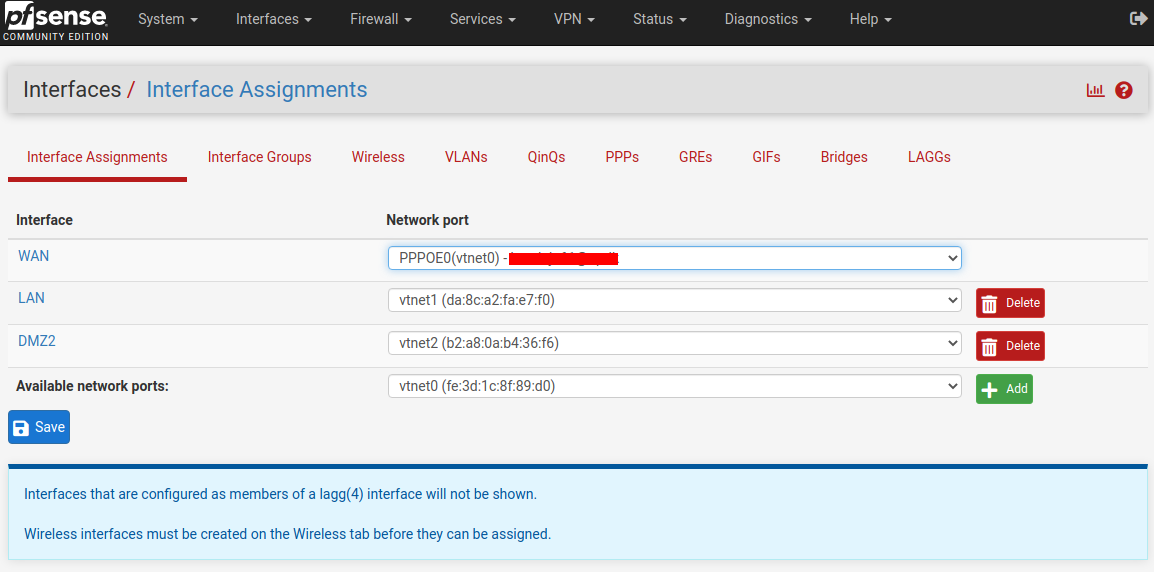
LAN: 192.168.1.0/24 DMZ: 192.168.20.0/24If I create a new network interface, then everything from and to should be disabled by default. In DMZ I created LXC debian 11 with IP address 192.168.20.12. There are no rules in DMZ.
If I ping from LAN (192.168.1.2) to a server in DMZ (192.168.20.12), it works!ping 192.168.20.12 PING 192.168.20.12 (192.168.20.12) 56(84) bytes of data. 64 bytes from 192.168.20.12: icmp_seq=1 ttl=63 time=1.28 ms 64 bytes from 192.168.20.12: icmp_seq=2 ttl=63 time=1.37 ms 64 bytes from 192.168.20.12: icmp_seq=3 ttl=63 time=1.23 ms 64 bytes from 192.168.20.12: icmp_seq=4 ttl=63 time=1.39 msIf I ping from 192.168.20.12 to 192.168.1.2, then it doesn't work.
How is it possible that I see a DMZ from the LAN? -
@gusto
Firewalls rule have to be defined on the incoming interface. So probably you have a rule on LAN which allow pings.If you really want to block any access to the DMZ despite pass rules on other interfaces, you can add a floating block rule with Quick checked for direction out to the DMZ interface.
-
@viragomann
do you mean this rule marked with a green border?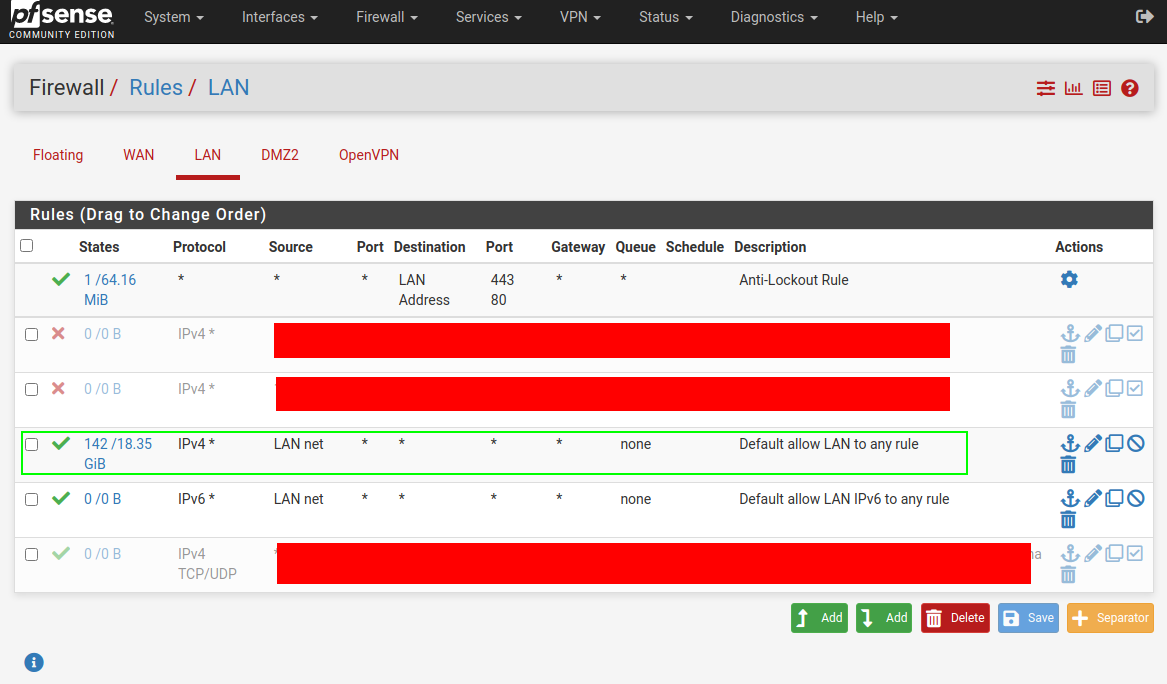
-
@gusto
Yes. It allows any access from LAN subnet to any IP and hence as well to the DMZ devices. -
I would like to ask more questions.
As I wrote in the first post, I haveLAN: 192.168.1.0/24 DMZ: 192.168.20.0/24Webconfigurator works on 192.168.1.1 but also on 192.168.20.1
Is this okay? -
@gusto said in Ping to DMZ works without a rule:
Webconfigurator works on 192.168.1.1 but also on 192.168.20.1
Is it - that would be for you decide.. If you don't want to be able to access 20.1 from lan, you could set a rule to block it. Same goes for if you don't want to access firewall gui no matter what IP you could set a rule to block that on your dmz interface, etc.
Its the same gui, so blocking it from lan would seem waste of time, since your allowing to 1.1, and there is a antilock out rule to allow anything from the lan to acess the lan IP on gui and ssh ports.
But if you don't want to allow clients from your dmz to access the gui, etc. then just create the rule on the dmz interface to block it.
-
@johnpoz
It's very strange
I created a DMZ network to protect the LAN.
I place servers in the DMZ that can be potentially compromised from the WAN, and for some reason I find that the DMZ also has the most vulnerable pfSense server.
I don't like that at all!
How is it possible that pfSense sits on two different IP addresses? -
@gusto said in Ping to DMZ works without a rule:
How is it possible that pfSense sits on two different IP addresses?
Its a router - its going to have multiple IP addresses. The gui listens on all its IP addresses.
As to dmz rules - it had zero when you created it. All deny which is default, so if you created a rule that allows access to whatever on it. That is on you.
The default on lan is any any - so yes it would be able to access any IP on pfsense, on the internet, in the dmz, etc..
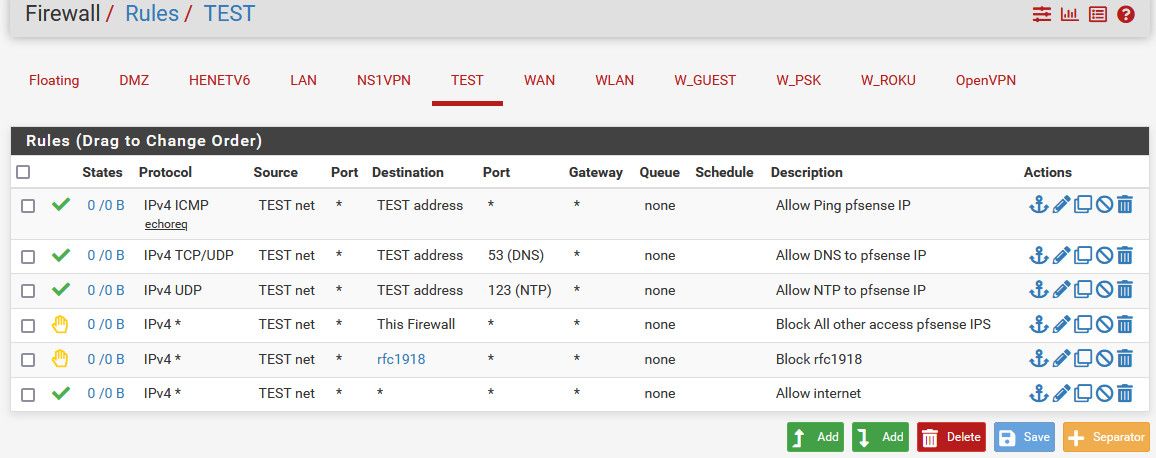
I would suggest using the "this firewall" built in alias for when you don't want a network pfsense attached to be able access anything on the firewall.
example: here set of rules that allows ping, dns and ntp to pfsense IP address on this network. Blocks all other access to any of my other networks, but allows internet.
-
@johnpoz
This is my situation
- I want to ping everything from the DMZ network (rule 1).
- I want to open these ports 80, 433, 53 from the DMZ network (rule 2)
- I want to deny LAN access from the DMZ (rule 3).
- There must be access to the DMZ from the LAN (This rule does not need to be set.)
Is this proposed solution for web servers in DMZ okay?
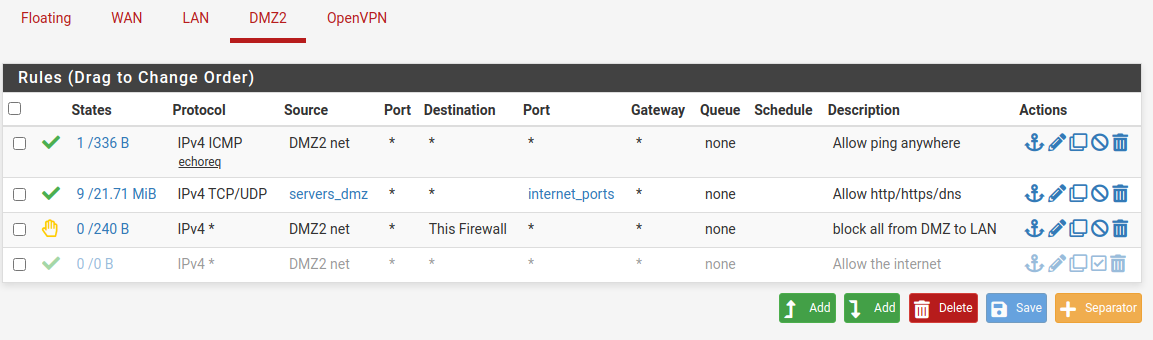
It seems that everything works even if the last rule is inactive / active.
Is it okay from a security standpoint? -
@gusto it would be up to you if you don't want that last rule - because your allowing internet access via your second tcp/udp rule - as long as your pointing them to some external dns. and only want http and https access then yeah that should work without that last rule.