How to access nextcloud from another VLAN in a HAProxy+DNS Resolver setup
-
@runevn Do you have your nextcloud config file under trusted domains, the specified domain name or just the ip?
-
@flat4 Thanks for your reply. I have added both my IP and domain name.
-
@runevn said in How to access nextcloud from another VLAN in a HAProxy+DNS Resolver setup:
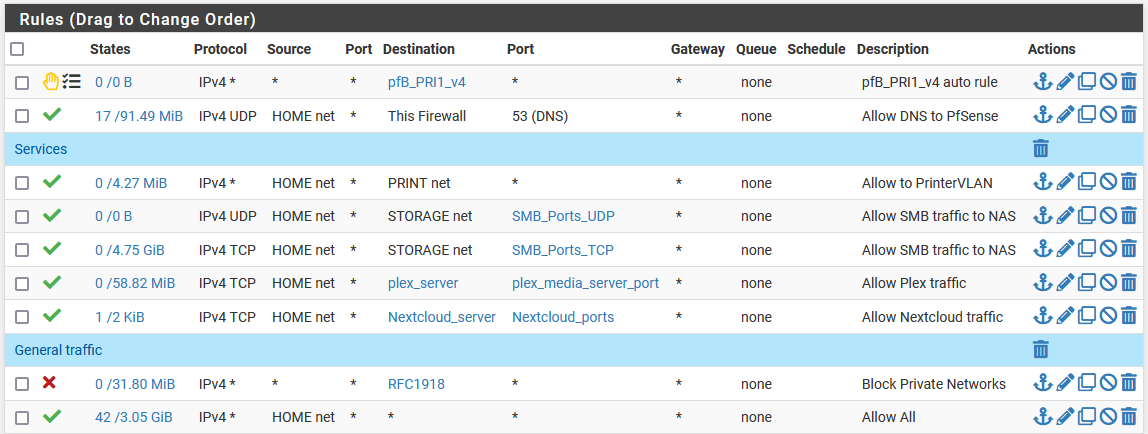
I have set a firewall rule allowing traffic from my HOME VLAN to the nextcloud VM (on Server VLAN) on port 80 and 443 (tcp).
That's the wrong way. Since you're running HAproxy with SSL offloading, simply allow access to the IP the proxy is listening on, presumably WAN IP.
If you have the public IP on the WAN of pfSense there is nothing more to do at all in the DNS. If it's a private WAN behind a router, add a host override to the Resolver and point it to the pfSense WAN IP.
-
@viragomann Thanks for your reply. Nextcloud is only being accessed on my LAN. If I set the nextcloud IP to my pfSense LAN IP it works.
However, that will allow all traffic from my HOME VLAN to access all the services on port 80/443 tcp using the SSL-offloading?
-
@runevn said in How to access nextcloud from another VLAN in a HAProxy+DNS Resolver setup:
Nextcloud is only being accessed on my LAN.
So I'm wondering what's the purpose of HAproxy in this setup. Though that changes the situation and would be worth to mention.
However, that will allow all traffic from my HOME VLAN to access all the services on port 80/443 tcp using the SSL-offloading?
That's correct and usually that doesn't matter, since the HAproxy interface is exposed to the internet in normal circumstances.
Whenever I try to access nextcloud.mydomain.com I can't access nextcloud but if I use the IP I can access nextcloud.
So did you add a host override pointing to the server IP?
-
So I'm wondering what's the purpose of HAproxy in this setup. Though that changes the situation and would be worth to mention.
The purpose is to have HAProxy providing let's encrypt wildcard SSL certificates to webinterfaces for my services, even though it is all on the LAN
So did you add a host override pointing to the server IP?
Yes, but because I'm running HAProxy on my pfSense box the Host overwrite must be the pfSense box it self (192.168.1.1) and not the server IP.
If I change the host overwrite to the server IP it works but then HAProxy will not provide the SSL-offloading.
-
@runevn
So you have to point the Nextcloud host override to pfSense.
If you want to restrict access to certain IPs, you can add an additional virtual IP to pfSense and point Nextcloud to this. Then add a frontend in HAproxy using this IP, but the same SSL cert.HAproxy must not run in transparent mode in your setup! This would end up in asymmetric routing issues.
-
@viragomann said in How to access nextcloud from another VLAN in a HAProxy+DNS Resolver setup:
Thanks for your reply. Just some further questions just to be clear:
So you have to point the Nextcloud host override to pfSense.
At the moment my current Nextcloud host overwrite is set to pfsense it self (192.168.1.1). Is that correct?
If you want to restrict access to certain IPs, you can add an additional virtual IP to pfSense and point Nextcloud to this. Then add a frontend in HAproxy using this IP, but the same SSL cert.
Okay, just so I get it right... When I add a Vitrual IP for Nextcloud should it be within the same VLAN as the original IP? And what do you mean by "point Nextcloud to this"? Is it within the configuration file of NC?
-
@runevn said in How to access nextcloud from another VLAN in a HAProxy+DNS Resolver setup:
At the moment my current Nextcloud host overwrite is set to pfsense it self (192.168.1.1). Is that correct?
It could be any IP of pfSense. The only requirement is that HAproxy is listening on it.
When I add a Vitrual IP for Nextcloud should it be within the same VLAN as the original IP?
The same answer. Could be on any interface, but yes for clarity, I would add it to the home VLAN, since you want to access it from devices of this network segment.
And what do you mean by "point Nextcloud to this"?
I meant to host override with this.
-
This post is deleted!