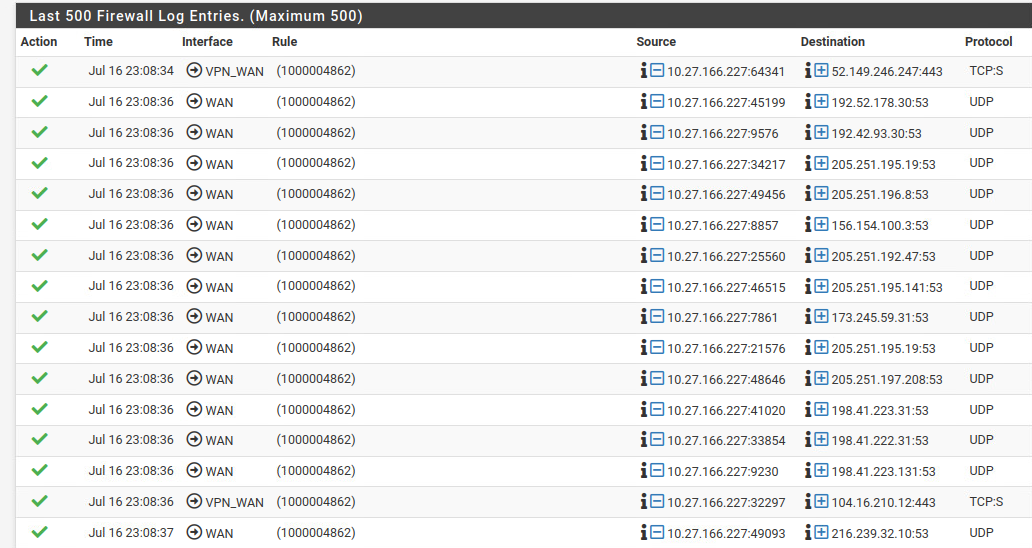
Traffic passing between WANs when blocked
-
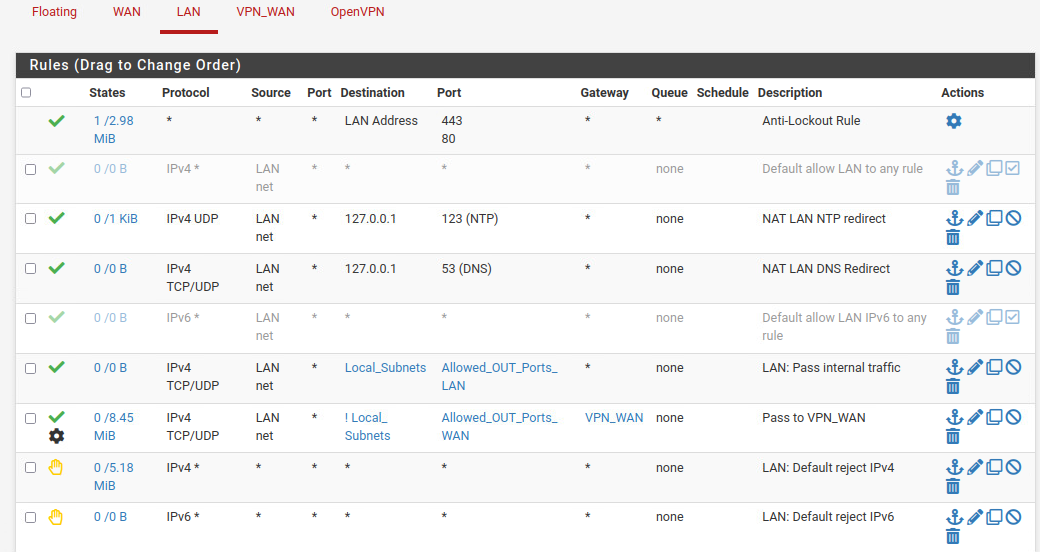
Simple setup, on this instance of PFsense I am only using is as a VPN server with openVPN with only one client on the LAN. The default WAN gateway is connected to the primary firewall and only 443 and 1194 are allowed to PF. openVPN works and everything looks fine except for these firewall passes.
I have DNS resolver turned on with PF's only DNS server pointed to the VPN internal DNS services. I have rules in place so that any DNS request is reflected back to localhost (DNS resolver) which has tested to be working as its setup as far as all my manual DNS requests/tests show. All exit traffic is also routed through the VPN_WAN as intended.
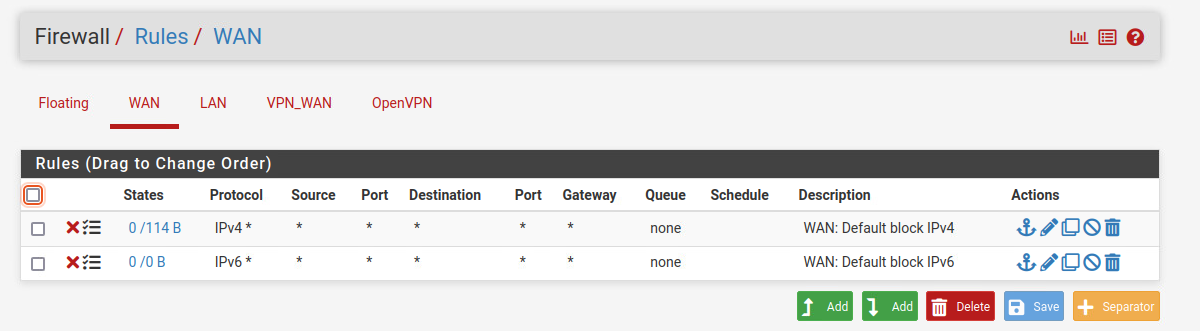
Default blocks for IPv4 and IPv6 are in place on both WAN and VPN_WAN and everything else should be blocked. Only traffic routed outbound on WAN is localhost. The only allow rules on LAN are for the internal NTP and DNS at localhost, LAN subnet's (LAN DHCP range) ports (Allowed_OUT_Ports_LAN) 53,123,80,443. and Inverse LAN subnet's ports allowed out to VPN_WAN - Allowed_OUT_Ports_WAN (80,443,8080)
The source IP address shown in the firewall log is the one internally given to me by the VPN service and is the address of VPN_WAN. Not sure how this traffic is being allowed to pass through to WAN on the DNS port from VPN_WAN's IP
-
@musicims
Seems to be a floating rule. Is there any on the floating tab?You can enable displaying of the rule names by editing Status > System Logs > Settings > Where to show rule descriptions or search the ID in /tmp/rules.debug to find out which rule is responsible.
-
Thank you for that! I had descriptions on, not sure why they are coming up with numbers. I did find it in the .debug though in #loopback on line 122 but honestly not sure where that rule exists from. I do not have any floating rules
115 # loopback 116 pass in on sloopback inet all ridentifier 1000004761 label "pass IPv4 loopback" 117 pass out on $loopback inet all ridentifier 1000004762 label "pass IPv4 loopback" 118 # let out anything from the firewall host itself and decrypted IPsec traffic 119 pass out inet all keep state allow-opts ridentifier 1000004763 label "let out anything IPV4 from firewall host itself" 120 121 pass out route-to ( vmXO 10.1.1.1 ) from 10.1.1.249 to ! 10.1.1.0/24 ridentifier 1000004861 keep state allow-opts label "let out anything from firewall host itself" 122 pass out route-to ( ovpnc1 10.27.166.1 ) from 10.27.166.227 to !10.27.166.0/24 ridentifier 1000004862 keep state allow-opts label "let out anything from firewall host itself" 123 # make sure the user cannot lock himself out of the webConfigurator or SSH 124 pass in quick on vmx1 proto top from any to (vmx1) port { 443 80 } ridentifier 10001 keep state label "anti-lockout rule" 125 126 # User-defined rules follow 127 128 anchor "userrules/*" 129 block in log quick on SWAN reply-to (vmXO 10.1.1.1) inet from any to any ridentifier 1657922927 label "USER_RULE: WAN: Default block IPv4" 130 block in log quick on $WAN inet6 from any to any ridentifier 1657922951 label "USER_RULE: WAN: Default block IPV6" 131 pass in quick on $LAN inet proto udp from 192.168.168.0/24 to 127.0.0.1 port 123 ridentifier 1658020437 keep state label "USER_RULE: NAT LAN NTP redirect" 132 pass in quick on $LAN inet proto { top udp } from 192.168.168.0/24 to 127.0.0.1 port 53 ridentifier 1658020510 keep state label "USER_RULE: NAT LAN DNS Redirect" 133 pass in quick on $LAN inet proto { top udp) from 192.168.168.0/24 to $Local Subnets port $Allowed_OUT_Ports_LAN ridentifier 1658023837 keep state label "USER_RULE: LAN: Pass internal traffic" 134 # rule Pass to VPN_WAN disabled because gateway VPN_WAN is down label "USER_RULE: Pass to VPN_WAN" 135 block return in quick on $LAN inet from any to any ridentifier 1657923637 label "USER_RULE: LAN: Default reject IPv4" 136 block return in quick on $LAN inet6 from any to any ridentifier 1657923662 label "USER RULE: LAN: Default reject IPv6" -
@musicims
So this might be the default pass rule.
By default, logging of that isn't enabled. Status > System Logs > Settings > Log packets matched from the default pass rules put in the rulesetThe source IP address shown in the firewall log is the one internally given to me by the VPN service and is the address of VPN_WAN.
This is the VPN interface IP?
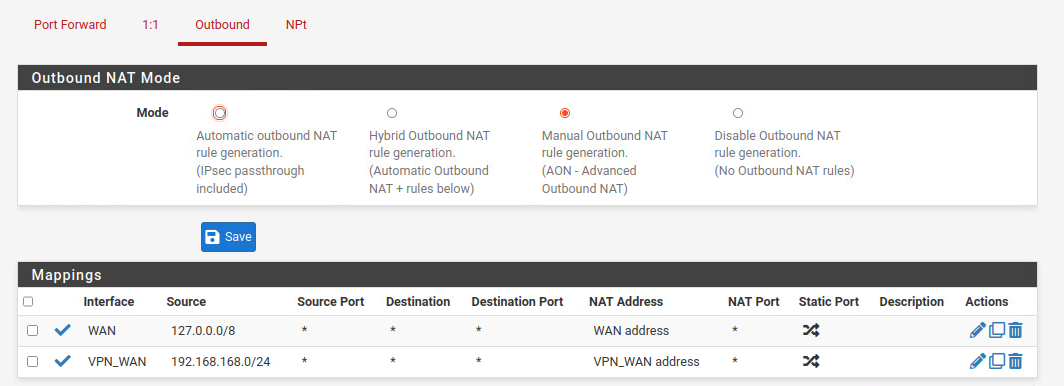
It's strange that it is used for traffic going out on VPN_WAN and WAN as well. Messed with outbound NAT?Not sure how this traffic is being allowed to pass through to WAN on the DNS port from VPN_WAN's IP
This rule cannot be disabled, and that wouldn't be useful at all in most cases. However, you can overrule it by an floating rule with Quick as far as I know.
-
Floating rule worked perfectly on quick. Thank you!