ACME/DuckDNS - SSL works, but only to DuckDNS hostname, not internal ip address
-
I have pfsense 2.6.0 -Release with ACME installed, and use DuckDNS. I have created an SSL cert and use it on the webgui -- let's call that host dave.duckdns.org. In System:Advanced:Admin Access I have added dave.duckdns.org to Alternate Hostnames. When I point my inside-the-firewall browser at https://dave.duckdns.org it all renders nicely and works with SSL. In reality the LAN ip address for the pfsense is 10.3.2.1, and if I try to browse to https://10.3.2.1 I get a not-secure HTTPS warning that the certificate is not valid.
What do I need to do such that internal network machines can browse to https://10.3.2.1 and negotiate a valid SSL session?
-
@jupiters_spot said in ACME/DuckDNS - SSL works, but only to DuckDNS hostname, not internal ip address:
What do I need to do such that internal network machines can browse to https://10.3.2.1 and negotiate a valid SSL session?
You need to know why a certificate is considered 'valid' by your browser

"Start date" and "end date" are important.
But also the "host name", as that is what it is all about. Inspect your certificate, and you will find it.
If you want "10.3.2.1" to be accepted by your browser, you have to add "10.3.2.1" to the so called SAN ( trusted host names) to the list.The thing is : Letsencrypt won't let you add IP address like host names.
When pfSense start, local DNS works.
The very first thing the local DNS knows about is this :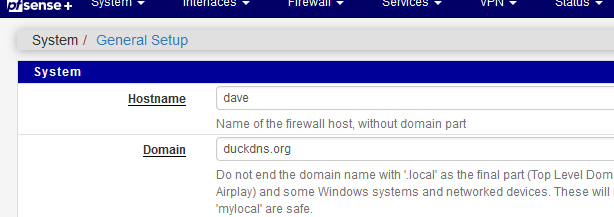
so when your browser asks : who is dave.duckdns.org, then the answer comes back right away : it's me : 10.3.2.1 - so now the browser knows where to connect to.
If pfSense (and DNS) doesn't work : no need to connect to 10.3.2.1 or dave.duckdns.org, both won't reply ^^Btw : and don't try to add "10.3.2.1" as it is RFC1918 : so how could the Letsencrypt verification server connect to it ? RFC1918 isn't routed over the Internet.
And adding your WAN IP is not good neither.
Connecting to the GUI over WAN is considered a security risk.
The WAN can change (often) and this makes the certificate useless.
Etc. -
Thank you for the explanation.
I don't expose the GUI to the WAN, and frankly I have little need for SSL to my pfSense beyond getting rid of the annoying "Invalid SSL Cert" interstitial page when logging in from an internal machine. Using "dave.duckdns.org" internally works nicely for this, solving my problem.