3.1.0_6 UPDATE
-
@jdeloach said in 3.1.0_6 UPDATE:
@cloudified
Did you manually create firewall rules for those aliases or did it create them automatically? Check your firewall rules and see if those aliases still appear in your firewall rules, if they do, delete those firewall rules.
I've seen cases where I created rules with aliases in pfBlocker but didn't delete them and they would still show up in that table, like you are showing.
I think you meant to reply to @turker.
-
@cloudified
Yeah, I just saw that and edited my post. Thanks! -
-
@cloudified said in 3.1.0_6 UPDATE:
@turker are you getting any table memory errors? That might indicate that you need to increase your Firewall Maximum Table Entries in the System / Advanced / Firewall & NAT section. I had to increase mine from 400,000 to 1,000,000 to account for all of the pfBlocker lists I have configured.
One other comment, there has been a lot of discussion in numerous posts on this forum as to what value, Firewall Maximum Table Entries should be. They are several cases where folks have used anywhere from 400,000 to 10,000,000. I think most consider 2,000,000 to be a good number to use but it seems to vary depending on each users system, memory and which/how many lists folks choose to use. I just checked my system and I have 4,000,000, why, I don't know, it works so I don't plan to change it.
As far as the default value, that bug/error has been around since day one with this package, even before BBcan177, took over as the maintainer, if remember correctly. I think the pfSense/Netgate/maintainer GODS think it is a low priority fix and have ignored it all these years.
-
@cloudified said in 3.1.0_6 UPDATE:
@turker are you getting any table memory errors?
No. -
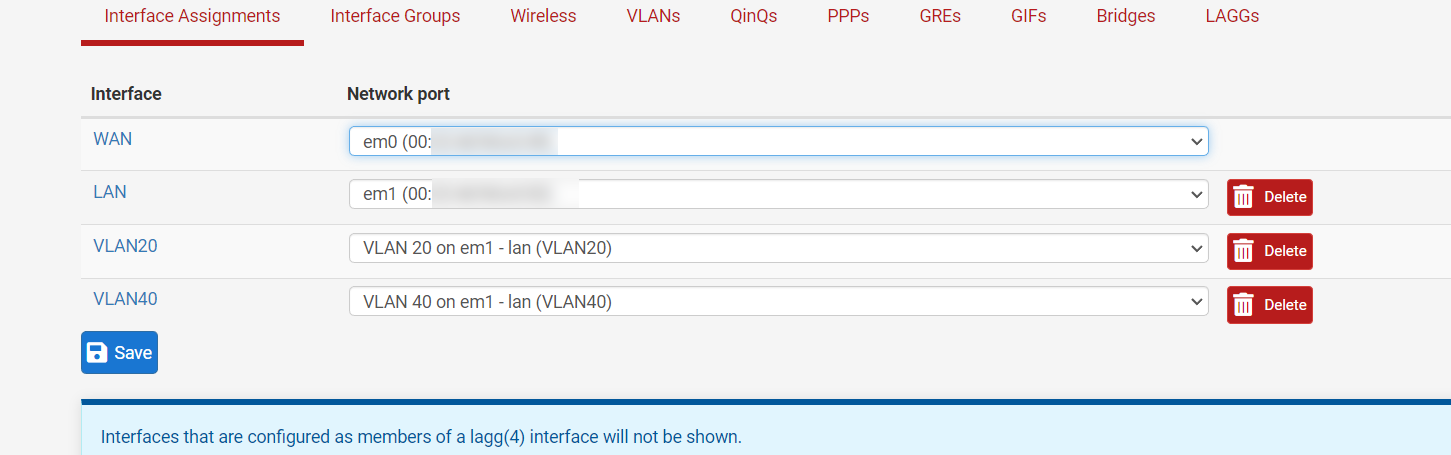
The problem may be caused by me.
Rule 5 seems to be assigned to the interface but i have 4 interfaces. I deleted one.
Looks like it was assigned to the deleted interface.
-
@jdeloach said in 3.1.0_6 UPDATE:
@cloudified said in 3.1.0_6 UPDATE:
@turker are you getting any table memory errors? That might indicate that you need to increase your Firewall Maximum Table Entries in the System / Advanced / Firewall & NAT section. I had to increase mine from 400,000 to 1,000,000 to account for all of the pfBlocker lists I have configured.
One other comment, there has been a lot of discussion in numerous posts on this forum as to what value, Firewall Maximum Table Entries should be. They are several cases where folks have used anywhere from 400,000 to 10,000,000. I think most consider 2,000,000 to be a good number to use but it seems to vary depending on each users system, memory and which/how many lists folks choose to use. I just checked my system and I have 4,000,000, why, I don't know, it works so I don't plan to change it.
As far as the default value, that bug/error has been around since day one with this package, even before BBcan177, took over as the maintainer, if remember correctly. I think the pfSense/Netgate/maintainer GODS think it is a low priority fix and have ignored it all these years.
In my case I was getting the error because the default size of 400,000 on my 6100 was not enough for the lists I have configured. The error went away after increasing it to 1,000,000.
-
@cloudified said in 3.1.0_6 UPDATE:
the default size of 400,000 on my 6100 was not enough for the lists I have configured
A few years ago I documented that BBcan177 posted to double the default, with a minimum of 2 million. It of course depends on the number of entries used and the RAM installed. In theory someone could just use one small list and not need very many at all. Others "block the world" and use quite a lot.
It would be nice if the package checked that setting upon install and showed a warning somewhere.
@jdeloach said in 3.1.0_6 UPDATE:
As far as the default value, that bug/error has been around since day one with this package
The Firewall Maximum Table Entries setting is a pfSense setting...it has nothing to do with the pfBlocker package. Other than, pfB creates table entries. I don't recall when the bug showed up but I noticed it a year or two ago, whenever I made the report. If you think it's been longer I'll just believe you. :) I didn't have any old routers to check...we keep our clients pretty current.
-
@steveits Totally agree. It was be really nice if pfBlocker checked your current table size setting when a list update goes above the threshold.
-
@steveits said in 3.1.0_6 UPDATE:
@cloudified said in 3.1.0_6 UPDATE:
It would be nice if the package checked that setting upon install and showed a warning somewhere.
@jdeloach said in 3.1.0_6 UPDATE:
As far as the default value, that bug/error has been around since day one ....
The Firewall Maximum Table Entries setting is a pfSense setting...it has nothing to do with the pfBlocker package.
You are correct, too damn many pf...... in pfSense/packages.
-
@keyser said in 3.1.0_6 UPDATE:
Rumors have it that it is Netgate that maintains this package now
FYI Netgate has a list: https://www.netgate.com/supported-pfsense-plus-packages
-
Note that pfBlockerNG and pfBlockerNG-devel are NOT the same package and are on different development tracks.
pfBlockerNG-devel will eventually replace pfBlockerNG but for now they're separate.
-
@keyser said in 3.1.0_6 UPDATE:
I wonder whats going on here… Rumors have it that it is Netgate that maintains this package now and @BBcan177 is no longer on board.
The thing about rumors... is that they're difficult to prove, or disprove.
TAC doesn't provide support for pfBlockerNG. BBcan is the maintainer. As I understood it BBcan was on paternity leave for the last few months.
What I can tell you is a colleague in TAC wrote a patch for the issue that was effecting logging (IIRC) and I think that's where people are thinking it's now a Netgate product. It was a patch, nothing more.
-
@rcoleman-netgate said in 3.1.0_6 UPDATE:
@keyser said in 3.1.0_6 UPDATE:
I wonder whats going on here… Rumors have it that it is Netgate that maintains this package now and @BBcan177 is no longer on board.
The thing about rumors... is that they're difficult to prove, or disprove.
TAC doesn't provide support for pfBlockerNG. BBcan is the maintainer. As I understood it BBcan was on paternity leave for the last few months.
What I can tell you is a colleague in TAC wrote a patch for the issue that was effecting logging (IIRC) and I think that's where people are thinking it's now a Netgate product. It was a patch, nothing more.
Plus he was very forthcoming about the issue and an upcoming patch and how to fix the issue beforehand...
-
@cloudified Never let a good theory get in the way of reality... :D
-
@bbcan177 Changing subject, "Thousands of GitHub repositories deliver fake PoC exploits with malware" found this on Bleeping Computer, some of the pfBlocker feeds are named in this article.
JMV
-
@jmv43-0 ??? I'm not aware of any IP or DNSBL list downloads from pfBlocker feeds which contain executable scripts. They're just lists of IPs, CIDRs, FQNDs to build lookup tables.
Do you have an example feed which contains a script?
-
https://twitter.com/BleepinComputer/status/1584202031044374528?t=0XBrpP3vz_7XvkMFnW4PcQ&s=19
"By looking closer into some of those cases, the researchers found a plethora of different malware and harmful scripts, ranging from remote access trojans to Cobalt Strike."
"IP address analysis: comparing the PoC's publisher IP to public blocklists"
So basically there are scripts and executables that were found in several Github repositories.
The researchers found that some of those malware IPs were matched in the public IP blocklists.
The best blocklists being hpHosts and Stop Forum Spam.
Tho hpHosts has been closed but I have been trying to get it back some what:
https://twitter.com/BBcan177/status/1582913688058855426?t=abL5y3qyGMikWZgRn7mbnw&s=19
-
And another reason why I resisted to automatically unblock any IPs of any feeds.
-
@bbcan177 Good idea. Making the same change now...