Snort is blocking on some alerts not others
-
I'm having an issue where Snort is blocking some IP addresses but not others with the same alert type or rule. For example,
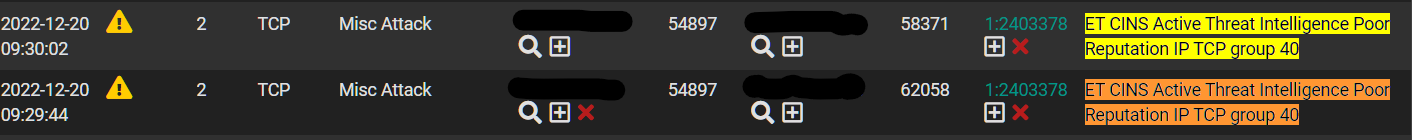
I made sure the offending IP was not in the pass list nor suppress list. I'm using the balanced policy and all snort package defaults. It is strange to me that the same alert type blocks one IP but not others. I just started seeing this a few days ago. For the IP that didn't get blocked on the Snort Alerts page, I checked the Firewall logs and don't see it there, meaning that connection wasn't blocked right? I'm still fairly new to firewall management. I prefer IPs that have poor rep to always be blocked, so in the mean time I've been adding any IP that has a bad rep to the IP List in Snort. There are a lot of them, and I have to check each one on abuseipdb to make sure it isn't a false-positive. -
@gfunk If you wanted to pull it out of Snort and just block them by firewall rule, usually those types of lists are in pfBlocker. I don't see that one offhand though. It has CINS Army and a couple of ET lists.
re: alert/block, is the LAN IP for that line in the suppress list?
-
@steveits I only have Snort set up on my WAN interface. I checked the suppress list for my WAN IP and it is not there. I did notice that my WAN IP never has the red X in Alerts which is normal based on the documentation I've read about Snort automatically allowing any IP associated with the interface Snort is running on.
-
@gfunk Consider running it on LAN. On WAN it will scan all packets even those that will be blocked by the firewall. On LAN you can see the LAN IP of the PC making the connection.
-
@steveits I did in fact have monitoring only enabled on my LAN interface before I started having connectivity issues. While troubleshooting I found that disabling Snort on my LAN interface restored connectivity. I just added my LAN interface to snort and will see what happens. I forgot to mention I also have IP rep blocking enabled, that might have been obvious in my post. Just boggles my mind why Snort wouldn't block an IP that triggers an alert when I have blocking enabled for all Alerts.
Also side question about WAN Categories. I currently have IPS Policy enabled and set to Balanced for both WAN and LAN. Should I not be using that and instead select all rules?
-
@gfunk To maybe clarify, I meant use LAN instead of WAN. I wouldn't run it on both.
Not sure about the policy setting, we have usually used Suricata and I'm not sure I have a Snort handy.
However if you read though recent posts by BMeeks he posts every few weeks about setup. You should be enabling the rules that fit your usage case, e.g. you're running a web server. Extra/unnecessary rules aren't helping and are using CPU and memory. Encrypted traffic like HTTPS can't be scanned.
-
@gfunk I encourage you to read through the pinned posts on https://forum.netgate.com/category/53/ids-ips
Unless you are hosting some services on the WAN its best to enable teh IPS on your LAN.
@gfunk said in Snort is blocking on some alerts not others:
While troubleshooting I found that disabling Snort on my LAN interface restored connectivity.
You more than likely have enabled blocking mode [legacy?] which you shouldnt do right away. You need to discover what is alerting and determine if they are false positives or not.
@gfunk said in Snort is blocking on some alerts not others:
Also side question about WAN Categories. I currently have IPS Policy enabled and set to Balanced for both WAN and LAN. Should I not be using that and instead select all rules?
Please dont do this. Do not enable Snort on the WAN. Unless you hae a permit any/any rule there is no beneift you are getting from having it run on an interfaec that would otherwise drop packets without snort.
I deeply encoruage you to read up on IPS in the forum catoegory i linked above before attempting to turn it on again. You are causing way more connectivity issues for yourself unnecessarily.If IP blocking is what you need, pfBlockerNG does a fantastic job at that.
-
I want to thank you all for the responses and guidance. I read through and followed the pinned beginner's guide for Snort. Figured I'd start from scratch. I have it set up on my LAN interface. One thing I think bmeeks left out was on the Categories page, in addition to selecting the Snort Subscriber IPS Policy, you have to check/enabled the rules themselves. Otherwise alerts will not populate. The only thing I have configured on my firewall for inbound traffic is OpenVPN, no web servers or anything like that. I have a DMZ VLAN for my cable box and FIOS router, which I guess I could add that interface to Snort, just to monitor for now.
Thanks again. I'll keep playing with it and refer back to the pinned posts from time to time.
-
@gfunk said in Snort is blocking on some alerts not others:
DMZ VLAN for my cable box and FIOS router, which I guess I could add that interface to Snort
IIRC Snort and Suricata will see the VLAN packets anyway so no need to add it as a separate interface.
-
@steveits said in Snort is blocking on some alerts not others:
@gfunk said in Snort is blocking on some alerts not others:
DMZ VLAN for my cable box and FIOS router, which I guess I could add that interface to Snort
IIRC Snort and Suricata will see the VLAN packets anyway so no need to add it as a separate interface.
This is correct. Be sure "promiscuous mode" is enabled and just put the instance on the VLAN parent physical interface. This is especially critical when using the Inline IPS Mode mode of operation.