(RESOLVED!!!) WARNING!! Emerging Threats Dshield rule set is now empty inside Snort and on Emerging Threats official website
-
Snort's OpenAppID is NOT seeing decrypted data. It simply analyzes the unencrypted SNI header in certain traffic types to guess at the application. Once encrypted SNI (ESNI) becomes a regular thing, OpenAppID is going to have some issues identifying applications.
And today neither Snort nor Suricata, by default, will see unencrypted SSL traffic on pfSense even when MITM is present with something like HA-Proxy. The network plumbing on FreeBSD by default puts the IDS/IPS immediately after the NIC driver, so all traffic seen there is still encrypted. You would have to utilize multiple NIC ports and set up custom routing outside of the package GUI for either Snort or Suricata in order to have them see the unencrypted traffic available with MITM.
-
@michmoor Noted: My firewall is not a enterprise class system like some PaloAlto's mine is just a home system, my streaming services never skip a beat now with pfSense running :) a smaller system is all I need. We went over so many PaloAlto options during class it can make your head spin they have so many options. I wonder with all the new whitebox software being installed right on the network cards if maybe something like a large Ciena router could also manage security options right on the router itself. Cisco started doing a firewall and router all in some years ago, it was cutting edge at the time to combine them.
-
@bmeeks but what about the sockets inside pfsense software, it lists nothing for snort? Is that separate from the software? I love this stuff it is so impressive what pfsense can do. The packages the firewall software all of it, it's a work of software art.
-
@jonathanlee said in (RESOLVED NEXT RELEASE) WARNING!! Emerging Threats Dshield rule set is now empty inside Snort and on Emerging Threats official website:
@bmeeks but what about the sockets inside pfsense software, it lists nothing for snort? Is that separate from the software?
Totally unrelated and not used by either package. Suricata offers an optional socket connection for control purposes (starting, stopping, reloading rules, etc.), but not for inspection purposes. But that optional control socket is not used on pfSense.
Sockets in the context you seem to be talking about are generally used for inter-process communications where applications swap limited amounts of data or control information with each other.
-
@bmeeks Have no fear Pfsense firewall software teams will always find a way to protect systems, HSM security modules today still need management software just like TPK attestation software. Firewall software teams work diligently to keep systems protected. A couple months ago I thought HTTPS/3 UDP QUIC was invincible and now wireshark can spot it, I even saw someone posted a video where they blocked specific QUIC website traffic. Without direct government protocol approval how can experimental traffic even get around a backbone internet router like a monster Ciena system? I personally think the wildwest days of dotcom are over, because more and more protocols and rules are taking hold, hence government compliance servers now just going to block it out if they want. It truly is mirrored analytics.
-
@bmeeks look at what Russia wants to do with ESNI
https://www.privateinternetaccess.com/blog/russia-wants-to-outlaw-tls-1-3-esni-dns-over-https-and-dns-over-tls/
They are going to force state issued certificates. WOW!!
-
@bmeeks curious are there any development projects to have the IDS sit after the proxy in order to scan packets or would that require a rework within FreeBSD?
-
@michmoor said in (RESOLVED NEXT RELEASE) WARNING!! Emerging Threats Dshield rule set is now empty inside Snort and on Emerging Threats official website:
@bmeeks curious are there any development projects to have the IDS sit after the proxy in order to scan packets or would that require a rework within FreeBSD?
Nothing in progress that I am aware of.
-
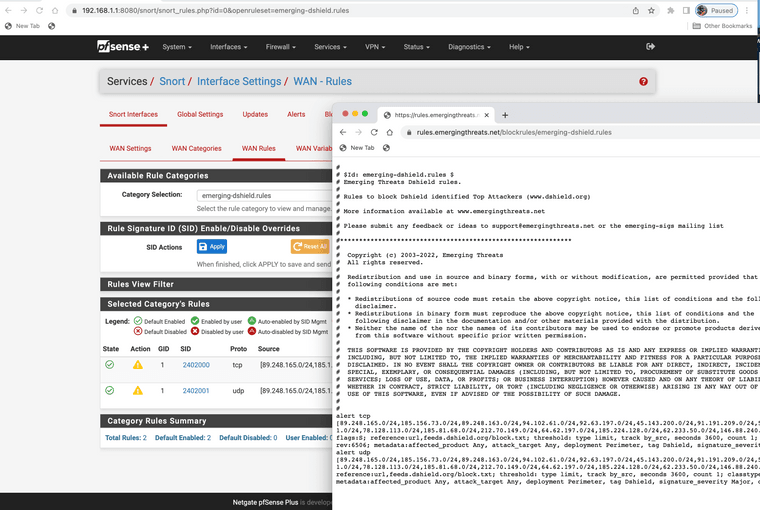
Brandon and others from emerging threats support has helped bring resolve to this issue.
Update your lists and they should populate again for all the items.
-
Jonathan, thanks for reporting! This disruption was due to an internal automation failing - we've fixed that problem and added some further alerting around failure points. We pushed the rules after the fixes were made on Saturday morning.
I'm glad we caught this post, and I'd also like to invite everyone to interact with us on twitter @et_labs and to join our Discourse.
Thanks again!
