Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash)
-
@bearhntr Windows DNS is much better.
Use only pfsense as GW and FW if you have the choice.
-
@bearhntr said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
lab machines will be Windows 7, 10, 11 and other servers - I truly feel this is the way I should go.
Which are windows.. Why would you not just use windows as your dns and dhcp? Especially if your going to run an AD, be it these machines are actual members of the AD or not, if your going to resolve and use AD in your setup.
Pfsense dhcp and dns is great when you don't have anything else to use.. But if your MS shop, and have windows servers running already then why would you not just leverage it for dhcp and dns - this makes it much easier to all your AD stuff resolving correctly, etc.
-
Windows Server 2019 Domain Controller as a backup to DNS
As noted above set a domain override to forward AD queries to Windows or you’ll have problems. (Login failures, slow login, group policy not found, etc.)
-
@johnpoz Although it works great using AD DNS/DHCP, you will face some problems with pfblockerNG DNSBL and/or pihole.
You won't be able to know what IP is being blocked because all of them will reach pfsense using AD IP.In this situation, I enable DHCP relay in pfsense and use DHCP from AD, in which will register A and reverse entries.
For users, I use DNS from pfsense, but there I create domain override and networks reverse entries.It's working fine for a few customers..
Edit: Using AD DNS will also create a problem with DNSBL bypass.
-
@mcury said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
you will face some problems with pfblockerNG DNSBL and/or pihole.
Nope, not an issue.. your clients point to your AD for dns, then your AD forwards to unbound, or shoot even forwards to your pihole, and then pihole forwards to unbound so you can use both pihole and pfblocker, etc.
with DNSBL bypass.
For clients you don't want to be filtered by unbound. Create a conditional forwarder in your AD dns that sends them somewhere else for dns that is not filtered by unbound. Say bind running on your pfsense that running on a different port even.
-
@johnpoz When you check the Reports tab in pfblockerNG, all you can see is the AD IP as source of the connections.
-
@mcury see my edit... Yes all stuff going to unbound from your AD would be from the AD IP, but you can create a conditional forwarder that sends clients asking AD that you don't want to be filtered to go somewhere else for upstream dns, etc .
-
@johnpoz said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
For clients you don't want to be filtered by unbound. Create a conditional forwarder in your AD dns that sends them somewhere else for dns that is not filtered by unbound. Say bind running on your pfsense that running on a different port even.
 Hmmm, that is another option too..
Hmmm, that is another option too.. -
@mcury said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
Hmmm, that is another option too..
There are always multiple ways to skin a cat.. But if your running AD, it makes sense to use that is as your first DNS, and also have it hand out dhcp.. And then skin the cat using that for whatever other thing you want to do with the skin.. Make a coat, or a purse, etc.
You could have your AD resolve even, and for stuff you want filtered use a conditional forwarder for those clients that forward to unbound/pihole, etc.
If everything is using your AD for dhcp and dns, this would be first stop to resolve all local resources - what happens after that you can configure in the AD dns - be it forwards to something that filters, be it forwarded to something that doesn't or even just resolve.
But when you run AD, clients of the AD should use it for dns and dhcp - this makes AD run easier and smoother.
-
@johnpoz I see your point.
I have been doing what I described above for a few years and no problems so far.But next time, I'll check that bind option indeed.. Point users to AD and check how it goes.
-
@mcury Sure if you know what your doing and how to setup domain forwards in unbound, etc, you can can have all your AD resolve, etc. But if your a MS shop, and your running AD.. It is cleaner to have your dns and dhcp via the AD.. What happens with filtering for dns records can either happen there in your AD dns.. or you can forward for your external filtered records to something that filters - be that pihole or unbound, etc.
Like said there are many ways to skin a cat ;)
-
@johnpoz said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
Like said there are many ways to skin a cat ;)
Indeed :)
-
@mcury personally I am what is good for the goose is also good for the gander.. If I am going to "filter" something - then all things should be filtered..
If there is some resource that should be able to resolve something, why would I filter it for just some and not all - the thing is either bad or its good.. Filtered or not filtered.. Not a fan of oh you can not lookup that fqdn, but my other device can..
You also have to keep in mind when your going to filter for some and not for others - that you don't run into a caching issue where client A looks up something and he is not filtered, and now that something is cached so when client B asks for it - guess what he gets the answer from cache, when it should of been filtered for him, etc.
Something is either filtered or not filtered - if you find you need to be able to resolve something or get to something for something to work.. Guess that something shouldn't be filtered in the first place, and all things should be able to get to it..
-
@johnpoz Me too, but sometimes that depends on what the customer needs.
Squid requires so much maintenance that I'm not using it anymore, and some customers asks for web filtering.In this situation, I'm using pfblockerNG to create a few block lists, create a GPO to block DOH, DOT, QUIC, in the browsers..
For the managers or VIPs, I just put them in the python bypass in DNSBL.Sometimes, when I need multiple filtering groups, I go for Squid but I only set it in the browsers, to avoid some applications problems.
Explicit, with some bypasses directly from the client or using PAC, or directly in the browser configuration.
When I do like this, I force the use of the proxy by GPO, not allowing the user to change this setting. -
@mcury said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
Sometimes, when I need multiple filtering groups
Maybe some education of your clients is what is needed here.. But yeah filtered of groups sometimes in a work setup is prudent.. While you might trust salaried guy to not spend his time shopping amazon while suppose to be working, while some group machine sitting on the plant floor that anyone can just walk by, etc.
Still not a fan of playing internet nazi, but yeah sometime customers don't get it. So you think keeping the plant floor machine from going to amazon stops them from going to amazon? They prob just use their phone if the computer can't get there.. Just like boss man could..
If it filtered it should be filtered for all, if its open - then its open for all.. I use to run web filtering for a large corp for many years, and they finally wised up and just used the same filtering set for all, vs like 5 different goups - oh these guys can go to shopping, these guys can only during lunch, etc. etc.. It just over complicates everything, and just leads to problems in all aspects - more work for the IT, more frustration for others - why can billy go to xyz.com while susan can't etc. etc.
They went with policy of group type kiosk machines out on the floor were just limited to specific whitelist internet a few external sites like insurance website, etc. And then they could get to anything on the intranet.
If you figured out a way to skin the cat to give the customer what they asked for then great.. But depending on the breed and size of the cat - there are always going to be multiple ways to skin it to make what you want out of the skin ;)
-
@johnpoz said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
If you figured out a way to skin the cat to give the customer what they asked for then great.. But depending on the breed and size of the cat - there are always going to be multiple ways to skin it to make what you want out of the skin ;)
That is it.. :)
-
You have all give some great ideas. In my current setup - I have pfSense immediately behind the Comcast modem , then from pfSense there is my Netgear Orbi (as my home has no wiring; yet, for Ethernet) and the Orbi has a satellite in the other end of the house (my office - with 4 ports and those are providing wired Ethernet to my personal and work computers); but for all intents everything in wireless in the home - one day that will all change. On pfSense I have CloudFlare DDNS setup which allows me access to my HomeAssistant with my own domain hosted at CF.
I would like to at some point use pfBlocker or some other filter adBlocker, but not gotten that far yet. My work role changed and thus the need to stand up some server and workstation VMs using AD/LDAP for signing on, etc.
pfSense is running on a stand-alone HP ThinClient and currently the Server 2019 I was going to use as AD/DS is on a Proxmox VM - which also has 2 other Server installs and 2x Windows 10, 1x Windows 7 and 1x Windows 11 VMs (lab).
Should I look to put the AD/DS on its own box - I do have a spare server (older) which on-board NIC and a 4-port PCI Ethernet card installed.
Looking for best suggestions to make this all work - and try to keep the lab and the home separate (not super familiar with VLANs - yet). Home uses a 10.9.28.1/24 network and was thinking that I would use 10.100.28.1/24 for Lab. But I would also like to make sure that "if I want/need to" - I can access lab from home network.
I know that during the installation of the AD/DS it will install DNS and it really needs to be setup to make things work best.
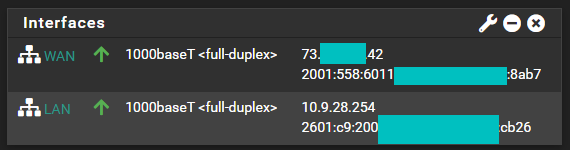
Currently pfSense looks like this - and has the roles of DNS, DDNS, IPv4 and IPv6:
-
I am also going to need at some point to setup a CA for the lab.
My real goal would be to have AD/DS logins for everything - which I realize means a HOME and a LAB Domain (or a sub-domain for one of them under the other).
-
Just a mind-scratcher for me. I have my own domain (to the Internet) that Google is my provider - for the next 2.5 years then may move. CloudFlare requires this.
Am I able to:
a) use that domain when I setup my DC? Is it going to cause fits?
b) somehow setup a sub-domain (will I need another DC or something else) to separate my home machines from the proposed lab?
Thanks in Advance
-
@bearhntr said in Using pfSense as firewall and Windows Server as DHCP and DNS server (re-hash):
a) use that domain when I setup my DC? Is it going to cause fits?
While "fits" may be a bit strong, it would most definitely cause you a lot of heartache and thus should be avoided. Don't use your public domain for your private Active Directory domain.
The proper way to do this is with a sub-domain. So, for example, if your public domain currently registered with Google is
mydomain.com, then your Active Directory domain on your LAN would beinternal.mydomain.com. There are a few other ways to name, but all suggest a sub-domain. Here is a TechNet article about this: https://social.technet.microsoft.com/wiki/contents/articles/34981.active-directory-best-practices-for-internal-domain-and-network-names.aspx.And yes, you need a separate domain controller for each Active Directory domain (including subdomains). You can't host multiple domains on the same domain controller. So, if you want a lab internal domain, then it will need its own domain controller separate from other domain controllers for your LAN.