Cannot connect with RDP via openVPN
-
@IrixOS connect via your wan interface.. Setup your lagg how you want it, validate its working.. Then reconnect your wan to your internet connection..
If you want put a switch between your wan and your isp device.. Put your laptop on some IP your wan is on.. etc..
Another option, add another nic - if you have no slots for one - use a usb nic, use that to connect to pfsense so you can setup your lagg..
-
The ip addressing is not correct but that's not the problem.
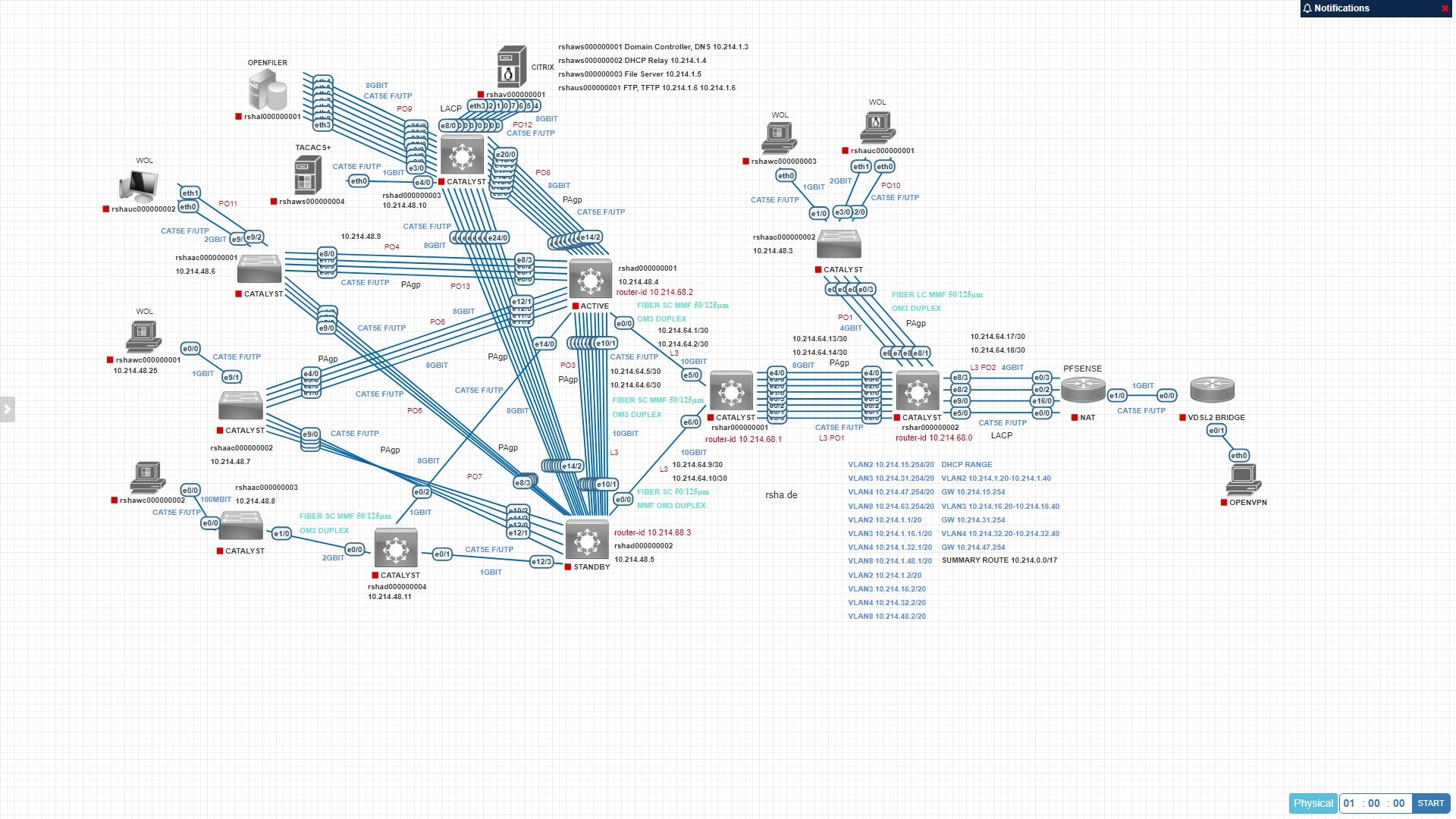
Have look at L3 PO2 near the pfsense router, assume one link of the four is the LAN link /30 subnet (10.216.64.17) on the switch and 10.216.64.18 is the interface, the LAN of the pfsense router. (The schema respresents 4 links, in reality it is three, because one is for the WAN connection to the modem so minus -1 is three, well I want all of three (includes the LAN) or at least two links to be part of the lagg0.
-
@IrixOS none of your routing or how crazy your network is makes any matter..
Connect into the pfsense box on an interface your not putting into the lagg.. Make sure your lagg is up, put your networks you want over lagg on the lagg.. If you need to add an interface, even if usbnic to set it up.. Then do that..
Not sure what else to tell you? But trying to setup a lagg on an interface your wanting to add to the lagg could be problematic if your lagg isn't coming up.. So use another interface.. Either come in over your wan, you might have to take down the wan for internet while you do that, or just use another interface.. If you don't have one - then add one..
-
@IrixOS this has your certificate listed you should delete the post with the SSL certificate information that can be copied and pasted into something
-
@JonathanLee you mean the ones I already snipped big chunks out already, see where it says <snipped by mod> to make that info useless.
-
In this discussion post please blank this out, it is the ssl certificate, bad guys can manually copy that info.
@IrixOS said in Cannot connect with RDP via openVPN:
persist-tun
persist-key
cipher AES-128-CBC
ncp-ciphers AES-256-GCM:AES-128-GCM
auth SHA1
tls-client
client
remote rshafw000000001.ddns.net 1194 udp
verify-x509-name "www.rsha.de" name
auth-user-pass
remote-cert-tls server
compress lz4-v2<ca>
-----BEGIN CERTIFICATE---
Blank this out for please
-----END CERTIFICATE-----
</ca>
<cert>
-----BEGIN CERTIFICATE-----
blank this out please
-----END CERTIFICATE-----
</cert>
<key>
-----BEGIN PRIVATE KEY——-
blank this out please
-----END PRIVATE KEY-----
</key>
<tls-auth>2048 bit OpenVPN static key
-----BEGIN OpenVPN Static key V1-----
blank this out please
-----END OpenVPN Static key V1-----
</tls-auth>
key-direction 1 -
@JonathanLee dude I rendered that info useless when he first posted it.. I snipped out big chunks of the data.. All that is there now is what amounts to random characters.
-
@johnpoz I didn't notice, I just saw SSL cert and I thought Nooooooooooooooooo don't post it

-
yeah, I have already been criticized for that, I don't think they are no valid no more, got a new box, what do you think? I will delete them later on.
-
I think I know what you mean, I have four ports in total, one for WAN, one for LAN and two free ports that I want to add to LAN in lagg, but there is no more port free, because I want all three to be part of the lagg so the manual says you can do it via VPN, so you have to configure the internal kitchen from the outside?
 That's the most stupid thing I ever heard in my entire life.
That's the most stupid thing I ever heard in my entire life. -
@IrixOS
Set up Lag on 2 of the 3 Lan NIC by connecting your laptop to the third NIC. Then- Unplug your router
- connect a laptop to your routers lan NIC to set the WAN physical port to temporary pfsense GUI access
- Connect your laptop to the routers WAN NIC
- Configure lagg on the 3 LAN physical NICs
- Connect your switch to the 3 LAN NICs now in lagg
- Connect your laptop to pfsence via your new lagg connected LAN interface
- Revet the WAN settings
- Plug back in your WAN
-
Forum doesn't allow me to delete my own posts.
Anyways thx for stripping the certificate. -
@Patch said in Cannot connect with RDP via openVPN:
to set the WAN physical port to temporary pfsense GUI access
'to set the WAN physical port to temporary pfsense GUI access'
How do you set that? In Firewall rules?
-
@IrixOS yes
There is a default anti lockout rule created for the first LAN. To access the pfsense gui from any other interface you need to add the firearm rule to allow it -
@Patch said in Cannot connect with RDP via openVPN:
To access the pfsense gui from any other interface you need to add the firearm rule to allow it
Lets clarify that a bit, if your rules on your other interface blocked access to the firewall specifically then yeah you would need to add an allow rule.. But if you just put say a any any rule on it, you would be able to access the gui.
Now the wan is a bit different.. Out of the box there are no rules, and most users unless they wanted to do some sort of port forward would never even need any rules on wan. It also defaults to blocking rfc1918 source, and bogon as a source.. If your going to use your wan to admin it, from rfc1918 you would need to disable that rfc1918 rule, and create an allow rule.
The only time "wan" defaults to allowing access is when pfsense is first setup and there is only the WAN interface setup.. If you then later setup lan then that allow rule is removed..
On a bit of side note - users wanting to block access to the web gui should prob use the "this firewall" alias because if they allow any any for internet, they prob forget about the pfsense public IP that would be allowed by a any any rule on some opt interface.. So blocking the pfsense gui ports using the "this firewall" alias makes sure clients can not get to any IP of pfsense, even though other rules below it might allow that, etc.
-
Johnpoz, Hey JohnPoz, I think you're the only one who can help me.
I have done a refit of my network with Catalyst 3750 and 4948-10GE.
I have a serious DNS problem.
I have a few switches/routers that run OSPF, 1 router is connected via a /30 subnet (lag of four ports) to the firewall.
All clients behind the ospf routers can reach the pfsense GUI webpage, but they cannot access the internet. Windows 10 diag indicates the DNS server is unavailable. Windows DNS server is configured with the IP address (LAN interface) of the firewall.
A null route is configured on the ASBR (0.0.0.0 0.0.0.0 next hop IP) and has been propagated to all ospf switches/routers. In pfsense there is a static route (the lagg link) back to the internal ospf network. So I know that routing works from the client to the edge firewall and vice versa.
I have configured a rule that allows the internal network (summary route) to the firewall and for outbound NAT, allows the internal network (summary route) to everything (*).Normally every client should be on the internet, but that doesn't happen, Windows 10 complains about DNS unavailable, I don't understand what is wrong.
In pfsense I did a few tests with nslookup in diagnostics for msn.be for example and the output is positive. I do not immediately see an error in the output. Can I assume that DNS resolution works on the firewall?One way to test is to connect a PC in a /30 directly to the LAN port, but the /30 LAN port has a port channel, and I tried one link instead but that didn't work, couldn't connect to the firewall, probably because of the static route which expects another network device, I dont' know.
Do you perhaps have some advice?