HA Proxy / Acme Lets encrypt : LAN access problem from inside with external url https
-
@ducati57 well you could set your local dns to resolve these public fqdn to your pfsense wan IP, vs public IP that is being reflected by your edge device.
That way vs going to your edge device to be reflected back in, they would hit your pfsense wan where haproxy would direct them where to go.. I do the same sort of haproxy ssl offload sort of setup.. But in my case my public IP is on my pfsense wan. So when my clients behind pfsense want to go there, they just hit the pfsense wan IP coming in from the lan side which is allowed.
You could setup a simple override or multiple if you have multiple different fqdns so your local devices using pfsense as their dns would resolve them to your pfsense wan IP..
-
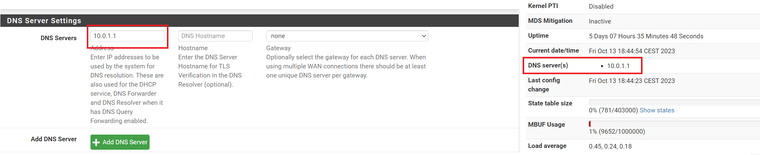
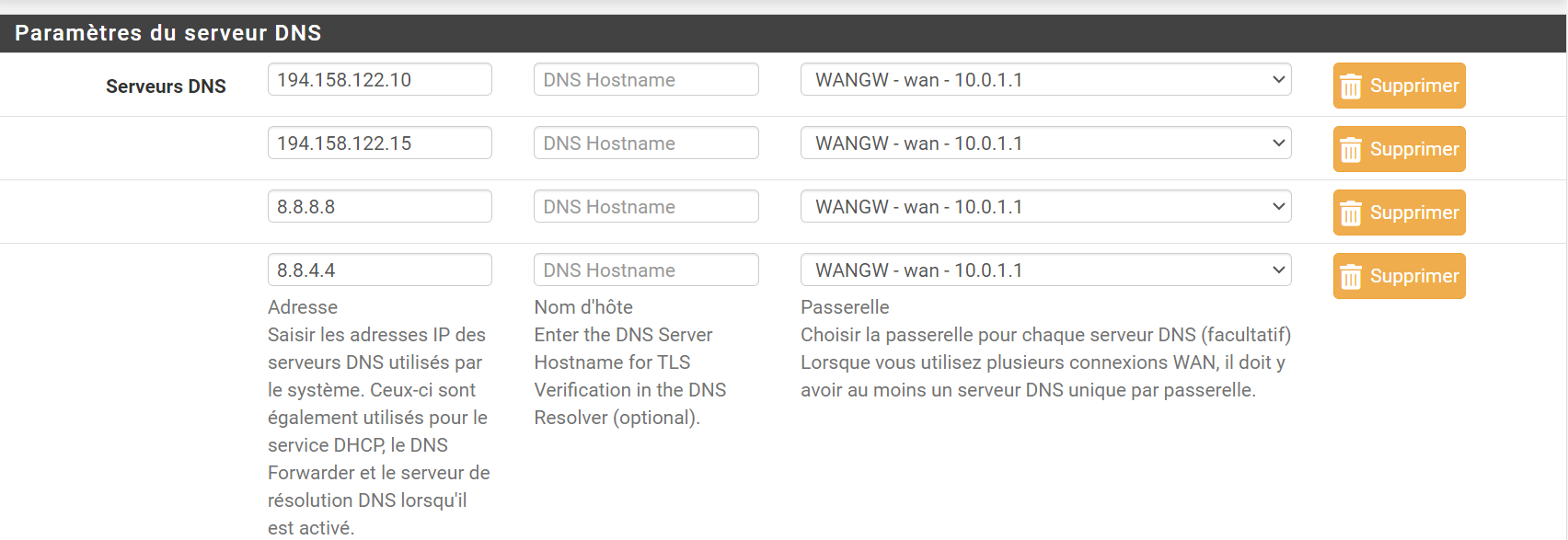
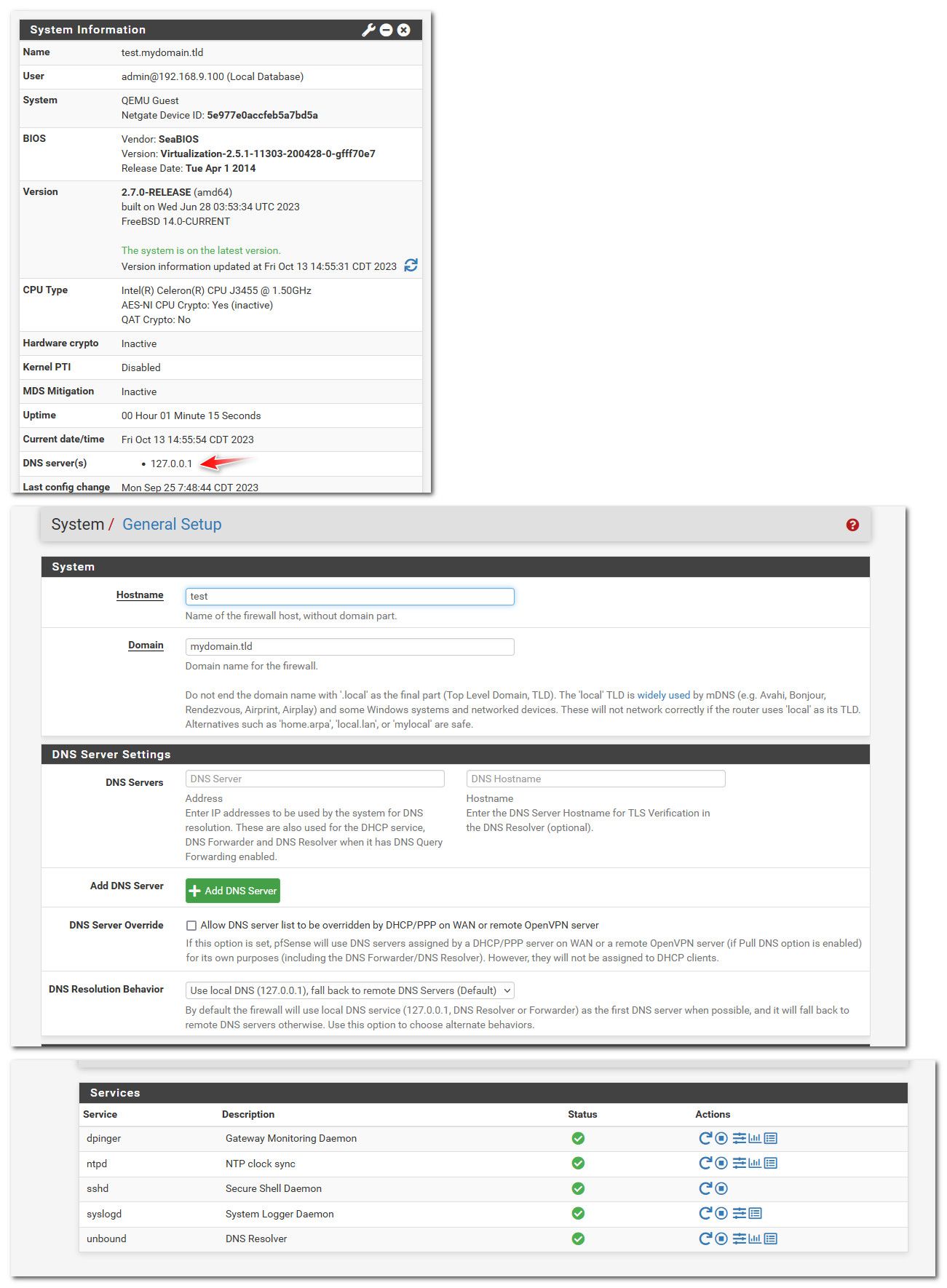
Here are the DNS currently used by Pfsense, the whole thing is attached to the WAN interface 10.1.1.1.
Provider: primary 194.158.122.10 Secondary 194.158.122.15
Google : primary 8.8.8.8 Secondary 8.8.4.4 -
@ducati57 don't matter what pfsense is using - matters that your clients are pointing to pfsense for theirs.
also - you could set those all you want, pfsense out of the box resolves. So unless you went in and enabled forwarding mode, unbound on pfsense just resolves.
-
Is there a tutorial for making the modification ? Because if I understand correctly, it is necessary to make the modification on each client or on Pfsense?
I am not an "expert" in the IT / Firewall part, I work in the telecom (backbone / longhaul) fiber optic sector :)
-
@ducati57 so out of the box if you enable dhcp on pfsense it would hand out its own IP to any dhcp clients. Unless you don't have unbound or dnsmasq running on pfsense. Then it would hand out the dns you have set in general.
To be honest, this is out of the box for most users - nothing really to do.
You would just need to create the host overrides in unbound (resolver).. example here is somee host overrides I have setup
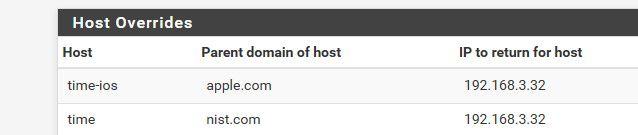
So when my clients ask pfsense for dns, it returns my local IP.. Vs the public IP you would get if you asked public dns
$ dig @8.8.8.8 time.nist.com +short 208.91.197.27 $ dig time.nist.com +short 192.168.3.32 $ dig time-ios.apple.com +short 192.168.3.32 $ dig @8.8.8.8 time-ios.apple.com +short time.g.aaplimg.com. 17.253.26.123 17.253.6.125 17.253.26.251So now clients wanting to look up those fqdn, instead of going to the public IP (your edge).. They would just go to your pfsense wan IP and haproxy would proxy them to where you have setup.. In my case they just ask my local ntp server vs the ntp servers on the public internet.
-
Here are the basic DNS on Pfsense.
I will make the modifications as you detailed previously and post a screenshot.
-
@ducati57 yeah - you already stated that.. Not sure what else you want me to say? Out of the box unbound doesn't even use those.. Unless you specifically setup unbound to forward.
And it doesn't matter what pfsense does be it resolve for forward.. If your client, ie some pc on your network is asking pfsense for dns.. And you setup a host override then that is the new iP that would be handed to the client for the fqdn it asked for.
If your pc is using say 8.8.8.8 or any of those you listed for dns directly - then no a host override wouldn't work, because the client is never asking pfsense to resolve anything anyway.
-
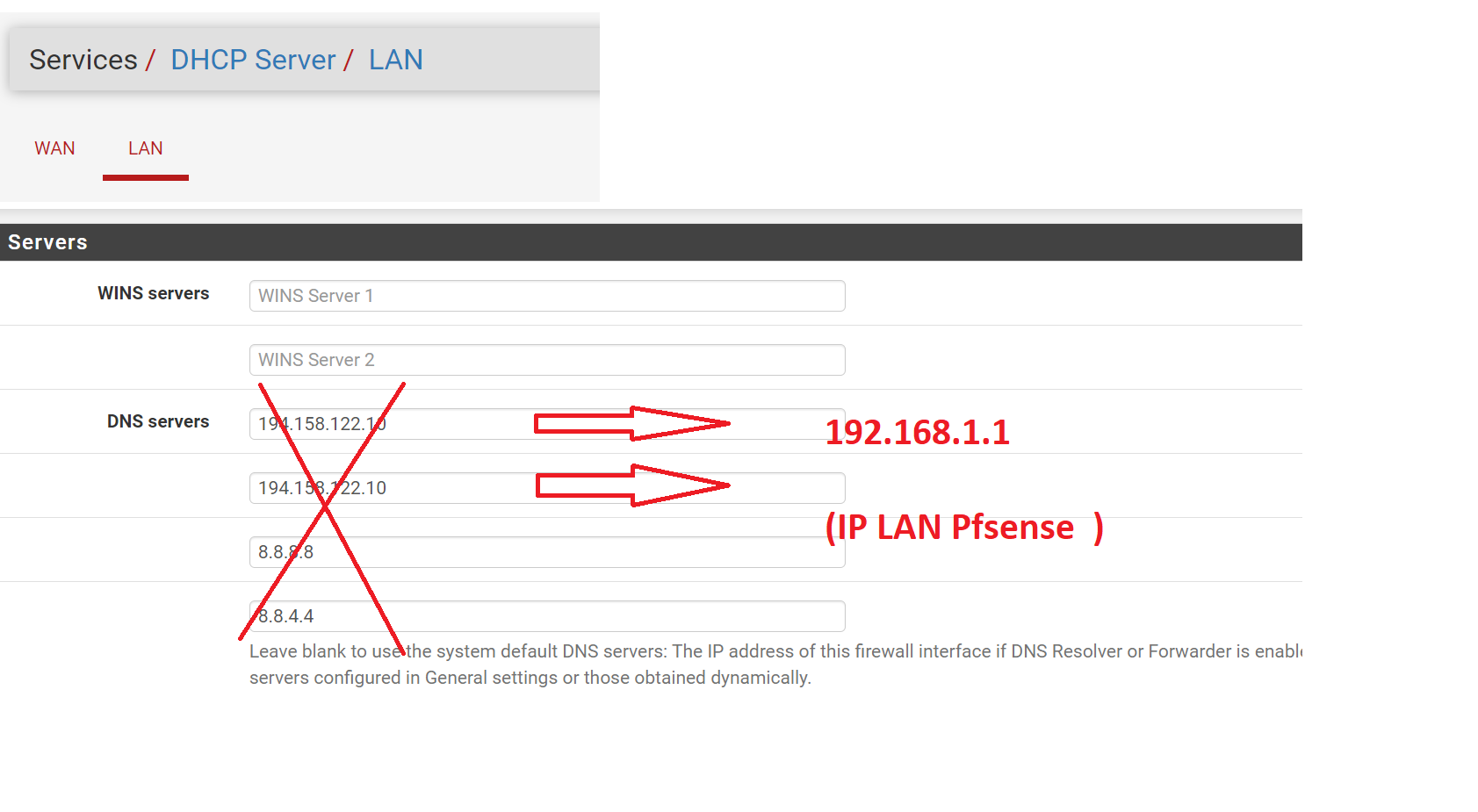
So here is the modification to be made, directly on the LAN/DHCP server?
-
@ducati57 You don't need to put anything in there..
Out of the box pfsense will ask itself (unbound) for dns - which resolves..
You only need to put those in - if you want pfsense to use them, or you want to forward to them from unbound, etc. I have zero use for any external dns provider since I just let unbound resolve, as it does by default anyway..
-
-
@ducati57 If that is pfsense IP, why would you set that and not just use loopback? Which is does all on its own..
-
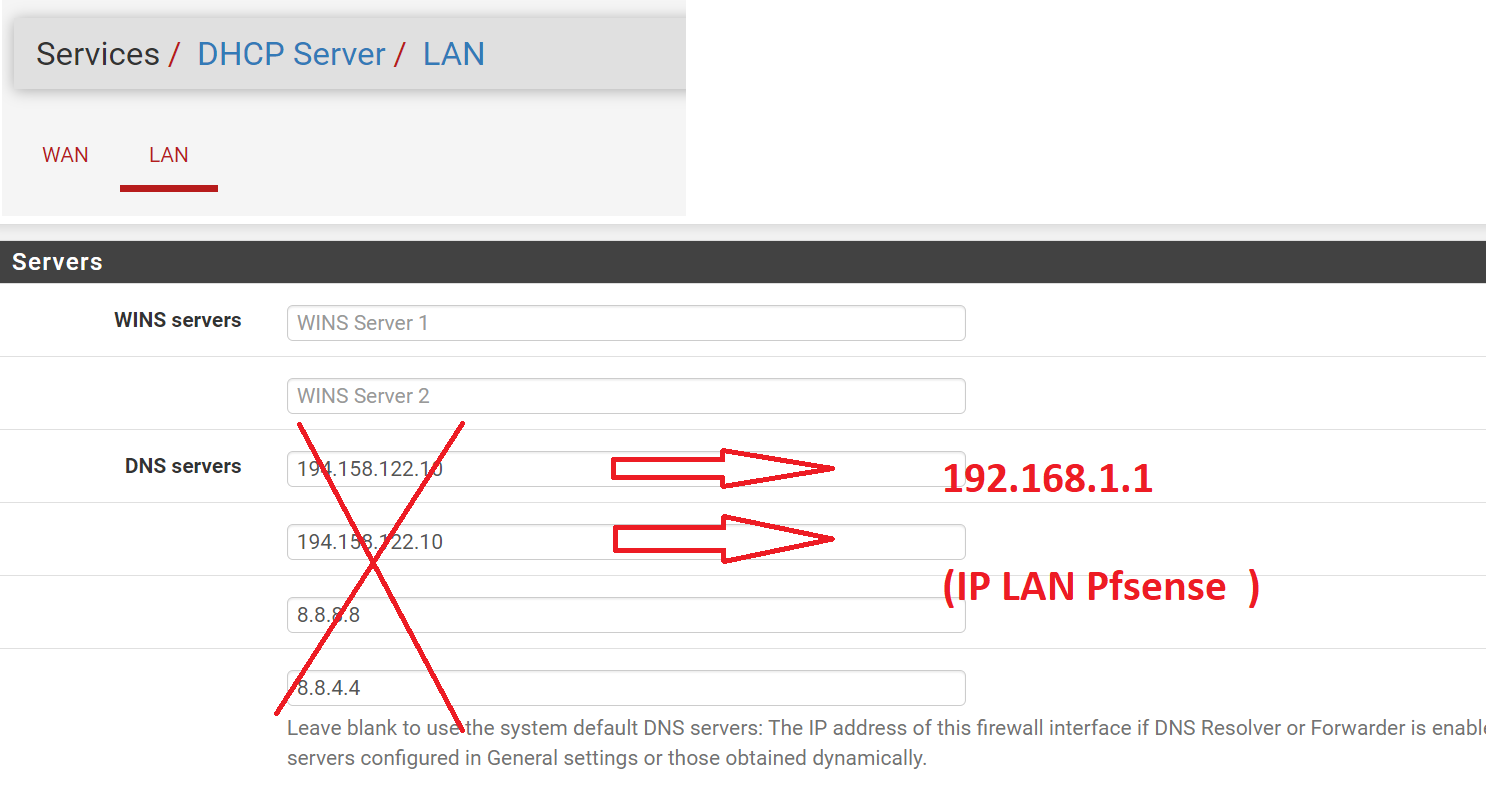
If I do not indicate anything, and I configure Pfsense identical to your screenshot, here is the result
(KO update status because no external access because no DNS?)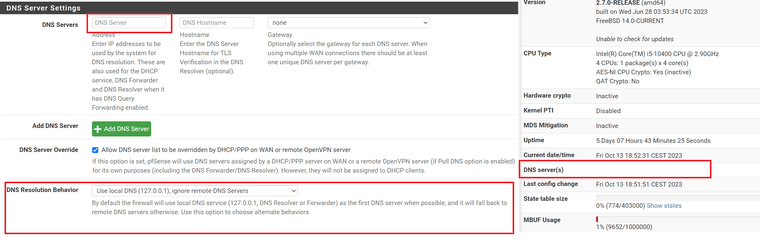
-
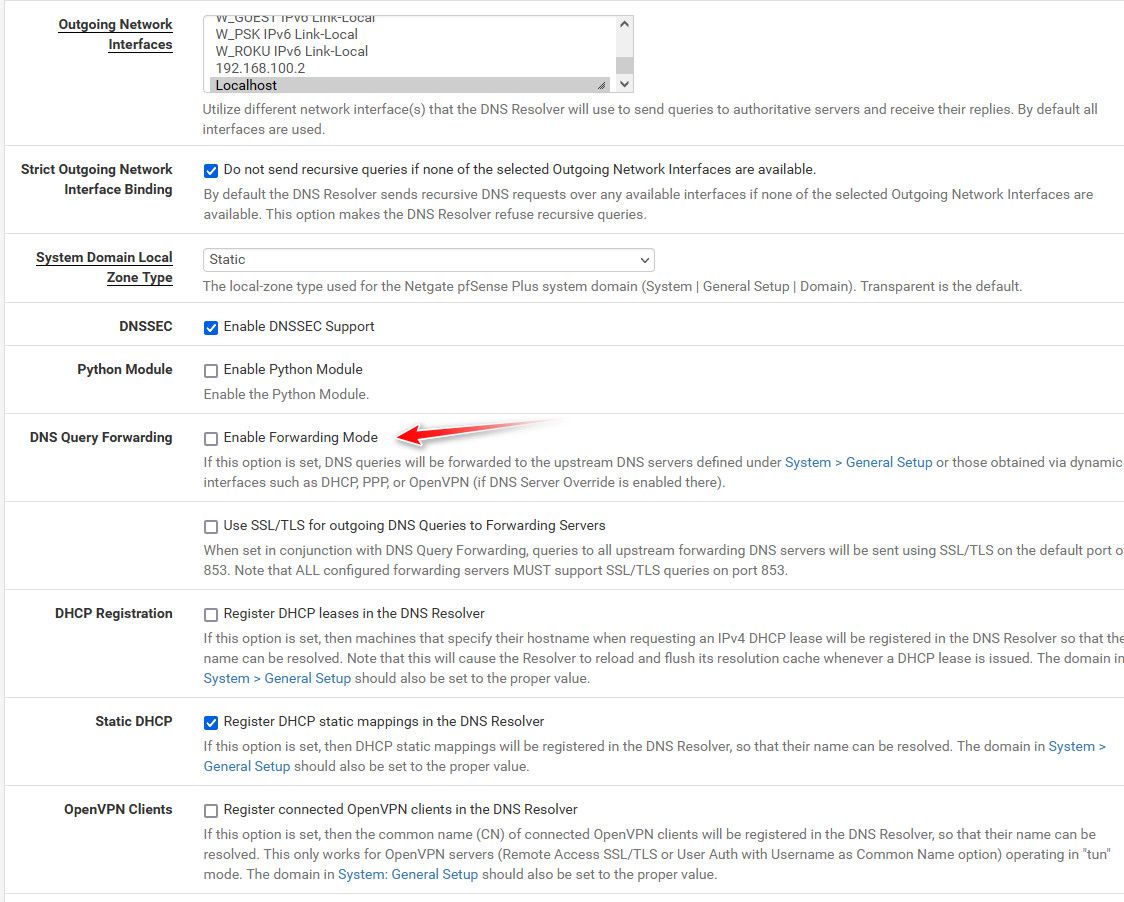
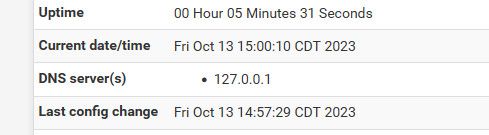
@ducati57 did you modify unbound settings?
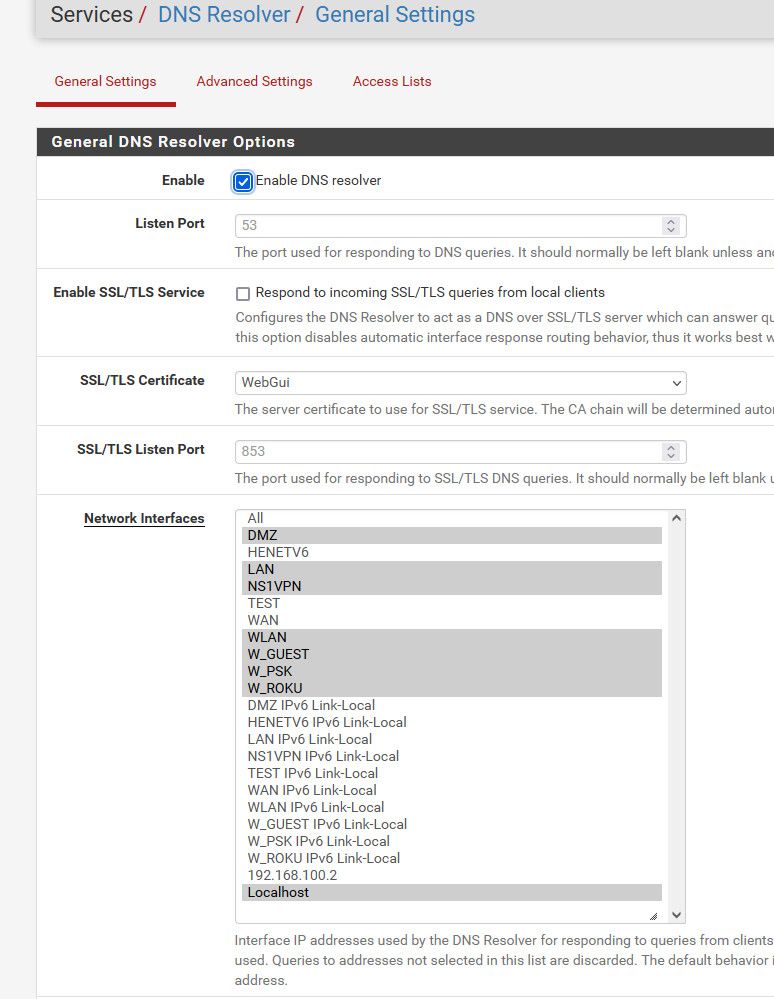
By default its ALL, did you change it and not include localhost?
Is unbound running even?
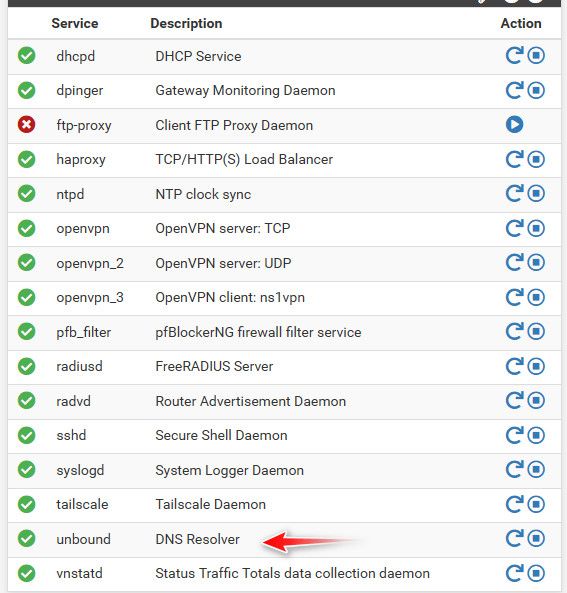
-
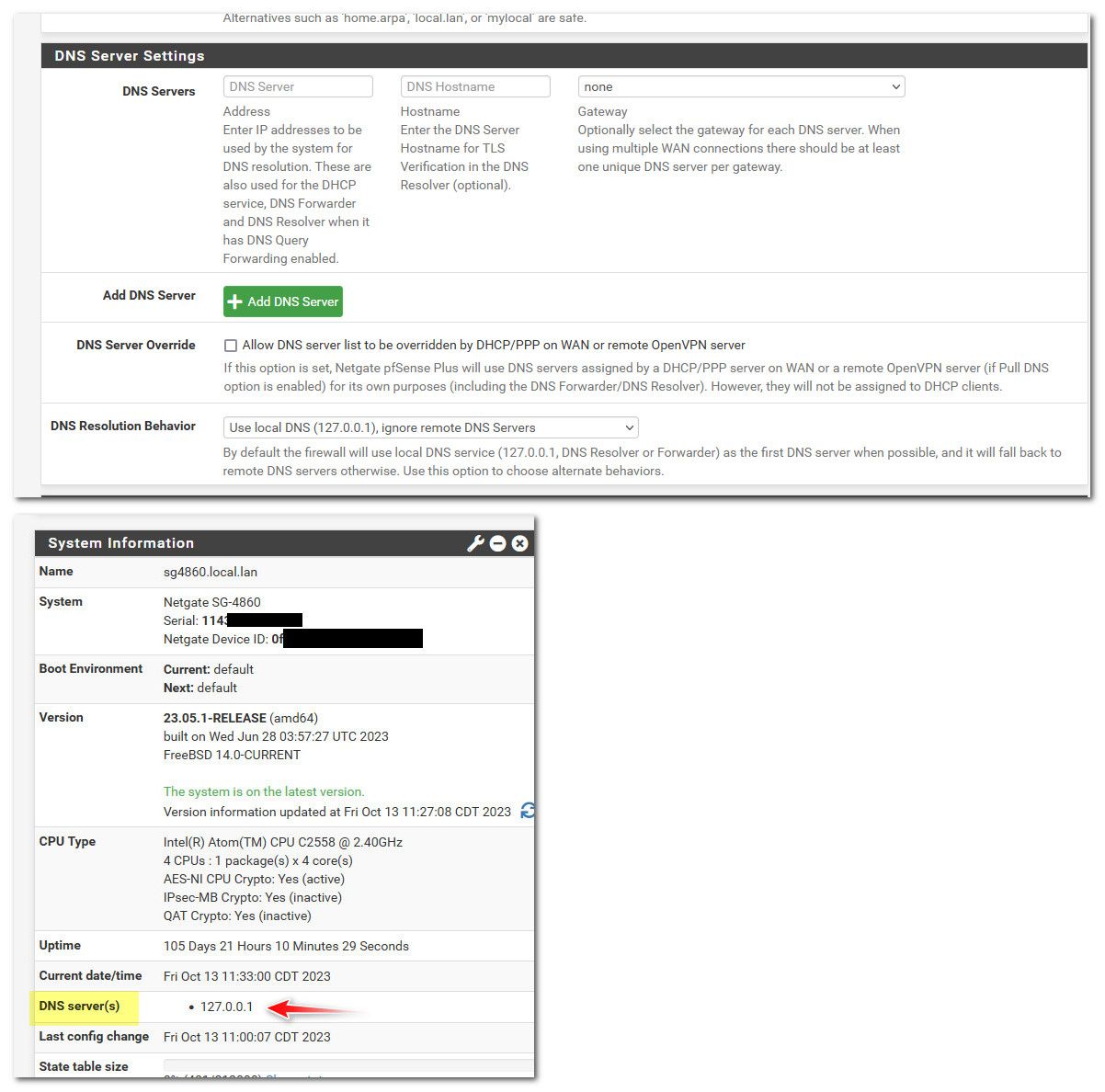
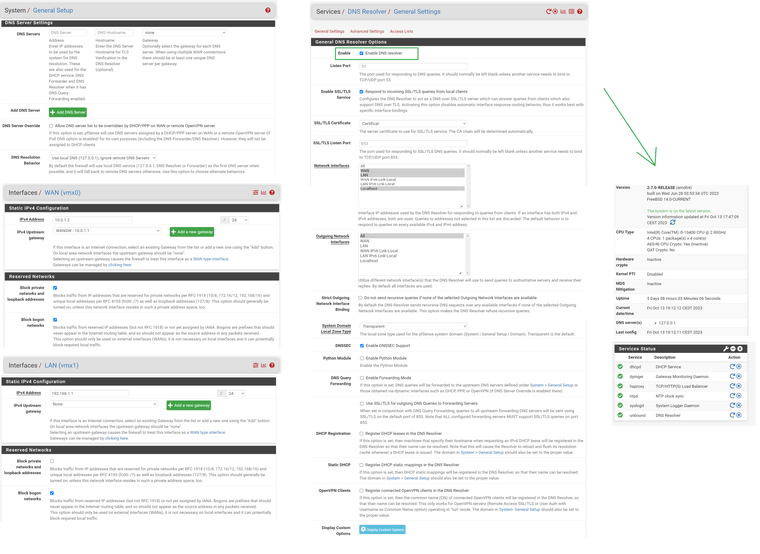
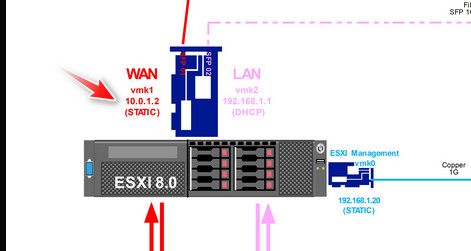
Here is the configuration of the different elements / services do you see an error? (security problem, loop, bug, useless,etc..)
-
@ducati57 well I see one thing that I personally would not do.. If your going to set the specific interfaces that unbound listens on, why would you click on wan.. Do you have devices that would be using the dns via its wan IP?
Your saying with those settings it does not populate 127.0.0.1 in the system tab for dns? If you do not put anything in the dns tab?
Here I just fired up my 2.7 box.. Its pretty much default out of the box.. Other than changing its lan to other than the default 192.168.1.1
I then changed from all, to just lan and got this error

So I selected localhost along with just lan and it worked and system still shows dns as loopback 127.0.0.1
-
@johnpoz
Good morning,I just made the modification, it's gone.
However still no local LAN access via HTTPS from an external url
-
@ducati57 said in HA Proxy / Acme Lets encrypt : LAN access problem from inside with external url https:
However still no local LAN access via HTTPS from an external url
did you create you host overrides??
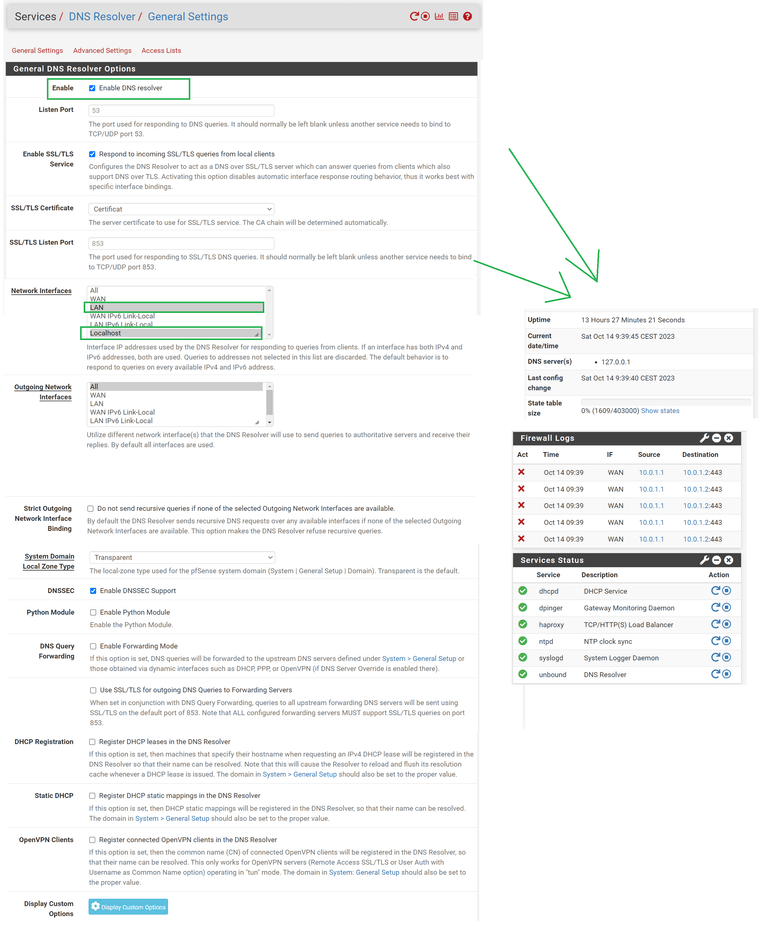
Are you clients pointing to pfsense for dns?
Do a simple dns query from a client - did it resolve your fqdn to pfsense wan IP? Vs the public.. Maybe your browser is using doh for dns? Vs pointing to pfsense IP for it.
-
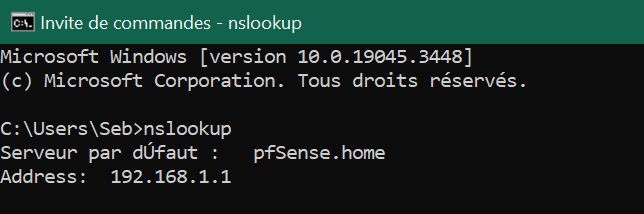
@johnpoz Yes, here is the conf for "Host Overrides"

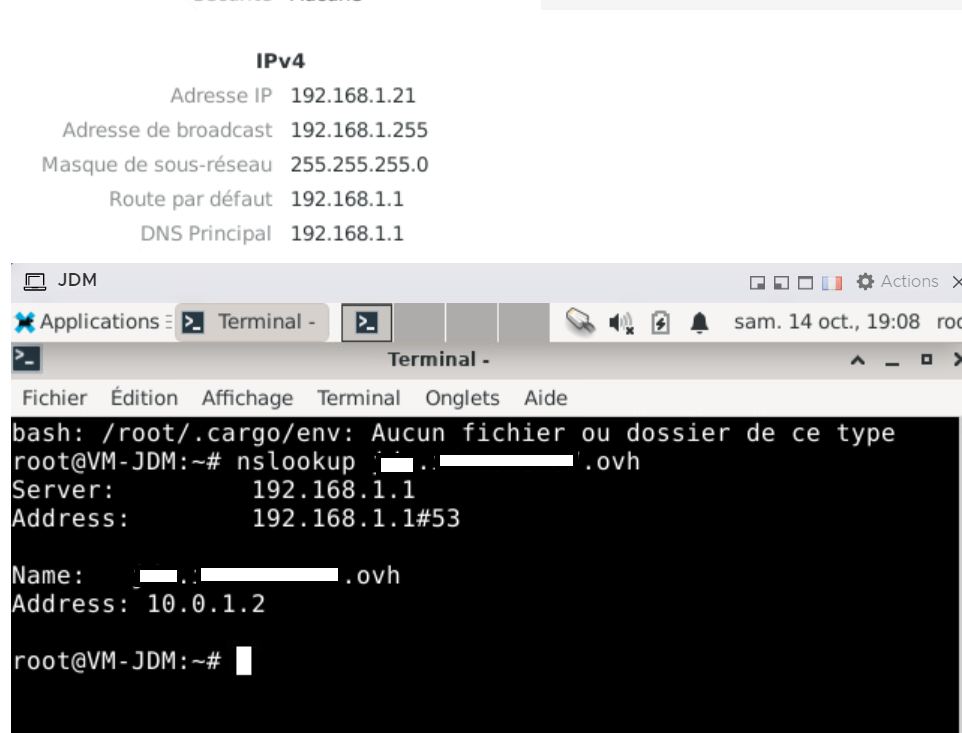
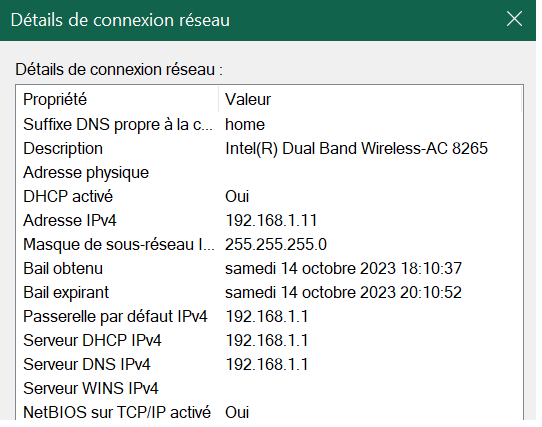
Yes, here is my PC (wifi) where it is visible in DNS (Pfsense) in 192.168.1.1
-
@ducati57 so your nslookup for dom.namedomaine.ovh returns 192.168.1.21
do your nslookup dom.namedomaine.ovh
What does it reply with - if that works and your still going to the public in your browser - you sure your browser isn't using doh vs your local dns.
And that is not the right override anyway - if you want it to bounce off pfsense wan IP running haproxy, then it should be to pfsense wan IP.. Not the actual host IP the site is running on.
-
@johnpoz said in HA Proxy / Acme Lets encrypt : LAN access problem from inside with external url https:
do your nslookup dom.namedomaine.ovh
A test from my laptop :
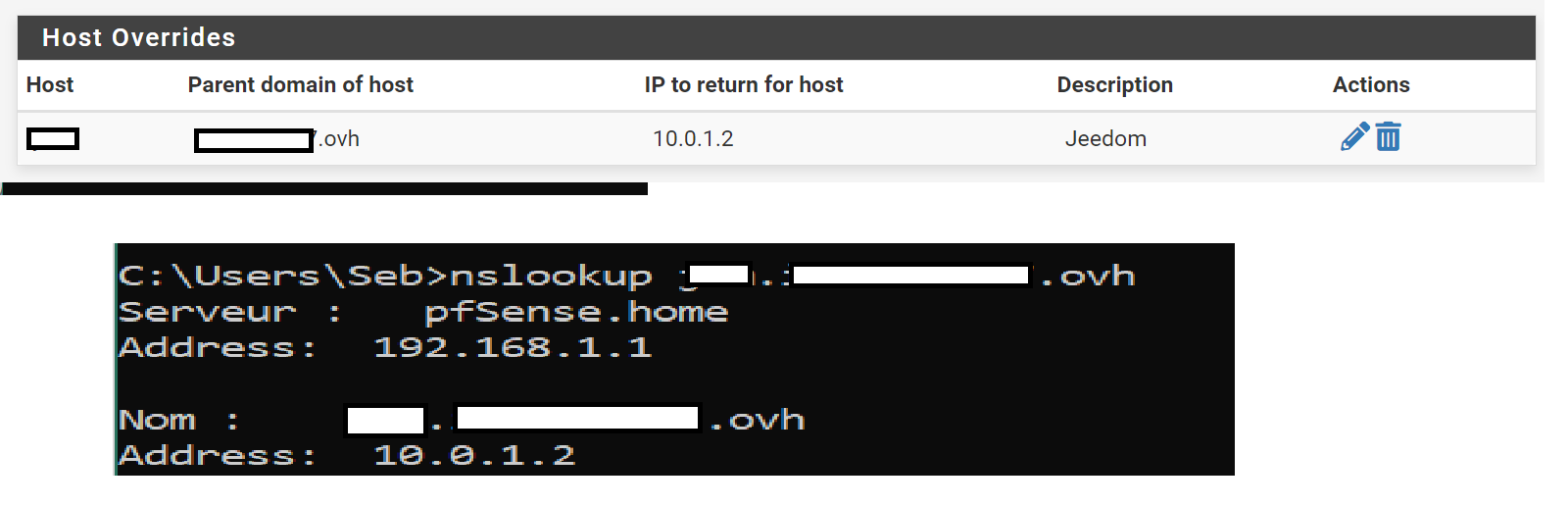
A direct test of the VM on my ESXI :