block outbound ICMP or not?
-
My setup: Netgate 1100, pfsense+ version 23.05.1.
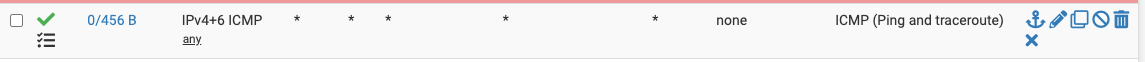
I have a rule that allows outbound an explicit pass on the LAN and OPT interfaces for ICMP, like so:
I don't do NATing, VPNs or anything else exotic. Logging for this rule shows outbound connections from various LAN/OPT devices to places like (mostly) cloudfront. Are these connections good, bad, harmless, nefarious? Is this rule a bright idea or a bad move?
-
What do you expect to accomplish by blocking it? ICMP is used for a lot of things and on IPv6 it's essential.
-
@JKnott My explicit pass rule has been there for a while, but I turned on logging the other day and started noticing outbound traffic beyond my own "traceroute -P icmp" work. Hence my question... I didn't know that IPv6 relied on it.
-
Hi- from the Netgate Doc; https://docs.netgate.com/pfsense/en/latest/firewall/configure.html
-
Thanks for pointing me to the ICMP part of the doc, I should have looked there. Another dumb question put to rest. I'll turn off logging for my pass rule (like it was) and leave things alone. Thank you both.