Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module
-
@bmeeks I will reinstall Suricata again here on plus because I ditched that switch in the meantime (again), one probe more, I will report what I find.
-
@Bob-Dig said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
@bmeeks I will reinstall Suricata again here on plus because I ditched that switch in the meantime (again), one probe more, I will report what I find.
Just had a Snort user report he is seeing the Signal 11 fault and core dump on 2.7.0-RELEASE, so maybe it is more widespread. All the pfSense versions now have the same flavor of the custom blocking plugin, and nearly all of the code in that plugin is identical for both Snort and Suricata.
-
@bmeeks said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
The vast majority (if not all) of the current reports seem to be coming from Plus users. But I'm still trying to get an accurate inventory of operating systems associated with the Signal 11 faults.
Hi, here pfsense CE 2.7.0 Snort 4.1.6_13 exit with signal 11 (coredumped).
When kill states are off - no crash. -
@fireodo said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
Hi, here pfsense CE 2.7.0 Snort 4.1.6_13 exit with signal 11 (coredumped).
When kill states are off - no crash.Thanks. So it is more widespread. I will feed this back to the Netgate kernel developer. We definitely found one typo in the new code, but does not seem it should be causing the Signal 11 fault.
-
@bmeeks Suricata works fine with the kill states unticked.
-
@NogBadTheBad said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
@bmeeks Suricata works fine with the kill states unticked.
Thanks for that report. It seems to further confirm the problem is solely within the new "kill states" changes. That is where we are currently focusing our efforts this morning.
-
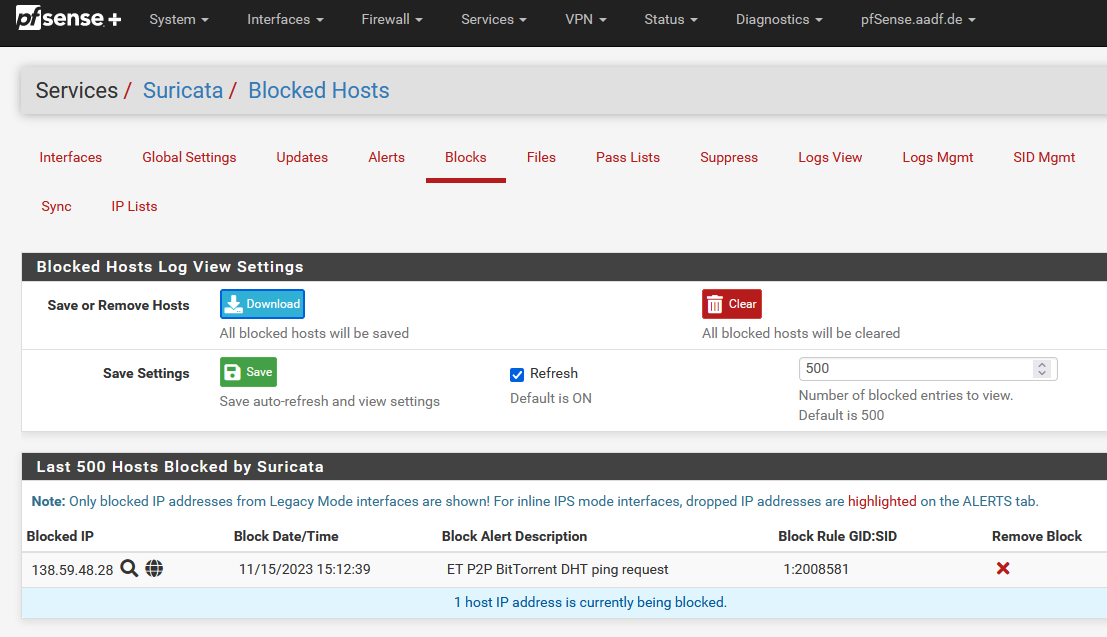
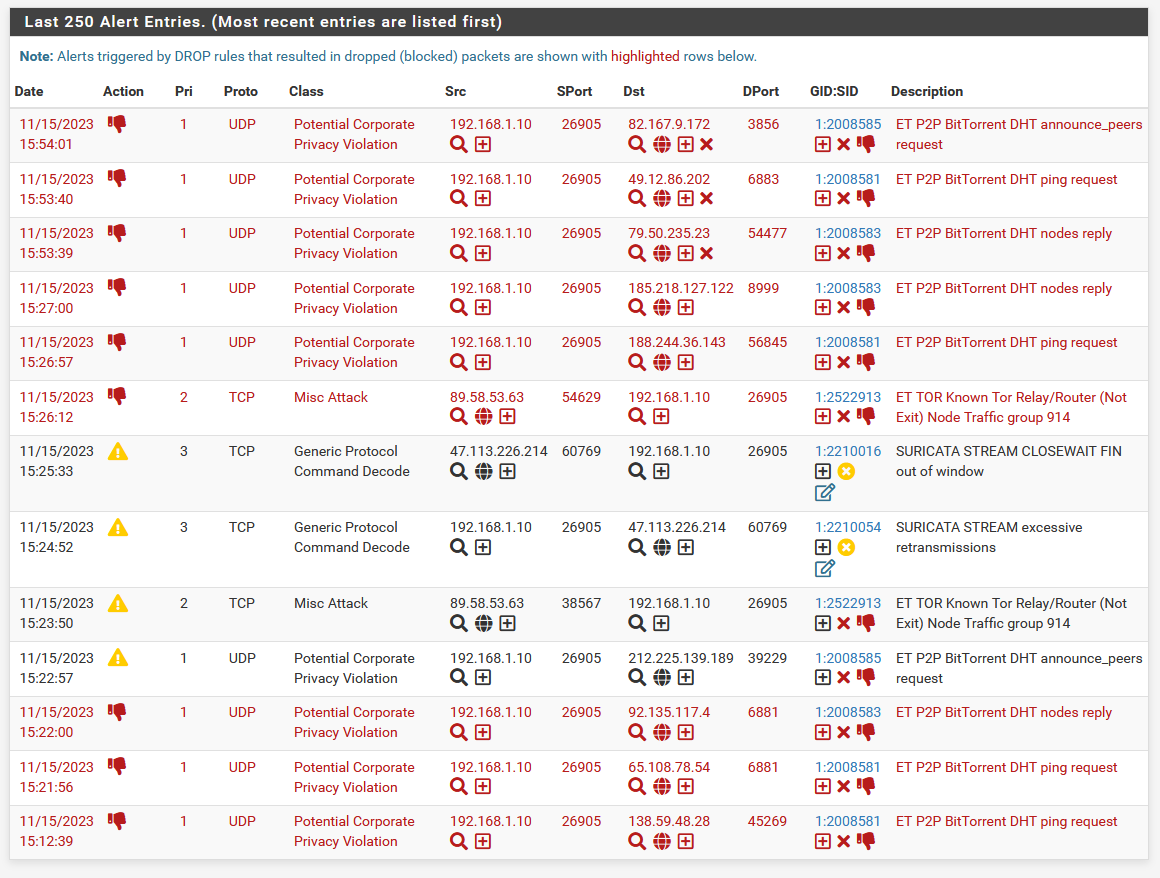
I have a block here (Kill States enabled), everything seems to be good, so maybe Suricata isn't affected. I don't use any snort rules though.
-
@Bob-Dig said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
I have a block here (Kill States enabled), everything seems to be good, so maybe Suricata isn't affected. I don't use any snort rules though.
Give it some running time. The fault is not always instantaneous for other users. Some are seeing up to 30 minutes of runtime before a fault.
The specific rules (Snort VRT versus Emerging Threats or others) should not play any role here. The custom blocking plugin code is generally ignorant of the rule specifics. It is just concerned with pulling out the offending IP from the data passed by the main binary and then deciding whether to block the IP or not based on any configured pass list.
From evidence gathered thus far, the bug appears to need multiple factors to trigger. I say this because it does not seem to be reproducible with any degree of certainty.
-
@bmeeks Add me to the list of 2.7.0 CE (just downgraded from Plus on Oct 31st) using Snort legacy mode and seeing core dumps. Mine all seems to occur just after a rules update when Snort is restarted, Does not occur with each rules update and restart though. Has occurred 3 times since Nov 1st.
-
@bmeeks said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
Give it some running time. The fault is not always instantaneous for other users. Some are seeing up to 30 minutes of runtime before a fault.
Still nothing to report here for Suricata.
-
@Bob-Dig You're running In-line mode aren't you ?
-
@NogBadTheBad No, legacy.
-
 B bmeeks referenced this topic on
B bmeeks referenced this topic on
-
Update -- I was finally able to experience the Signal 11 core dump on my CE 2.7.0-RELEASE testing machine. It took about an hour for the event to trigger. Seemed to happen when it attempted to kill open states.
I am now building a debug-enabled version of Snort for further testing to see if I can trigger the fault again. Having a debug-enabled version will help track down what's happening. Since the fault happens randomly, this may take a bit to work out.
-
@bmeeks Just another Datapoint regarding Suricata. I let it run over two hours on my VPS with pfSense CE RC on WAN. Hundreds of blocks, still no problem.
-
@Bob-Dig said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
@bmeeks Just another Datapoint regarding Suricata. I let it run over two hours on my VPS with pfSense CE RC on WAN. Hundreds of blocks, still no problem.
Is this with Kill States checked or unchecked on the INTERFACE SETTINGS tab?
-
@bmeeks Checked. The only thing of note, I block only for 15 mins, so right now there are "only" 33 blocks and no snort-rules.
suricata 7.0.2 -
@Bob-Dig Run it "infinete" and you will see :)
-
@Bob-Dig said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
I block only for 15 mins, so right now there are "only" 33 blocks and no snort-rules.
suricata 7.0.2Run it over night, still no problem, will stop it now.
-
@Bob-Dig said in Important Snort and Suricata Package Announcement -- probable bug in Legacy Blocking Module:
Run it over night, still no problem, will stop it now.
Probably, in your case, the second condition (kill states is the main one) is not occurring (considering Bill Meeks theory) so there is no crash ...

-
@fireodo My theory is, it is a snort problem, not suricata. Let's see.