Authenticating Users with Google Cloud Identity
-
Like:
-
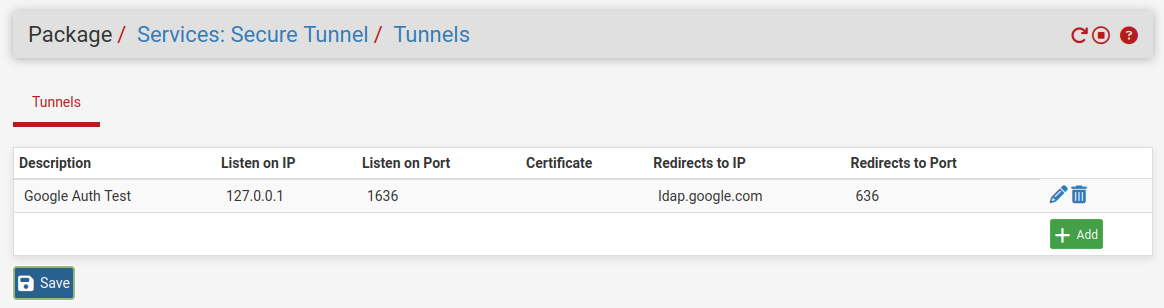
it's a box where you have to choose something but if I choose Default I have a view like yours i.e. the Certificate field is empty. However, even in this way the service does not start
-
Ok so not a certificate issue.
Do you have other STunnel entries that might have misconfig?
Do you have some other service already listening on port 1636?
What happens if you just try to run the command at the CLI:
[24.03-RELEASE][admin@4200.stevew.lan]/root: stunnel [ ] Initializing inetd mode configuration [ ] Clients allowed=54725 [.] stunnel 5.71 on amd64-portbld-freebsd15.0 platform [.] Compiled/running with OpenSSL 3.0.13 24 Oct 2023 [.] Threading:PTHREAD Sockets:POLL,IPv6 TLS:ENGINE,OCSP,PSK,SNI [ ] errno: (* __error()) [ ] Initializing inetd mode configuration [.] Reading configuration from file /usr/local/etc/stunnel/stunnel.conf [.] UTF-8 byte order mark not detected [ ] Compression disabled [ ] No PRNG seeding was required [ ] Initializing service [Google Auth Test] [ ] Initializing context [Google Auth Test] [ ] stunnel default security level set: 2 [ ] Ciphers: HIGH:!aNULL:!SSLv2:!DH:!kDHEPSK [ ] TLSv1.3 ciphersuites: TLS_AES_256_GCM_SHA384:TLS_AES_128_GCM_SHA256:TLS_CHACHA20_POLY1305_SHA256 [ ] TLS options: 0x2100000 (+0x0, -0x0) [ ] Session resumption enabled [ ] Loading certificate from file: /usr/local/etc/stunnel/stunnel.pem [ ] Certificate loaded from file: /usr/local/etc/stunnel/stunnel.pem [ ] Loading private key from file: /usr/local/etc/stunnel/stunnel.pem [ ] Private key loaded from file: /usr/local/etc/stunnel/stunnel.pem [ ] Private key check succeeded [ ] No trusted certificates found [:] Service [Google Auth Test] needs authentication to prevent MITM attacks [ ] OCSP: Client OCSP stapling enabled [ ] DH initialization skipped: client section [ ] ECDH initialization [ ] ECDH initialized with curves X25519:P-256:X448:P-521:P-384 [.] Configuration successful [ ] Deallocating deployed section defaults [ ] Cleaning up context [stunnel] [ ] Binding service [Google Auth Test] [ ] Listening file descriptor created (FD=9) [ ] Setting accept socket options (FD=9) [ ] Option SO_REUSEADDR set on accept socket [.] Binding service [Google Auth Test] to 127.0.0.1:1636: Address already in use (48) [!] Binding service [Google Auth Test] failed [ ] Unbinding service [Google Auth Test] [ ] Service [Google Auth Test] closed [ ] Deallocating deployed section defaults [ ] Cleaning up context [stunnel] [ ] Deallocating section [Google Auth Test] [ ] Cleaning up context [Google Auth Test] [ ] Initializing inetd mode configurationThere you see it fails to start for me because it's already running.
-
Hi @stephenw10
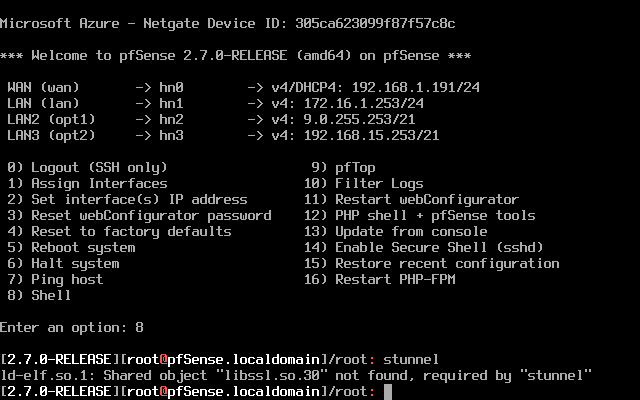
I changed the Listen on Port field from 1636 to 1696 but nothing changed. I ran the stunnel command from the shell and the following error came out:
-
You probably broke the golden rule.
You've installed package(s) that depend on other packages like OpenSSL.
When installing "stunnel", the latest and greatest was put in place. But .... your pfSense 'core' (kernel, system libraries) in not recent or up to date : now you've entered "DDL" or library conflict hell.The golden rules says : before installing and or updating packages, first upgrade pfSense.
The current version is 2.7.2. -
Hi @Gertjan
well I'm sure you're right but keep in mind that when I tried to install stunnel from 2.60 the system told me that it was necessary to upgrade Pfsense and in fact I updated it to 2.70 and in fact after doing this upgrade of PfSense I was It is possible to install Stunnel, but with all the problems you see.
You won't believe it, but before reading your post I went to System / Update again and found 2.7.2 and I said to myself: "But why not try?".Well I did that upgrade and...... STunnel WORKS!!!
-
Great

Now you know what 'golden' is in that rule. -
@Gertjan sure sure I understood hahaha. Thanks and thanks also to
@stephenw10. Now I move forward with the implementation of the captive portal. Tomorrow I will be at the customer's site so... let's hope for the best!
If I have other problems, can I bother you again? Thank you -
Nice! Yup it pulled in the STunnel pkg from 2.7.2 and that won't run in 2.7.0.
Got there in the end.

-
So, here I am again bothering you.
I solved the Google authentication problem with Stunnel and it finally works. At this point I moved on to configuring the captive portal, as the director of the client school wants a captive portal to appear on all the school's PCs when they try to go out on the Internet. I carried out the following steps:-
I set the pf dhcp so that the clients have the pfsense IP as their primary DNS
-
I have checked the filtering rules so that outgoing DNS traffic is not blocked
-
In System / General setup I have set the external DNS to which Pfsense will forward queries via the DNS resolver
-
I created a CA and a related certificate
-
I have enabled and configured the DNS resolver
Enable SSL/TLS Service: I have NOT enabled "Respond to incoming SSL/TLS queries from local clients"
I left all fields as they are and made sure that:
SSL/TLS Certificate: I have given the certificate created above
System Domain Local Zone Type: Transparent
DNS Query Forwarding I checked "Enable Forwarding Mode"
host overraides: I entered the pfsense server data -
I have enabled and configured the captive portal
services /Captive portal/ add / enter Zone name / Save & Continue / tick Enable Captive Portal
in Interfaces I chose the interface on which the captive portal should appear
I set the following 2 timeouts
Idle timeout (Minutes)
Hard timeout (Minutes)
I checked "Enable logout popup window"
In the Authentication section for the Authentication Method field I chose "Use an Authentication backend" and for Authentication Server I chose "ServerGogoel Workspace" configured previously
I checked "Enable HTTPS login" so that the captive portal appears even with https traffic
in HTTPS server name I gave "pfsense server name". "domain" as inserted in the common name (CN) of the CA and the certificate created
SSL/TLS Certificate: I gave the created certificate
The problem is that when the client tries to connect to the Internet the message "Connect to the Wi-Fi network" initially appears but then when I click on Connect the error appears:
pfsense.localdomain has redirected you too many times
ERR_TOO_MANY_REDIRECTSHow can I solve it? Thank you
-
-
@leonida368 said in Authenticating Users with Google Cloud Identity:
host overraides: I entered the pfsense server data
What did you enter there? Why did you add that?
I would start out by just enabling the default captive portal values and make sure that works as expected.
Then add the external auth, check that works.
Then add further settings and check those.
-
@stephenw10 I deleted the pfsense data from Host Overrides and the DNS resolver still works anyway.
I created a captive portal giving the default values and it works, but it only works on http which is absolutely not needed -
It redirects to an http login?
-
yes
-
And just enabling https login causes an error?
-
@stephenw10 said in Authenticating Users with Google Cloud Identity:
And just enabling https login causes an error?
Reply
yes
-
Same redirect error?
Anything logged?
-
@leonida368 said in Authenticating Users with Google Cloud Identity:
Enable SSL/TLS Service: I have NOT enabled "Respond to incoming SSL/TLS queries from local clients"
That option is only usable if you control every LAN client, so you can set up each client to use DNS over TLS on port 853. That wasn't even possible with Windows devices nort so long ago.
This option is not usable for a captive portal, where you do not control the connecting devices.@leonida368 said in Authenticating Users with Google Cloud Identity:
I checked "Enable logout popup window"
You don't need it.
Must users, yourself included, have already disabled those nasty popup windows ages ago.
So that windows never (or very rarely) pops up.@leonida368 said in Authenticating Users with Google Cloud Identity:
I checked "Enable HTTPS login" so that the captive portal appears even with https traffic
in HTTPS server name I gave "pfsense server name". "domain" as inserted in the common name (CN) of the CA and the certificate created
SSL/TLS Certificate: I gave the created certificate"https" login is mandatory if you want a portal that isn't flagged as suspicious (or worse) on every client connecting to the portal. Classic "http" is pretty much gone these days.
To have "every" browser trust your certificate, you can't make your own. Nobody trusts you ^^
You to get a certificate from a known trusted Certificate Authority.
That's why where the pfSense package ACME comes in handy : it will 'arrange' a trusted certificate for you. The certificate will be free of charge, will get renewed every xx days, with you doing nothing.
And here it comes : Before Lets-encrypt creates and signs a certificate for you, you have to proof that you own (actually : rent) the domain name.
Maybe your school already has its own domain name ?
And maybe the registrar used support one of the "DNS API" methods that acme offers ?
If so : declare (example) this domain : "portal.your-school-domain-name.tld" and set up acme to it will ask a cert for this sub domain. Use this domain like this :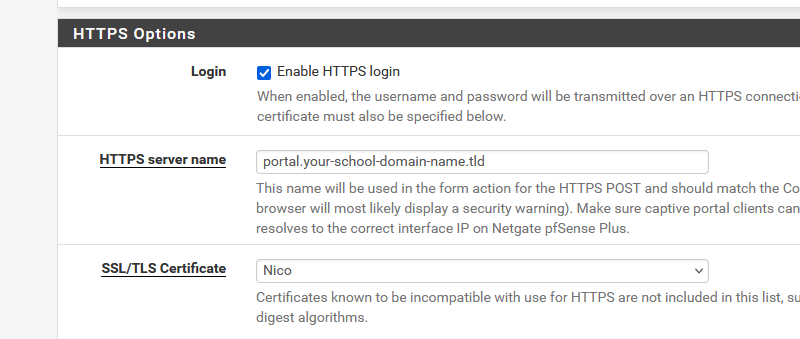
Or maybe they already have a wildcard certificate for the your-school-domain-name.tld domain ? You can use that also, as that will work for pfsense.your-school-domain-name.tld and portal.your-school-domain-name.tld and printer.your-school-domain-name.tld etc etc .
"Nico" is the name of the acme account where I've set up the cert request for "portal.your-school-domain-name.tld".
Place also a domain override under the Resolver, at the bottom :
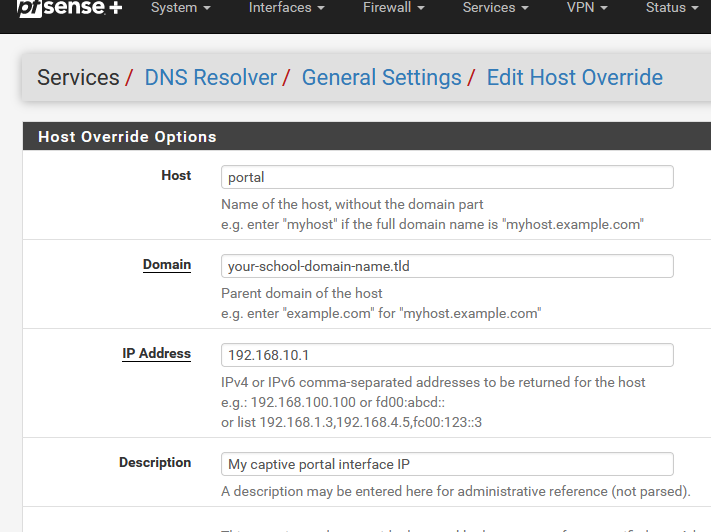
and now you have done everything that is needed to create a https web server, as that is what the captive portal login page server actually is (should be).
Btw : you can also buy a cert from a cert signing company, as we did all before. Upload the cert into the pfSense cert manager, and select it on the captive portal's settings page.
Now the clients will connect to the login page web server with a valid, trusted certificate, and everything will work without any issues.
Btw : this step isn't much different as building your own web server.
In the past, you started a web server, threw in a bunch of html files, later on PHP and whatever, but these days you have to get your hands on a valid certificate, and place it in the web serer config files. Without a cert : no https .....
Not a big issue, as a web server on the Internet means : you have a domain name already. So arranging a cert is just another admin job.
A captive portal isn't a public web server, but you still need to own a domain name or sub domain name. -
This post is deleted! -
I can't reply, I always go to spam