Switch interface for gui access
-
Hello together
I have a pfsense setup with multiple networks:
- WAN (DHCP), igb0
- LAN (192.168.0.1/24), igb1
- Management (192.168.1.1/24) -> VLAN 2, igb2
- Server (192.168.2.1/24) -> VLAN 10, igb2
The GUI is currently accessible via the LAN network. How can I change it so that access is only possible via the management network and not via any other network?
Do I have to change the interface, is there a drop-down field where I can select the desired interface or do I have to do this painstakingly via firewall rules? If so, where and how do I set this?
Thanks for your help
-
@ff101
Generally it's recommended to use the LAN for accessing the pfSense webGUI. You can rename the LAN interface if you want.If you want to prohibit access from LAN, however, you must disable the Anti-lockout rule in System > Advanced > Admin Access.
Additionally you have to add a block rule for the web configurator port to all interfaces you want.
Best to do this with a floating rule with Quick checked. You can assign a single rule to multiple interfaces, so you don't need to create a rule on each interface. -
Thank you @viragomann . That helps me a lot.
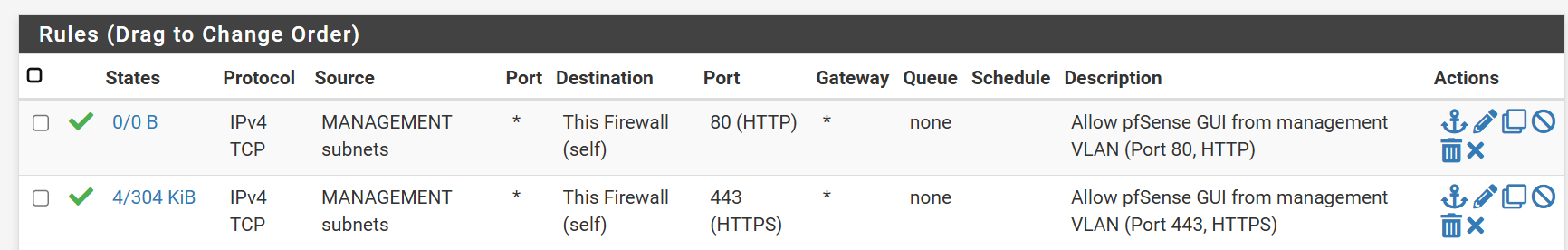
I have now created two firewall rules to allow access from the management network. This is already working perfectly.
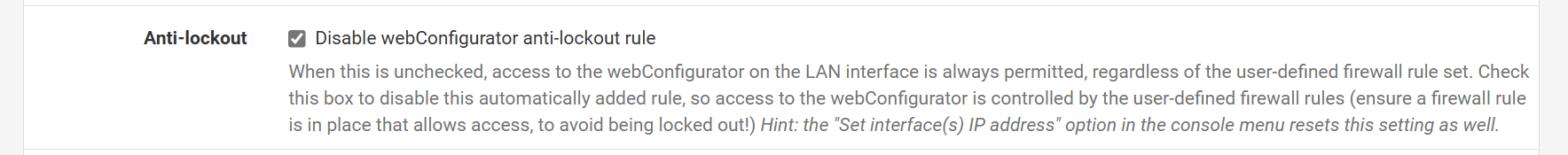
I have deactivated the lock-out rule and it no longer appears under Firewall / Rules / LAN.
Unfortunately, however, I am not able to prevent access from the LAN. I have created a new floating rule and tried the destination with "This Firewall (Self)", but also with the desired IP address (192.168.0.1). I have also tried different protocols (Any, TCP).
What am I doing wrong here?
-
@ff101
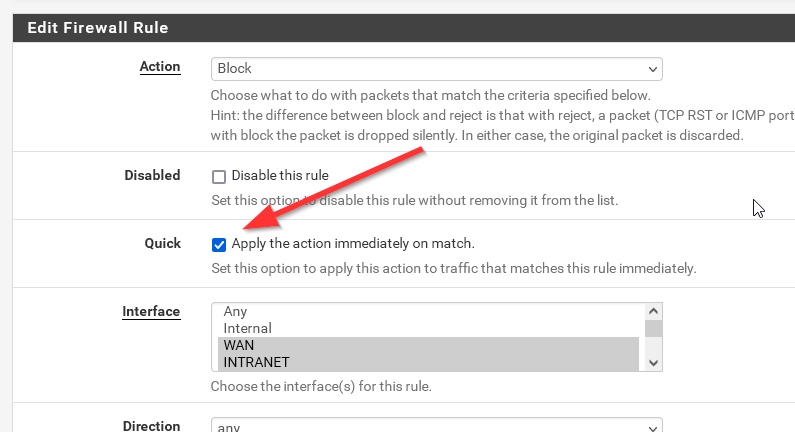
You have to check "Quick" in the floating rule.
Also remember to flush the states then before testing.
-
@ff101 you sure you want such a rule in floating.. That would block access to anything.. dns, ntp, etc. those are services you might want to use on pfsense..
Unless your doing an outbound rule, I prefer to put the rules on the specific interface directly.. I find this easier - just looking specific at the interface I can see what is allowed or not - without having to also look in the floating rule tab.
-
@johnpoz said in Switch interface for gui access:
you sure you want such a rule in floating.. That would block access to anything.. dns, ntp, etc. those are services you might want to use on pfsense.
That's correct. I recommended to block only the web configurator port.
-
This is it!
Thanks @viragomann and @johnpoz.
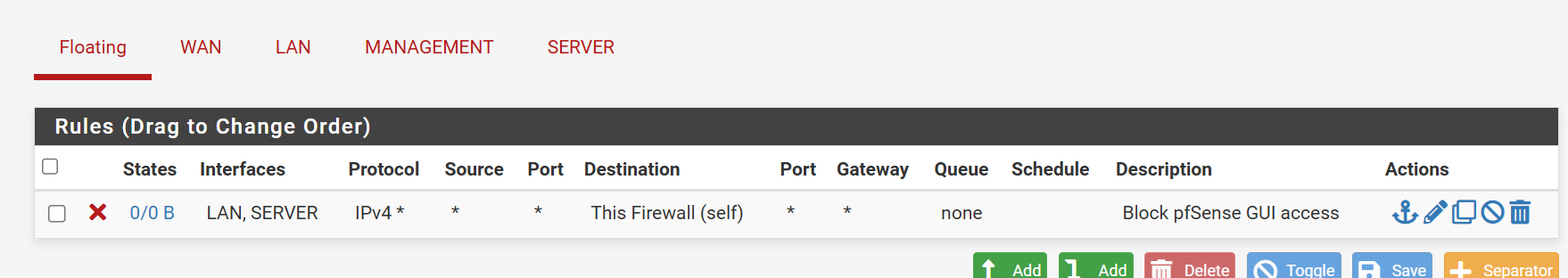
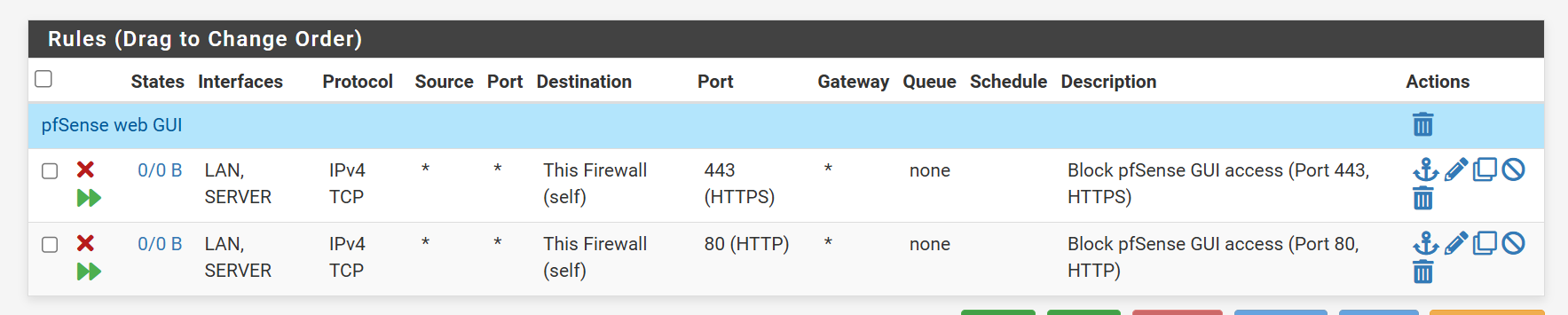
In fact, after I checked the checkbox "Quick", "Apply this action immediately on match" box, it worked.Now only the devices in the management VLAN network have access to the web interface and normal users or servers no longer have access. Port 80 and 443 are blocked for all other networks.
Here is the final configuration, in case anyone needs it:
Floating:
Management:
-
@ff101 you might want to combine them into one rule, just create an alias that has your web gui port(s) - I don't have mine listen on 80 at all. Disabled the redirection option.
And don't forget ssh (normally port 22) if you have ssh enabled on pfsense..