isolated VLAN Internet access
-
@Stingo Sorry, I mis-spoke in the previous post. You'll need to add the allow DNS Before the block rule. The RFC Alias includes the interface address on each subnet, so that gets blocked also.
What's the point of the first rule? -
@Jarhead said in isolated VLAN Internet access:
What's the point of the first rule?
While it is not good, it should allow for local DNS, don't you think? It is clearly doing something.

-
How's your setup?
Pfsense and modem?
Pfsense behind another router?
Double NAT? -
@Jarhead what should the DNS rule look like? I want to be sure I get it right.
The purpose of the first rule is to allow intra vlan communication since the second rule is blocking all the subnets including subnet that the VLAN is on. The first tule allows instructions within the subnet.
My old rule created an alias for the lan and vlan subnets and then gave access to everything but not the vlan subnets. (with the inverted button I understood that !private_nets = let all through except private nets.). That was supposed to replace the all open rule but whenever it was active I lost internet on the vlan.
@the-other nothing fancy. Just PFsense router and TPLink switch. Most of the vlan clients are wireless over a TPlink AP. The vlan works fine until I block the other subnets and the lan in particular. It is almost as if the subnet is getting DNS from the lan. I thought DNS was supposed to be connected through 192.168.20.1 but I obviously am still too uninformed on the mysteries of networking. :-)
-
@Stingo said in isolated VLAN Internet access:
The purpose of the first rule is to allow intra vlan communication
pfsense is not involved in communication between devices on the same network.
That rule should really allow clients to access dns on pfsense IP on that vlan though - but if your clients are pointing to a IP for dns that is on another network of pfsense your block rfc1918 rule would prevent that.
Here is example locked down rules for an interface that might be helpful
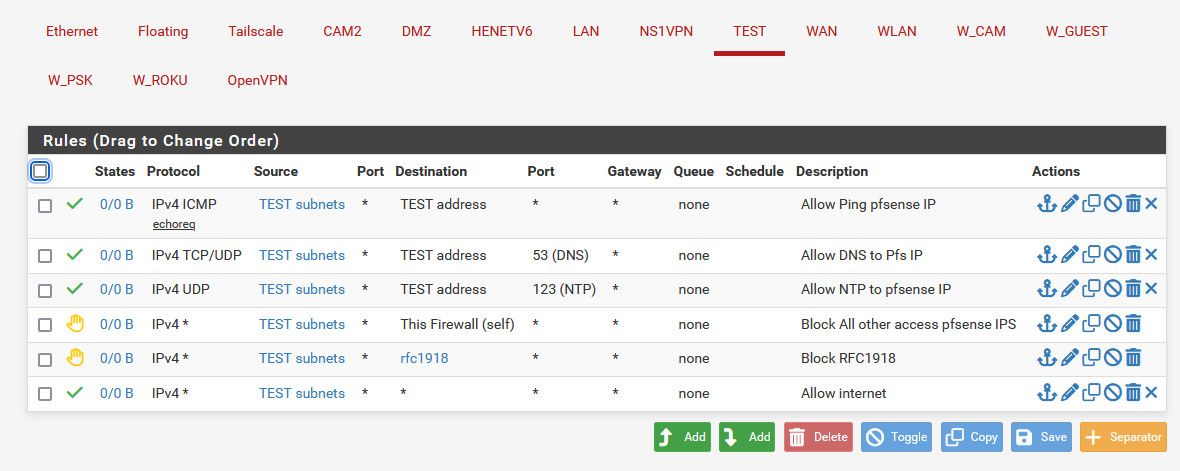
The rules description say what the rule does.
The block rule there to pfsense IPs "this firewall" prevents say access to the pfsense web gui on the public wan IP, which would be allowed by the last rule that is any any to allow internet access.
-
@johnpoz This is extremely helpful. Thank you very much.
I understood that if I tell the firewall on VLAN20 "dont allow any calls to these private subnets" and the private subnets include the VLAN20 subnet then I need a rule allowing the VLAN20 subnet to the the VLAN20 subnet first. Then again I am just trying to dig through a ton of of stuff online to get to the gold. :-)
Netgate has good notes but they could be better.
Thanks again.
-
@Stingo yeah if you block all rfc1918 it would block access to pfsense IP address that is rfc1918.. So yeah you need rule(s) above the block rfc1918 rule that allows access to pfsense address for say dns.
Rules are evaluated top down, first rule to trigger wins, no other rules are evaluated.. So while yes your rule there on top should allow access to pfsense IP on that vlan.. It a bit overboard for allowing access to 1 IP, the rule should just be to pfsense address.
But your saying that rule isn't even working? Which would make no sense unless your clients were talking to some other IP on pfsense or another network for dns?
-
@johnpoz the rules that you shared above worked fantastically. I think the problem was in the rules that I did not have for NTP or DNS. I hope you know you probably helped prevent a divorce or a murder since I put my wife on a separate vlan so she had lost internet connection. She was getting damn scary.
One question since I am trying to learn. Why the ping rule? Why does the vlan need to ping echoreq the vlan address?
-
@Stingo its there for ability to test.. if wanted to actually make sure you could talk to pfsense.. Not something you need, but I like to be able to validate I can actually talk to my router/dns etc..
-
@johnpoz good idea. I think I'll keep the rule. Thanks again. Most of the fun so far has been learning with PFSense. I just wish there were clearer guides out there.