Firewall and routing for my LAN
-
@SteveITS I've got two interfaces on pfsense, LAN (192.168.56.3 | pfsense IP) and LAN 2 (10.45.0.3 | for the 5g and ue)
10.45.0.1 is the 5g networks IP from the tunnel it creates (ogstun), has a 192.168.56.116 IP aswell on the enp0s3 adapter
10.45.0.2 is the user equipment IP from the tunnel it creates (uesimtun), has a 192.168.56.115 IP aswell on the enp0s8 adapter
192.168.56.121 is the FTP machine's IP and only has one enp0s8 adapterive allowed all traffic flow in the firewall rules on both interfaces from LAN to LAN2. With this, i can monitor the .115 to .116 connection and response (user and 5g) and can monitor the 10.45.0.2 to .121 (user to ftp connection) in the pcaps.
Since im able to monitor these connections with the created interfaces, i assumed i can configure a specific rule that will allow/reject the user to ftp traffic.
I have ip routes on the individual machines for this communication to work before i started using pfsense, i am using pfsense for a firewall and routing solution so that i can get rid of the ip routes on the individual machines, monitor the traffic flow and allow/reject traffic based on the IP's in the firewall rules. But until now i can only monitor the traffic, if i get rid of the routes on the individual machines, i cant connect the user to the ftp machine and cant create specific rules to enable the flow, not too sure where im going wrong
-
That should work as long as all devices are using pfSense as their default route. I suspect they are not though.
-
@stephenw10 I've tried using pfsense 192.168.56.3 IP as the default for each machine, but no luck.
If i use the pfsense IP as the default gateway on each machine, do i need to configure static routes on pfsense similar to how I was using the ip routes on the each individual machine for the traffic to flow again?
Because once i add the default gateway and remove the ip routes i had on the machines for the communication before, the user machine cant access the ftp machine anymore from the 10.45.0.2 IP to the 192.168.56.121 IP
-
@kramnoraa Did firewall rules on LAN2 allow access to that server on LAN?
Does any firewall on the FTP server allow access from the other subnet?
If two devices on two pfSense networks both use pfSense as their gateway then the routing is all automatic and you just need firewall rules to allow it.
Allow ICMP and then test with ping/traceroute.
-
@kramnoraa said in Firewall and routing for my LAN:
10.45.0.1 is the 5g networks IP from the tunnel it creates (ogstun), has a 192.168.56.116 IP aswell on the enp0s3 adapter
10.45.0.2 is the user equipment IP from the tunnel it creates (uesimtun), has a 192.168.56.115 IP aswell on the enp0s8 adapter@kramnoraa said in Firewall and routing for my LAN:
Because once i add the default gateway and remove the ip routes i had on the machines for the communication before, the user machine cant access the ftp machine anymore from the 10.45.0.2 IP to the 192.168.56.121 IP
I think, I got you wrong first. So forget the bridge.
I don't know, how the tunnel between the user equipment (uesimtun) and the 5g networks (ogstun) work. But I can imagine, that the user equipment sets the default route to the 5g, when connecting.
This means the connection to the FTP would be directed across the 5g. Maybe this is an issue.For proper routing, the 5g would have to masquerade the source IP.
However, it's not clear to me, how the 5g goes to other subnets / the internet. You wrote, you gave pfSense an IP in LAN2 (10.45.0.3). But if this is just a tunnel network between the 5g and the user, I don't expect, that there goes any traffic to the pfSense LAN2 interface.
Maybe you can clarify the function of the tunnel. -
@viragomann For the internet, yes, the route goes through the 5g network, but for the FTP there's no such route to go through the 5g network, the source IP is the user equipment's tunnel IP thats created when i build the equipment, 10.45.0.2 directly to the FTP server, 192.168.56.121, this is confirmed with a tcpdump and since the connection only works when i create a route on the user machine to direct all traffic to the FTP's IP via the user equipment tunnel
The pfSense's IP in LAN is 192.168.56.3, the LAN2 IP in pfsense is 10.45.0.3.
To my knowledge as of yet, the connection should go from the user to 5g network and then to the FTP server but since i'm not too sure how to do that, i'm sticking with the user equipment connecting directly to the FTP server, with the user equipments tunnel IP, 10.45.0.2 > 192.168.56.121
How can i allow/block the ftp or icmp traffic from 10.45.0.2 to 192.168.56.121 with no routes on the machines and only routes on the web gui? is this possible
-
@SteveITS I'm able to monitor the packets from LAN2 to LAN, cant control access
There is no firewall on the FTP server, ufw is disabled and i'm only using the pfsense as a firewall
I've tried using the default gateway on each individual machine but not sure why it isn't working, will try it again now
-
@kramnoraa said in Firewall and routing for my LAN:
For the internet, yes, the route goes through the 5g network, but for the FTP there's no such route to go through the 5g network
And how can the machine differ this without a specific static route for the FTP?
If the the default route goes to the 5g, without specific routes, it will send traffic to all destinations outside of its own subnet to the default gateway, which is the 5g.How does the 5g go to the internet? Does it have a certain tunnel on its own or does it use 192.168.56.3 as upstream gateway?
-
@viragomann I've added static routes on both the user machine and the ftp machine to allow traffic between them based on their IP's, since the traffic gets sent to the 5g network by default, maybe i need to specify a route on the 5g machine itself to forward traffic to the ftp machine's IP ?
The 5g network when ran, creates a tunnel 'ogstun' that handles the traffic for the 5g network, from the open5gs docs, i've added this rule ' sudo iptables -t nat -A POSTROUTING -s 10.45.0.0/16 ! -o ogstun -j MASQUERADE ' when building the network for internet access i believe ( i might be wrong).
Would i add a rule somewhat like ' sudo iptables -t nat -A POSTROUTING -s 10.45.0.0/16 -d 192.168.56.121 -j ACCEPT ' to allow traffic from the user equipment, to the 5g network and then to the ftp server? instead of the user equipment's tunnel IP, 10.45.0.2 directly accessing the ftp server with the static route on the two machines
-
@kramnoraa said in Firewall and routing for my LAN:
I've added static routes on both the user machine and the ftp machine to allow traffic between them based on their IP's,
The static route on the user machine should be all you need.
since the traffic gets sent to the 5g network by default, maybe i need to specify a route on the 5g machine itself to forward traffic to the ftp machine's IP ?
We have to know, how the 5g goes out to get further. I requested this above.
Can you post its routing table, when the 5g network is running? -
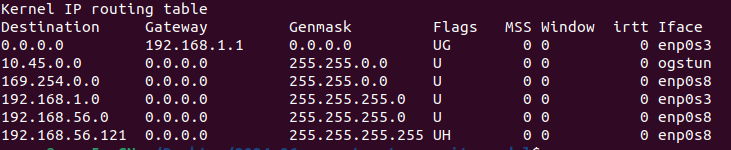
Routing table for the machine thats running the 5g network ^
-
@viragomann
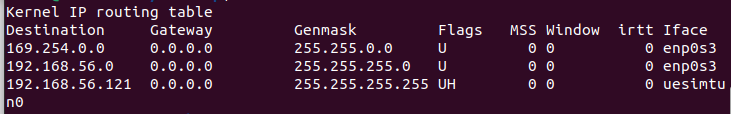
Routing table for user equipment machine ^ -
@kramnoraa said in Firewall and routing for my LAN:
Routing table for the machine thats running the 5g network ^
Why is the default gateway 192.168.1.1? You didn't mention this subnet till now.
Shouldn't it rather be 192.168.56.3?Also I don't get, why the user machine has a route for the FTP bound to uesimtun, since it should have an IP in the LAN on enp0s3.
-
@viragomann I want the communication for the ftp from user machine to go via the uesimtun0 which has an IP of 10.45.0.3, this would mean that the connection is going through the 5g network and not directly from the user machine to the ftp machine (its using the generated tunnel). Thats why im routing all traffic from the user to ftp machine with the rule 'sudo add ip route 192.168.56.121 dev uesimtun0' on the user machine and 'sudo ip route add 10.45.0.3 dev enp0s8' on the ftp machine, only with these static routes on the machines, i can access the ftp from the user machine, and its using the 10.45.0.3 IP rather than its host only 192.168.56.115 IP to communicate with it, confirmed with a tcpdump
-
@kramnoraa said in Firewall and routing for my LAN:
I want the communication for the ftp from user machine to go via the uesimtun0 which has an IP of 10.45.0.3, this would mean that the connection is going through the 5g network and not directly from the user machine to the ftp machine (its using the generated tunnel).
Okay, if this is what you want, you will not get rid of the static routes, as long as you don't logically separate the FTP from use machine and put it into another network segment.
The static route on the FTP is needed as well then to avoid asymmetric routing.
-
@viragomann Alright, initially my plan was to get rid of the static routes that i created on each machine except the 5g machine for security simulation purposes, and let pfsense handle all the routing. Maybe this isn't possible, although it should be i assume?
Regardless, im not able to control the traffic on the firewall (i want to allow/block ftp access from user machine) even with these static routes on each machine. I am only able to monitor the connections in the packet captures, but no access control
Any recommendations on how I can do this ?
-
@kramnoraa said in Firewall and routing for my LAN:
@viragomann Alright, initially my plan was to get rid of the static routes that i created on each machine except the 5g machine for security simulation purposes, and let pfsense handle all the routing. Maybe this isn't possible, although it should be i assume?
As I implied above, just put the FTP into another network segment. It's a virtual machine and a virtual network, so this wouldn't be a big deal.
-
@viragomann Thank you for your prompt replies.
Okay i see, sorry i'm just a bit confused as to why putting the FTP into another network segment other than the .56.0/24 subnet would change things, bit lost as to how this would help me have access control using pfsense
right now the user machine is using 10.45.0.3 and 192.168.56.115
the ftp is on 192.168.56.121so if i move the ftp to 192.168.57.121, how would this change let me have control over the traffic flow ?
-
@kramnoraa said in Firewall and routing for my LAN:
Okay i see, sorry i'm just a bit confused as to why putting the FTP into another network segment other than the .56.0/24 subnet would change things, bit lost as to how this would help me have access control using pfsense
This doesn't help to control the access, but to get rid of static routes.
If the traffic passes pfSense anyhow, but not tunneled, you should be able to monitor and control it.
However, the pfSense IP in the tunnel subnet might be pretty useless for this, as mentioned above already.Since you don't clarify, how the 5g work, I can only make assumptions on this.
I guess, that the 5g uses 192.168.56.3 as default gateway and do masquerading on upstream traffic. All already mentioned.
This would mean, that when you access the FTP from the user machine (with routes), pfSense is seeing FTP access from the 5g with the source IP 192.168.56.116.
Don't you see this traffic? -
Hmm, this is a confusing thread!

Unclear exactly what you're trying to do here.
Whatever it is I'd be amazed if you're not hitting some asymmetric routing issues. I agree it would be much beter to have the FTP server in a different subnet so you can correct route to it and filter traffic.