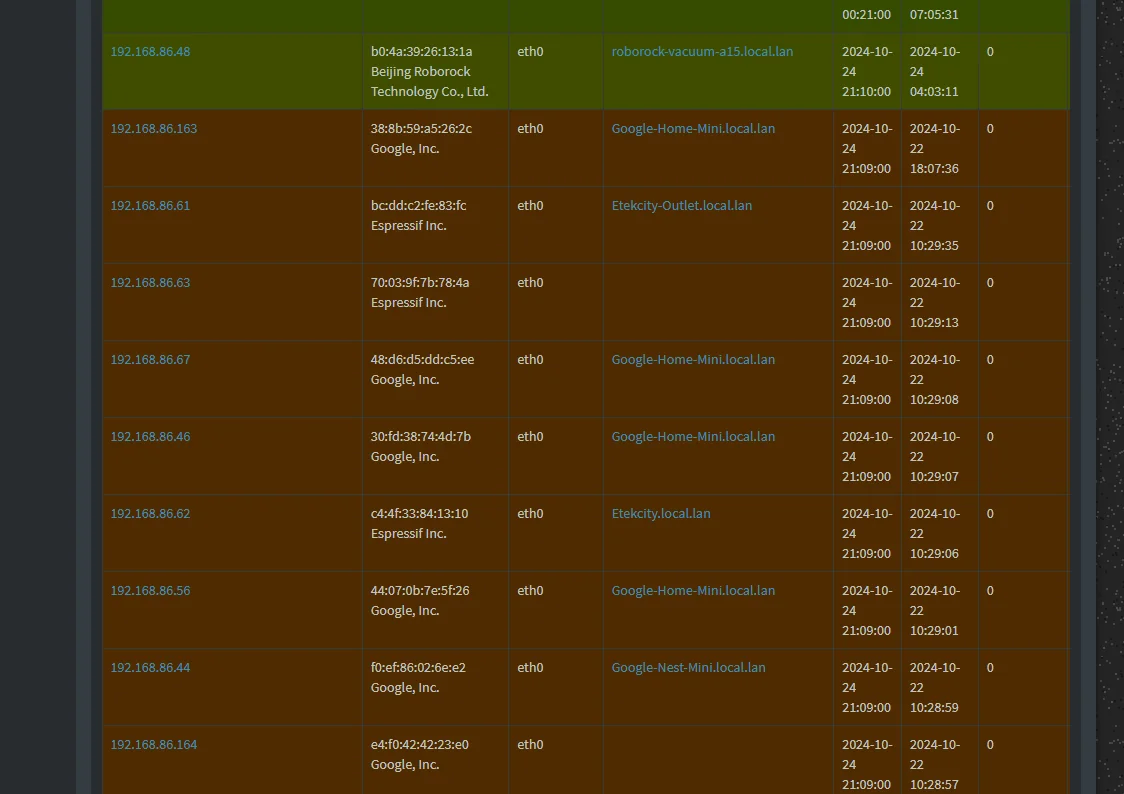
Redirected all DNS to pihole using pfSense. Pihole still showing some hosts as not using the DNS ?
-
@abesh
You should rather redirect any traffic to pfSense. So it's treated by the DNS resolver and host overrides will take place, while other requests are forwarded to the pihole from the Resolver. -
@abesh Seems your setup is done correctly. Have you considered that the IP of those sessions might be hardcoded into the missing device?
Otherwise it is likely some unknown DNS over HTTPS server you are not blocking - or vendor specific nameresolution method - in play. -
@keyser That was my thought process as well. Seems like killing DoH is like playing whack-a-mole !!!
-
@abesh
Hardcoded DNS IP will be redirected anyway.
DoH can be an issue. You should consider to block DoH using pfBlockerNG. -
@viragomann Already blocking in pihole. But I have noticed a lot of these servers running on either cloudfront or google or amazon ec2 instances...
-
@abesh said in Redirected all DNS to pihole using pfSense. Pihole still showing some hosts as not using the DNS ?:
@Raffi_ Yup, officially supported by Pihole. Here's the documentation : https://docs.pi-hole.net/guides/dns/unbound/
Thanks for the tip. I learned something new. I figured it would be installed on the OS itself via apt. I just never thought about doing it that way since pfsense already had it out of the box. I may one day have to try this since I'm currently unable to run pfsense at my home setup.
-
@Raffi_ Hit me up if you decide to run this. I will share my optimized unbound config file with you :) You can just replace the existing unbound config and should be good to go :)
-
@abesh said in Redirected all DNS to pihole using pfSense. Pihole still showing some hosts as not using the DNS ?:
Already blocking in pihole.
DoH (https) will not go to the pihole. It will go straight to the default gateway, which is pfSense, I guess.
Edit:
So you block the resolution of DoH hosts on the pihole?
OK, but blocking it on pfSense would be more reliable, if a device goes to the IP directly. -
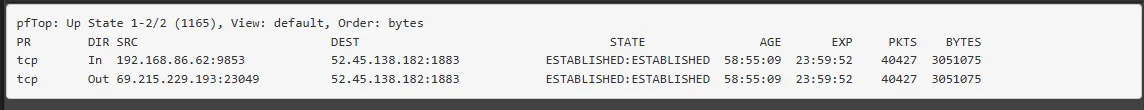
@viragomann It was hardcoded application IP endpoint I was reffering to - not hardcoded DNS. Aka: The APP on the device just contacts the IP directly - no DNS resolution beforehand.
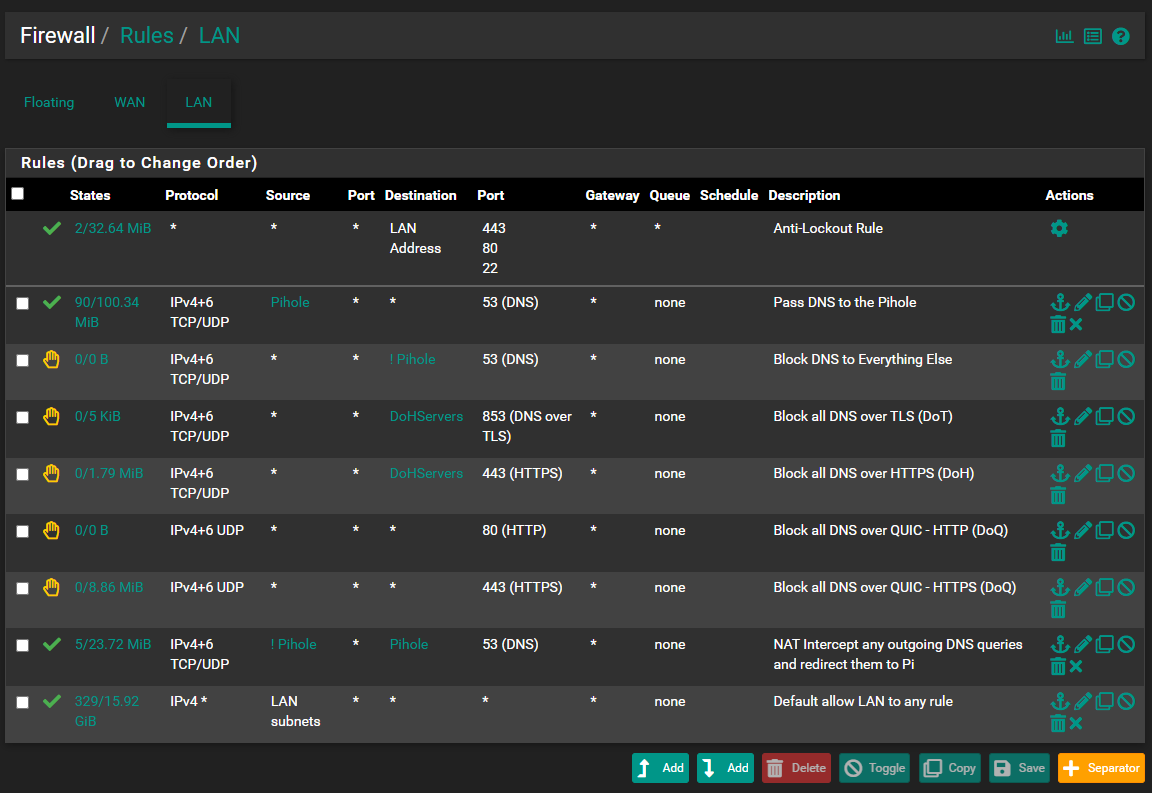
DoH is a game of Whack a Mole - as is DoT even though most of them can be blocked by blocking port 853.
Unfortunately this is where everything is going (in the name of privacy - even though it is mostly used by vendors to make sure they have the revenue of selling your data rather than your ISP)
-
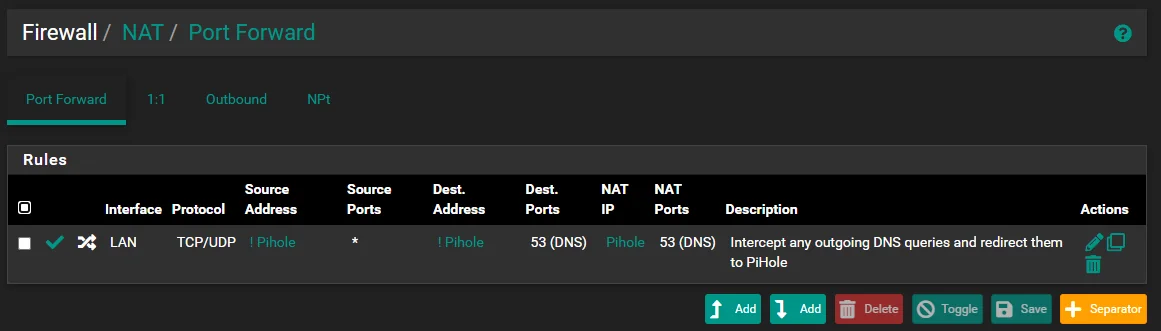
@viragomann I think it will, if it needs to look up hostnames :) I have two lists (you can see one on the Rules screenshot). I block IPs of DoH servers in pfSense and block domains in piHole.
-
@keyser said in Redirected all DNS to pihole using pfSense. Pihole still showing some hosts as not using the DNS ?:
It was hardcoded application IP endpoint I was reffering to - not hardcoded DNS. Aka: The APP on the device just contacts the IP directly - no DNS resolution beforehand.
Got it. There is not really much you can to on the DNS to prohibit this, if it's not used then.
-
@viragomann @disi1 @AndyRH @keyser So from debugging this a bit it seems that these might be showing up as "not using pihole" because maybe they send their DNS queries to pfSense which is then forwarded to pihole. Pihole thinks it is coming from pfSense and not the device itself. How do I configure pfSense so that it also send the device hostnames when forwarding the request ?
-
@abesh said in Redirected all DNS to pihole using pfSense. Pihole still showing some hosts as not using the DNS ?:
@viragomann @disi1 @AndyRH @keyser So from debugging this a bit it seems that these might be showing up as "not using pihole" because maybe they send their DNS queries to pfSense which is then forwarded to pihole. Pihole thinks it is coming from pfSense and not the device itself. How do I configure pfSense so that it also send the device hostnames when forwarding the request ?
This is beginning to sound like an Abbott and Costello sketch. I hope no one queried who's on first. Sorry bad joke.
Have you tried my original suggestion of allowing pfsense to run unbound and then point pi-hole to it?
-
@Raffi_ That was actually the first setup that I ran and I moved on to this :)
-
@abesh And we're still talking about brown or red entries? I saw all brown on your screen shot.
And to be clear, you had the same exact issue with that original setup which prompted you to try something else or were you trying to address something else? In my experience there might be a couple of devices which do not use pi-hole. How many exactly are you noticing?
-
@Raffi_ Yeah, let me wait and observe a bit.
-
@abesh said in Redirected all DNS to pihole using pfSense. Pihole still showing some hosts as not using the DNS ?:
Pihole thinks it is coming from pfSense and not the device itself.
@Raffi_ said in Redirected all DNS to pihole using pfSense. Pihole still showing some hosts as not using the DNS ?:
Have you tried my original suggestion of allowing pfsense to run unbound and then point pi-hole to it?
I don't expect, that this makes any difference on the pihole seeing requests coming from pfSense.(?)
@abesh
If you want to see the origin client IPs, you have put the pihole into a separated network segment on a different interface, so that you can get rid of the masquerading rule. -
@viragomann That makes a lot of sense. Thank you :)
-
@viragomann Would I get anything else other than local domain name resolution for forwarded queries if I move the pihole to a different subnet ? If not I would just like to keep it as is :)
-
@abesh
There is no benefit else, I can think of at the moment.