host in alias used by firewallrule refuses to work
-
I have a VPN gateway and use an alias (VPN_Clients) to send hosts to that gateway, it works properly.
But when adding one specific host to that alias it doesn't work for that one host, the other in the alias do get to the VPN gateway
When i remove the alias from the firewall rule (and send all my hosts using the "any" as source setting) it will use the VPN gateway. (all the hosts, also the one not working in the alias)Troublehhooting so far;
new IP for affected host (UTP connected)
switched to WiFi adapter (turned NIC off)
created new alias, tested with the one host in it, akso doesn't work
reset ARP states -
@a1aba Create a rule for just that IP and see if it matches?
https://docs.netgate.com/pfsense/en/latest/troubleshooting/firewall.html#new-rules-are-not-applied
-
@SteveITS thanks for helping!
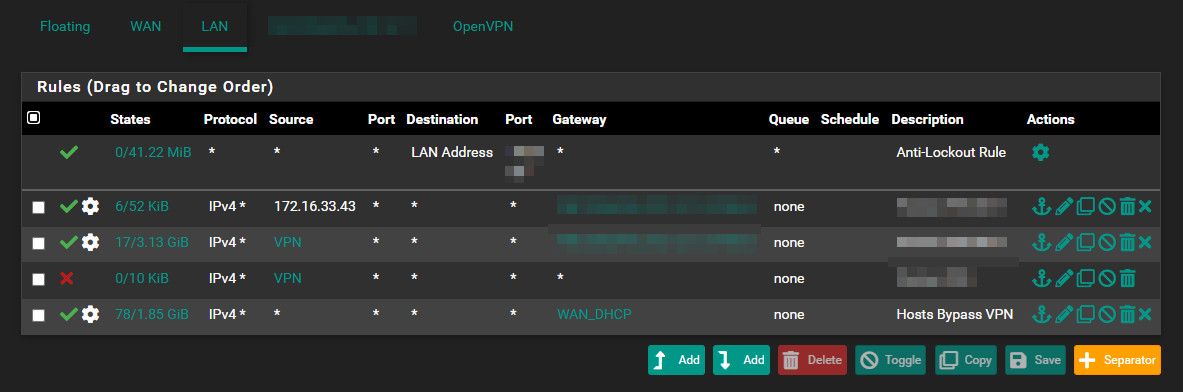
created a separate rule and moved it to the top position (below anti lockout rule) and reloaded the rules
same problem -
@a1aba Then either it’s not being loaded (see doc) or it isn’t matching. IPv6? UDP vs TCP?
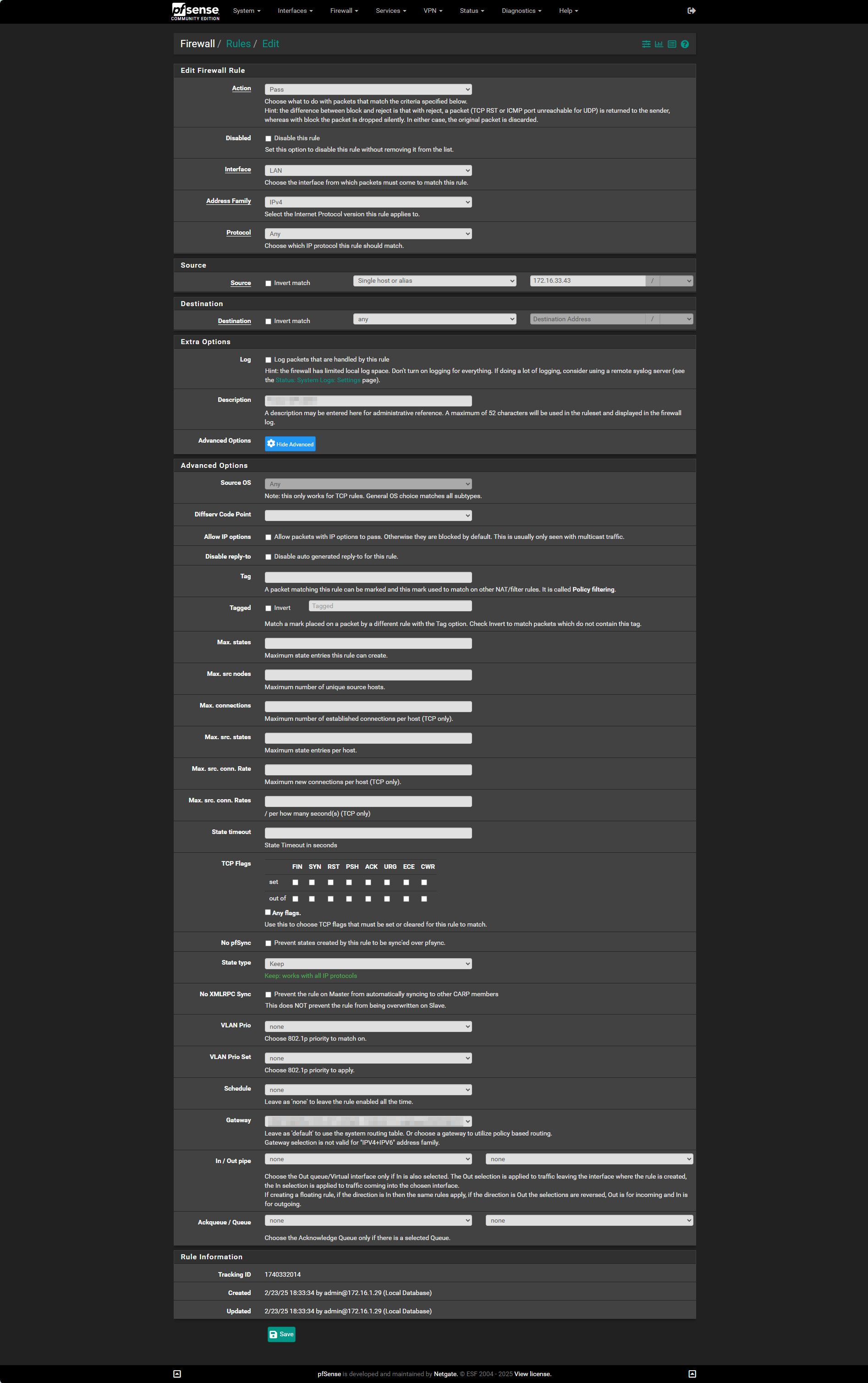
Show your rule?
-
-
@a1aba On the LAN page of rules does it show 0/0 or have a count? (tells you if it's matching)
Does a filter reload show any errors?
Is IPv6 in use?
-
@SteveITS
No IPV6 in use (turned it off on client NIC) -
@a1aba The “6/“ means 6 open states/connections for that rule. In theory you can click on it and see them but it doesn’t seem to work for me.
So, why do you think it’s not working?
-
@SteveITS i check the client using ipchicken.com or whatsmyip.org or similar sites to check the IP shown there.
All other hosts (used in the alias) get the VPN IP but this client always gets my true external IP
Only when changing the firewall rule so all trafic is routed to the vpn gateway, this client will get a VPN IPthat is not working as i expect it
-
So if fails both adding a specific rule or adding it to the alias?
You are just adding that host as an IP address to the alias?
Do you have any floating rules that might be passing that client?
-
@stephenw10 @a1aba Besides some other rule superseeding this one, could it be sticky states playing into this?
If so, going to Diagnostics > States and filter on that IP 172.16.33.43 and then kill all states. Or go all in and simply kill all states for all connections...Another possibility could be multiple IP's for that client? Does it have more than one port, or wifi connected in parallell?
-
@stephenw10 Yes, it fails both adding a specific rule or adding it to the alias
it's added by it;s IP address and there is no floating rule -
@Gblenn killed all states earlier, no solution
only 1 connection active on that host
for troubleshooting tested it on NIC and WiFi (perhaps MAC related, but the same issue) -
@a1aba said in host in alias used by firewallrule refuses to work:
@Gblenn killed all states earlier, no solution
only 1 connection active on that host
for troubleshooting tested it on NIC and WiFi (perhaps MAC related, but the same issue)Ok so I suppose it got a different IP on wifi right? And you changed the rule to match the new IP?
Also, when you checked the IP on the host, did you check with ipconfig /all (assuming windows)? I mean an application can generate an additional connection... -
@Gblenn yep, tried it all
strange thing is if delete the alias from the rule and change it to "any" as source it does work and the hosts gets the VPN IP (ipchicken.com to chech that) -
@a1aba said in host in alias used by firewallrule refuses to work:
@Gblenn yep, tried it all
strange thing is if delete the alias from the rule and change it to "any" as source it does work and the hosts gets the VPN IP (ipchicken.com to chech that)Yes that is really strange... and is the result the same if you use "LAN subnet" instead of any as the source?
Btw, do you have IPv6 enabled in pfsense?
-
@Gblenn said in host in alias used by firewallrule refuses to work:
Besides some other rule superseeding this one, could it be sticky states playing into this?
It would be unlikely for a connection to, say, ipchicken.com. A TCP/https connection like that would be new each time you opened or refreshed the page and should use the new rules to create new states.
Open a state by starting a ping. Then check the states to see what rule opened that:
pfctl -vvssThen check the ruleset to see what rule that is:
pfctl -vvsrIt's either not matching your new rule or getting matched by some other rule before it reaches it.
Or it's not loading your new rule at all. Make sure Status > Filter Reload returns clean.
-
OP's screen cap above shows open states on the rule. (I assume the .43 is the desired client IP, didn't reread this thread)
The third rule should block all other traffic as long as .43 is in the VPN alias. (it also has 10kb traffic)
@a1aba Do you have "Do not create rules when gateway is down" checked?
https://docs.netgate.com/pfsense/en/latest/multiwan/policy-route.html#enforcing-gateway-use -
@Gblenn no IPV6 in pfsense and none configured on client
-
@SteveITS said in host in alias used by firewallrule refuses to work:
OP's screen cap above shows open states on the rule. (I assume the .43 is the desired client IP, didn't reread this thread)
The third rule should block all other traffic as long as .43 is in the VPN alias. (it also has 10kb traffic)
@a1aba Do you have "Do not create rules when gateway is down" checked?
https://docs.netgate.com/pfsense/en/latest/multiwan/policy-route.html#enforcing-gateway-useturned the setting on and it worked
deleted the rule for the .43 address and disabled WiFi and enabled the NIC and updated the alias with the NIC ip address and it keeps working nowturned the setting off (it was never on to begin with) again and it keeps on working now