Successful Install on Watchguard Firebox X700!
-
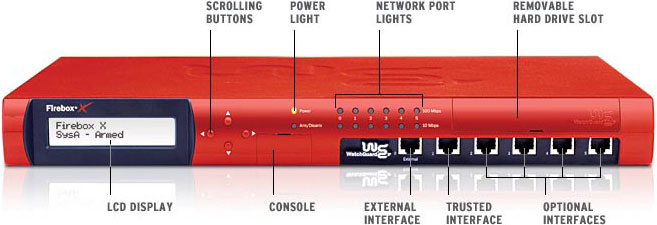
I replaced my Watchguard Firebox X700 with a PC running pfSense, so I wondered if I could make pfSense run on the Watchguard Hardware. IT WORKS!
Steps(more simple than I was expecting)
1. Opened FB(Firebox), Removed CF Card
2. Hooked up a notebook drive to my machine, booted from Live CD (1.2 RC3)
3. 99 Install, accepted all defaults except chose embedded kernel
4. After install was done, took the drive and plugged it into the FB
5. Used the console cable that came with the FB and plugged it into the FB and my Com port
6. Opened HyperTerminal, new connection: BPS: 9600 / Data bits: 8 / Parity: None / Stop : 1 / Flow control: Hardware
7. Turned on FB and it immediately started booting FreeBSD
8. Couldn't mount drive(since installed on different machine), so it asks what you want to mount enter: ufs:ad2s1a
9. Boots up into pfSense just fine!
10. Get into the web interface, "Diagnostics", "Edit File"
11. Load "/etc/fstab"
12. Change the old drive information to the correct one(ad2s1a & ad2s1b).
13. Save (This should fix it asking what drive to mount on boot).Anyway I haven't had a chance to really use it yet, but I will let you know how it performs. This FB also has a VPN/SSL accelerator card, not sure if I can use it in pfSense so if anyone has info about that let me know. Also if anyone has ideas on how to make the display do something that would be awesome! Otherwise everything works!
Here are the hardware specs if anyone is interested:
Celeron 1.2 Ghz
256MB PC133
Intel Chipset
6x Realtek NICs
SafeNet VPN/SSL Accelerator Card (in mini-pci slot)
Open standard PCI Slot
CF card slot
Standard IDE connector
Notebook IDE connector
and bunch of other pins for ports(not sure what they are for)Pic(I will get some of the inside if anyone is interested)
-
Very cool!
Nice to know it works so far!
-
Wow, I'm impressed!
Just wondering, doesn't the Watchguard actually have more feature than pfSense at this point?
I'm not sure that you are actually gaining anything by putting pfSense on that hardware.
What was your reason for doing this?
Thanks!
-
One less watchdog in the wild, that's the reason!
Slap a pfSense sticker on that puppy!!
-
@ flachance - Just because they list a bunch of features doesn't mean they work :D…...We have had tons of problems with these watchguards, we even paid for fireware pro to get all the features available, ie: dual wan, just wanted it to fail to the second wan when the first failed and half the time it wouldn't ever failover even if I completely unplugged the first wan interface....anyway I shouldn't get started on these things. Plus if I did the same stuff with these fireboxes that i'm doing with pfSense I would be paying over $7200/year for licenses(don't get any ideas pfSense creators, btw if pfSense keeps running well, and passes our audits, you can expect a donation from me)!
Anyway, if anyone else is interested in these watchguards, the X500, X700, X1000, and X2500 are all the same hardware, they just have different licenses to allow higher throughput.
-
@ flachance - Just because they list a bunch of features doesn't mean they work :D…...We have had tons of problems with these watchguards, we even paid for fireware pro to get all the features available, ie: dual wan, just wanted it to fail to the second wan when the first failed and half the time it wouldn't ever failover even if I completely unplugged the first wan interface....anyway I shouldn't get started on these things. Plus if I did the same stuff with these fireboxes that i'm doing with pfSense I would be paying over $7200/year for licenses(don't get any ideas pfSense creators, btw if pfSense keeps running well, and passes our audits, you can expect a donation from me)!
Anyway, if anyone else is interested in these watchguards, the X500, X700, X1000, and X2500 are all the same hardware, they just have different licenses to allow higher throughput.
We won't be changing this any time soon but I encourage you to check out our commercial support which does benefit the pfSense community by helping fund commercial projects and such.
-
Could you post a dmesg from that box?
-
???
What's a dmesg?
-
run "dmesg -a" from a command prompt (option 8 from console menu) or ssh in.
-
I assume this is what you are looking for:
Copyright
 1992-2007 The FreeBSD Project.
1992-2007 The FreeBSD Project.
Copyright (c) 1979, 1980, 1983, 1986, 1988, 1989, 1991, 1992, 1993, 1994
The Regents of the University of California. All rights reserved.
FreeBSD is a registered trademark of The FreeBSD Foundation.
FreeBSD 6.2-RELEASE-p10 #0: Tue Jan 15 22:46:42 EST 2008
sullrich@builder6.pfsense.com:/usr/obj.pfSense/usr/src/sys/pfSense_wrap.6
Timecounter "i8254" frequency 1193182 Hz quality 0
CPU: Intel(R) Celeron(TM) CPU 1200MHz (1202.73-MHz 686-class CPU)
Origin = "GenuineIntel" Id = 0x6b4 Stepping = 4
Features=0x383f9ff <fpu,vme,de,pse,tsc,msr,pae,mce,cx8,sep,mtrr,pge,mca,cmov,pat,pse36,mmx,fxsr,sse>real memory = 268435456 (256 MB)
avail memory = 253267968 (241 MB)
wlan: mac acl policy registered
ath_hal: 0.9.17.2 (AR5210, AR5211, AR5212, RF5111, RF5112, RF2413, RF5413)
cpu0 on motherboard
pcib0: <intel 82815="" (i815="" gmch)="" host="" to="" hub="" bridge="">pcibus 0 on motherboard
pir0: <pci 11="" interrupt="" routing="" table:="" entries="">on motherboard
$PIR: Using invalid BIOS IRQ 9 from 2.13.INTA for link 0x63
pci0: <pci bus="">on pcib0
pcib1: <pci-pci bridge="">at device 1.0 on pci0
pci1: <pci bus="">on pcib1
pcib2: <pcibios pci-pci="" bridge="">at device 30.0 on pci0
pci2: <pci bus="">on pcib2
pci2: <unknown>at device 6.0 (no driver attached)
re0: <realtek 10="" 8139c+="" 100basetx="">port 0xd500-0xd5ff mem 0xefefa000-0xefefa1ff irq 10 at device 9.0 on pci2
miibus0: <mii bus="">on re0
rlphy0: <realtek internal="" media="" interface="">on miibus0
rlphy0: 10baseT, 10baseT-FDX, 100baseTX, 100baseTX-FDX, auto
re0: Ethernet address: 00:90:7f:30:e6:73
re0: [FAST]
re1: <realtek 10="" 8139c+="" 100basetx="">port 0xd600-0xd6ff mem 0xefefb000-0xefefb1ff irq 5 at device 10.0 on pci2
miibus1: <mii bus="">on re1
rlphy1: <realtek internal="" media="" interface="">on miibus1
rlphy1: 10baseT, 10baseT-FDX, 100baseTX, 100baseTX-FDX, auto
re1: Ethernet address: 00:90:7f:30:e6:74
re1: [FAST]
re2: <realtek 10="" 8139c+="" 100basetx="">port 0xd900-0xd9ff mem 0xefefc000-0xefefc1ff irq 11 at device 11.0 on pci2
miibus2: <mii bus="">on re2
rlphy2: <realtek internal="" media="" interface="">on miibus2
rlphy2: 10baseT, 10baseT-FDX, 100baseTX, 100baseTX-FDX, auto
re2: Ethernet address: 00:90:7f:30:e6:75
re2: [FAST]
re3: <realtek 10="" 8139c+="" 100basetx="">port 0xda00-0xdaff mem 0xefefd000-0xefefd1ff irq 12 at device 12.0 on pci2
miibus3: <mii bus="">on re3
rlphy3: <realtek internal="" media="" interface="">on miibus3
rlphy3: 10baseT, 10baseT-FDX, 100baseTX, 100baseTX-FDX, auto
re3: Ethernet address: 00:90:7f:30:e6:76
re3: [FAST]
re4: <realtek 10="" 8139c+="" 100basetx="">port 0xdd00-0xddff mem 0xefefe000-0xefefe1ff irq 9 at device 13.0 on pci2
miibus4: <mii bus="">on re4
rlphy4: <realtek internal="" media="" interface="">on miibus4
rlphy4: 10baseT, 10baseT-FDX, 100baseTX, 100baseTX-FDX, auto
re4: Ethernet address: 00:90:7f:30:e6:77
re4: [FAST]
re5: <realtek 10="" 8139c+="" 100basetx="">port 0xde00-0xdeff mem 0xefeff000-0xefeff1ff irq 6 at device 14.0 on pci2
miibus5: <mii bus="">on re5
rlphy5: <realtek internal="" media="" interface="">on miibus5
rlphy5: 10baseT, 10baseT-FDX, 100baseTX, 100baseTX-FDX, auto
re5: Ethernet address: 00:90:7f:30:e6:78
re5: [FAST]
isab0: <pci-isa bridge="">at device 31.0 on pci0
isa0: <isa bus="">on isab0
atapci0: <intel ich2="" udma100="" controller="">port 0x1f0-0x1f7,0x3f6,0x170-0x177,0x376,0xff00-0xff0f at device 31.1 on pci0
ata0: <ata 0="" channel="">on atapci0
ata1: <ata 1="" channel="">on atapci0
orm0: <isa option="" rom="">at iomem 0xe0000-0xe0fff on isa0
ppc0: <parallel port="">at port 0x378-0x37f irq 7 on isa0
ppc0: Generic chipset (ECP/PS2/NIBBLE) in COMPATIBLE mode
ppc0: FIFO with 16/16/16 bytes threshold
ppbus0: <parallel port="" bus="">on ppc0
ppi0: <parallel i="" o="">on ppbus0
sio0 at port 0x3f8-0x3ff irq 4 flags 0x10 on isa0
sio0: type 16550A, console
sio1: configured irq 3 not in bitmap of probed irqs 0
sio1: port may not be enabled
unknown: <pnp0c01>can't assign resources (memory)
speaker0: <pc speaker="">at port 0x61 on isa0
unknown: <pnp0501>can't assign resources (port)
unknown: <pnp0401>can't assign resources (port)
RTC BIOS diagnostic error 20 <config_unit>Timecounter "TSC" frequency 1202733781 Hz quality 800
Timecounters tick every 10.000 msec
Fast IPsec: Initialized Security Association Processing.
ad2: DMA limited to UDMA33, controller found non-ATA66 cable
ad2: 76319MB <toshiba mk8025gas="" ka023a="">at ata1-master UDMA33
Trying to mount root from ufs:/dev/ad2s1a</toshiba></config_unit></pnp0401></pnp0501></pc></pnp0c01></parallel></parallel></parallel></isa></ata></ata></intel></isa></pci-isa></realtek></mii></realtek></realtek></mii></realtek></realtek></mii></realtek></realtek></mii></realtek></realtek></mii></realtek></realtek></mii></realtek></unknown></pci></pcibios></pci></pci-pci></pci></pci></intel></fpu,vme,de,pse,tsc,msr,pae,mce,cx8,sep,mtrr,pge,mca,cmov,pat,pse36,mmx,fxsr,sse> -
BTW whoever fixed the bootup and shutdown beeps in RC4 THANK YOU! I swear this thing would sit and beep for a minute and a half whenever I started it up.
And it seemed to boot a lot faster and is using quite a bit less memory than RC3 was!
-
Hey this is pretty cool. I just found myself a x700 box on bay for cheep and am anxious to give this a try. You start pricing out the newer alix boards, if you can find a good deal on one of these it really makes sense. These seem to have a more powerful CPU.
-
how noisy are these boxes? Anything like the nokia Ip330's? Also, I dont see your crypto card being recognized in your dmesg.
-
how noisy are these boxes? Anything like the nokia Ip330's? Also, I dont see your crypto card being recognized in your dmesg.
Yea i'd be curious to know too. From what it looks like there are only 3 fans in the back. I'm hoping its quite.
Like you, I also noticed nothing about the encryption card in his dmesg log; I'll also be looking to try to figure that piece out when I get my paws on mine.
-
Dunno if you had tried this, but I figured I'd attempt just swapping their CF card out for one with the pfSense embedded image on it. No luck that way. :( (Figured I'd mention it in case anyone else had the same thought.) Guess it's off to scrounge up a spare hard disk.
-
Dunno if you had tried this, but I figured I'd attempt just swapping their CF card out for one with the pfSense embedded image on it. No luck that way. :( (Figured I'd mention it in case anyone else had the same thought.) Guess it's off to scrounge up a spare hard disk.
I wonder if a simple IDE to CF adapter would work?
-
anyone tried a full hard drive install with a IDE adapter, instead of embedded ?
(-edited to add, this works fine)
-
On another platform, yes. The FX5620 comes with a built in IDE-CF adaptor and I plugged a microdrive in then did a full install onto that.
-
Would this work on the older WG FB II?
-
Have a look here http://www.ls-net.com/m0n0wall-watchguard/ (Hardware seems to be a bit weak though and remember you'll need 128 mb ram at least).