Не работает ipcad(не запускается)
-
вот настройки
# # Configuration file for ipcad - Cisco IP accounting simulator daemon. # Copyright (c) 2001, 2002, 2003, 2004, 2005 # Lev Walkin <vlm@lionet.info>. # # Please see ipcad.conf(5) for additional explanations. # Please contact me if you have troubles configuring ipcad. My goal is to make # initial configuration easier for new users, so your input is valuable. # ################## # GLOBAL OPTIONS # ################## # # Enable or disable capturing UDP and TCP port numbers, IP protocol and # ICMP types for RSH output. # # capture-ports {enable|disable} ; # # Enabling this will BREAK Cisco RSH output format compatibility, # increase memory requirements and may slow down traffic processing. # This option takes effect IMMEDIATELY, that is, it can be specified # multiple times, even between interfaces configuration. # This option has NO effect on NetFlow operation (NetFlow always captures # port information). # capture-ports enable; # # Buffers to be used for transferring the data from the kernel, # if applicable (BPF, ULOG). # Using larger buffers may increase the performance but will # affect responsiveness. # # buffers = <number>[{k|m}] ; # # Reasonable defaults are used if this parameter is not set. # ## buffers = 64k; ##################### # INTERFACE OPTIONS # ##################### # # interface <iface>[ promisc ] [ input-only ] # [ netflow-disable ] [ filter "<pcap_filter>" ] ; # OR # interface ulog group <group>[, group <group>...] # [ netflow-disabled ]; # OR # interface ipq [ netflow-disabled ]; # man libipq(3) # OR # interface {divert|tee} port <divert-port># man divert(4) # [ input-only ] [ netflow-disabled ]; # OR # interface file <tcpdump-output.pcap>[ netflow-disabled ]; # # Options meaning: # # promisc: # Put interface into promiscuous mode. # This enables listening for the packets which are not destined for # this host and thus ipcad will count and display all the traffic within # the local network. Note that the interface might be in promiscuous mode # for some other reason. # # input-only: # Use kernel feature of counting only incoming packets. # # netflow-sampled: (DO NOT ENABLE THIS OPTION, unless you have to!) # If the NetFlow export mechanism is used, this option instructs # the interface to supply only one out of N packets to the NetFlow # accounting code, thus lowering the CPU requirements. The value of N # is configured explicitly in a NetFlow configuration section. # NOTE: This option is NOT used to enable NetFlow on the interface, # it just modifies the NetFlow behavior on this interface. # DO NOT ENABLE THIS OPTION, UNLESS YOU HAVE TO! # # netflow-disable: # By default, all interfaces are included into NetFlow accounting. # This option is used to disable NetFlow on a particular interface. # # filter: # Install a custom filter on packets instead of basic # IP protocol filter. Requires libpcap (even if BPF is being used). # May be employed to eliminate CPU overhead on passing unnecessary # data between the kernel and user space (by installing the filter # directly into the kernel). # # NOTES: # * "input-only" directive must be supported by kernel. # Probably, you were noticed about it during the compilation process # if it was not supported. # FreeBSD 3.x and elder kernels do not support this feature. # * ULOG packet source (interface ulog) is supported under # Linux >= 2.4.18-pre8. # You should configure iptables to dump the packet stream # into the appropriate group, i.e.: # iptables -A OUTPUT -j ULOG --ulog-nlgroup <group># Given ULOG groups will be OR'ed together. # * A wildcard (*) may be specified as part of an interface name. # interface vr0 filter "ip and dst net 192.168.0.0/24 and not src net 192.168.0.0/24 and not src port 80"; # # aggregate <ip>/ <masklen>strip <maskbits>; # # Aggregate addresses from the specified network (<ip>/<masklen>), # by AND'ing with specified mask (<maskbits>). # # aggregate 192.168.0.0/24 strip 32; /* Don't aggregate internal range */ aggregate 0.0.0.0/0 strip 32; /* Aggregate external networks */ # # aggregate <port_range_start>[-<port_range_end>] into <port>; # # Aggregate port numbers. Meaningful only if capture-ports is enabled. # #aggregate 1024-65535 into 65535; /* Aggregate wildly */ #aggregate 3128-3128 into 3128; /* Protect these ports */ #aggregate 150-1023 into 1023; /* General low range */ Aggregate ports 80..80 into 0 Aggregate ports 3128..3128 into 0 Aggregate ports 443..443 into 0 ########################## # NetFlow EXPORT OPTIONS # ########################## # # Enable Cisco NetFlow export method. # NetFlow uses UDP to feed flow information to the receiver. # If the destination is not specified, NetFlow is disabled. # # netflow export destination 127.0.0.1 9996; netflow export version 5; # NetFlow export format version {1|5} netflow timeout active 30; # Timeout when flow is active, in minutes netflow timeout inactive 15; # Flow inactivity timeout, in seconds netflow engine-type 73; # v5 engine_type; 73='I' for "IPCAD" netflow engine-id 1; # Useful to differentiate multiple ipcads. # The following option is enabled by the "netflow-sampled" interface flag. #netflow sampling-mode packet-interval 10; # 1 out of 10 packets accounted # DO NOT ENABLE THIS UNLESS YOU KNOW WHAT ARE YOU DOING. # # NetFlow protocol exports an SNMP id instead of the interface name # (i.e., "eth0", "ppp32"). The following statements options define # mapping between the interface names and a set of "SNMP identifiers". # netflow ifclass eth mapto 0-99; # i.e., "eth1"->1, "eth3"->3 netflow ifclass fxp mapto 0-99; # i.e., "fxp4"->4, "fxp0"->0 netflow ifclass ppp mapto 100-199; # i.e., "ppp32"->532, "ppp7"->507 netflow ifclass gre mapto 200-299; netflow ifclass tun mapto 300-399; # i.e., "tun0"->300 ###################### # RSH SERVER OPTIONS # ###################### # # Enable RSH Server: # # rsh {enable|yes|on|disable|no|off} [at <listen_ip>]; # # If "at <listen_ip>" omitted, rsh server listens on IP address 0.0.0.0, # which may be undesirable. # rsh enable at 127.0.0.1; # # RSH access rules: # # rsh [<user>@] <host_addr>{admin|backup|[default]|view-only|deny} ; # rsh root@127.0.0.1 admin; /* Can shutdown ipcad */ rsh root@127.0.0.1 backup; /* Can dump/restore/import accounting table */ rsh root@127.0.0.1; /* Can view and modify accounting tables */ rsh 127.0.0.1 view-only; /* Other users can view current tables */ # Keep IP packet time to live reasonably low to avoid remote attacks. # (The rsh client must reside no more than three hops away from the # router running ipcad.) rsh ttl = 3; # Set rsh timeout for the same purpose. rsh timeout = 30; # # Dump active IP accounting table to this file on exit and read on startup. # (read about -s and -r options in ipcad(8) manual page) # NOTE: This setting has no effect on NetFlow operation. The flow cache # contents are flushed to the collector upon ipcad termination. # dumpfile = /var/log/ipcad/ipcad.dump; # The file is inside chroot(), see below... ################# # OTHER OPTIONS # ################# # # Chroot to this directory before processing. # # Of course, you could disable chroot()'ing by commenting it out, # but it is not recommended, so I left this confusing default # to encourage you to change it. # chroot=/var/log/ipcad; # # File to keep getpid() in it. ipcad will also hold a lock. # # WARNING: Pidfile is created AFTER chroot()'ing, so if you're using # chroot statement above, make sure the path to the pidfile exists # inside chrooted environment. # pidfile = ipcad.pid; # # UID/GID privileges dropping # Please note: RSH service will be UNAVAILABLE when uid is not zero. # Use it only when you know what are you doing (i.e., NetFlow without RSH). # # uid = 65534; # gid = 65534; # # Few useful settings. # # # Memory usage limit for storing per-stream entries. # # memory_limit = <number>[{k|m|e}] ; # Where k, m and g are for kilobytes, megabytes or table "entries". # memory_limit = 10m;</number></host_addr></user></listen_ip></listen_ip></port></port_range_end></port_range_start></maskbits></masklen></ip></maskbits></masklen></ip></group></tcpdump-output.pcap></divert-port></group></group></pcap_filter></iface></number></vlm@lionet.info>#!/bin/sh net="192.168" ttime=`/usr/bin/rsh localhost sh ip acco | grep 'Accounting data saved' | awk '{print ($4)}'` rsh localhost clear ip accounting rsh localhost show ip accounting checkpoint | grep $net | awk -v vtime=$ttime '{if ($5 != 0) print (vtime".000",1,$2,"TCP_MISS/200",$4,"CONNECT",$1":"$5,"-","DIRECT/"$1,"-")}' >> /var/squid/logs/access.logpfsense 2.1.4-RELEASE (i386)
- <cron>- <minute>1,31</minute> <hour>0-5</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/nice -n20 adjkerntz -a - <minute>1</minute> <hour>3</hour> <mday>1</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/nice -n20 /etc/rc.update_bogons.sh - <minute>*/60</minute> <hour>*</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 sshlockout - <minute>1</minute> <hour>1</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/nice -n20 /etc/rc.dyndns.update - <minute>*/60</minute> <hour>*</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/nice -n20 /usr/local/sbin/expiretable -v -t 3600 virusprot - <minute>30</minute> <hour>12</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/nice -n20 /etc/rc.update_urltables - <task_name>squid_rotate_logs</task_name> <minute>0</minute> <hour>0</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/bin/rm /var/squid/cache/swap.state; /usr/pbi/squid-i386/sbin/squid -k rotate - <task_name>squid_check_swapstate</task_name> <minute>*/15</minute> <hour>*</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/local/pkg/swapstate_check.php - <minute>*/1</minute> <hour>*</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/root/tolog.sh - <task_name>lightsquid_parser_today</task_name> <minute>*/60</minute> <hour>*</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/perl /usr/pbi/lightsquid-i386/www/lightsquid/lightparser.pl today - <task_name>lightsquid_parser_yesterday</task_name> <minute>15</minute> <hour>0</hour> <mday>*</mday> <month>*</month> <wday>*</wday> <who>root</who> <command></command>/usr/bin/perl /usr/pbi/lightsquid-i386/www/lightsquid/lightparser.pl yesterday</cron>файлики дампов пустые.
логи работают но без портов.
команда top не отображает ipcad
запуск скрипта ./tolog.sh
localhost: Operation timed outкуда копать ?
-
запуск ipcad
/libexec/ld-elf.so.1: Shared object "libpcap.so.5" not found, required by "ipcad -
Какая версия pfSense? Я недавно ставил на 2.1.4 по известной инструкции и все прошло нормально. Только compat ставить не надо и rsh должен быть от FreeBSD 8.3
-
Какая версия pfSense? Я недавно ставил на 2.1.4 по известной инструкции и все прошло нормально. Только compat ставить не надо и rsh должен быть от FreeBSD 8.3
2.1.4-RELEASE (i386)
built on Fri Jun 20 12:59:29 EDT 2014
FreeBSD 8.3-RELEASE-p16А я делал, по вашей инструкции и компакт ставил и всё с вытекающими, не могли бы описать как это удалить и переставить на более новое
-
попробуйте:
pkg_delete ipcad pkg_delete compat6x-i386 setenv PACKAGESITE ftp://ftp-archive.freebsd.org/pub/FreeBSD-Archive/old-releases/i386/8.3-RELEASE/packages/Latest/ pkg_add -r ipcadRSH брать тут
в tolog.sh еще забыли последнюю строчку: chown proxy:proxy /var/squid/log/access.log -
попробуйте:
pkg_delete ipcad pkg_delete compat6x-i386 setenv PACKAGESITE ftp://ftp-archive.freebsd.org/pub/FreeBSD-Archive/old-releases/i386/8.3-RELEASE/packages/Latest/ pkg_add -r ipcadRSH брать тут
в tolog.sh еще забыли последнюю строчку: chown proxy:proxy /var/squid/log/access.logУдалил, переустановил, всё равно не чего не работает, даже ipcad.dump пуст, может по тим виверу сможете глянуть ?
-
Нет, лучше здесь. Что выдает ipcad -rds ?
-
Нет, лучше здесь. Что выдает ipcad -rds ?
Opening vr0… [LCap] [ERSH] [4096] Initialized as 1
Aggregate network 192.168.0.0/255.255.255.0 -> 255.255.255.255
Aggregate network 0.0.0.0/0.0.0.0 -> 255.255.255.255
Config parse error near line 131: parse error131-строка имеет вид:
Aggregate ports 80..80 into 0Закоментил все строки с Aggregate ports
выдаёт теперь:
Opening vr0… [LCap] [ERSH] [4096] Initialized as 1
Aggregate network 192.168.0.0/255.255.255.0 -> 255.255.255.255
Aggregate network 0.0.0.0/0.0.0.0 -> 255.255.255.255
Configured RSH Server listening at 127.0.0.1
Can't open dump file /var/log/ipcad/ipcad.dump
Daemonized.хотя файлик есть и права на нём 777
-
значит надо убить этот файл и перезапустить ipcad
он у вас уже и так работает "Daemonized", но для порядка -
значит надо убить этот файл и перезапустить ipcad
он у вас уже и так работает "Daemonized", но для порядкаА те строки которые я закоментировал, они не нужны ?
-
значит надо убить этот файл и перезапустить ipcad
он у вас уже и так работает "Daemonized", но для порядкаперезагрузил pfsense теперь пишет
Opening vr0… [LCap] [ERSH] [4096] Initialized as 1
Aggregate network 192.168.0.0/255.255.255.0 -> 255.255.255.255
Aggregate network 0.0.0.0/0.0.0.0 -> 255.255.255.255
Configured RSH Server listening at 127.0.0.1
Can't start: another instance running, pid=80555
Can't initialize pid file /var/log/ipcad/ipcad.pid: Operation not permitted
Make sure you have . under /var/log/ipcad used as new root. man 2 chroot.
[2.1.4-RELEASE][root@pfsense.localdomain]/root(18): -
ipcad запустился при загрузке и не дает создать еще одну копию - все нормально, все работает. Смотрите лог загрузки в консоли, есть там ругань на ipcad.dump?
-
ipcad запустился при загрузке и не дает создать еще одну копию - все нормально, все работает. Смотрите лог загрузки в консоли, есть там ругань на ipcad.dump?
А как он называется и где он лежит ?
var/log system.log - в нём про dump нету не чего -
ты ж сам выше писал
Can't open dump file /var/log/ipcad/ipcad.dump
наверное там и лежит :) -
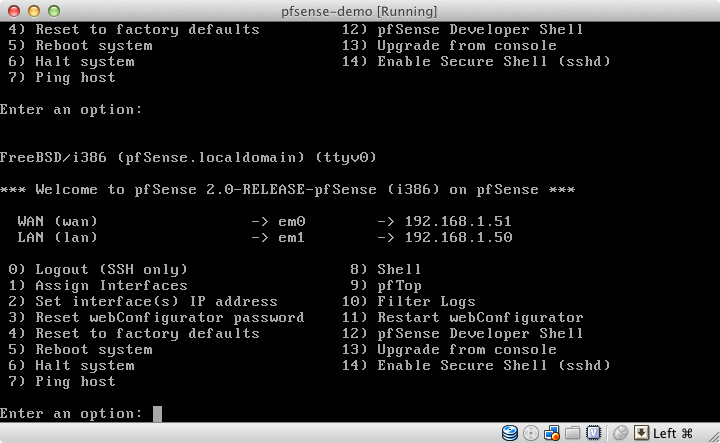
Вот здесь можно посмотреть. Жмете Pause/Break и стрелочкой листаете вверх.
-
-
Так не чего и не работает, сайты типо сбербанка так и не попадают в список лога, я так понимаю вообще сайты с https не попадают в лог ?
-
В сквиде стоит галка Enable logging?
-