Port Forward over VPN interface?
-
I have a port forward rule to allow a specific port inbound over my VPN_WAN interface. Rule is set as follows:
If: VPN_WAN
Proto: TCP/UDP
Src. addr: *
Src. ports: *
Dest. addr: *
Dest. ports: 12345 (just an example)
NAT IP: 10.x.x.x (Plex Media Server)
NAT Ports: 32400So any request using port 12345 should come through my AIRVPN_WAN interface. Howerver when I do a test from that interface (My VPN provider has open port test tool) I see blocks on my firewall showing the request is coming from my regular WAN address.
What am I doing wrong?
-
VPN provider first has to forward the port to you. Do a packet trace on VPN_WAN to be sure traffic for your VPN IP address on port 12345 is actually making it to you when you attempt a connection from the outside. It's not going to work until that happens. Or edit the auto-gen firewall rule and turn on logging….
If that's happening, refer to this for everything you need to check:
https://doc.pfsense.org/index.php/Port_Forward_Troubleshooting
-
VPN provider first has to forward the port to you. Do a packet trace on VPN_WAN to be sure traffic for your VPN IP address on port 12345 is actually making it to you when you attempt a connection from the outside. It's not going to work until that happens. Or edit the auto-gen firewall rule and turn on logging….
If that's happening, refer to this for everything you need to check:
https://doc.pfsense.org/index.php/Port_Forward_Troubleshooting
I forwarded the port myself on my VPN provider's site but I'll give what you suggested a shot.
-
I can't seem to get this to work but I'm not sure I'm doing a proper test. I have a computer on my AIRVPN_LAN subnet which is goes out my AIRVPN_WAN interface for internet via policy routing. When I'm on that PC and check my external IP it shows the IP of my VPN connection. From here I'm going to CanYouSeeMe.org to try and do a port forward test, which is failing.
Obviously I'm doing something wrong but I've configured everything exactly as it is suggested by others using AirVPN port forwarding so I must be missing something outside of the NAT / Firewall rules.
-
The destination in the port forward should be VPN_WAN address not *.
Do a packet capture and be sure the VPN provider is really forwarding the port. You should see the inbound SYN on 12345 (just an example)
The next test would be to do a packet capture on the 10.x.x.x interface. You should see an outbound SYN to your plex on 32400.
-
The destination in the port forward should be VPN_WAN address not *.
Do a packet capture and be sure the VPN provider is really forwarding the port. You should see the inbound SYN on 12345 (just an example)
The next test would be to do a packet capture on the 10.x.x.x interface. You should see an outbound SYN to your plex on 32400.
Whoops forgot to update the OP, I do have the VPN_WAN address as the destination.
I did a package capture for the AIRVPN_WAN on port 32400 (the one I'm trying to forward) and this is what I see when I do a test from CanYouSeeMe.org.
15:01:21.176845 IP 107.20.89.142.44570 > 10.4.x.x.32400: tcp 0
15:01:22.174622 IP 107.20.89.142.44570 > 10.4.x.x.32400: tcp 0
15:01:24.178720 IP 107.20.89.142.44570 > 10.4.x.x.32400: tcp 0
15:01:28.186845 IP 107.20.89.142.44570 > 10.4.x.x.32400: tcp 010.4.x.x is the virtual address of the OpenVPN client connection.
EDIT: Also after turning on some additional logging I see that the traffic is passing from the AIRVPN_WAN into my network as shown by the below entry:
PASS Aug 11 15:22:45 AIRVPN_WAN 107.20.89.142:47385 10.x.x.x:32400 TCP:S
-
why are you hiding rfc1918 address space? ie your 10.x.x.x ?
Well if show pfsense sending it on.. Why is your machine not answering? Or does it just send it out the wrong path, ie out your normal network connection. And now your out of state.. Asymmetric routing and stateful firewalls don't work well together.
Why not just tunnel straight through to this PC to your vpn if you want it to get stuff inbound from that IP? Why make the connection on pfsense in the first place. You have to make sure that when this machine answers it goes back out the tunnel
-
why are you hiding rfc1918 address space? ie your 10.x.x.x ?
Well if show pfsense sending it on.. Why is your machine not answering? Or does it just send it out the wrong path, ie out your normal network connection. And now your out of state.. Asymmetric routing and stateful firewalls don't work well together.
Why not just tunnel straight through to this PC to your vpn if you want it to get stuff inbound from that IP? Why make the connection on pfsense in the first place. You have to make sure that when this machine answers it goes back out the tunnel
Just a habit I guess (not posting full internal network details).
The reason I don't just tunnel in is that I have a lot of people who access this Media Server so it's just not feasible to have them all VPN in.
I'm using policy based routing to send all traffic from my AIRVPN_LAN (the subnet my media server is on) out my AIRVPN_WAN interface as shown below:

-
Fundamental misunderstanding about how firewall rules work in pfSense.
Interface AIRVPN_LAN will never see traffic with a destination of AIRVPN_LAN net
Read it. Learn it. Live it.
https://doc.pfsense.org/index.php/Firewall_Rule_Processing_Order
https://doc.pfsense.org/index.php/Firewall_Rule_Troubleshooting
-
Fundamental misunderstanding about how firewall rules work in pfSense.
Interface AIRVPN_LAN will never see traffic with a destination of AIRVPN_LAN net
Read it. Learn it. Live it.
https://doc.pfsense.org/index.php/Firewall_Rule_Processing_Order
https://doc.pfsense.org/index.php/Firewall_Rule_Troubleshooting
Thanks for that link, I just finished reading it all and it cleared up a bunch of confusions I had.
The rule I had there with a destination of AIRVPN_LAN net didn't make much sense to me either but I had read some posts on here about that being the way to ensure any device on the AIRVPN_LAN network always goes out the AIRVPN_WAN. Howerver I may have gotten 2 different recommendations mixed up there.
It does appear I have some asymmetric routing issues. I'm just very new to multi-WAN routing so while I'm trying my best to route a specific subnet over my AIRVPN_WAN (with some inbound port-forwarding), I'm not sure the ideal way to do that. Hence the hodge-podge of rules I have at the moment.
-
"Just a habit I guess (not posting full internal network details)"
So bad habit then ;) if its rfc1918 space hiding it is pointless and just less likely to get any decent help because its harder to understand your setup and 2nd it makes people think they are working with newbs that don't understand basics ;)
So did you fix your asymmetric routing problem?
-
"Just a habit I guess (not posting full internal network details)"
So bad habit then ;) if its rfc1918 space hiding it is pointless and just less likely to get any decent help because its harder to understand your setup and 2nd it makes people think they are working with newbs that don't understand basics ;)
So did you fix your asymmetric routing problem?
Understood.
Haven't solved it yet, still trying to isolate the issue.
-
I'm trying my best to route a specific subnet over my AIRVPN_WAN (with some inbound port-forwarding), I'm not sure the ideal way to do that.
My advice is to forget about the port forwarding until you have the outbound VPN routing figured out.
One thing at a time.
And also:
https://doc.pfsense.org/index.php/What_is_policy_routing
https://doc.pfsense.org/index.php/Bypassing_Policy_Routing
-
I'm trying my best to route a specific subnet over my AIRVPN_WAN (with some inbound port-forwarding), I'm not sure the ideal way to do that.
My advice is to forget about the port forwarding until you have the outbound VPN routing figured out.
One thing at a time.
And also:
https://doc.pfsense.org/index.php/What_is_policy_routing
https://doc.pfsense.org/index.php/Bypassing_Policy_Routing
Ah that second link was what I was reading when I set that top rule with the destination of AIRVPN_LAN net, I just interpreted it wrong. So instead of AIRVPN_LAN net I can put the RFC1918 alias that I created for a different rule. In theory that should work fine in conjunction with the 2nd rule I have there sending all other traffic out the AIRVPN_WAN interface right?
-
Dude.
Precisely what is the problem you're having? You've gotten so clicky clicky putting who knows what where it's impossible at this point to make a simple recommendation.
Start over.
Get the VPN up.
Get the traffic you want routed out the VPN going out the VPN.
Get the port forward working.
-
Dude.
Precisely what is the problem you're having? You've gotten so clicky clicky putting who knows what where it's impossible at this point to make a simple recommendation.
Start over.
Get the VPN up.
Get the traffic you want routed out the VPN going out the VPN.
Get the port forward working.
I haven't been clicky clicky at all. In fact I have just a few firewall rules in place at all other than the standard allow trusted LANs to any rules. I've got my VPN up and I've got all traffic from the AIRVPN_LAN network routing out the AIRVPN_WAN interface. So I'm pretty much back where I started at the beginning of this thread in trying to determine why when traffic enters the AIRVPN_WAN interface it can't seem to get back out.
-
What do you mean "get back out?"
I say again, what specific problem are you having? be specific, use IP addresses, interfaces, and rules. Specific sources, destinations, and expected behavior.
-
What do you mean "get back out?"
I say again, what specific problem are you having? be specific, use IP addresses, interfaces, and rules. Specific sources, destinations, and expected behavior.
I have the following NAT rules configured:

I've configured port forwarding of port 32400 with my VPN provider. When I do a port forwarding test from a website I get the following passes in the firewall:
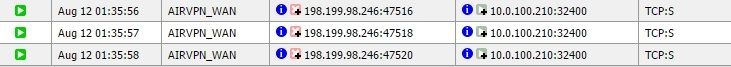
However the tests fail because I "believe" (though you clearly have me doubting I'm right now) that somehow the traffic isn't getting back out of my network after coming in the AIRVPN_WAN interface.
-
From that it looks like the target NAT host isn't responding. Or is responding out another gateway.
https://doc.pfsense.org/index.php/Port_Forward_Troubleshooting
Look at - REALLY LOOK AT - every item - REALLY EVERY ITEM - in that troubleshooting list. Did I say REALLY LOOK AT? REALLY! LOOK AT EVERY ONE!
-
Why it is limited to TCP? Because it's default?