Access internal VPN, but also keep access of work LAN. Split VPN?
-
This is hard to describe, but I am curious if its possible (and how) to be able to remote into my OpenVPN server that I have set up, but then also be still able to access the internal sites that I have on my remote computer.
Another way of putting this is that at work I have the public IP of 123.456.789.10. At home my internal IP is 192.168.1.1 and when I VPN in I have it set for 192.168.2.1.
When I VPN in I can access my internal LAN just fine, but my computer at work takes on the public IP at my house. It works the way it should.
What I ideally want is to be able at work to still have my public work IP so that I can access work mapped drives and intranet sites, but at the same time be able to remote into my computer at home using VNC (port 5900) or other home internal sites.
Is it possible to split a VPN client station up like that so that I can tunnel only VNC traffic from the VPN, but keep outside traffic from going to the VPN also? Almost like a split VPN.
Sorry if that's confusing. It's hard to explain!
-
If it is as hard to explain, draw a map of your situation and what you're trying to achieve.
Where is your VPN server? At work? At home? Where is the client? … ??? -
I'd say the locations are pretty simple to explain. I am running pfsense at home and have OpenVPN setup on it. The client is running at work.
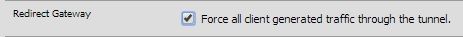
Right now when I connect all my traffic is going through to the VPN. I'd like to split that up if possible.
-
Well don't send your client default route then, and only send the routes that are at your home..
This way it uses the vpn to get to networks that are at your home, and then its normal routing to get to anything else, like the internet, etc.
I do this all the time I am always connected to my home vpn while at work.. But I only route my home networks through the vpn.
-
-
That was it! Thanks @marvosa. All is working beautifully now.