@magician-balmy-stainable said in Enabled Suricata on LAN interface, now can't access pfSense browser interface?:
How can I regain access and/or fix this?
You are going to need to access the console interface directly to fix this. You did not tell us anything about your hardware, so I'm giving the suggestions below based on the two most likely possibilities:
Assuming you have whitebox hardware, get to the keyboard and monitor attached to the pfSense machine and login to the CLI (command line interface). After logging in to the firewall, choose Option "8" to exit to a shell prompt and type this command to stop all Suricata instances:
/usr/local/etc/rc.d/suricata.sh stop
If you have a Netgate hardware appliance, you will need to find and attach the USB serial console cable to access the CLI. After getting that connected and working (just like you did when you first configured the device), exit to a shell prompt and follow the same directions as given above for logging in and stopping Suricata.
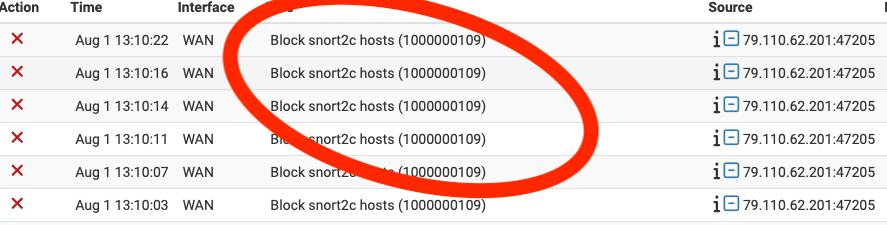
If you are using Inline IPS Mode, stopping the service should restore GUI access. If you are using Legacy Blocking Mode, then you will need to also clear out the snort2c table to remove any lingering IP blocks. Do that with this command from the shell prompt:
/sbin/pfctl -t snort2c -T flush
At this point you should be able to access the web GUI login. I would immediately navigate to Suricata under the SERVICES menu and edit the LAN interface where you have Suricata enabled and either disable it on that interface or turn off the blocking mode by unchecking the Block Offenders checkbox. Save the change. If you fail to do this, then Suricata will get automatically restarted at some point and you will likely find yourself locked out again.
I am fairly certain you have a misconfiguration problem because Suricata has several built-in options to prevent locking you out. Either you have a fundamental hardware compatibility issue, or you have a significant misconfiguration of the package.
@magician-balmy-stainable said in Enabled Suricata on LAN interface, now can't access pfSense browser interface?:
Why did this happen?
Can't really say with certainty because you gave us very little information to go on.
What hardware are you using?
What version of pfSense and what version of the Suricata package?
What is your network topology? (what's connected to what?).
Are you using Legacy Mode Blocking or Inline IPS Mode?
Note that if you are a first time Suricata user, then I highly recommend that you NOT enable blocking when first installing the package. Instead, install it, choose the rules to enable, then let it run on your network for a few days or weeks and regularly monitor the alerts received on the ALERTS tab. See what things are generating alerts and deteremine whether they are legitimate alerts or false positives. Tune the enabled rules and create appropriate Pass Lists (if you intend to use Legacy Mode Blocking) or custom PASS rules (if you intend to use Inline IPS Mode).