@jegr said in Any chances to get Netflix 's Open Connect Appliance (OCA) TCP code (RACK and BBR) into pfSense?:
@sergei_shablovsky said in Any chances to get Netflix 's Open Connect Appliance (OCA) TCP code (RACK and BBR) into pfSense?:
@w0w said in Any chances to get Netflix 's Open Connect Appliance (OCA) TCP code (RACK and BBR) into pfSense?:
https://klarasystems.com/articles/using-the-freebsd-rack-tcp-stack/
Thank You for news!
Available only on the Freebsd 13 and additional options needed when compiling the kernel. I am pretty sure that Netgate uses the Freebsd 12.3 and I have seen somewhere that there are no plans currently to change the version.
Recently I asking here on forum about pfSense shift to the FreeBSD 13, but no any great news from NetGate.
Really, not good news.
Because pfSense looks outdated on FreeBSD 12.X due most end-users traffic today (80%+ in US/EU and around 90%+ in Asia) are classified as “with big latency, packet loss” where BBR2/QUIC are much better CC solution that all we have before.
About that: Don't understand that nonsense about "pfSense looking old on FreeBSD 12.3". It's simply not true.
FreeBSD 12.2 and 13.0 are the current production ready/stable versions listed on the project page. So talking about "old" or "outdated" is simply false. That Negate currently is staying on 12.x with the current 2.5.x release tree is completely normal and understandable as they aim for a STABLE release. Not bleeding edge. And as we are talking about a border gateway, router, gateway device, that's a good approach. FreeBSD 13 is still young and was only released on April this year. So just about half a year of age and as a new release it wasn't even immediatly pushed to -stable but to a -current/-release state.
I don't see the sense in rushing to new releases as that always requires a complete rebasing and updateing of all components of pfSense and its base system. That doesn't work with the wish for more stable releases per year as is currently planned for pfSense plus. With 3 releases per year you aren't simply adapting a completely new base system every few weeks and can include testing for all bells and whistles.
What I say on this? ;)
My experience in IT after more than 20+ years told me, that You are absolutely right.
There is one BUT: the world running faster and faster. And this speed more and more impact on the ”STABILITY vs NEW FEATURES” balancing that we, as network engineers and SysAdmins need to keep well. And of course, this balance vary depend on network environment, client goals, and many other factors.
And the features that we was very septic about, become more valuable and more needed by our clients.
And this is no “bells and whistles”, this is the protocols and technologies that 3-5 years before not exist, but now become a key for a business.
Media streaming coming (Amazon, Netflix, etc...) - and modern and ** more effective CC** like BBR/BBR come in!
Social networking + better cameras in smartphones coming (with a lot of photos and videos) - and modern effective CC QUIC coming and stay as standard RFC protocol in near a future.
I'm really all for new things that make sense. Hands down. But a stable and more tested release is far better than stupid running around after every new driver and release to include the latest and greatest commits there are.
With this I more than agree: in security sector we need to be more traditional, more stable.
Additionally it was already talked about in several blog posts, that pfSense will get FreeBSD 13 (potentially with 2.6 or 2.7 depending on when/what 2.6 will include) later on. So I see no sense in downtalking the use of a stable base OS :)
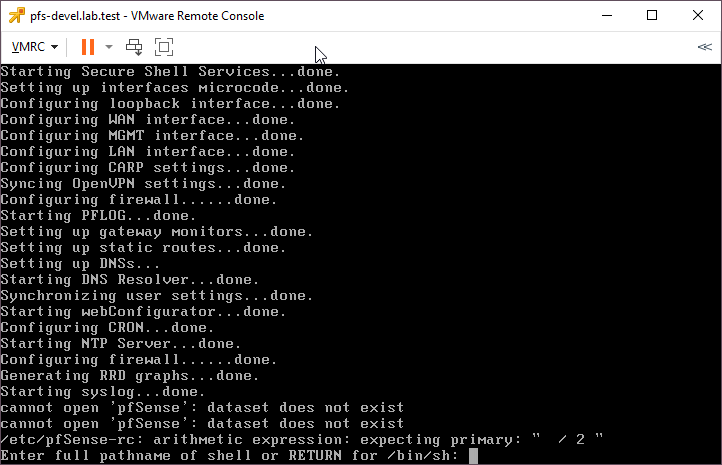
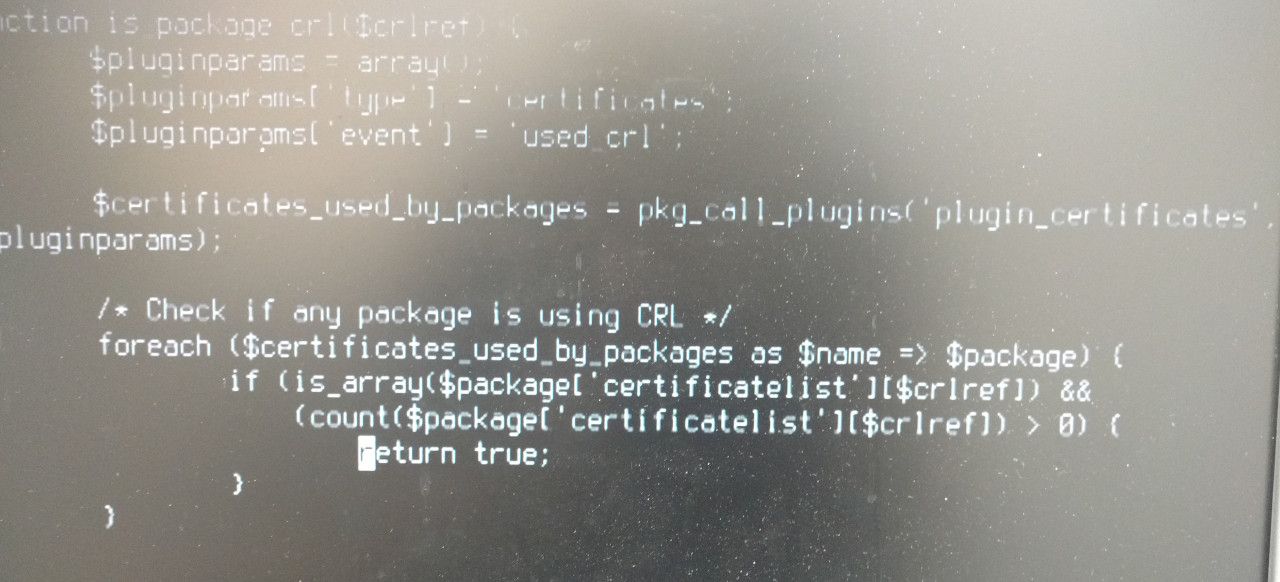
I am not sure that coming as fast as we need: after recent issue with error in code (that mean no effective code quality check system exist in Netgate) I am not sure there are so much resources to keep both CE and TNSR versions and (as You good write) ** that always requires a complete rebasing and updateing of all components of pfSense and its base system. That doesn't work with the wish for more stable releases per year as is currently planned for pfSense plus. With 3 releases per year you aren't simply adapting a completely new base system every few weeks and can include testing for all bells and whistles.**.