pfSense HA LAN Interfaces Only
-
@viragomann hmm. Can't seem to get to working. I have turned off HA static route sync from the master node and then on the backup node I have created a new gateway using LAN pointing to the LAN interface IP of the master node and then created a Gw Group with pppoe wan as tier 1 and my new gw as tier 2 and set this group as default but still no internet. I have also included pics of what I did. Any suggestions?
-
@iptvcld
The gateway and gateway group are looking correctly, but you have to troubleshoot the gateway monitoring problem.
Ensure that pinging 8.8.8.8 from 192.168.2.81 is allowed on the master and that there is an outbound NAT rule present on WAN for that source. -
@viragomann I did a test from my master to ping out to 8.8.8.8 and that works ok.
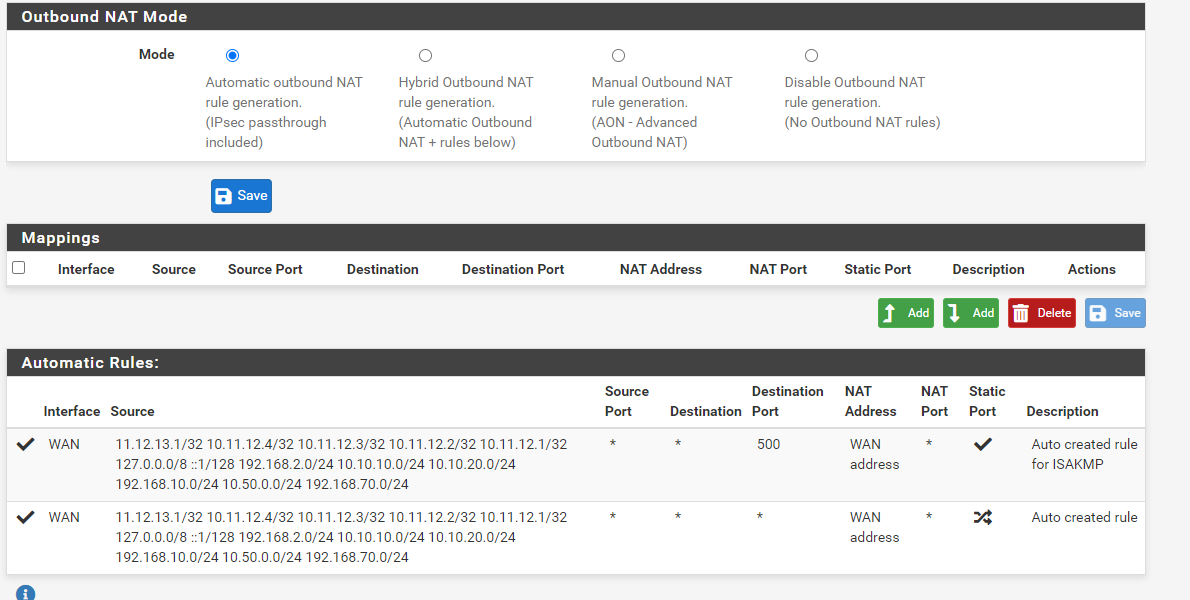
Also on master; this is what my outbound nat section looks like. I can see under source there is y LAN network 192.168.2.0/24
I am not too sure what else i should be looking at; would really appreciate your help. thank you!
-
@iptvcld
I think, I've forgotten something:
On the secondary you will need to add an outbound NAT rule to LAN for 127.0.0.0/8 and switch into hybrid mode. -
@viragomann Thanks; so on my backup PF i did the below:
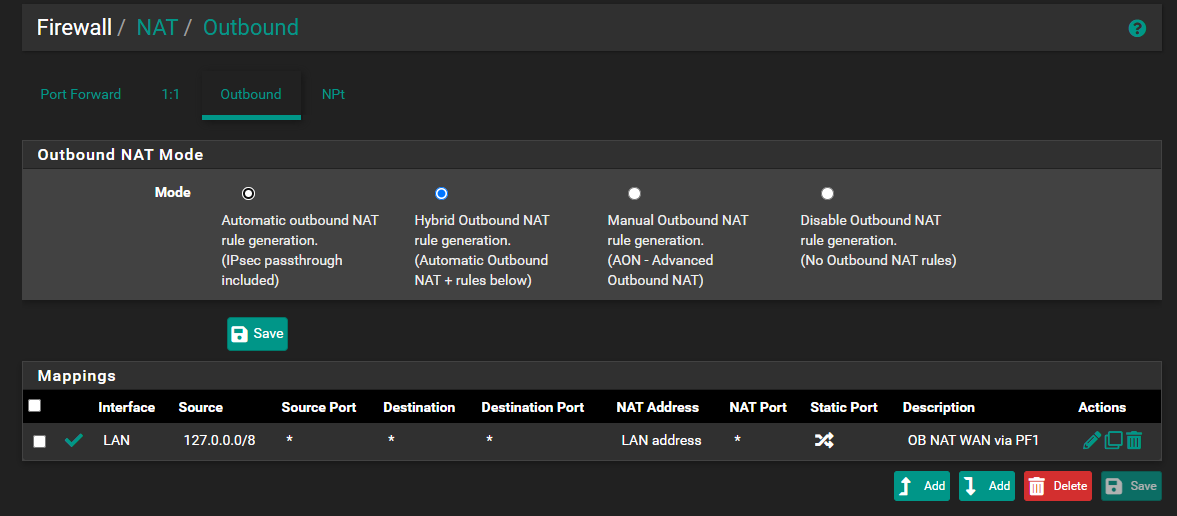
This did not work still then i tried this
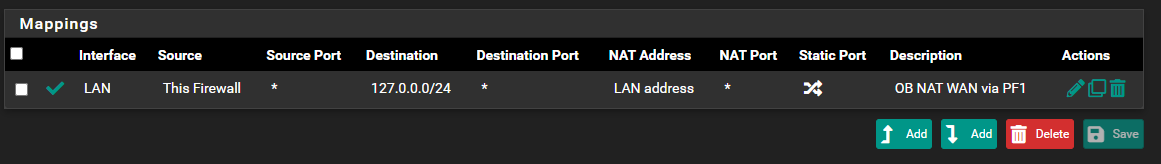
But this did not work as well.
-
@iptvcld
Keep the first one.Tried to restart the machine?
If it still doesn't take a packet capture on the LAN interface. You should see periodic pings to 8.8.8.8. As well you should see them on the masters LAN and also on the masters WAN if it works as expected.
-
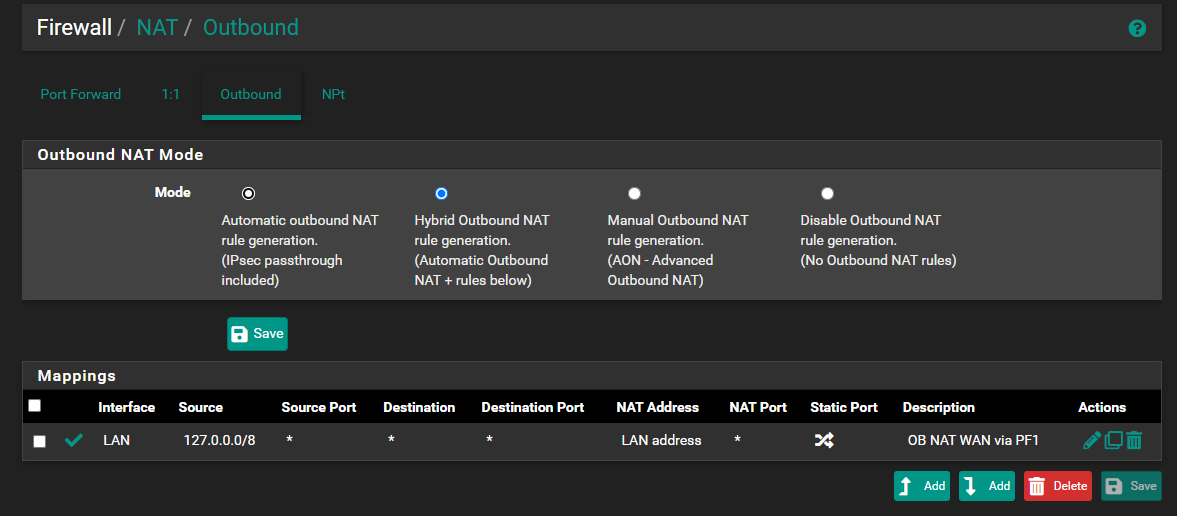
@viragomann I also just noticed since i made this NAT mode change from auto to hybrid and also adding the mapping on my backup PF; after the reboot, it reverted back to auto and got rid of the mapping as my master sync'd over. Should i be making this change on my master then?
-
@iptvcld
Yes, you can add this rule to the master as well. It won't be used there anyway. -
@viragomann i did this on the master now and i saw it synced over to the backup. I rebooted the backup again as well.
I ran a packet capture on the LAN (backup pf) and i see a few of these lines. IP: 76.64.x.x is my wan
10:54:16.598225 IP 76.64.x.x > 8.8.8.8: ICMP echo request, id 13920, seq 321, length 9but GW still shows offline
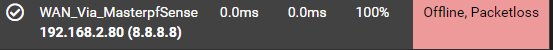
When i run a ping to 8.8.8.8 using backup, i get this
PING 8.8.8.8 (8.8.8.8): 56 data bytes
64 bytes from 8.8.8.8: icmp_seq=0 ttl=115 time=2.599 ms--- 8.8.8.8 ping statistics ---
3 packets transmitted, 1 packets received, 66.7% packet loss
round-trip min/avg/max/stddev = 2.599/2.599/2.599/0.000 ms -
@iptvcld said in pfSense HA LAN Interfaces Only:
I ran a packet capture on the LAN (backup pf) and i see a few of these lines. IP: 76.64.x.x is my wan
10:54:16.598225 IP 76.64.x.x > 8.8.8.8: ICMP echo request, id 13920, seq 321, length 9Even if the WAN cable is disconnected??
I was assuming that the WAN is offline, so not clear, why it use the WAN IP. -
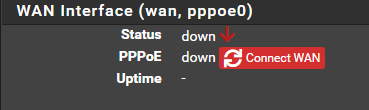
@viragomann That is correct Sir; i do not have my WAN connected to my backup pf right now
-
@iptvcld
Not clear, what's wrong here.
As first step for troubleshooting you can remove the monitoring IP from the LAN gateway on the backup. Hence it should monitor the masters LAN and the gateway state should get online.
But not sure if the failover will work after. -
@viragomann I ran a packet cap again and i am seeing those monitoring requests come in as well:
11:14:31.073869 IP 8.8.8.8.853 > 192.168.2.81.17018: tcp 0
11:14:31.073887 IP 76.64.x.x.11762 > 8.8.8.8.853: tcp 0 -
@viragomann When i remove the monitoring ip from the GW; yes it puts the master LAN IP in there and yes it shows Green and Online but no internet.
Ah i really hoped this would have worked out; was such a nice idea to have.
-
@iptvcld said in pfSense HA LAN Interfaces Only:
I ran a packet cap again and i am seeing those monitoring requests come in as well:
11:14:31.073869 IP 8.8.8.8.853 > 192.168.2.81.17018: tcp 0
11:14:31.073887 IP 76.64.x.x.11762 > 8.8.8.8.853: tcp 0So you're using 8.8.8.8 for DNS resolution as well.
Possibly that's an issue when you've stated the WAN gateway in System > General Setup.
However, when using this IP for gateway monitoring, pfSense will automatically add a static route and point it to the respective gateway. So there might be a conflict.As mentioned above, you can use any other public IP for gateway monitoring which is responding to pings. It might be a good idea, to use another IP.
Also you should have a check at System > Advanced > Miscellaneous > State Killing on Gateway Failure.
For further testing you can set the WAN gateway as down manually on the backup.
-
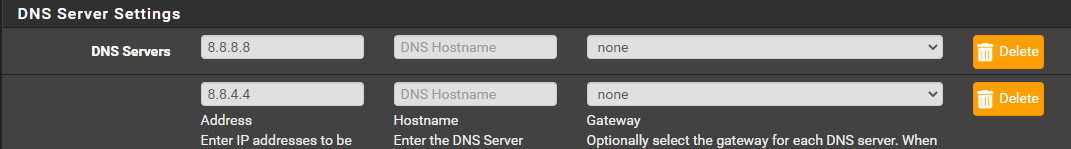
@viragomann Correct; i am using 8.8.8.8 and 8.8.4.4 as DNS Res via system > gateway.
I have now changed my GW monitoring IP to 1.1.1.1 on the secondary pf. Also on the secondary pf i have placed a CHECK under System > Advanced > Miscellaneous > State Killing on Gateway Failure.
When i try to ping 8.8.8.8 from the secondary; i get this timeout
PING 8.8.8.8 (8.8.8.8): 56 data bytes 92 bytes from 127.0.0.1: Time to live exceeded Vr HL TOS Len ID Flg off TTL Pro cks Src Dst 4 5 00 0054 263f 0 0000 01 01 0000 127.0.0.1 8.8.8.8 92 bytes from 127.0.0.1: Time to live exceeded Vr HL TOS Len ID Flg off TTL Pro cks Src Dst 4 5 00 0054 b74f 0 0000 01 01 0000 127.0.0.1 8.8.8.8 92 bytes from 127.0.0.1: Time to live exceeded Vr HL TOS Len ID Flg off TTL Pro cks Src Dst 4 5 00 0054 66ba 0 0000 01 01 0000 127.0.0.1 8.8.8.8 --- 8.8.8.8 ping statistics --- 3 packets transmitted, 0 packets received, 100.0% packet lossI have marked my PPPOE WAN as down on the 2nd pf as well.
This is so bizarre..
I also have just an open rule for LAN
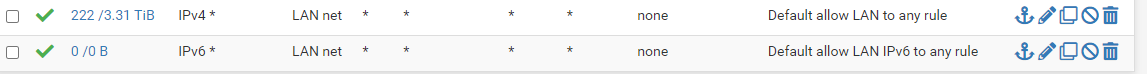
-
@iptvcld said in pfSense HA LAN Interfaces Only:
When i try to ping 8.8.8.8 from the secondary; i get this timeout
You cannot use 8.8.8.8 for troubleshooting, since you direct it to WAN gateway.
However, for getting the DNS resolution work on the secondary when the WAN cable is connected to the primary, you should set the gateway to "none" for all DNS servers in System > General Setup.I have now changed my GW monitoring IP to 1.1.1.1 on the secondary pf.
So try to ping 1.1.1.1 while taking a capture on the LAN interface.
-
@viragomann My master pf DNS settings like like this
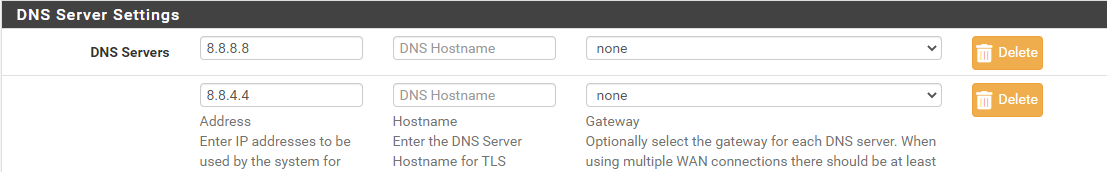
and secondary pf is the same
When i ping 1.1.1.1 in seconday the packet capture just gave this
12:57:15.477198 IP 192.168.2.81 > 1.1.1.1: ICMP echo request, id 18433, seq 797, length 9 -
@iptvcld said in pfSense HA LAN Interfaces Only:
When i ping 1.1.1.1 in seconday the packet capture just gave this
12:57:15.477198 IP 192.168.2.81 > 1.1.1.1: ICMP echo request, id 18433, seq 797, length 9You should see the same on the masters LAN. Check that out, please.
-
@viragomann thats correct; i just ran a packet cap on master LAN and then sent a 1.1.1.1 ping from the secondary pf
13:05:44.735976 IP 192.168.2.81 > 1.1.1.1: ICMP echo request, id 18433, seq 1785, length 9