Bypassing DNSBL for specific IPs
-
Thank you to all who commented here. I didn't know views were possible in unbound until reviewing this post. I was working through implementing this in my use case which is different than others here. I wanted to comment and share in case anyone else has a similar issue.
tldr: listing only networks for bypassing dnsbl, with defaulting to use of dnsbl for clients
I have many networks (vpns, vlans, etc.), and wanted to configure the use of dnsbl as a default from any network except for specific clients or networks listed. In the examples above, each network has to be listed as either dnsbl or bypass. I didn't want to have to list all networks, and only list bypass IPs/networks since most will use dnsbl.
The key I found to get this working was to set
view-first: noThis wasn't entirely clear to me from the unbound documentation, but seems to work as ignoring the default settings.
I also tried entering a view network such below, to cover all possible private IPs. But these didn't work:
access-control-view: 172.16.0.0/12 bypass_dnsbl access-control-view: 192.168.0.0/16 bypass_dnsblMy working config is here:
server: include: /var/unbound/pfb_dnsbl.*conf access-control-view: 172.20.0.0/24 bypass_dnsbl #guest vlan view: name: "bypass_dnsbl" view-first: no include: /var/unbound/host_entries.conf #Host overrides AND DHCP reservations include: /var/unbound/dhcpleases_entries.conf #DHCP leasesI think this would also have the added benefit of pfblocker not re-adding the "include:" config, but not entirely sure since I have only added recently. If anyone notices an issue with this, please let me know!

-
Hello everyone, is there a possibility to allow a particular host or network to access a certain category of dnsbl? Example: IP 192.168.0.1 access the social networks category and continue with the rest blocked?
Thanks.
-
@fabioccoelho said in Bypassing DNSBL for specific IPs:
Hello everyone, is there a possibility to allow a particular host or network to access a certain category of dnsbl? Example: IP 192.168.0.1 access the social networks category and continue with the rest blocked?
Thanks.
Looks like its being worked on, good timing.
https://www.reddit.com/r/pfBlockerNG/comments/kdg5wq/preliminary_dnsbl_group_policy/Without these upcoming features, what you want to do would be pretty complicated. I have previously set up different pfsense/pfblocker instances to to accomplish this.
-
@risfold Thanks a lot :-)
-
This thread started in 2018 and has comments up to the end of 2020.
Do we have an option in the gui to allow one or more ip addresses or hosts to do unblocked DNS?
What I am looking for is something in the GUI that is stable and will stay when doing upgrades. Command line tricks and extra config files are not what I am asking for.
Thanks,
Joe -
-
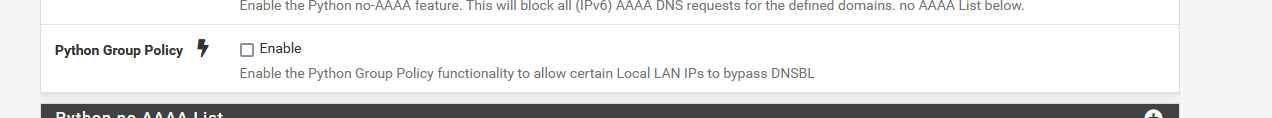
@gertjan I'm not getting that on the page. Using v3.0.0_16 on pfsense 2.5.1
-
@godatum Check the reddit link posted above, there is a tip that says to switch to python mode for the option to become available:
Preliminary DNSBL Group Policy : pfBlockerNG
https://www.reddit.com/r/pfBlockerNG/comments/kdg5wq/preliminary_dnsbl_group_policy/ -
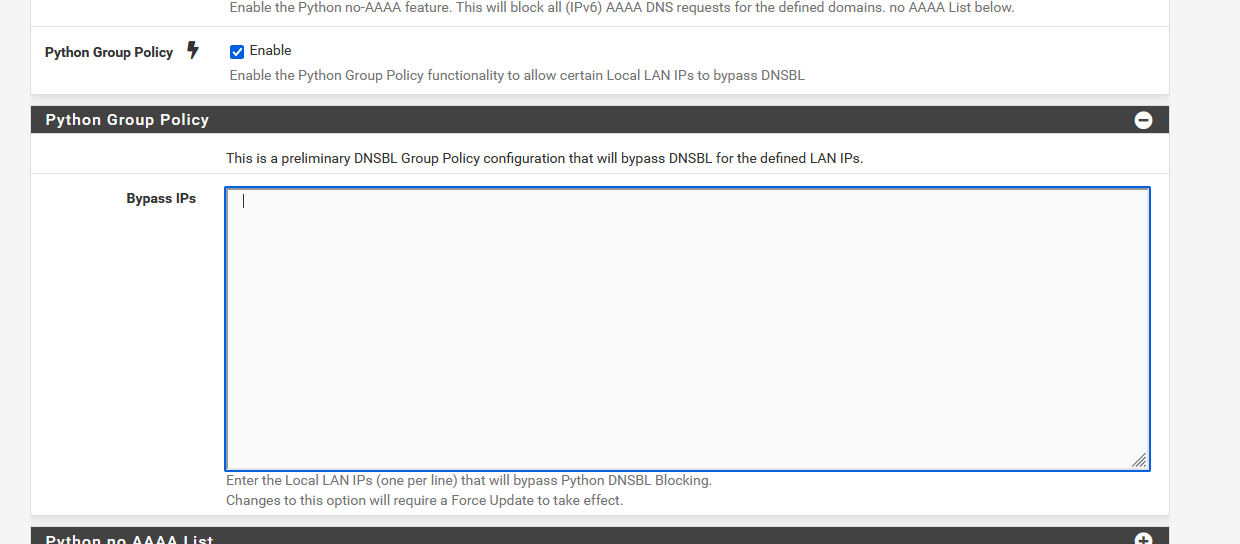
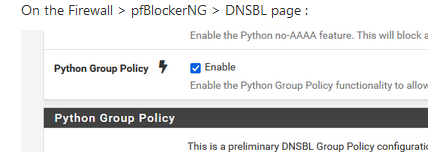
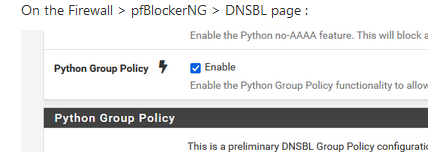
Yep, this box should be checked :
-
Here from Reddit, then Mayfield IT...
I've got a setup where I'd like to bypass pfBlockerNG for one single entire interface but keep it enabled for my other 2 interfaces. Interfaces "LAN1" (10.0.0.0 /24) and "Crapwork" (192.168.0.0 /24) should still get the full pfBlockerNG treatment (DNSBL+IPBL) while the unlucky guests on interface "BARN" (172.16.0.0 /24) won't and will have to see ads and get random IPs from bad places poking around!Would I need to enter the below into the "custom options" box in DNS resolver settings and then also make sure interface "BARN" is not selected (while LAN1 and Crapwork are) in the "Outbound Firewall Rules" section of IP tab under pfBlockerNG?
server: access-control-view: 172.16.0.0/24 bypass access-control-view: 10.0.0.0/24 dnsbl access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes include: /var/unbound/pfb_dnsbl.*confOr should I update pfSense (on 2.4.5 yikes) and then update pfBlockerNG (on 2.2.5_30) and use the Bypass IPs field where I'd put (presumably) 172.16.0.0/24 and then same as above for IPBL settings?
-
@turbotater19 said in Bypassing DNSBL for specific IPs:
Or should I update pfSense (on 2.4.5 yikes)
Back then, as for as I can remember, you had to enter the custom unbound parameters (like you showed - can't tell if they are correct, though).
The latest pfSense, and the latest pfBlockerNG makes it possible to exclude IP (or even networks ?) using the pfBlockerNG GUI.
Select the (DNSBL) 'Python Group Policy' option and fill in the IP's. -
@gertjan said in Bypassing DNSBL for specific IPs:
Back then, as for as I can remember, you had to enter the custom unbound parameters (like you showed - can't tell if they are correct, though).
The latest pfSense, and the latest pfBlockerNG makes it possible to exclude IP (or even networks ?) using the pfBlockerNG GUI.
Select the (DNSBL) 'Python Group Policy' option and fill in the IP's.Thanks for the reply. I guess then what I'm asking for is if anyone thinks my code is correct for keeping DNSBL active on 2 of my 3 interfaces while the one interface gets bypassed. All the examples I've seen appear to show a single IP bypassed while the rest are blocked or 2 VLANs.
Also, to implement this (provided I don't just update pfSense and then update pfBlockerNG), do I disable pfBlockerNG, add lines into custom options, save, then start pfBlockerNG? Or do I add this into custom options while pfBlockerNG is enabled?
-
I pasted my code in and initially it didn't work. Took out the leading spaces on each line and that fixed it, working as I'd hoped!
-
@gertjan
I can't find it? Is it removed?I'm trying to find a solution to unblock an IP, which is one of my blocklist as false positive.
-
@overlord said in Bypassing DNSBL for specific IPs:
I can't find it?
Find what ?
The initial - see above - is "how to bypass a specific IP".
Reading the post shows that @Ns8h wanted to exclude a LAN device from being DNSBL'ed by pfBlocker - this was in 2018.Or do you man : You want to whitelist an IP ( or DNSBL ?) from a list/feed you use ?
In that case, go to Firewall > pfBlockerNG > Alerts and look up the line where the IP was blocked. Example :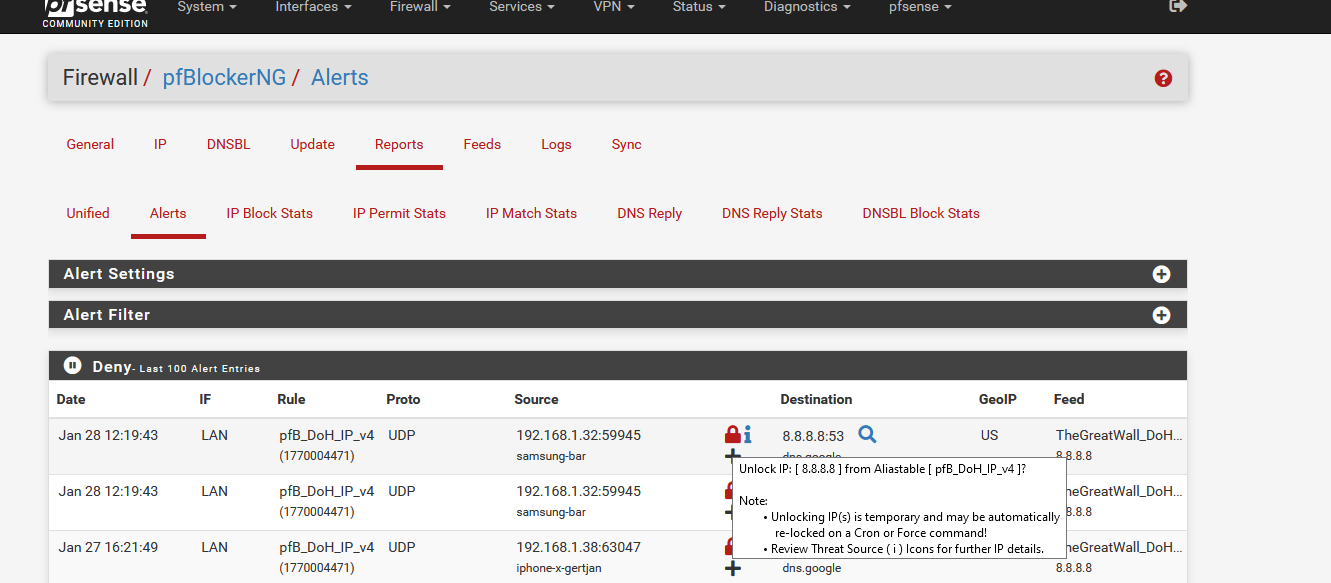
if I want to unblock "8.8.8.8" blocked by the firewall rule pfB_DoH_IP_v4 (uses an alais that contains all the IPs from the TheGreatWall_DoH... DNDBL feed, I have to move the mouse to the red padlock, click and follow the instructions.
This measure is temporary - as stated.Clicking on the black + sign is permanent :
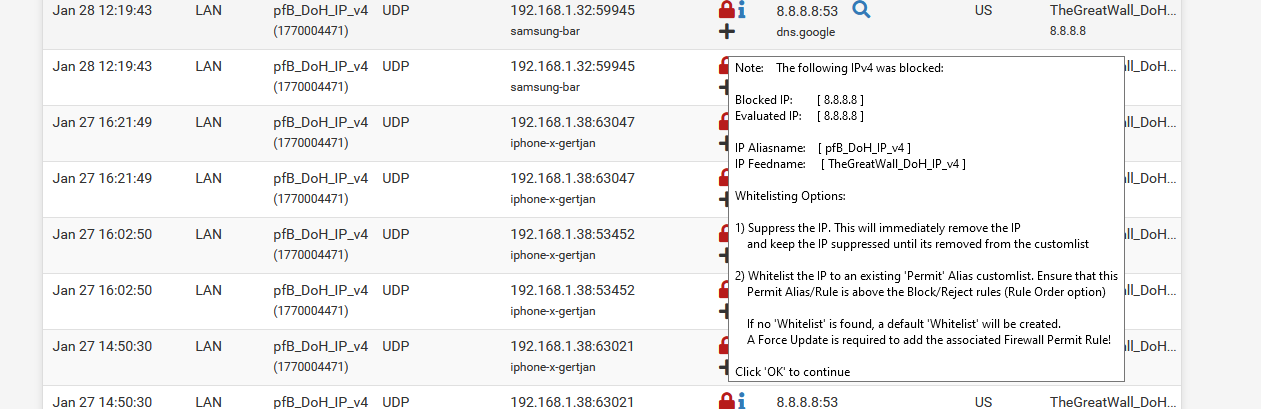
Just follow the instructions.
-
@gertjan said in Bypassing DNSBL for specific IPs:
Yep, this box should be checked :
This did not work for me at all, and neither using custom unbound views. Not sure where else to look.
-
Just checking "Python Group Policy" does nothing.
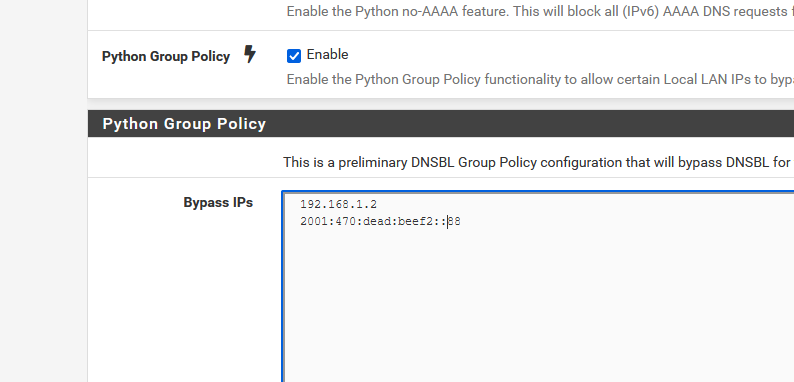
It's stated that "Enable the Python Group Policy functionality to allow certain Local LAN IPs to bypass DNSBL"So certain local IPs have to be entered.
Like :
edit :
I didn't have any DNSBIl activated, so I activated one.
This one :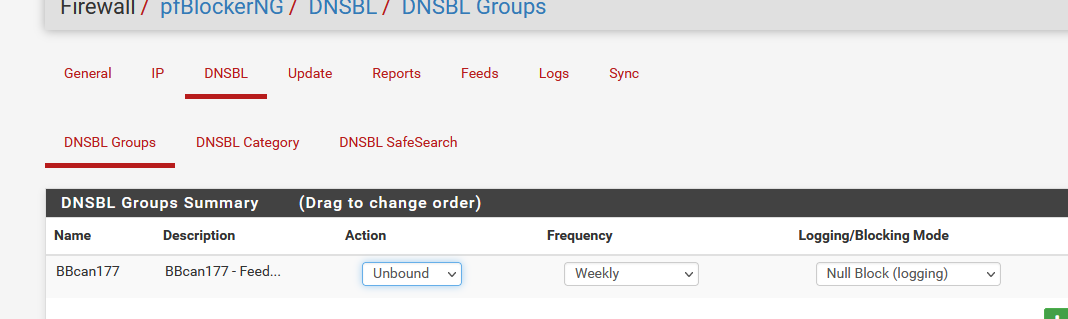
Take a look at the feed text, and you find the last entry :
avsvmcloud.comOn my PC with the IP 192.168.1.2 (on the policy list - see my image above) I could obtain an IP :
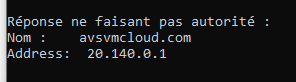
Or, on another PC using IP 192.168.1.9, I obtained "0.0.0.0" == DNSBL blocked ( I'm not using the build in pfBlockerNG web server, if I was, I would have received 10.10.10.1 ).
My conclusion : Group policy works.
I did not test IPv6 here. For IPv4 it worked.
-
@gertjan I added my local IP4 addresses under the group policy as host IP's with no subnet mask range e.g. /32 /24 etc.. I restarted pfsense, unbound, ran , update force, reload and still no dice. I love the way it works but I need to whitelist IP's to get around pfblocker/dnsbl/geoip restrictions I've set already. thanks!
-
@gertjan
As I can see there are no rules under "Deny". I have read there, that this issue could be from the installed version (2.1.4_26). Is this 2x version still in development? Is there a release date for the 3.x devel version? (Devel becomes non devel) -
@smokinmojoe I was literally saying this out loud to myself. This package has been available for quite some time and the fact that this request which is very reasonable and very obvious that is needed is not implemented really hurts my soul.
Yes, DNS sinkholing is great. You would think along the way someone would've thought to themselves "Gee, what if there's a user that shouldn't be restricted". Pretty much the follow-up to that thought was "ehh that would never happen. what an unlikely thing to think".