OPT1 needs LAN DNS access
-
Maybe we are getting out of sync.
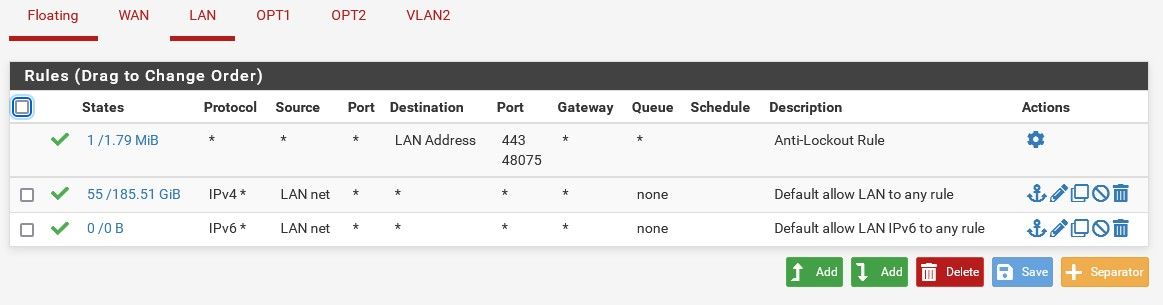
The only place that anti-lockout option is enable (or unchecked) is on the LAN.
Meaning, in system, advanced, the anti-lockout is not checked.I tested from the other networks and they cannot reach the firewall which is what I wanted so I'm not following what the problem is. I did this based on some pfsense document I found which talked about anti-lockout.
Some information suggested using this method, others suggested creating an alias and using that as a rule so it's kind of confusing to know which is the right way.
-
@lewis said in OPT1 needs LAN DNS access:
I tested from the other networks and they cannot reach the firewall which is what I wanted so I'm not following what the problem is.
Don't worry, friend, don't drown in a glass of water, just do a tracert and set the route your team takes to get there.
-
@lewis said in OPT1 needs LAN DNS access:
The only place that anti-lockout option is enable (or unchecked) is on the LAN.
Ok that is correct, because it is not possible to enable that or disable that on any other interface.. Its a LAN thing only.. So yeah might be some confusion there that you were removing the antilock out for some reason.
Some information suggested using this method
It is possible if you wanted to restrict devices that were on your lan from getting to the web gui, to turn off the antilock out and set your own rules. But to be honest if you were going to be locking down your network, I wouldn't be putting anything on the "LAN" that shouldn't be there, ie admin only sort of thing.. Turning off the antilock rule should be carefully considered..
There was recently a thread where they were locked out and had to refer them here
https://docs.netgate.com/pfsense/en/latest/troubleshooting/locked-out.html -
I want to understand what is being said and it's not clear to me.
From the OPT1 (10.0.0.1/24) and OPT2 (192.168.254.1/24) network, I cannot reach or even see anything on the 192.168.1.1 network using nmap.
From clients on each network, I get a reply from devices on the same network as expected but none see anything on other networks.
Of course, I need to block the firewall from any clients on each of those networks. The only network that should have access to the firewall is LAN.
-
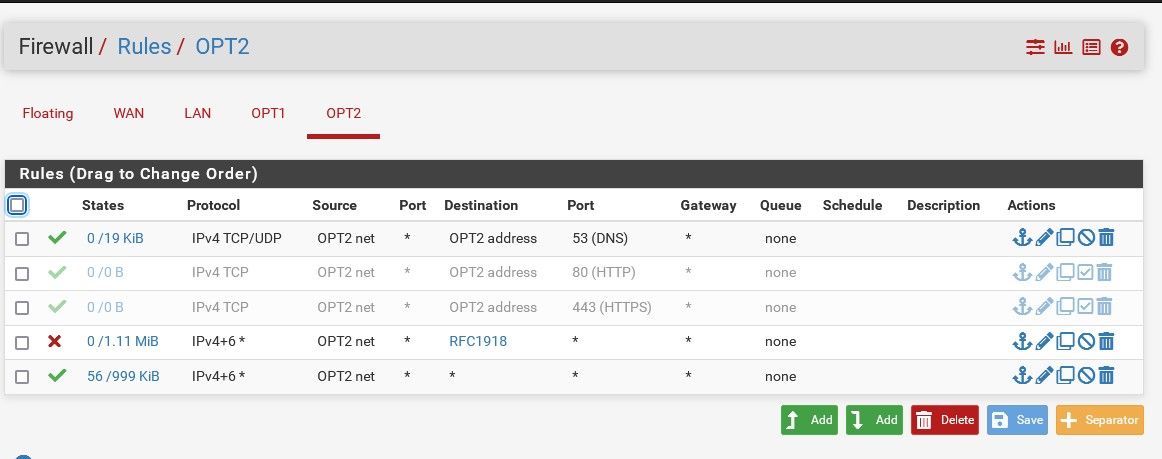
And that is correct. The rules you had on LAN were fine. If the rules you have on OPT1 and OPT2 are as they were previously in this thread that's also fine.
If not then post the rules you have now for all 3 interfaces and we can review them.Steve
-
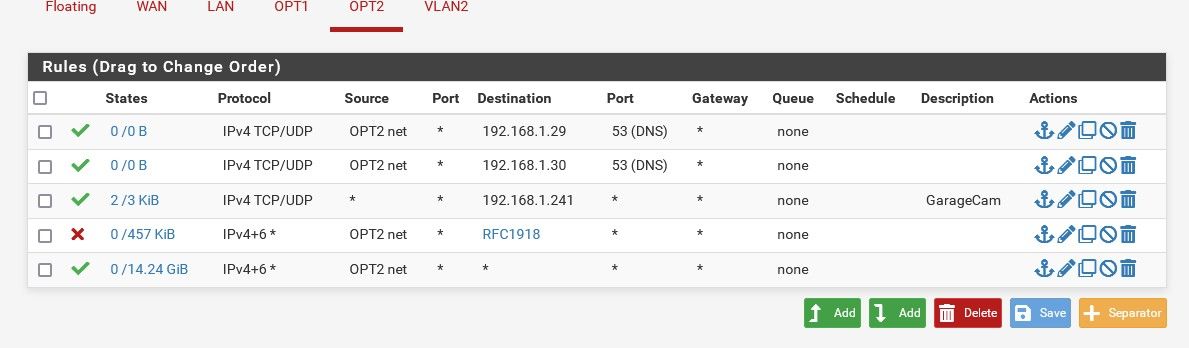
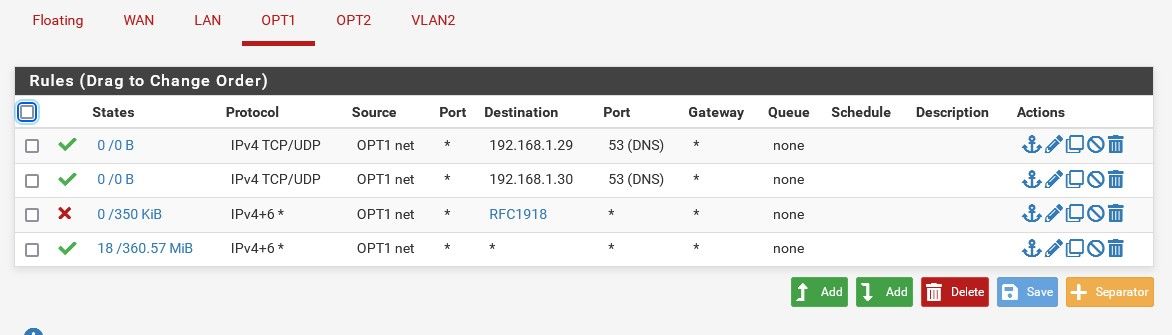
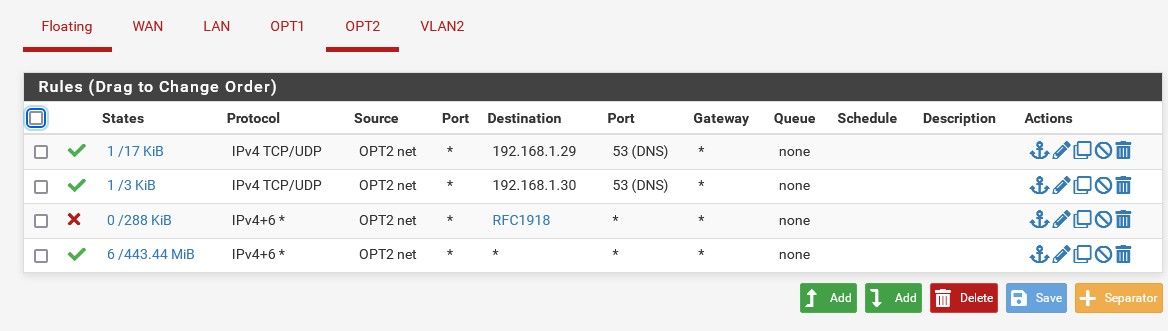
To be safe, here they are. DNS servers are on the LAN, hence the rules.
-
I think all I really need to do now is to add a rule on each network to not allow clients to access the gateway/firewall right?
-
@lewis said in OPT1 needs LAN DNS access:
each network to not allow clients to access the gateway/firewall right?
Your rfc1918 rule would do that, other than the wan IP which I would assume is public. This is good use of the "this firewall" alias. Which would include any IPs on the firewall, even if they change.
-
Correct, none of the clients on each network can see the pfsense firewall.
Or I should say, using nmap from a client, I can see the gateway of the network which is the pfsense device but no ports show up which is good.However, I have a bit of a different situation on another network. I set up OPT2 recently for my new AP and the wireless clients can see ports 22, 53, 80 and 443 on the AP.
It's not yet clear to me if I should block that from the AP (running openwrt now) or using pfsense.
What is interesting to me is like our DHCP talk, it would be nice to have just one place (pfsense) to monitor/maintain all access rules.I will have to block access to clients using the AP rules but am curious to know if there might be a way to do it from pfsense instead. Meaning, some rules on pfsense that would block other clients on the same network from being able to see those ports while also allowing the LAN to have access to the AP.
-
@lewis said in OPT1 needs LAN DNS access:
I set up OPT2 recently for my new AP and the wireless clients can see ports 22, 53, 80 and 443 on the AP.
Pfsense has no control over devices talking to other devices on the same network.. If you fire up some device, even an AP on a network and it has services listening on ports pfsense would have no way to stop a client on the same network from seeing those. That would have to be done on the device.
With something like an AP, the management IP should be on a network that is not available to wireless clients for example..
-
Got it. I thought there might be a way to block clients on the network itself.
I'll block access on the AP then and allow the single LAN IP that should have access. -
@lewis said in OPT1 needs LAN DNS access:
I thought there might be a way to block clients on the network itself.
Nope - not how it works.. When a device want to talk to an IP that is on the same network as its IP via its mask, it just arps and then sends the traffic directly to that mac.
Traffic is only ever sent to the router (pfsense) when the IP the client wants to talk to is not on the clients own network. When a devices want to talk to say IP 1.2.3.4, which is not part of its local network. It will arp for the gateway mac if not already in its cache. And then send the traffic to the mac of the gateway with the destination IP of 1.2.3.4, pfsense will see this traffic and based on its routing send the traffic on either out another interface that is attached to the network that IP is on, or to its default gateway. That is if the firewall rules allow the traffic.
edit: The only possible way pfsense could be involved in traffic on the same network talking to each other is there was a bridge setup in pfsense, then pfsense could filter traffic between devices on opposite sides of the bridge. But if devices were all on the same side of the bridge then pfsense would not see the traffic to be able to filter.
-
Very informative thread.....
-
Figured I should add to this rather than start a new thread but happy to start a new one if needed.
The last thing we did was to fix the OPT2 gateway so I could reach the AP from the LAN. All good since then.
However, something weird happened today and I realized something is still not right.
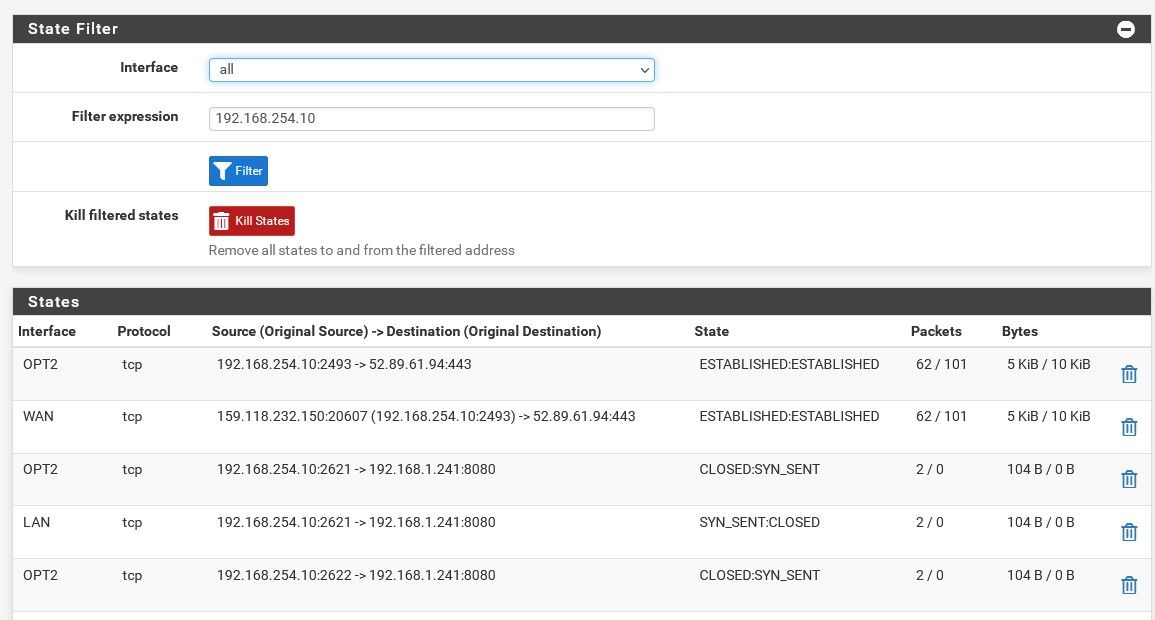
I am trying to reach a LAN IP from the OPT2 network so I created a rules that should allow this. But it didn't work. OPT2 devices cannot reach the IP on the LAN.
While testing this, I noticed that none of the clients on the AP could even nmap the DNS port for the DNS servers they are allowed to use.
If I disable the DNS rules, clients definitely lose DNS services as expected. If I re-enable the rules, clients get DNS again.
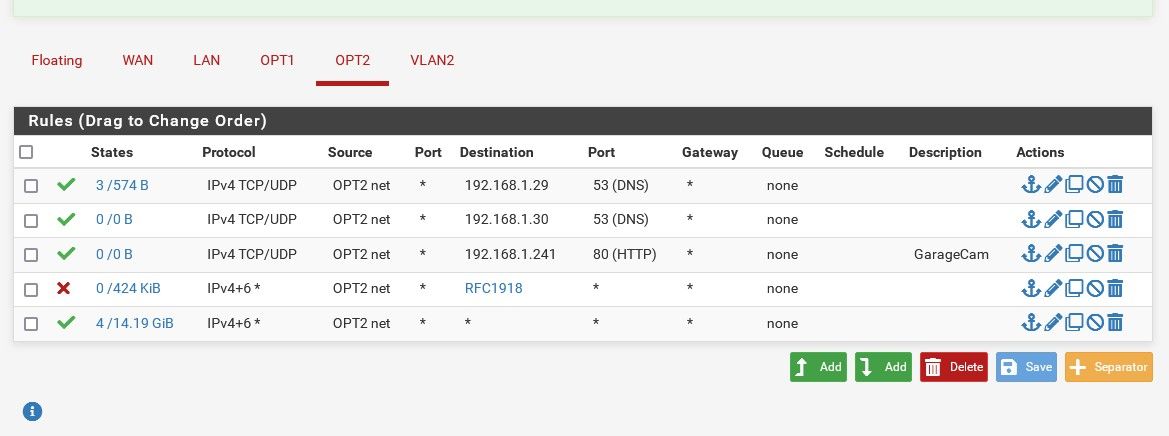
So, why aren't clients able to access the garage device since there is a rule that should allow them to?
-
@lewis said in OPT1 needs LAN DNS access:
So, why aren't clients able to access the garage device since there is a rule that should allow them to?
I don't see that rule even evaluated, see the states 0/0.. You sure its 80, and not https (443) etc. or some other port, rtsp uses 554 for example.
Also Cam device, you sure that device has a gateway setup up pointing to pfsense.. if not then you wouldn't be able to access it from another network without doing source natting.
-
I assume the second DNS is never hit since the first is always up, hence, 0/0.
The cam server is an openwrt device running mjpeg-streamer on port 80. It does have a gateway.
# route -n Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 0.0.0.0 192.168.1.1 0.0.0.0 UG 0 0 0 br-wan 192.168.0.0 0.0.0.0 255.255.0.0 U 0 0 0 br-wan 192.168.1.0 0.0.0.0 255.255.255.0 U 0 0 0 br-wan 192.168.1.1 0.0.0.0 255.255.255.255 UH 0 0 0 br-wan -
@lewis I wasn't talking about the 2nd dns, I was talking about your cam rule on port 80, there are zero hits to that rule.

Why not just make that rule any any to that .241 address - can you ping it? At least until you have validated its working, then you can get more restrictive on the rules.
-
@johnpoz said in OPT1 needs LAN DNS access:
@lewis I wasn't talking about the 2nd dns, I was talking about your cam rule on port 80, there are zero hits to that rule.

Why not just make that rule any any to that .241 address - can you ping it? At least until you have validated its working, then you can get more restrictive on the rules.
Ah ok, probably because nothing is able to connect to the cam.
Yes, I also tried making it 'any'. I can't ping it from an OPT2 client but maybe that's because I don't have a rule allowing pings.
-
@lewis said in OPT1 needs LAN DNS access:
Ah ok, probably because nothing is able to connect to the cam.
Nope not how it works, if pfsense saw traffic that said hey I want to go .241 on port 80 tcp/udp that rule would trigger.. Be it the cam answered or not.. 0/0 says that pfsense never saw any traffic on opt2 that matched that rule.
Or you had a floating rule maybe that triggered before that rule.
maybe that's because I don't have a rule allowing pings.
If your cam is .241 address, make the rule any any to that IP.. Nope a tcp/udp only rule on port 80 is not going to allow for pinging.
example: I don't have a 192.168.42 network, and I block outbound access out my wan to anything rfc1918.. But I created a rule that would match, and then tried to ping that address. You can see that the rule triggered.
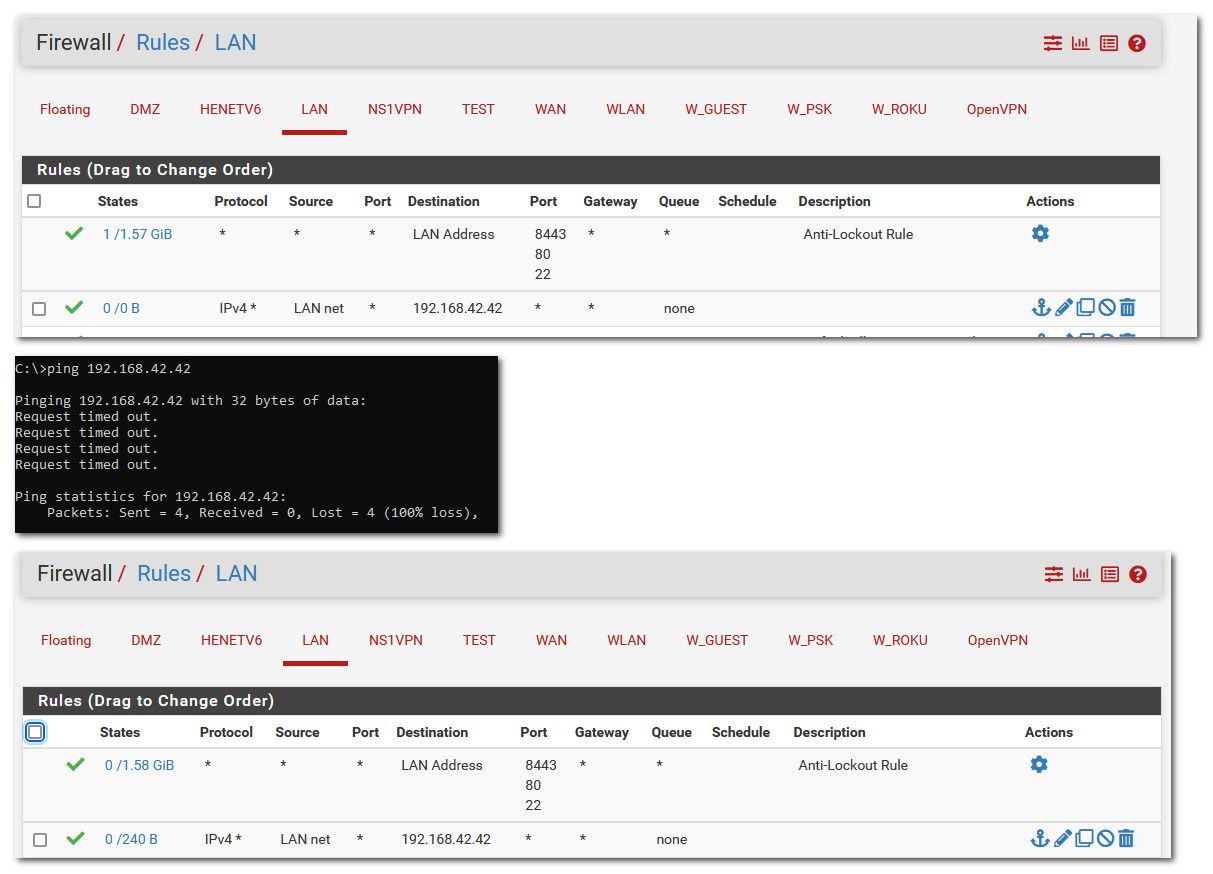
-
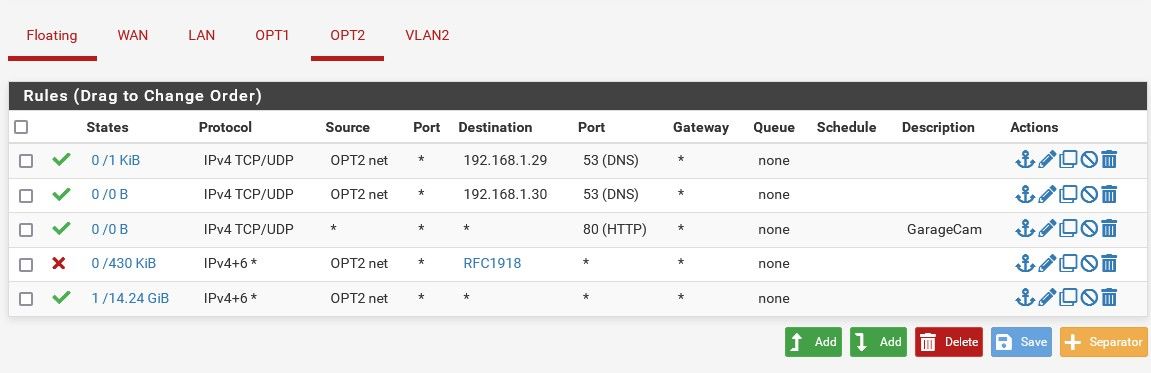
Ok, so as long as traffic gets to the rule, it will show states, no matter if it was allowed or not.
I changed the rule and made it quite open but still cannot get to the camera or ping the device at that IP. I do see something hitting it however.