New OpenVPN server, can connect but can't get to LAN subnet.
-
@viragomann Yes the default gateway for the LAN network it pfsense.
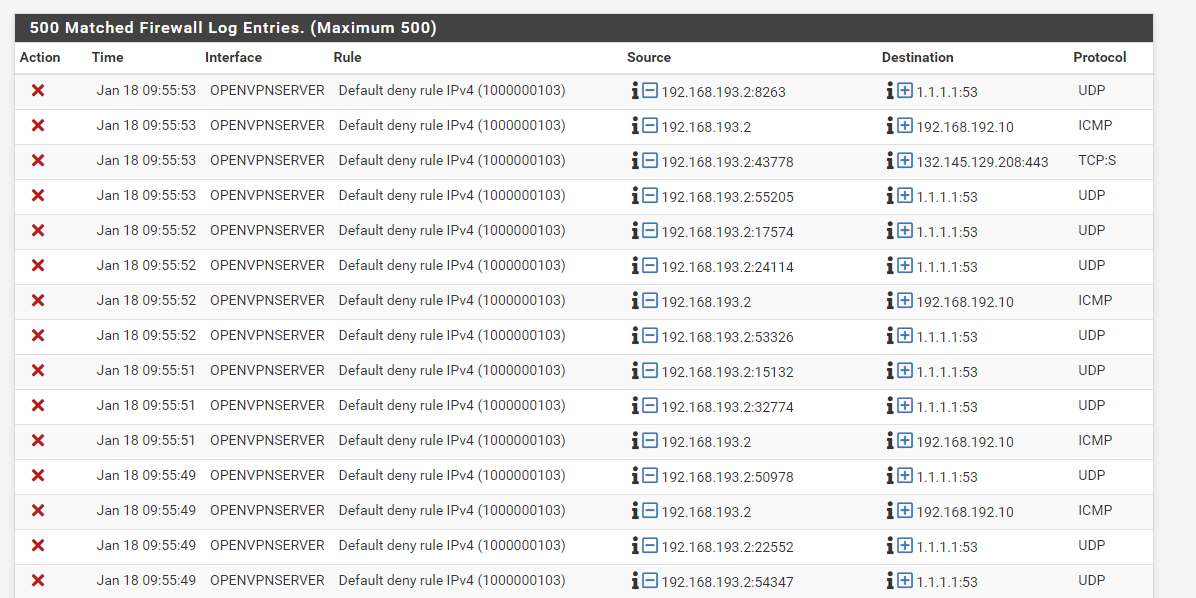
Here are the new logs. I agree much cleaner.
-
@fatman032
Since the ping from 192.168.193.2 to 192.168.192.10 is blocked in the second line, the rule on the OPENVPNSERVER does obviously not match.
So either 192.168.193.2 is not included in "OPENVPNSERVER net" or 192.168.192.10 is not included in "LAN net"I'm wondering, where do you get the "OPENVPNSERVER net" from?
I've also assigned interfaces to access servers, but there is not ...net generated by pfSense.So I'd replace that by 192.168.193.0/24 and try again.
Further the log shows that the VPN client tries to access 1.1.1.1 for DNS resolution, which is not allowed.
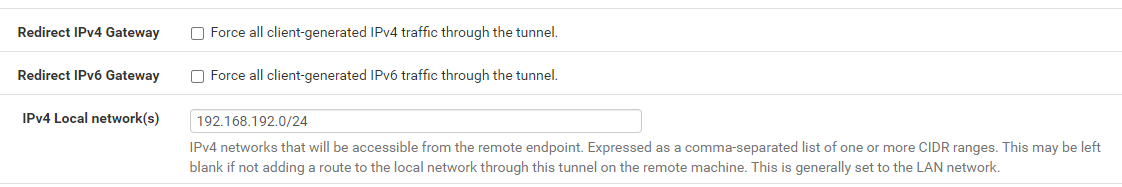
Obviously you route the whole clients upstream traffic over the VPN. Is this what you want?
If yes, you might also have to configure the outbound NAT for the tunnel network. -
@viragomann I changed the rule for OpenVPNserver. Still no go.
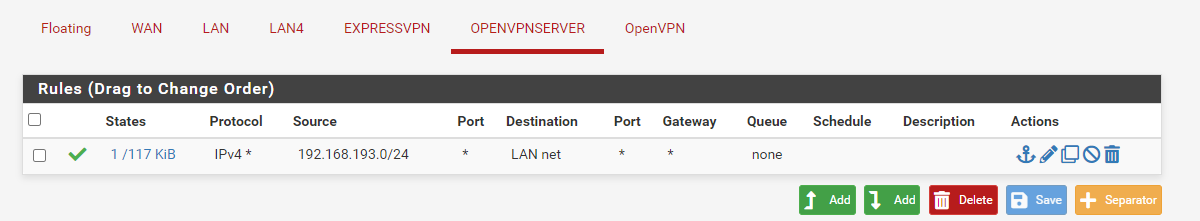
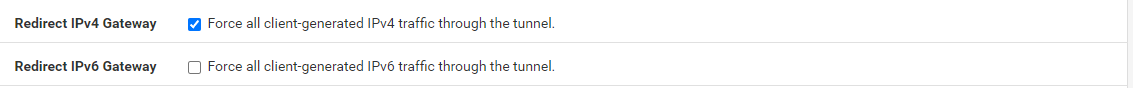
I wouldn't mind a spilt tunnel. If I uncheck the box to "Force all client-generated IPv4 traffic through the tunnel.". I don't get any blocks from 192.168.193.2 (source or destination) but still can't get to my devices.
I do get blocks and lots of them if I check the above box.
-
@fatman032
A view to the logs would be helpful.Is the access from 192.168.193.2 to 192.168.192.10 still blocked by the default deny rule?
If you unscheck "redirect gateway" you have to enter your LAN network into the "Local Networks" to push the proper route to the client.
-
OP is using a bogon address as the tunnel 192.168.193.0/24
Just FYI
-
@chpalmer
No, it's a private one out of 192.168.0.0/16. -
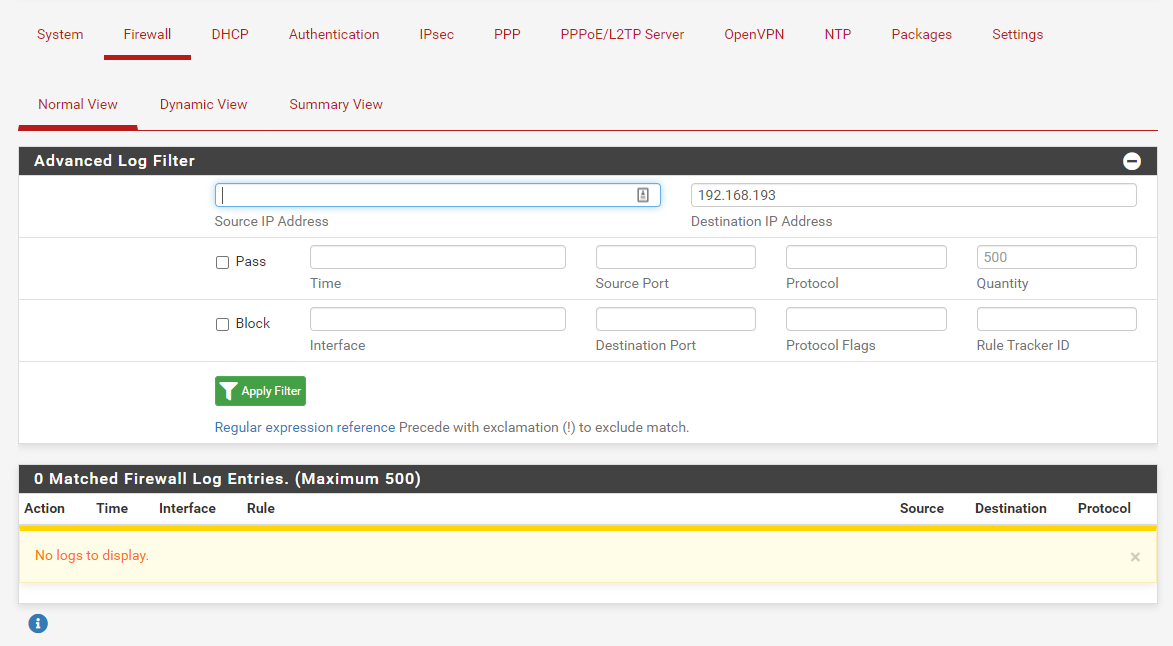
If I setup the VPN this way. I get no blocks from 192.168.193.0/24
Filter source 192.168.193
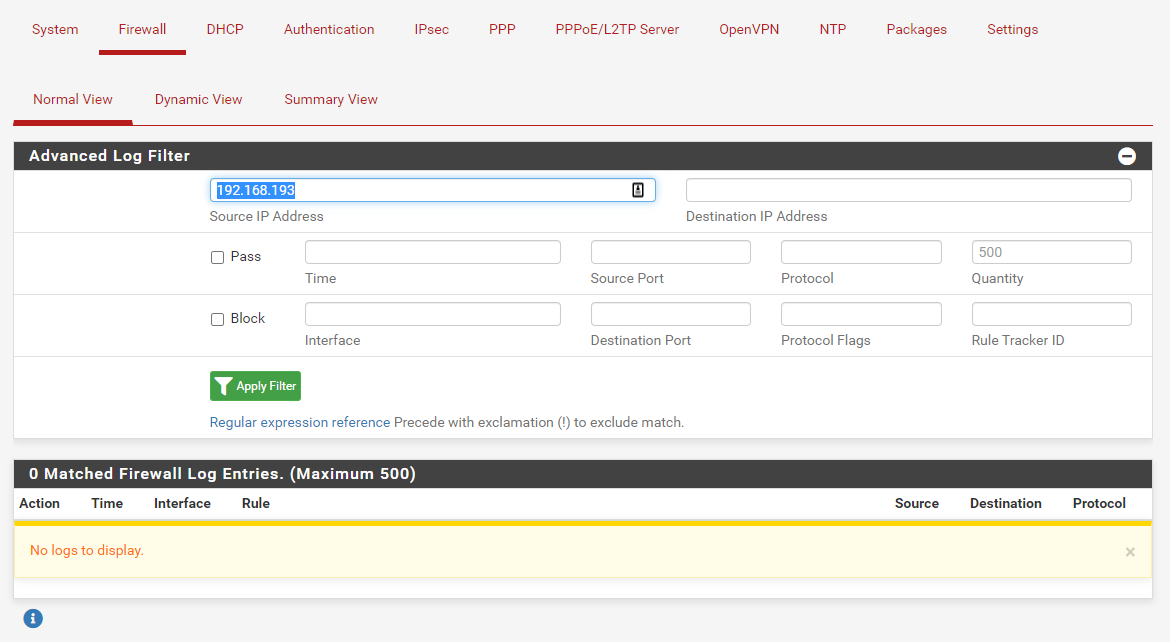
Filter Destination192.168.193
I do get blocks on my WAN interface but I don't think they have anything to do with OpenVPN. I'm little scared to post those log on the internet since they have my public IP address.If I setup the VPN this way.
I get blocks. No filter
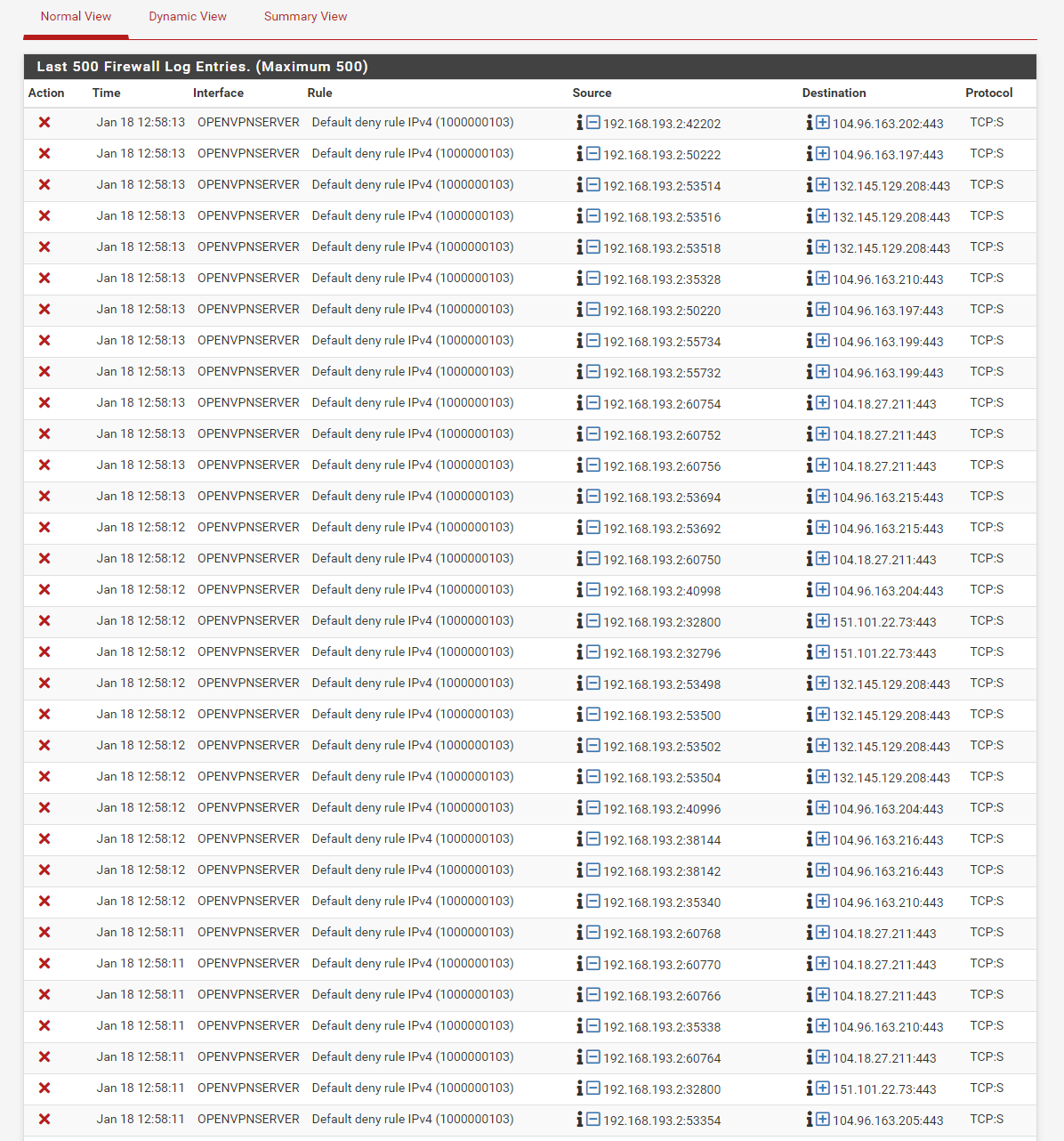
This why I'm so confused.
-
@fatman032 said in New OpenVPN server, can connect but can't get to LAN subnet.:
I'm little scared to post those log on the internet since they have my public IP address.
No, you shouldn't show your public IP here. If the logs were relevant you can disguise it, but they might not be.
This why I'm so confused.
All right with that now. The log shows solely blocks to public IPs.
I mentioned already above, by checking "Redirect gateway" the client routes the whole upstream traffic to the vpn server. But your pass rule on OVPNSERVER doesn't allow it, it permits access to LAN net only. -
I mentioned already above, by checking "Redirect gateway" the client routes the whole upstream traffic to the vpn server. But your pass rule on OVPNSERVER doesn't allow it, it permits access to LAN net only.
I understand that. I just wanted to show this is the only blocks I'm getting now. Also I setup a NAT rule to allow 192.168.193.0/24 out. Not sure why they are still getting blocked. This isn't the part I'm confused on.
The part that I don't get is why I'm not seeing any blocks now form this network to my LAN network.
-
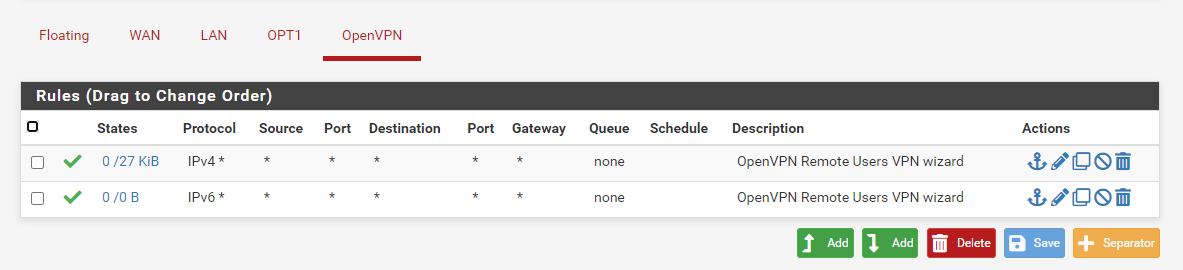
@viragomann Should I have any rules under OpenVPN?
-
@fatman032 said in New OpenVPN server, can connect but can't get to LAN subnet.:
The part that I don't get is why I'm not seeing any blocks now form this network to my LAN network.
Possibly because pfSense doesn't block any.
Maybe the remote device blocks the access by its own firewall. Since you said, this was already working before, this shouldn't be the case, but possibly you had set up a workaround with masquerading.To investigate on pfSense you can take a packet capture on LAN, while you try to access from the remote client to see if the device is responding properly.
-
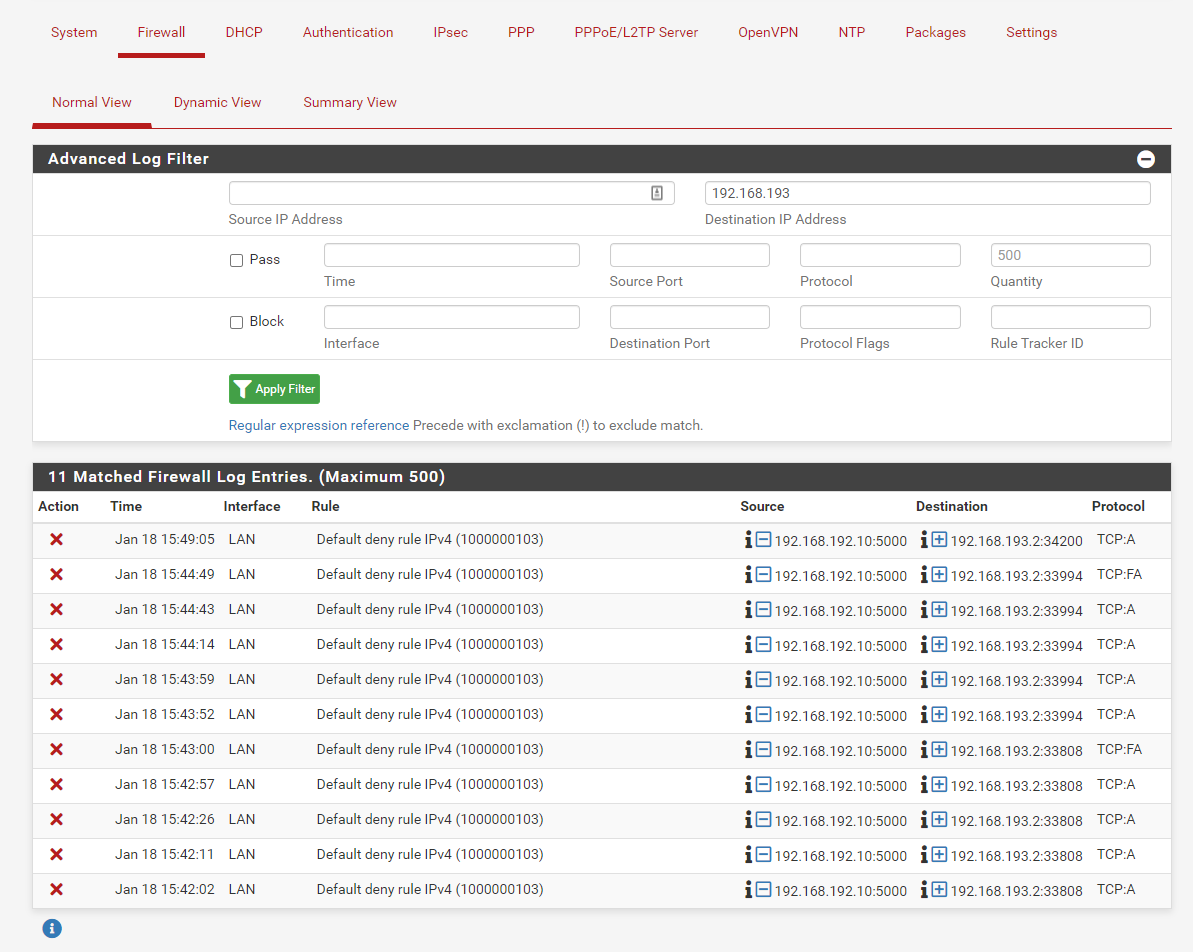
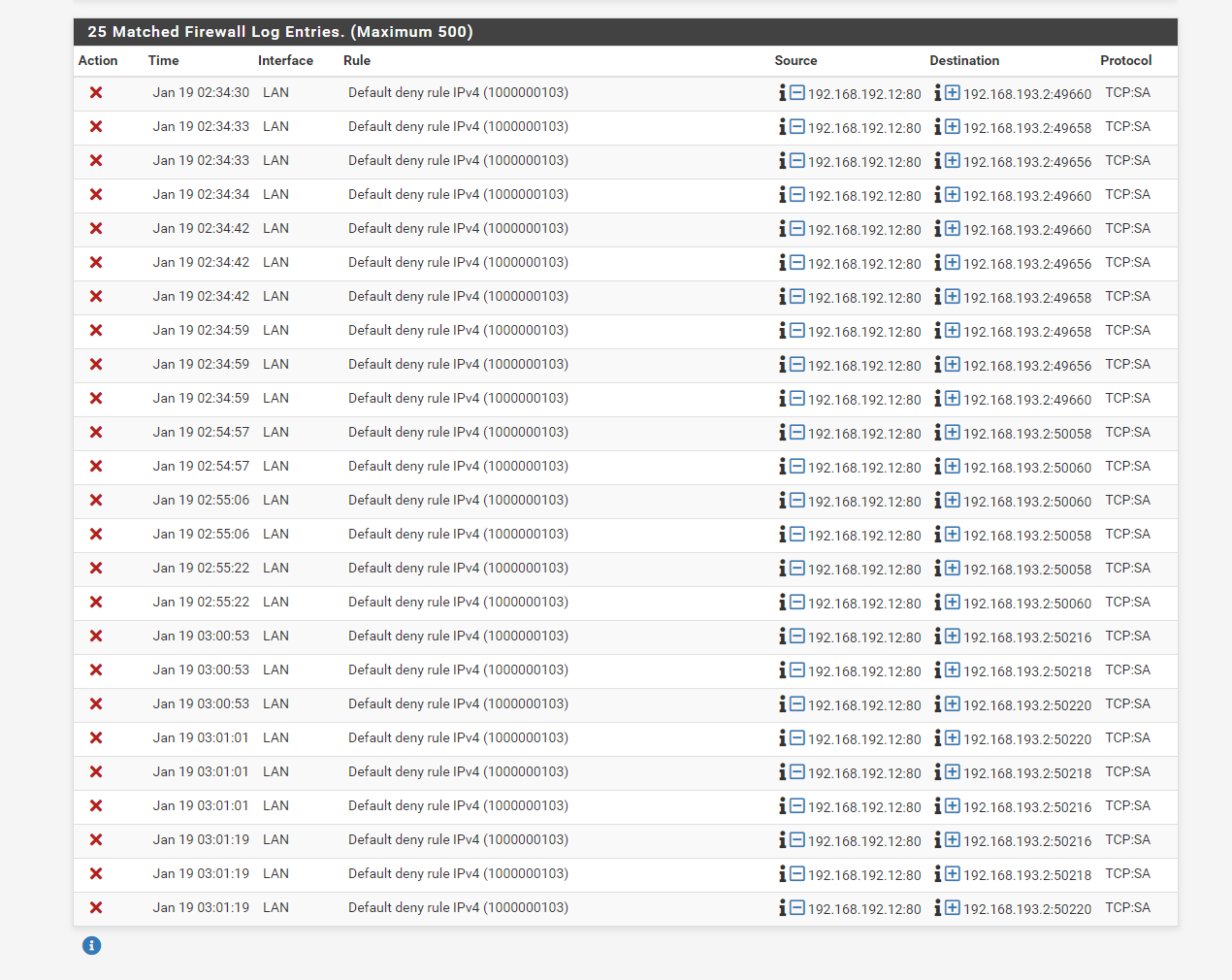
@viragomann I think I found part of the problem. I added the OpenVPN rule back in. I can now see blocks from 192.168.193.2
-
@viragomann said in New OpenVPN server, can connect but can't get to LAN subnet.:
@chpalmer
No, it's a private one out of 192.168.0.0/16.I see that now.. I was an octet off.
-
@fatman032
These blocks are out of state packets. That is no traffic which should be allowed at all.
However, I've no idea, why you see this only, when you allow traffic on the OpenVPN interface.Is the port 5000 this one you tried to access from the remote client?
-
@viragomann Nope I can try any LAN IP device and I get the same thing. At this point I'm about restore my entire firewall and start over. The other strange part is when I try to reset the states it basically is crashing the browser. I read this might be because it is running into some sort of error and can't rebuilt the states.
-
@fatman032
Do you have a Synology which you tried to access from the client? -
@viragomann yes and a raspberry pi is hosting a web server that I play with. I block all traffic on it so it can't get out to the internet. This is part of the reason I want to setup the VPN.
-
@fatman032
So maybe on the vpn client runs any software, which is accessing it. But the Synology may send responses to another destination than pfSense, because it uses another default gateway. -
Okay so I factory reset my pfSense. I have nothing plugged into my network but one computer and my raspberry pi at 192.168.192.12.
My LAN network is 192.168.192.0/24I setup the VPN using these setups instructions.
I have no other VLans no other VPNs. I have two any to any rules on every interface. One for IPV4 and one for IPV6.
I'm still getting a default deny rule. I have no idea what is going on.
I know this is not the ideal setup. I just want to get everything out of the way that could be causing this problem. I have no idea how this can be blocked. I don't remember my other netgate being this big of a pain to setup. Is there something different with this new SG-2100?
-
@fatman032
Again, it look like that the raspberry is sending response not to pfSense, but to another device.So go to the Pi and check out his routing table to get any further, please.