MAC Passthrough
-
Your device is listed in the "MACs" table
@worlddrknss said in MAC Passthrough:
--- table(administrators_pipe_mac), set(0) ---
XX:XX:XX:XX:XX:XX any 2003 6845 2818160 1645293467
any XX:XX:XX:XX:XX:XX 2002 13520 15935201 1645293467that is, if XX:XX:XX:XX:XX:XX is the MAC being used.
Look at the numbers :
XX:XX:XX:XX:XX:XX any 2003 6845 2818160 1645293467
any XX:XX:XX:XX:XX:XX 2002 13520 15935201 16452934672003 and 2002 are the pipes, these are constants.
1645293467 and 1645293467 are probably ipfw firewall rule indexes, constants
But these : 6845 2818160 and 13520 15935201 are bytes passed.Do a ping test.
Note down the numbers - also the final block rule :
@worlddrknss said in MAC Passthrough:
65534 9820 8111146 deny ip from any to any
and re do a ping test.
What changes ?
If none of the numbers in the table administrators_pipe_macchanged, then your MAC wasn't used.Btw : when you turned of the captive portal, pings are passing, this means the the GUI firewall (pf) isn't the issue.
--- table(cp_ifaces), set(0) --- bge1.4 2100 189541 158255829 1645293467bge1.4 : Your are using VLANs ?
It's time to packets capture your portal interface, and do you see the 'ping' packets coming in ? The VLAN interface tag is "4" ? (because if not, you've your answer) -
I don't think there is a link with VLANs as I have the same problem with and without VLANs on different configurations.
On the other hand, I tested by removing the tag1 from ipfw (/etc/inc/captiveportal.inc lines 590,692,744&746) in order to return to the way it was in 2.5.2 and it's no better.
-
@leofox I might just go back to 2.5.2 where Captive Portal worked, or just wait a few releases and see if they figure out the issue. CP isn't that huge of a deal for me as I was just using it as a secondary security option to port security.
-
You did a ping test while watching the "bytes counters" ?
The final block rule - line 65534 - was incrementing ?
The xxxxx_pipe_mac table content : your MAC, the counters were incrementing ?
Another line ?edit :
Look at the last line :
65535 0 0 allow ip from any to anyThis is a "pass all traffic line".
What happens when you place the same line at position 1, like
ipfw add 1 allow ip from any to anyNow the entire captive portal "ipfw" should be transparent as everything passes right at the start ?
Try also other positions. Did the rule go hit/matched ?
Btw : if a rule like "02108" exisys, you can create second "02108".
But when you delete "02108", you delete them both. Just restart the portal to recreate all the rules. -
Adding the following (excluding the Administrator Network):
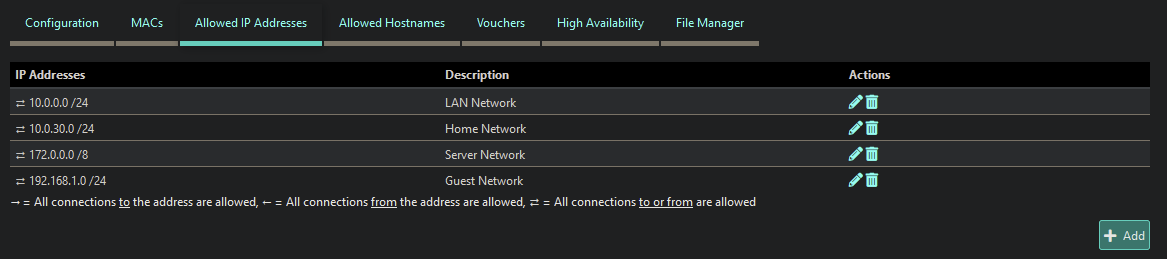
Fixed the internal ping issues, but ping over the internet is still being blocked. Eg: google, msn, yahoo, etc. -
This is related to: https://forum.netgate.com/topic/169879/udp-icmp-is-not-working-after-upgrade-to-2-6-0/2 and https://redmine.pfsense.org/issues/12834
-
Good point about these links. Indeed, my Windows clients can no longer reach the AD domain either, which is the problem with the UDP protocol.
-
I can also confirm this issue. I recently upgraded to 22.01 on my Netgate 1100 appliance.
Users authenticate via a freeradius server with Pass-through MAC automatic additions enabled. Before, once a user authenticated and got past captive portal, nothing was blocked as the only firewall rule on that interface was to allow any IPv4 traffic, anywhere.
After the upgrade, those with authenticated MAC addresses are only allowed basic web traffic. I can no longer connect to a VPN, ping DNS servers outside the network, or even ping the WAN address or gateway address. The only fix is to disable Captive Portal which I obviously don't want to do.
The network diagram is:
Modem >> Netgate 1100 >> UniFi Switch >> UniFi Access Points
The UniFi switch is connected to the OPT1 (192.168.10.1/24) interface on the router that captive portal is active on. I've got a dumb switch connected to the LAN (192.168.1.1/24) interface that connects all the wired PC's in our office.
-
@all
I wouldn't believe it.
I've installed the App of my Expr*ss VPN ISP to my phone, and Pad, and connected both to my captive portal.
I fired up the VPN App.
Initially, no connection could be made. That's new .... because it was falling back to a TCP tunnel, it connected.I'm using my portal for hotel client, and no one, complained .... yet. I guess most clients use the wifi just to check mails, update FB, and watch Netflix anyway.
II think the "pipes" used by the portal connections have an issue.
You can see them here : Diagnostics > Limiter Info
These "pipes" are also used for the bugger bloat limiters I was using before, this is not possible any more with 2.6.0. I can live with that. But the captive portal partially broken .... hummm. Never saw that before.When I remove all connected clients.
And I de activate the captive portal, all limiters and schedulers should be removed, right ?
Wrong :These stay in place :
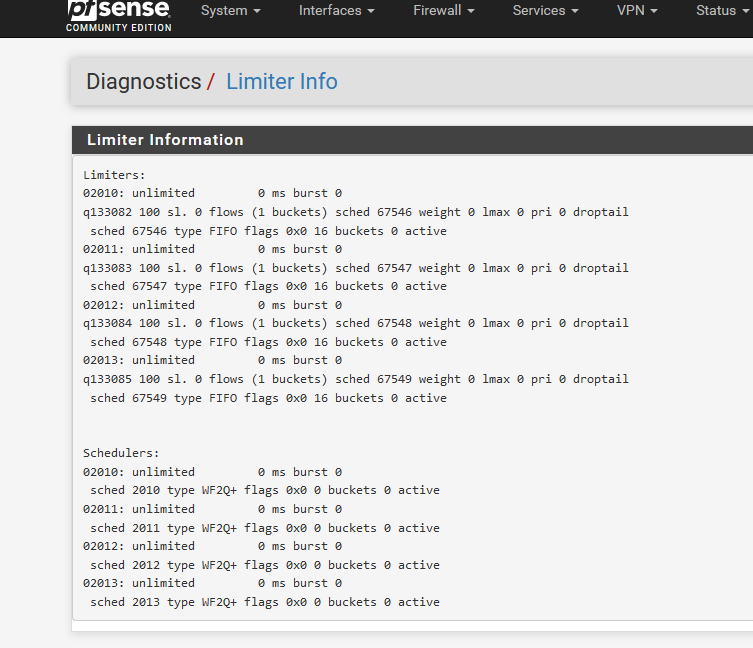
This should also be 'empty' :
[2.6.0-RELEASE][admin@pfsense.mynetwork.net]/root: ipfw table all list --- table(cp_ifaces), set(0) ---[2.6.0-RELEASE][admin@pfsense.mynetwork.net]/root: ipfw table all list --- table(cp_ifaces), set(0) --- [2.6.0-RELEASE][admin@pfsense.brit-hotel-fumel.net]/root: ipfw show 00999 1093652 159826765 allow tagged 1 01000 3334509 3552256101 skipto tablearg ip from any to any via table(cp_ifaces) 01100 25766627 20440009158 allow ip from any to any 65534 51291 14897634 deny ip from any to any 65535 144 33784 allow ip from any to anyas the captive portal is de activated.
I rebooted pfSense :
[2.6.0-RELEASE][admin@pfsense.mynetwork.net]/root: ipfw show ipfw: retrieving config failed: Protocol not available [2.6.0-RELEASE][admin@pfsense.mynetwork.net]/root: ipfw ipfw table all list ipfw: bad command `ipfw'this is normal, no portal == no ipfw loaded.
I have a pfSEnse home setup @home. I'll do some testing this weekend.
edit 2022-03-01 :
Pipes or limiters are probably another issue, or not the issue at all
When I introduce a '00998' rule like this :
2.6.0-RELEASE][admin@pfsense.portalbroken.net]/root: ipfw show 00998 94719259 85479897044 allow ip from any to any 00999 5485259 1007470890 allow tagged 1 01000 11615464 11431517900 skipto tablearg ip from any to any via table(cp_ifaces) 01100 93906271 71988908641 allow ip from any to any .....00999 and further are default captive portal ipfw rules.
My captive portal becomes 100% transparent, that is : still no UDP neither ICMP, just TCP.
Looks like the issue is ipfw ....
-
I ended up just reinstalling the firmware on my Netgate 1100 until this gets resolved. I followed this guide and requested access to version 21.05 in a support ticket. Install went fine and after restoring my config, everything works as it should.
-
Read https://forum.netgate.com/topic/170300/new-system-patches-v2-0?_=1646343673426 - Apply patch (Redmine #12834) and ICMP/UDP will be handled just fine.
-
It's ok for me. The patch has fixed the issue. Thanks.