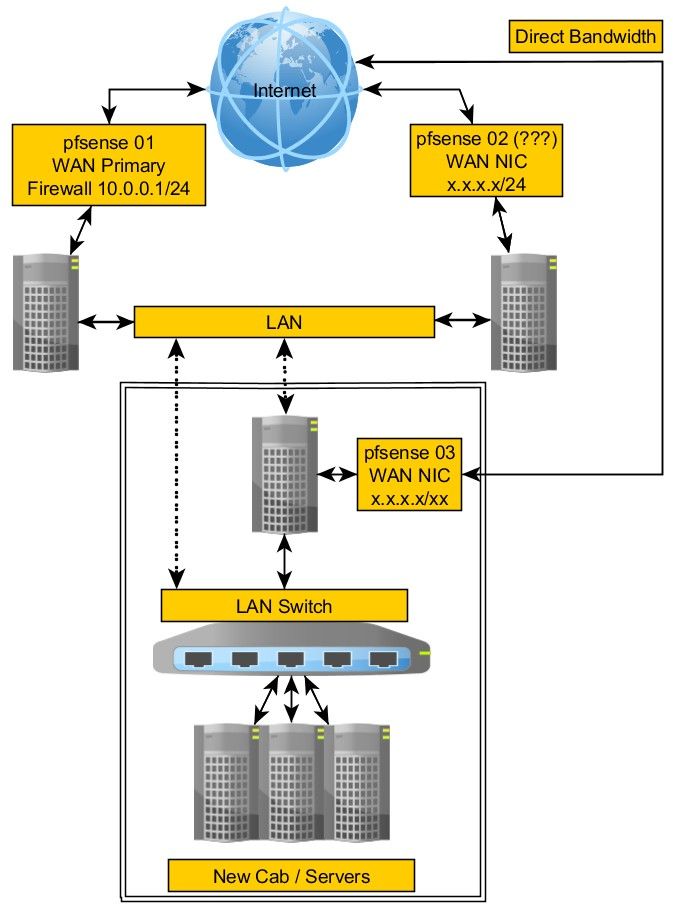
Using pfsense with multiple WANs
-
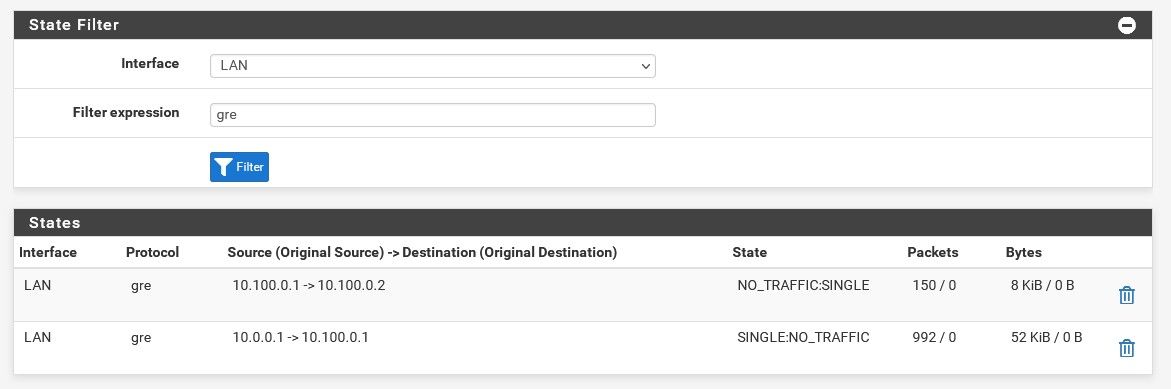
Try filtering by
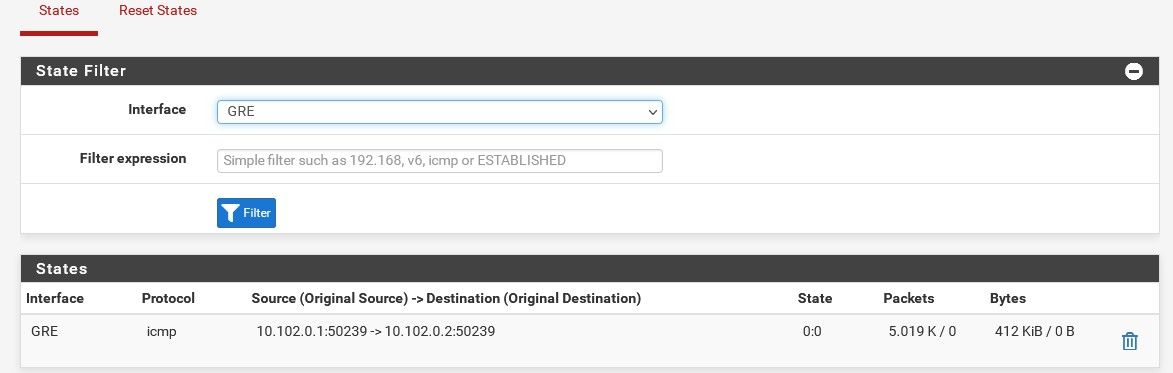
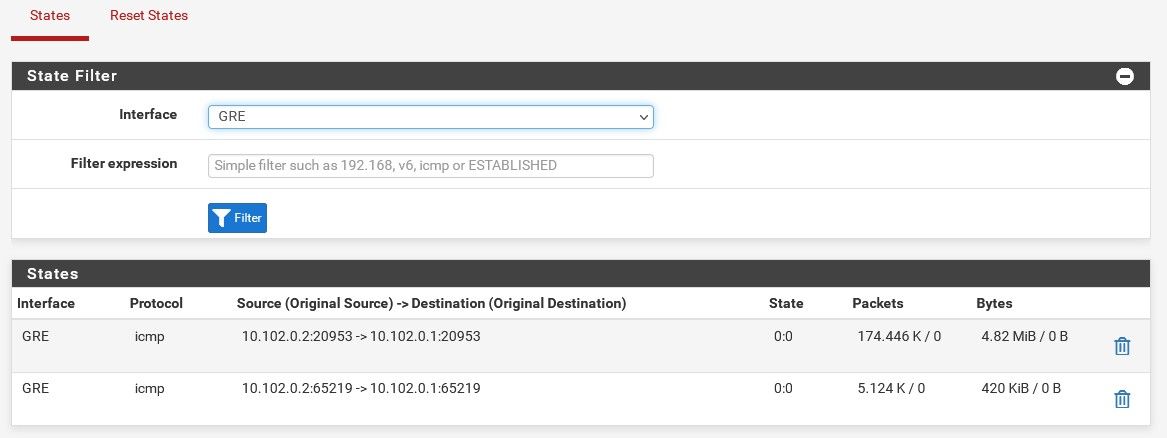
gre. You should see the states with traffic both ways: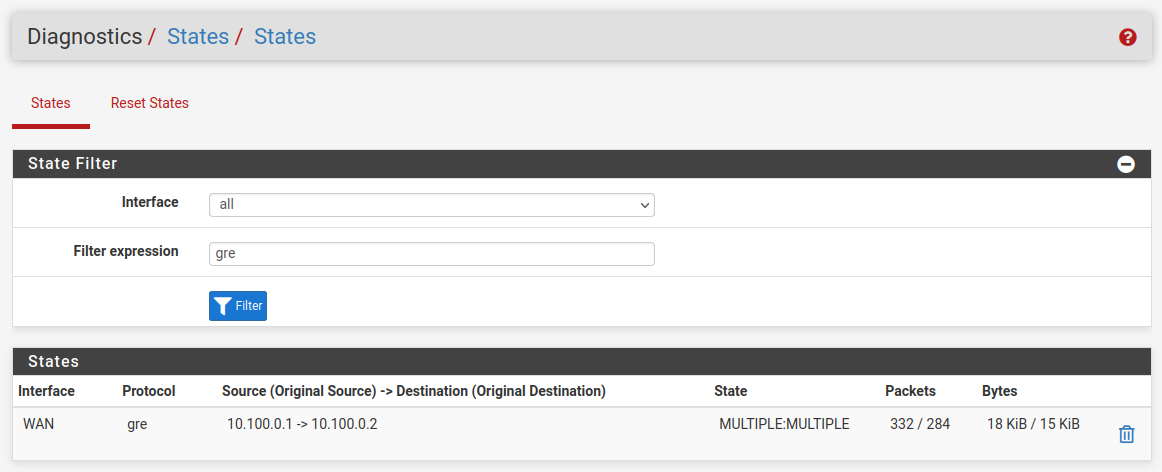
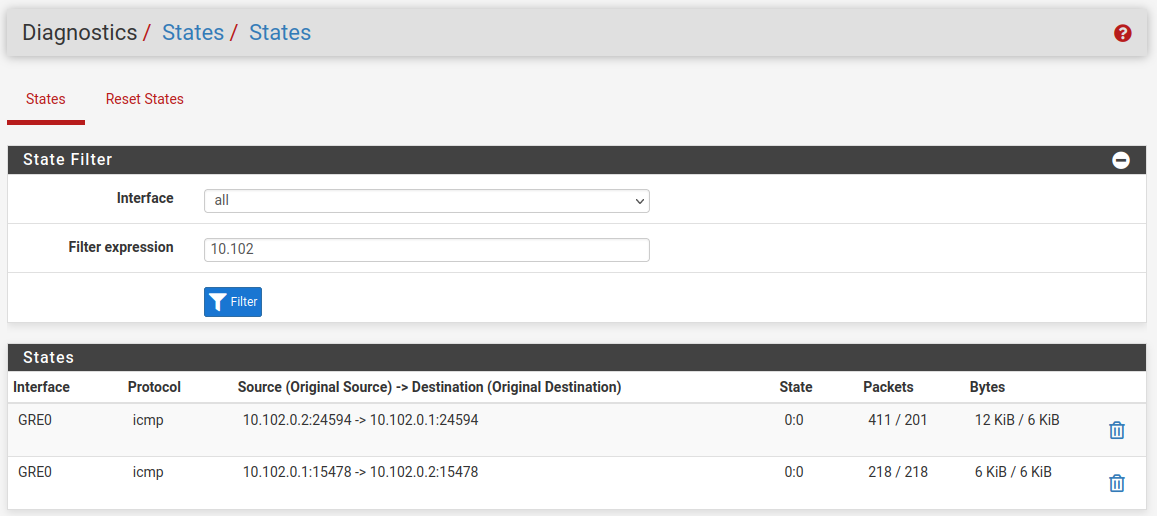
And if it's passing correctly you should see both those gateway monitoring pings replying:
It looks like there is no incoming state there so either the firewall rules are blocking it, check the firewall logs, or one side has no route for some reason.
Steve
-
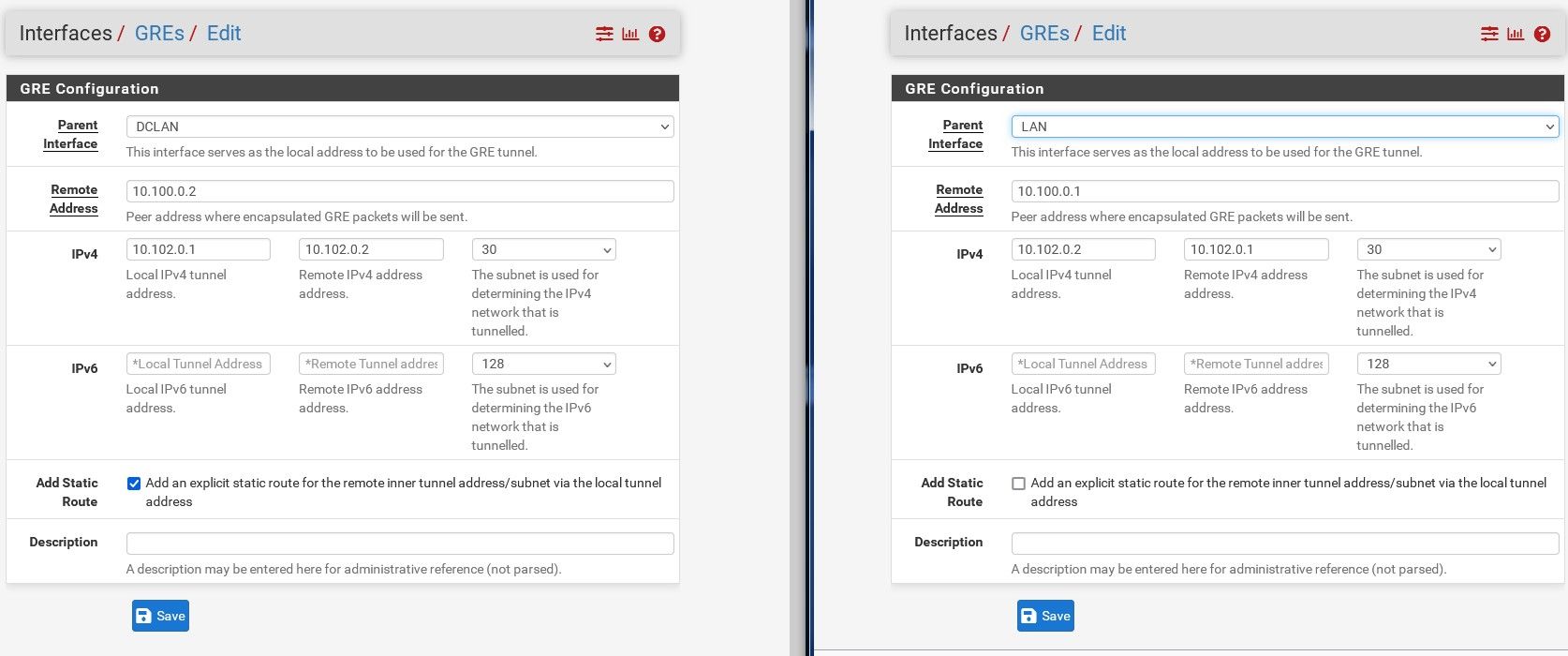
I note that you have set 'add a static route' in the GRE setup at the pf01end. I have not done that in my test setup here.
-
My main fear at this point is messing up pf02 and causing down time since that is production.
I've removed the static. I think I enabled that because of something I read. And that's one problem with reading about something like this. People have different variations so when you've never done it and don't get the concept yet, it's easy to make a mess of tests.
I think this is where I'm at now and I've removed all rules, again, because I'm nervous about messing up prod traffic. I'll re-add slowly.
I added an ICMP rule allow all on both LAN and GRE on pf02 and cannot ping 10.102.0.2 from the pf01 CLI. However, I can ping 10.100.0.2 from pf01 and vise versa.
-
Do you see gre states open on both firewalls?
-
-
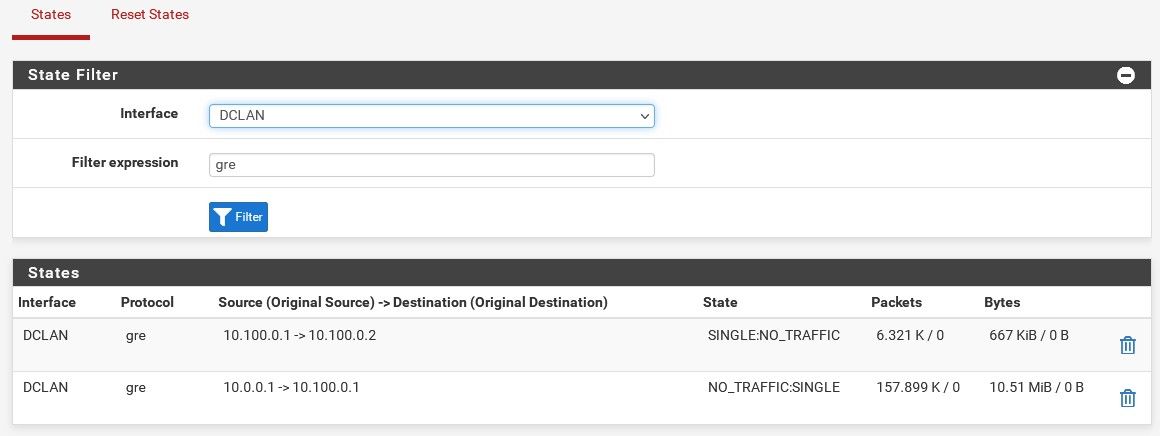
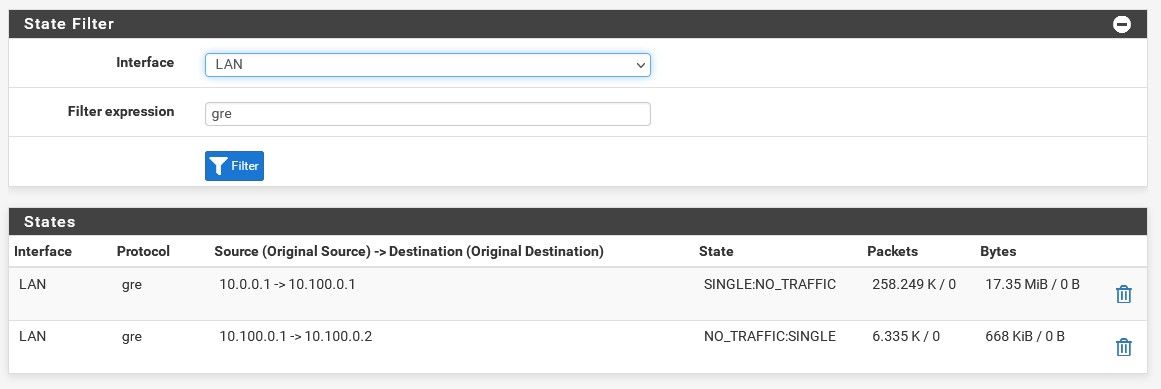
Not states on the GRE interfaces, gre states on the LAN and DCLAN interfaces.
Just filter by
greon all interfaces as I showed above. -
All this time, I'm still pinging from one pf to the other.
-
You said most times that I seemed to have things set right other than the masks. I've updated those but still cannot ping between GRE sides. What in the world am I missing?
-
Ok, so the problem becomes apparent. On one side (looks like pf02) the GRE tunnel is incorrectly using 10.0.0.1 when it should be using the VIP address, 10.100.0.2.
So probably it is set to be on the LAN there and should be on the VIP.Steve
-
One guy tells me, why bother with a GRE tunnel? Just use DNAT.
I gave him an example of wanting to reach a vm at 10.0.0.120 port 443 behind pf02 from the LAN on pf01.He says, create a dnat on pf02 10.100.0.120:443 to 10.0.0.120:443
Not really sure what he's talking about but he's got a point. I can ping 10.100.0.2 on pf02 so doesn't that mean there's already a way to get this to work? I just don't understand how to map/route private IPs to private IPs.
Maybe I just need to create a new network, 10.100.0.1/24 and map pf02 IPs to that?
Mind blown here. All week on this.
-
This post is deleted! -
@stephenw10 said in Multi LAN networks to one pfsense:
Ok, so the problem becomes apparent. On one side (looks like pf02) the GRE tunnel is incorrectly using 10.0.0.1 when it should be using the VIP address, 10.100.0.2.
So probably it is set to be on the LAN there and should be on the VIP.Steve
I see that in the image I shares but not in the config anywhere.
-
@lewis said in Multi LAN networks to one pfsense:
He says, create a dnat on pf02 10.100.0.120:443 to 10.0.0.120:443
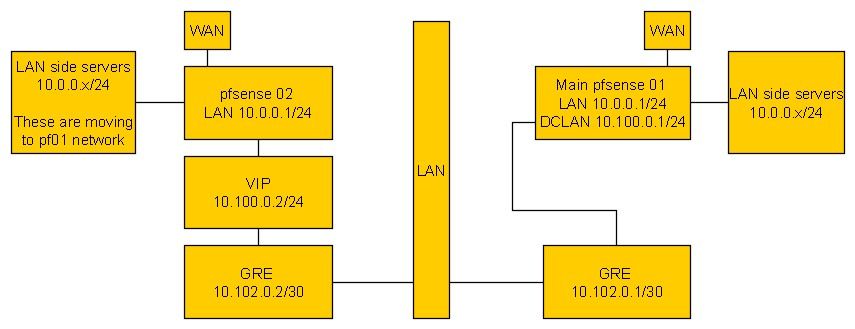
10.100.0.120 doesn't exist but assuming you create it as a VIP on pf01 you can do that. But it will only work for one pfSense instance forwarding traffic because that is the gateway on pf01 DCLAN.
If you try to something similar from pf03 without a GRE tunnel replies will go back via pf02 resulting in an asymmetric route and blocked traffic.
Steve
-
@lewis said in Multi LAN networks to one pfsense:
I see that in the image I shares but not in the config anywhere.
I expect that is i the GRE tunnel config on pf02.
-
It's still like this cept the masks are now /30 and static is disabled on both sides. Where is that 10.0.0.1 coming from then?
-
@stephenw10 said in Multi LAN networks to one pfsense:
@lewis said in Multi LAN networks to one pfsense:
He says, create a dnat on pf02 10.100.0.120:443 to 10.0.0.120:443
10.100.0.120 doesn't exist but assuming you create it as a VIP on pf01 you can do that. But it will only work for one pfSense instance forwarding traffic because that is the gateway on pf01 DCLAN.
If you try to something similar from pf03 without a GRE tunnel replies will go back via pf02 resulting in an asymmetric route and blocked traffic.
Steve
What I meant is that instead of a VIP, what if I created a new /24 network interface instead of a tunnel? Most everything is port forwarded so really, to move things from pf02 to pf01, I mainly need to access one host/server at a time, then forward that access from pf02 to pf01.
-
I'm just not sure where that 10.0.0.1 is coming from. Maybe it was something I was playing with when I took the pic but it's gone now.
Not sure if it's strange or not but to simply try something new, I deleted all the GRE stuff on both pf. I then created a VIP of 10.100.0.120 on pf02 and port forwarded that to a vm at 10.0.0.120 but even with a full any any rule, I can't reach that vm from pf01.
Weee, how could nothing work?
-
You need to change the parent interface for the GRE tunnel on pf02 to the VIP.
Right now it's set as LAN in your screenshot and that's 10.0.0.1.
Steve
-
Was not able to find that. I removed everything so I have a clean slate. I'm starting all over right now.
pf01: I have 10.100.0.1/24 on DCLAN.
pf01: I have 10.0.0.1/24 on LAN (10g1LAN).pf02: I have 10.0.0.1/24 on LAN.
pf02: I create a VIP of 10.100.0.2/24 on LAN interface.pf01: I create a GRE tunnel on DCLAN.
Remote address: 10.100.0.2
IPv4 local: 10.102.0.1 /30
IPv4 remote: 10.102.0.2/30
I do not enable static.
New interface shows up so I add it. I rename it to GRE and enable it.pf02: I create a GRE tunnel on LAN.
Remote address: 10.100.0.1
IPv4 local: 10.102.0.2/30
IPv4 remote: 10.102.0.1/30
I do not enable static.pf02
New interface shows up so I add it. I rename it to GRE and enable it.Now I can ping from either side but only to the GRE IPs, not the tunnel ones. (Sorry, don't know the correct terms yet).
pf01: ping 10.100.0.2 = replies
pf02: ping 10.100.0.1 = repliesThis is where I'm at now.
States on pf02 still show 10.0.0.1.
-
@lewis said in Multi LAN networks to one pfsense:
pf02: I create a GRE tunnel on LAN.
Nope, it must be on the VIP otherwise the source IP will be wrong as you are seeing.