"Google 1e100 addresses" & Google invaled certificates "Common Name invalid2.invalid"
-
Stephen,
I just not know, in principle everything which is allowed to pass is/should be passed via rules above these final rules.
I would like to log all things which are not passed by the rules above these end rules, with the exception of the tcp-rules having states like "RA / PA / FPA"
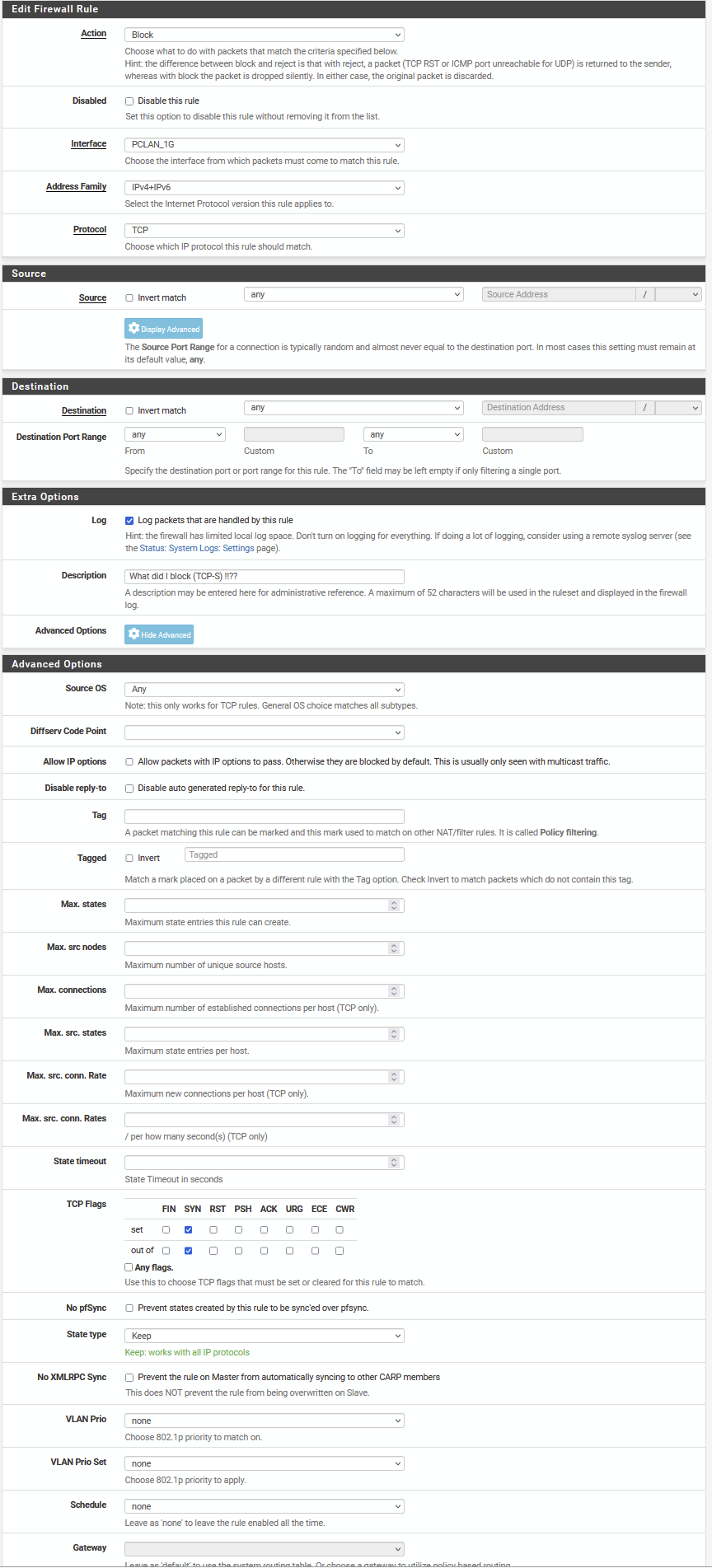
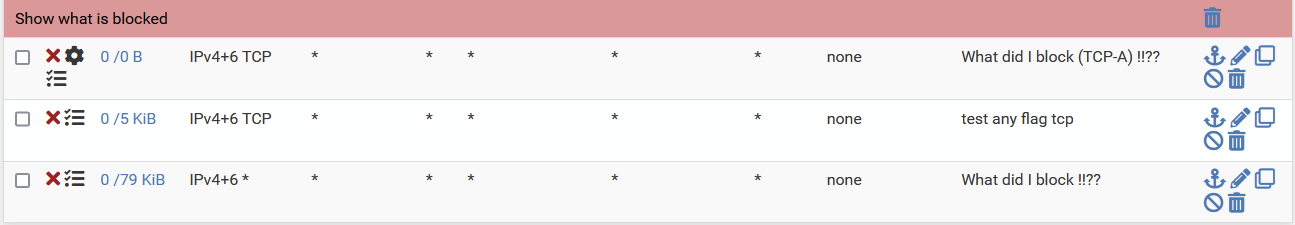
So for that reason three end rules:
- first one intended to log tcp-S (because I would like to see what I perhaps should have passed)
- the second rule is "not to log" the rest of the blocked tcp (the RA / PA / FPA etc). (for this test the log is on)
- and the final rule is to log the rest (not being tcp)
As said my problem is that the first two rules, intended to deal with TCP, do not work !! WHY O WHY !?
-
What does the second rule actually look like?
The first rule should only match anything if the pass rules above are wrong. So that fact it isn't is a good thing!
You either need one rule to block anything TCP:ACK or you need three rules for each of those flah combinations. You can't match all three specific combinations with one rule.
Steve
-
-
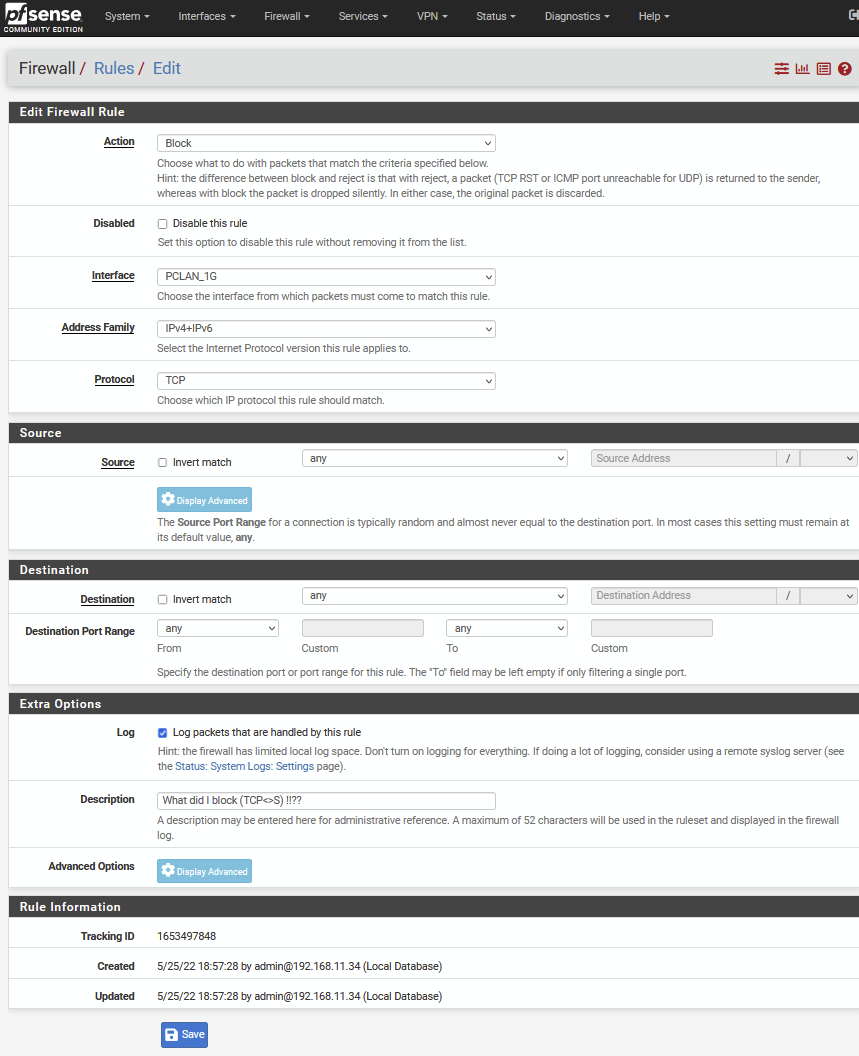
There are no flags set on that second rule. So it won't match.
Change the first rule from SYN to ACK. Remove the second rule.
-
..... I do not understand any thing related to rules which have to capture a certain tcp state ....
I tried
three rules in a row where I did expect the first rule to trigger on tcp packages having "RA / PA / FPA"
I used
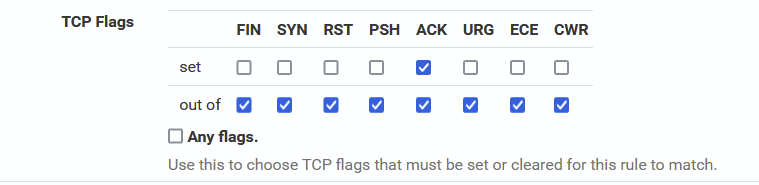
there and did also test with ^out of "ack"^. In both cases nothing triggered the ruleSo I tried the second rule, setting ^TCP Flags^ to ^Any flags^. This rule seems to fetch the FA etc.
However, I really do not understand
-
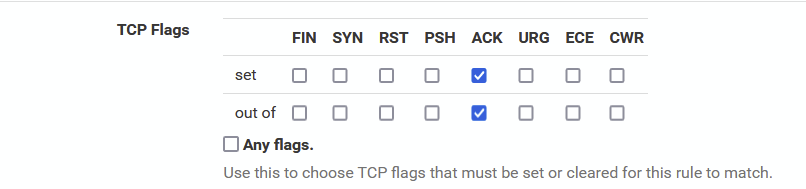
Ah, OK. No that needs to be this:
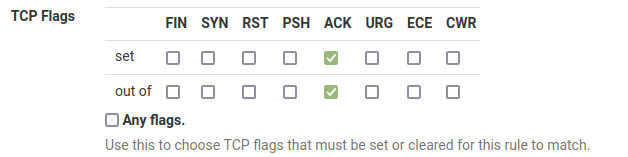
It means: The ACK flag must be set, only check the ACK flag.
The rule that you have says: check all flags and match packets that have only ACK set. Which wouldn't include any of the blocked traffic you were seeing that all has multiple flags set.
Steve
-
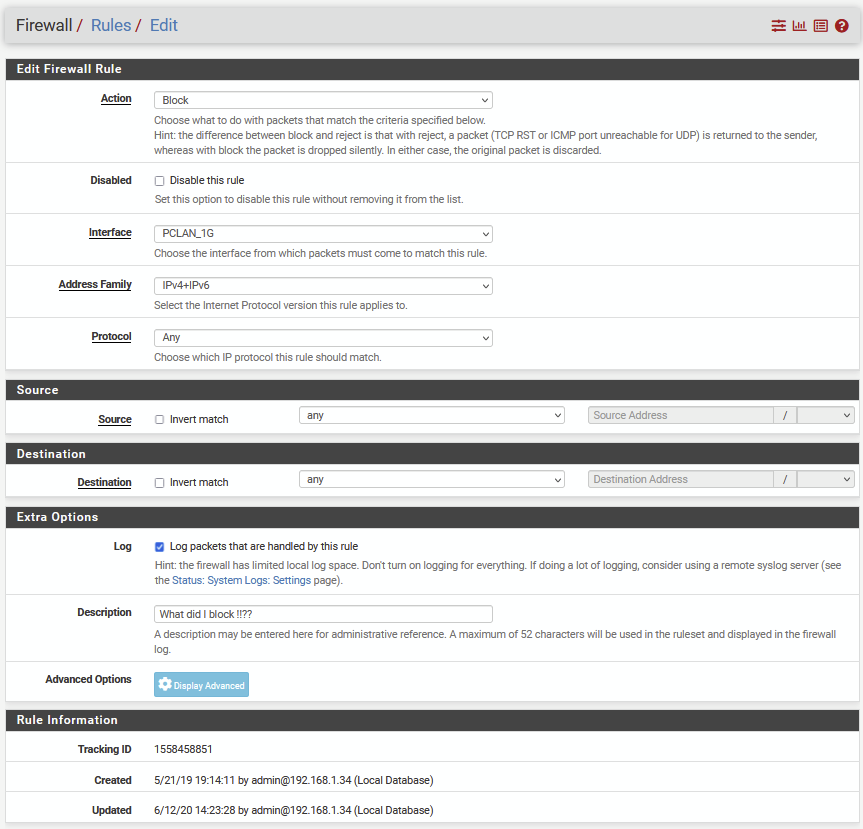
I am using these two rules now, which seems to work
First rule is defined like this (I did try that before, but not likely good enough)
Still wondering what "Any Flag" is supposed to do
-
@louis2 I personally wouldn't do it that way ;)
I would just turn off the default log. This removes all the other unwanted log stuff like multicast broadcasts and the like, stuff from link-local addresses, etc.
And then create a rules at the end to block, and only log stuff that has syn set. And then a rule to log any sort of common udp ports you want to see..
-
The 'Any flags' box will cause it to match TCP packets with any combination of flags. That means you can pass traffic that is asymmetric for example.
Steve
-
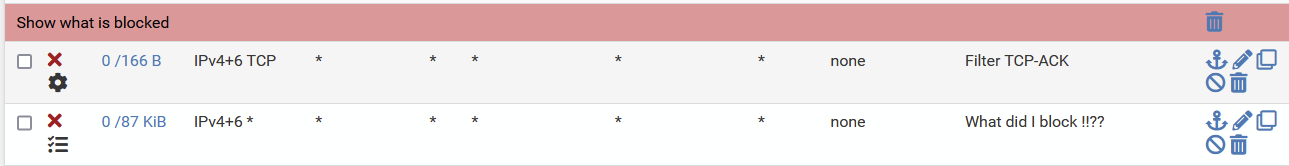
The Filter TCP-ACK rule works, however ....... does change the firewall behavoir in a couple of ways. Suddenly new loggings occur which where not there before.
Conclusion is that this rule must be changing some FW internal state table ....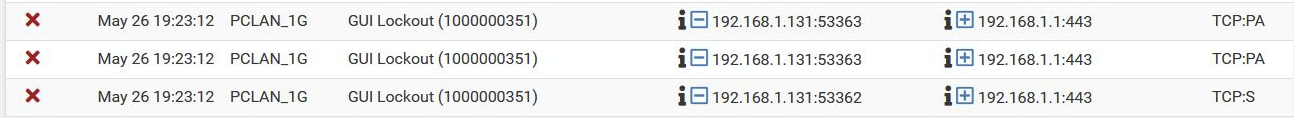
Let me start with the logging above. I did never see that message before, but apart from that, it is communication between two devices in the same subnet. And communication within one subnet normally does not pass the FW. Where this is of course a strange situation, since one of the communication parties is the FW itself.

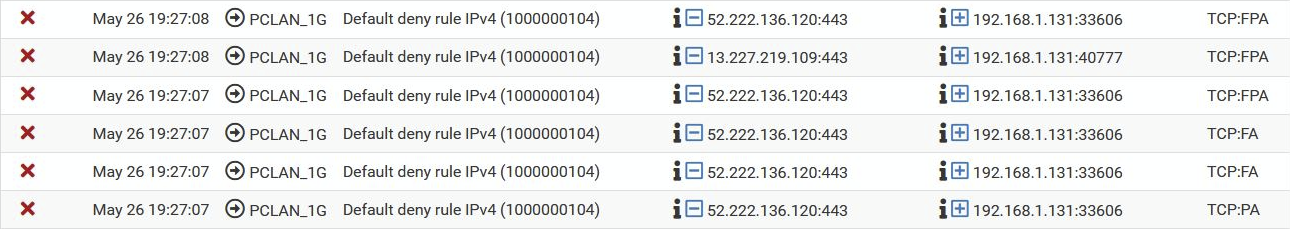
Here we see a second effect. A message from the floating rule set "Default deny rule ipv4".
Here a set of the same "Default deny rule ipv4", however it is different since the source is somewhere on the internet (google / amazon)
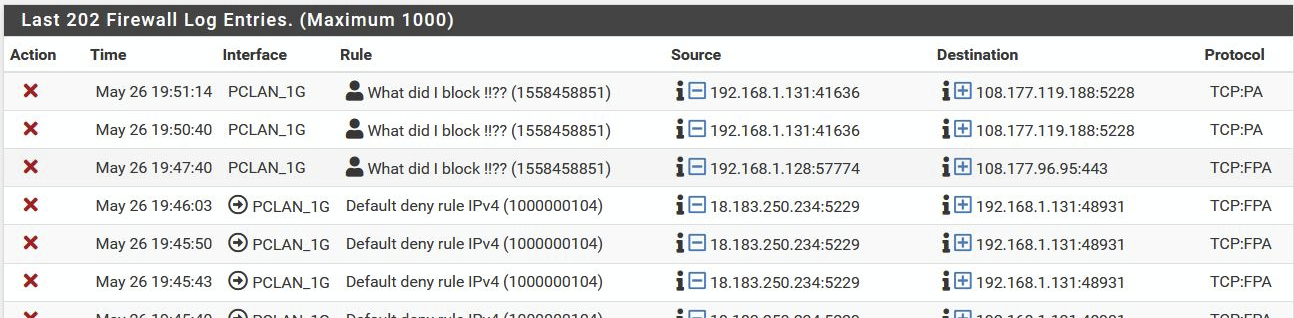
Switching off the TCP-ACK filter rule stops this "new" FW behavoir, we are back to the same situation as before.
So this TCP-ACK filter, has unexpected and unwanted side effects .......
-
I suggest that all of those are because the IP you're testing from hit locked out of the firewall dues to excessive login attempts and the it's existing states were cleared. That applies before the user rules so it still hit and logged.
The arrow there shows it was blocked outbound on PCLAN_1G whicb is almost always out-of-state traffic because the state was closed.
The extra rule you have added does nothing more than block some traffic without logging before it hits your block everything rule anyway.
Steve