Management lockdown ?
-
Hi Saw a video from David McKone "How To Install And Configure pfSense Firewall Pt2" on youtube.
Have a question about the methodology, and maybe a few more after. Please help.
When locking down the management interface he uses the following rule set.
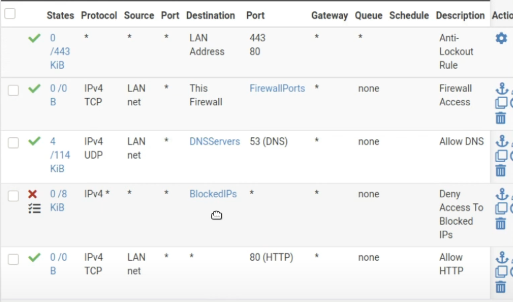
The first Block "Deny Access to Blocked IPs" is where he blocks only 192,172,10 RFC networks not all possible private IPS. He says it is necessary ahead of the internet rules below.
I do not understand this at all, especially since there is an implicit deny all at the end. Is this because a connection out the internet can point back into a local IP part of a private network ?
My Question:
Want to do two things- Dedicate on port on my NIC to management only where I physically have to plug a computer into it to access the web interface and that is the only way to access the web configurator.
- I want to have another port on my NIC for financial use cases that cannot access anything internally, but can just go out to the internet.
The rules for in/ out port firewall and wan/lan are very confusing for me to come up with a solid rule set to accomplish this (or a guide that has something similar) ?
How do I get 1 and 2 done?
-
@srytryagn said in Management lockdown ?:
When locking down the management interface
Locking down management interface for what - why would you use the management interface for anything than access to the web interface - which is open with the antilock out rule.
So this is your admin/management network - why would you block access to your other networks? Just at a loss there - I could see preventing your IOT vlan from talking to your other networks, etc..
The antilock out rule already does exactly what his 2nd rule is doing.
His rules there on the bottom - that is exactly what it does out of the box anyway, logging the defaut deny..
Seems like yet another - don't have a clue, let me make up a guide for users that have less of a clue than I do sort of guides.
Your questions are easy enough to do.
-
If you don't want your other vlans/networks to access pfsense webgui - then block them, use the "this firewall" alias.
-
Ok then do that - simple create an alias with all of rfc1918 space, put it your rule listing.
I really don't get your desire to make your life harder with 2.. So you think financial sites are going to hijack your machine? And then infect the rest of your devices?
-
-
Not sure why he did it exactly like that to lock it down.
He also created external DNS + DHCP servers.Here is the architecture:
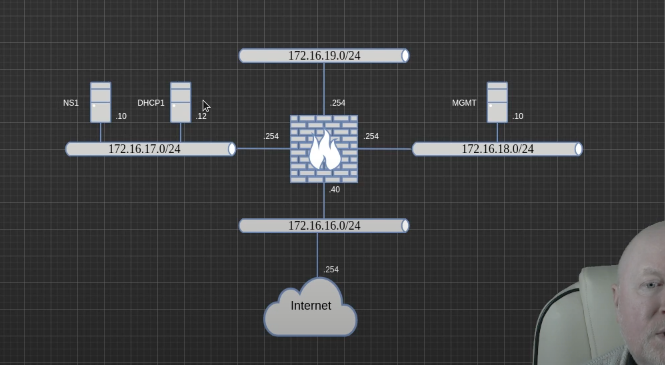
And here is the video link : https://www.youtube.com/watch?v=HCIkg3nbPvM
-
@johnpoz
Strange thing is that with this setup I cannot get out to the internet.Looks like it has everything enabled to be able to hit the internet ports protocols..what am I missing ?
Why is cant it connect to websites?
-
@srytryagn No desire to waste my time watching such a video..
As to why you can not get to the internet - your rules don't even show any hits, see the 0/0 s From that nothing has hit pfsense in such a way that the rules were even evaluated..
-
@srytryagn LOL on time waste, only noobs like me spend time watching things like this.
The screenshots are from his video, as he is setting it up, from not my screen. Still have no idea why it provides no internet connectivity...
I suppose the question is: If you and an implicit deny all; what are the minimum amount of specific ports/protos that need to be allowed to connect ?
-
@srytryagn You seem to allow dns - where your allowing that too, have no idea.. But there seem sot atleast be some traffic there.
Internet is normally 443, sure some 80 traffic. But again your rules are 0/0 - that means nothing ever asked pfsense to go to those ports. Maybe you have a floating rule blocking traffic, maybe your clients are not even talking to pfsense? Maybe dns is not working? Have idea where you pointed it to dns.. Is it your alias for allowed dns? Dns doesn't work - internet not going to work..
Before I worry about locking down anything, I would just get basics working.. The default lan rule is any any, and clients point to pfsense for dns, and unbound resolves.
Is that working? If so then you can lock down your rule as you see fit..
Following some guide without a clue to what any of it means anyway, and just pointing and clicking trying to duplicate some settings pretty always going to lead to issues.
-
This post is deleted! -
@srytryagn Show what the Alias "DNSServers" is on your system.
-
@jarhead Head an error, list of all private IPs blocked was set to * not to my alias.
Reaching internet now.