Searching for the fastest way to isolate each VLANs using pfSense firewall rules
-
Dear Users,
I'm a newbie and I'm trying to learn and understand the best practices about the pfSense firewall rules usage.
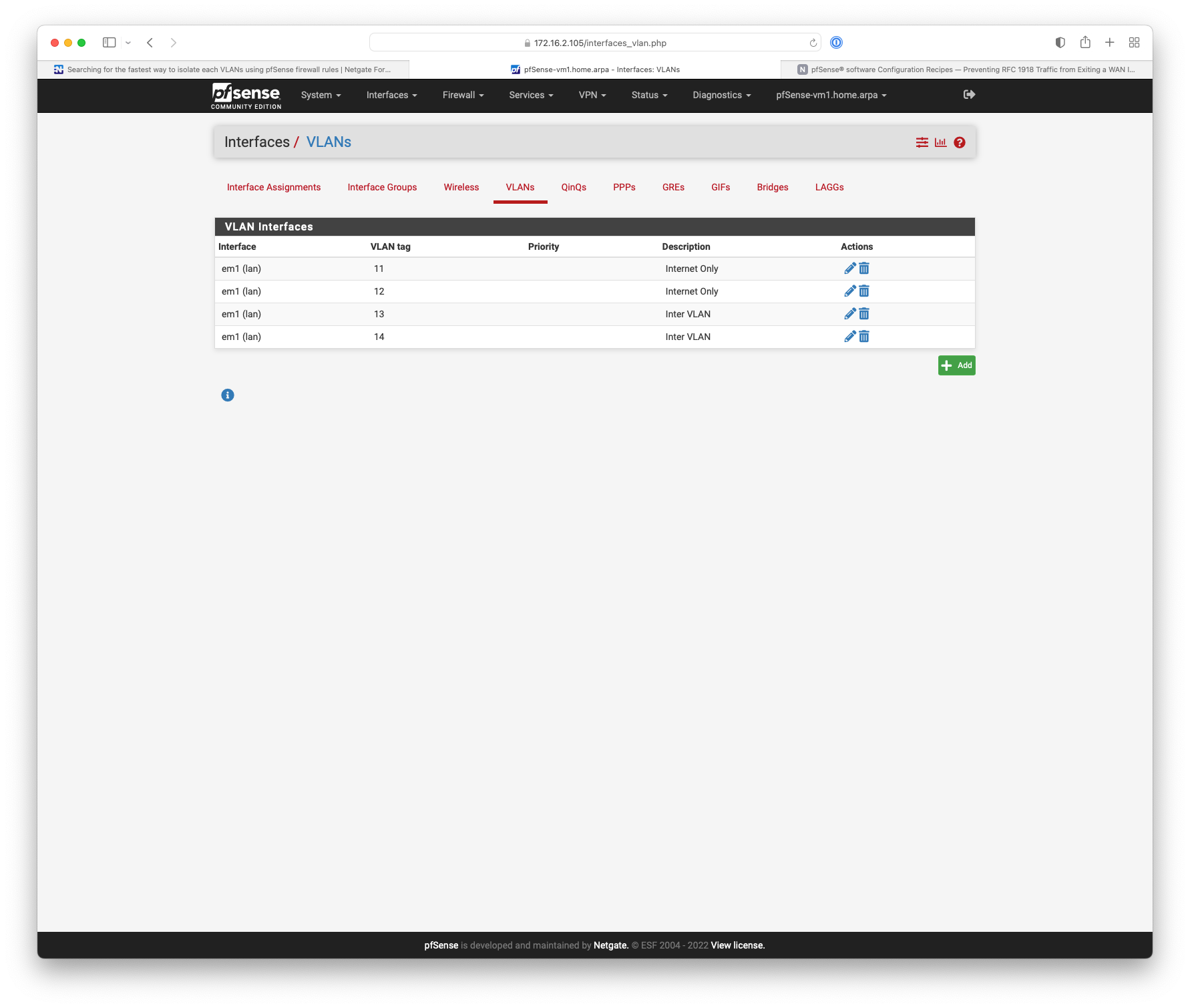
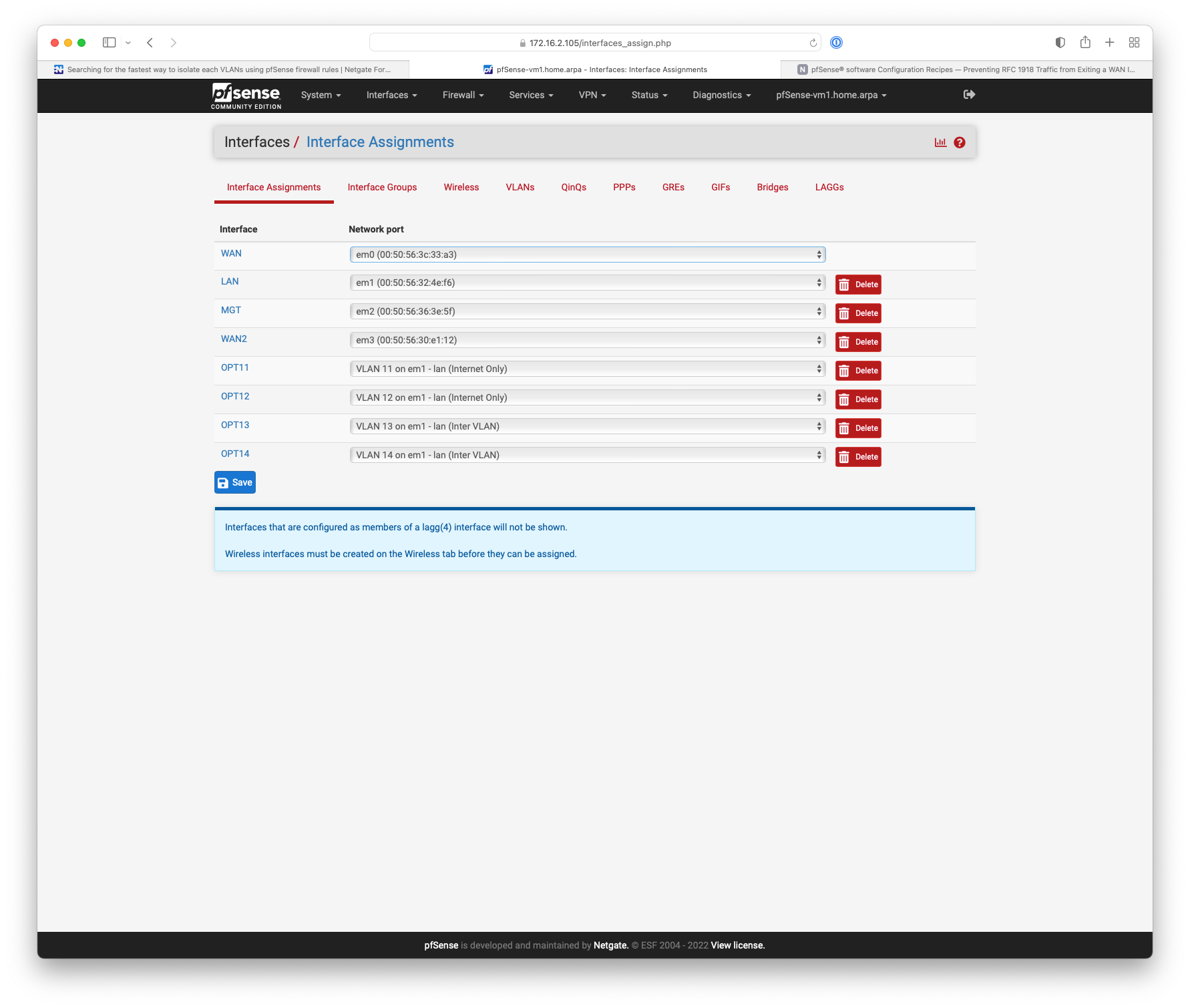
I created a lot of VLANs on the same pfSense instance.Let's say, for example, that the following VLANs have been created:
OPT1
OPT2
OPT3
OPT4
OPT5
OPT6
OPT7
OPT8
OPT9
OPT10So, at the moment, since no particular rules have been defined, each VLANs hosts can reach each other.
Now, I would like to activate some firewall rules in order to have the following scenario:
OPT1 is isolated from other VLANs
OPT2 is isolated from other VLANs
OPT3 is isolated from other VLANs
OPT4 is isolated from other VLANs
OPT5 is isolated from other VLANs
OPT6 is isolated from other VLANs
OPT7 is isolated from other VLANs
OPT8 is isolated from other VLANsOPT9 and OPT10 can reach every VLANs hosts.
So, my very basic idea is to activate, on each interface, the following rules:
on interface OPT1, block, source: OPT1 network, destination: OPT2 network
on interface OPT1, block, source: OPT1 network, destination: OPT3 network
on interface OPT1, block, source: OPT1 network, destination: OPT4 network
on interface OPT1, block, source: OPT1 network, destination: OPT5 network
on interface OPT1, block, source: OPT1 network, destination: OPT6 network
on interface OPT1, block, source: OPT1 network, destination: OPT7 network
on interface OPT1, block, source: OPT1 network, destination: OPT8 networkon interface OPT2, block, source: OPT2 network, destination: OPT1 network
on interface OPT2, block, source: OPT2 network, destination: OPT3 network
on interface OPT2, block, source: OPT2 network, destination: OPT4 network
on interface OPT2, block, source: OPT2 network, destination: OPT5 network
on interface OPT2, block, source: OPT2 network, destination: OPT6 network
on interface OPT2, block, source: OPT2 network, destination: OPT7 network
on interface OPT2, block, source: OPT2 network, destination: OPT8 networkand so on...
Unfortunately, I should apply almost the same rules to each interface and it seems to be a very annoying work.
Is there a way to simplify this process?Thank you in advance,
Mauro -
@mauro-tridici just create an alias containing all your vlan-subnets. Block them all with a single rule.
If you need access to the pfsense device don't forget to add a rule on TOP to allow such access.
-
@mauro-tridici said in Searching for the fastest way to isolate each VLANs using pfSense firewall rules:
So, at the moment, since no particular rules have been defined, each VLANs hosts can reach each other.
Are you saying each host can access other hosts on the same vlan or other vlans?
With no rules applied all should be blocked except for the LAN interface. -
@heper many thanks, it is a very simple solution.
I appreciated it.
Do you know if we can also create a group of rules and "copy & paste" them on each interface? (maybe it's a too fanciful idea).Thanks,
Mauro -
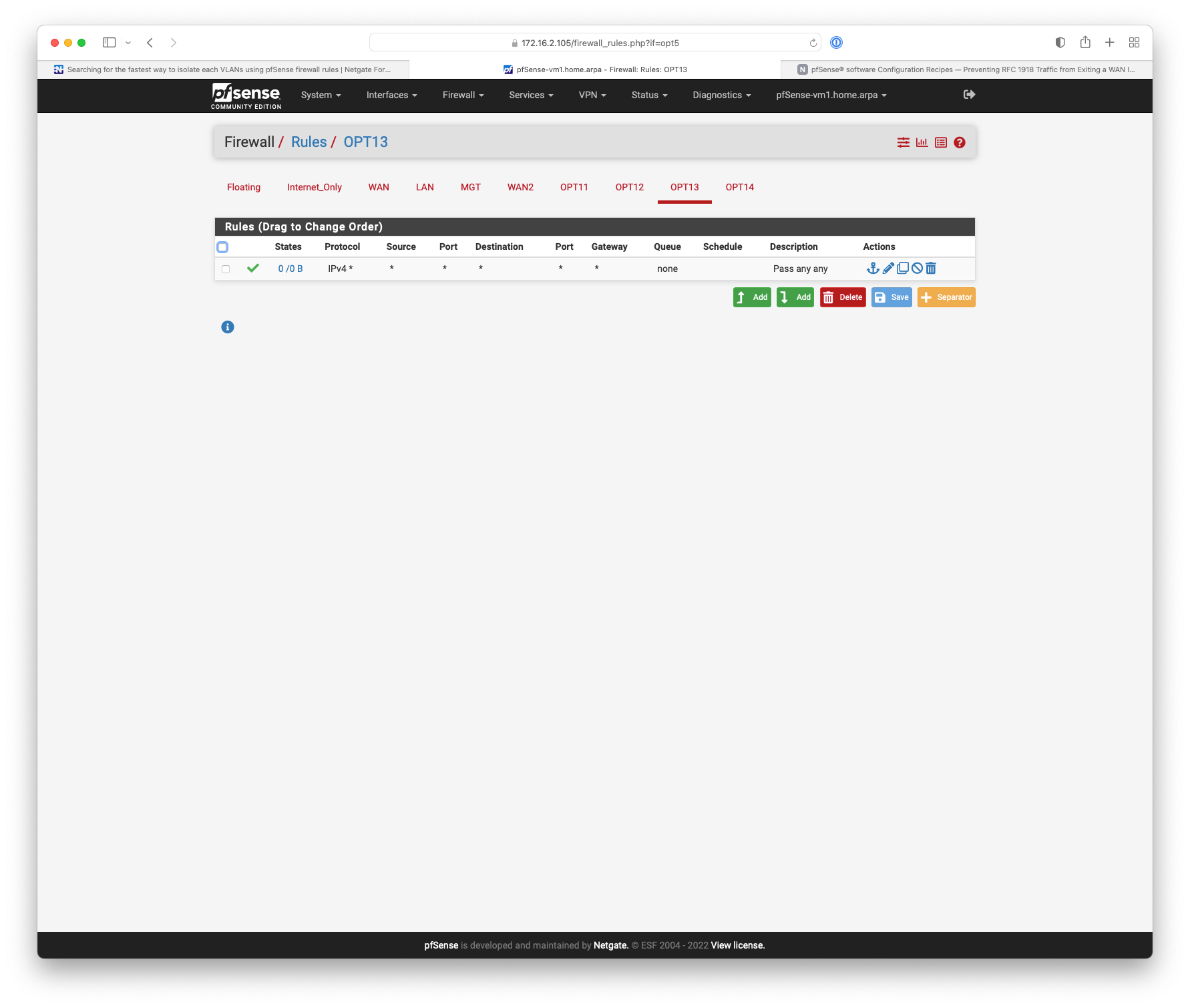
@jarhead, in our case, each interface has a "accept any/any" very basic rule, just to test connectivity.
But, now, we are going to define the final firewall rules. Or, at least, we are thinking about them. -
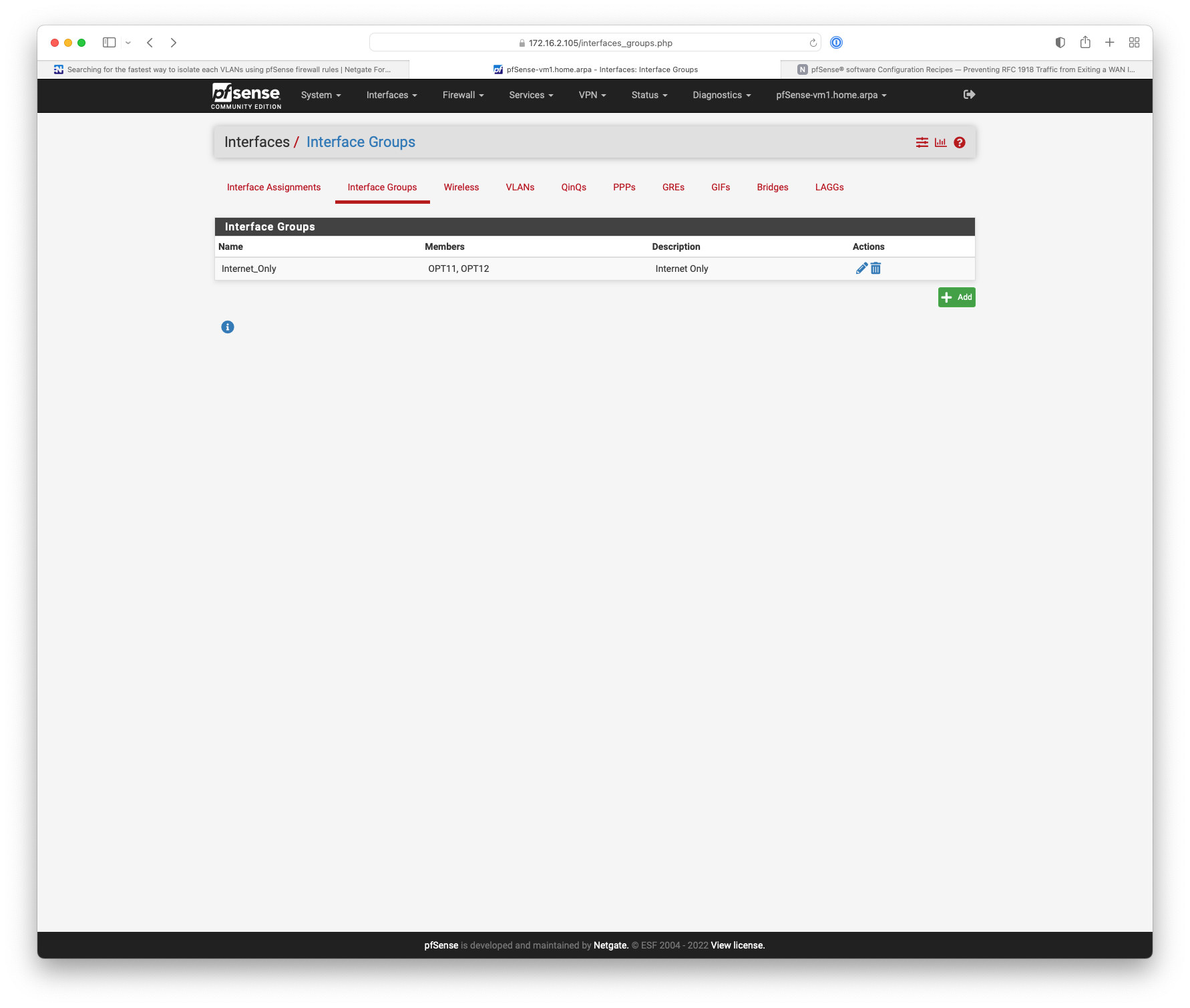
@mauro-tridici You could also use interface groups.
https://docs.netgate.com/pfsense/en/latest/interfaces/groups.html
The rule processing order for user rules is:-
Floating rules
Interface group rules
Rules on the interface directly -
@mauro-tridici said in Searching for the fastest way to isolate each VLANs using pfSense firewall rules:
@jarhead, in our case, each interface has a "accept any/any" very basic rule, just to test connectivity.
But, now, we are going to define the final firewall rules. Or, at least, we are thinking about them.Gotcha, thought you had no rules yet.
So there's a button on the rules themselves, all the way to the right, that will copy the rule. Third icon.
Click that, then change the interface it's on to copy to different interfaces. -
If you remove the any to any, you have the default block behavior.
Then all you need to do is on all OPTs except for 9&10 is allow in from OPT9|10. I think an interface group of OPT1-8 and an interface group rule would do that.
Traffic out of OPT9 to OPT1 should wind up creating a state so the traffic back from OPT1 to OPT9 should be allowed back in.
OPT9 and OPT10 you could either put interface rules or just add them to the interface group.Basically what @NogBadTheBad is saying.
Simple rules are always easier to debug
-
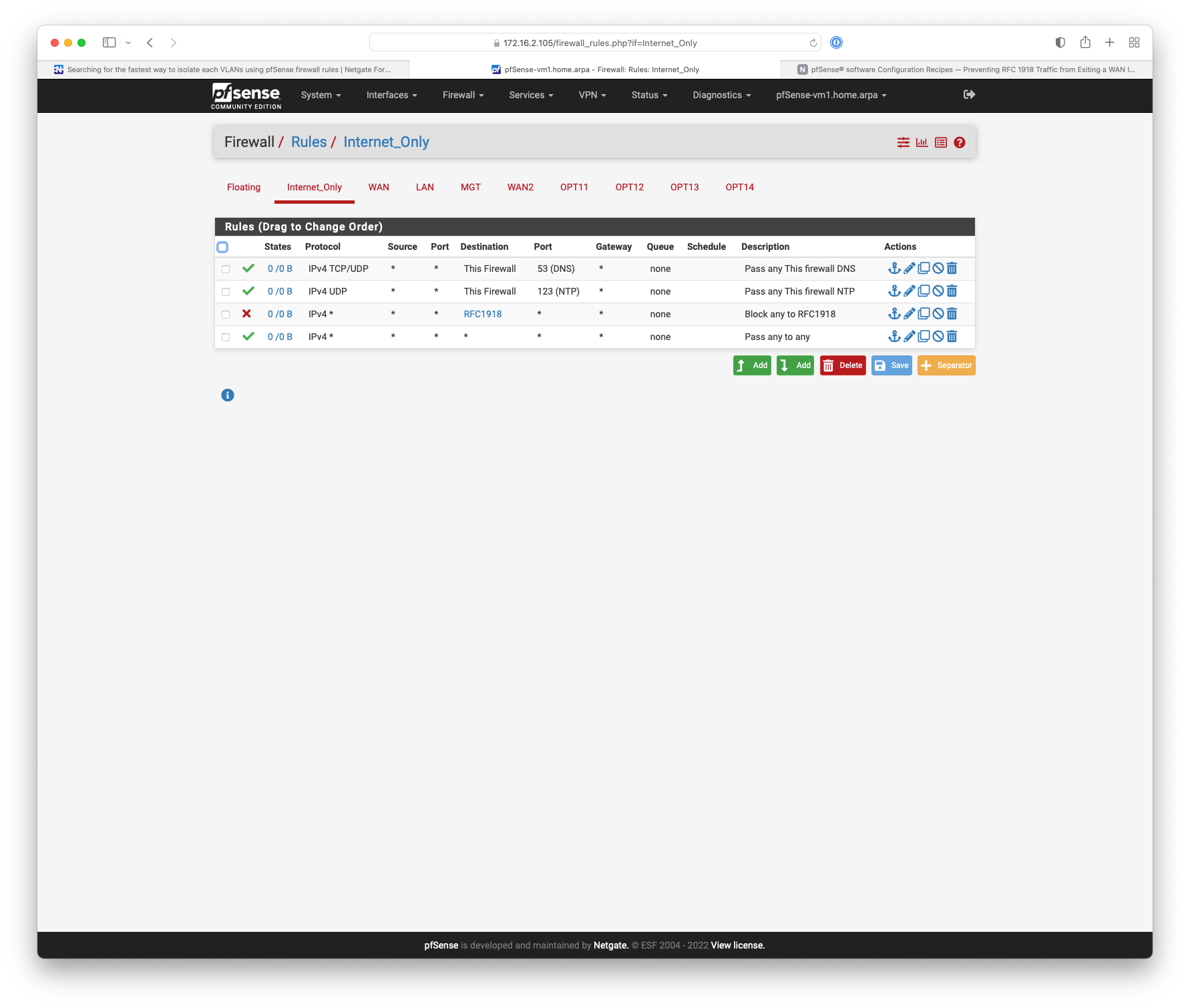
Something like this.
-
@nogbadthebad many thanks for your help. Appreciated.
-
@mauro-tridici No worries your welcome, I do however think you trying to simplify things may make it a bit harder for you in the long run

-
@nogbadthebad said in Searching for the fastest way to isolate each VLANs using pfSense firewall rules:
may make it a bit harder for you in the long run
I concur with this sentiment, vs looking for some shortcut on how few rules you can create to allow or block whatever you would be better off putting very explicit rules on each interface tab.
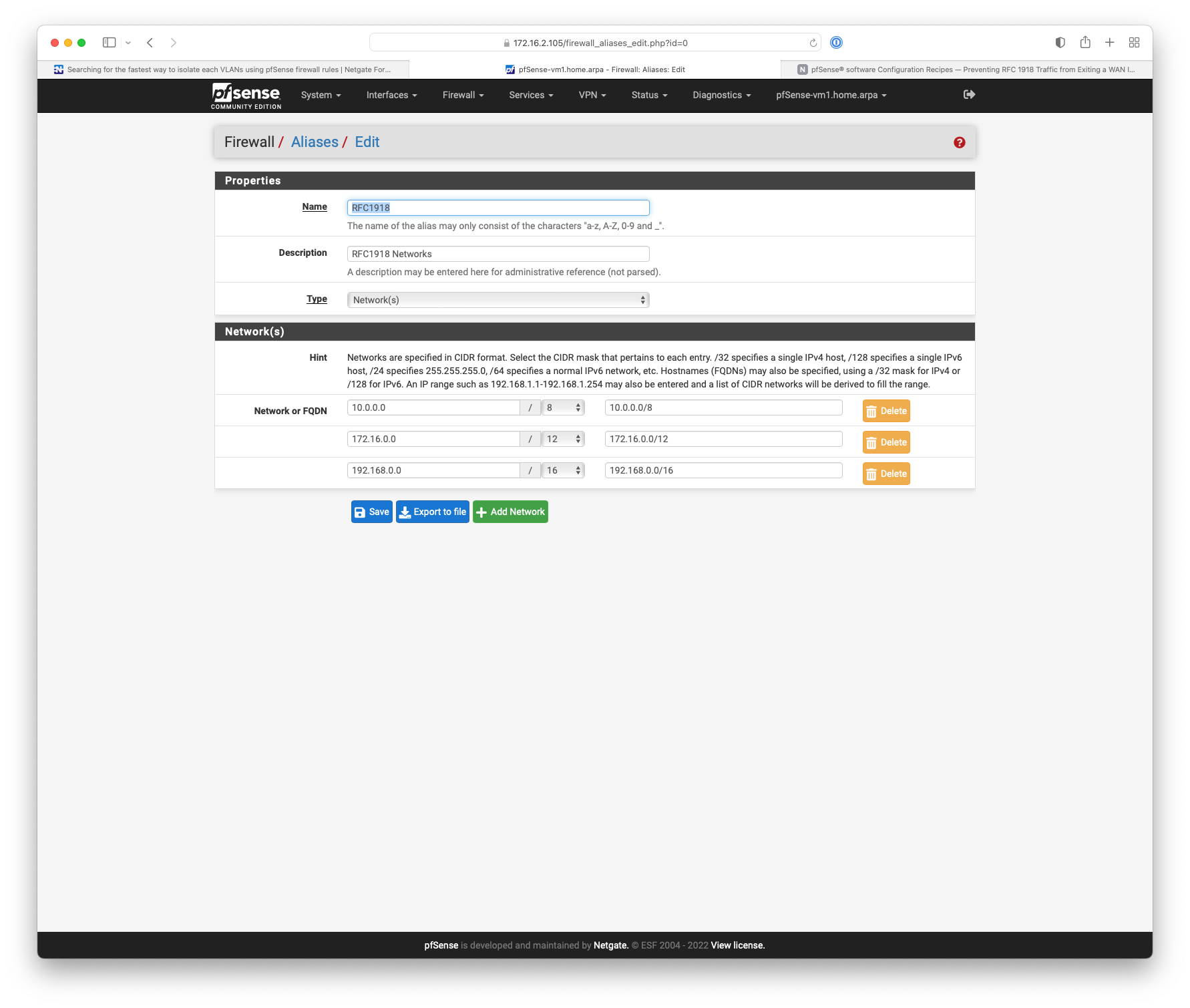
If your looking for simple way to block access to other vlans, assume all your vlans are rfc1918 is just create an alias that has all rfc1918 space. And use that alias on a rule on each interface to block access to your other vlans.