Gre tunnel to protect IP.
-
@stephenw10
Can you tell me where I can disable NAT?
For GRE tunnel only. I have the ip 192.168.1.2 with NAT for port 8006 going out through my WAN since it doesn't need protection that ip.
Thanks -
I've already disabled NAT only in the tunnel on the pfsense client and it's already here without NAT. Now it will just be creating a static route right?
-
Ok, so you need to add an Outbound NAT rule on that side for 192.168.1.0/24 on WAN.
If you have added a static route back to the main side I would expect the auto outbound rules to cover that so I assume there is not.
Steve
-
I have now bought a new ip since I don't want to use the router's ip on the machines
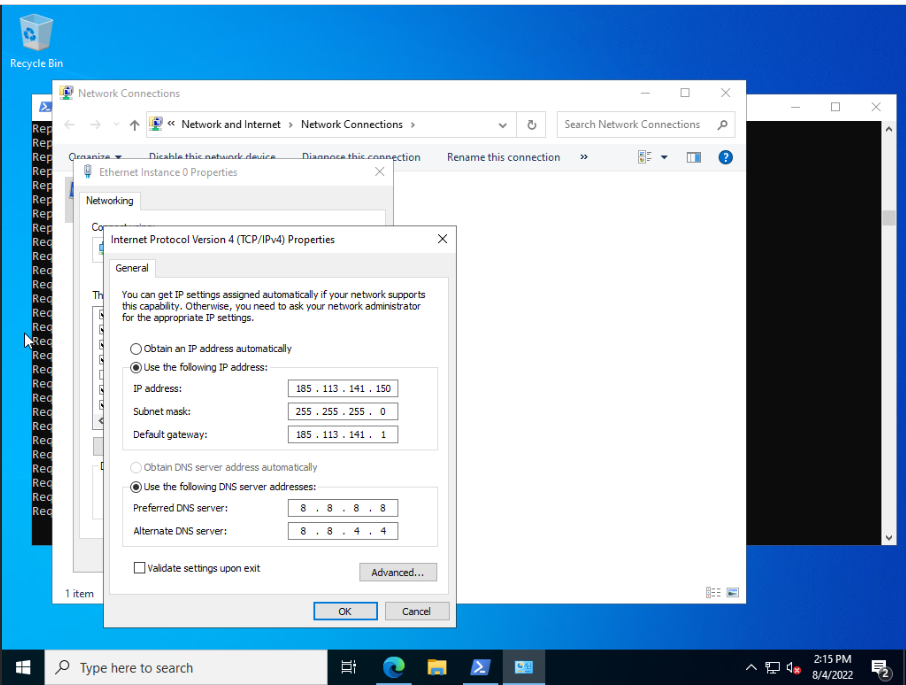
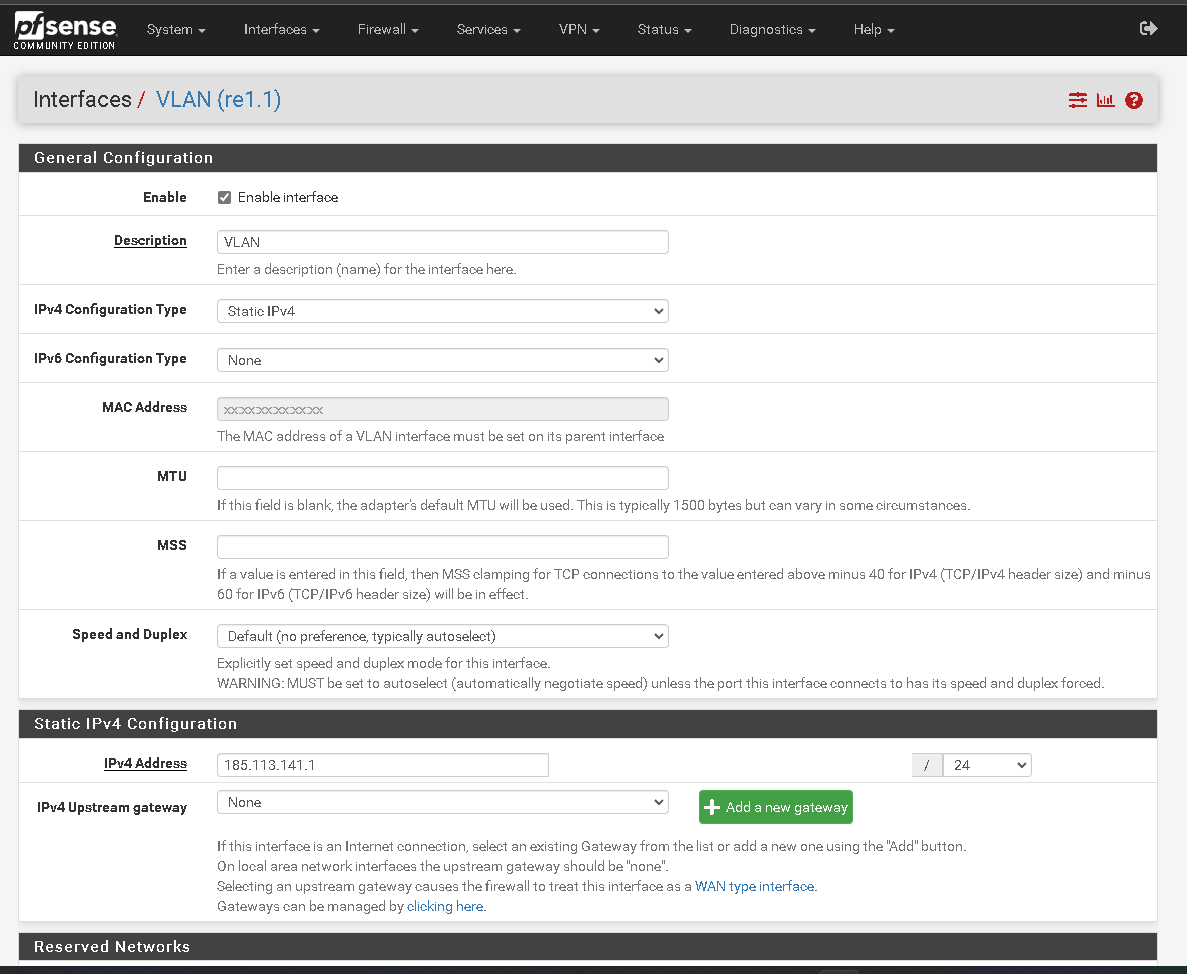
I configured it on the windows machine like this and created a VLAN on the pfsense client.
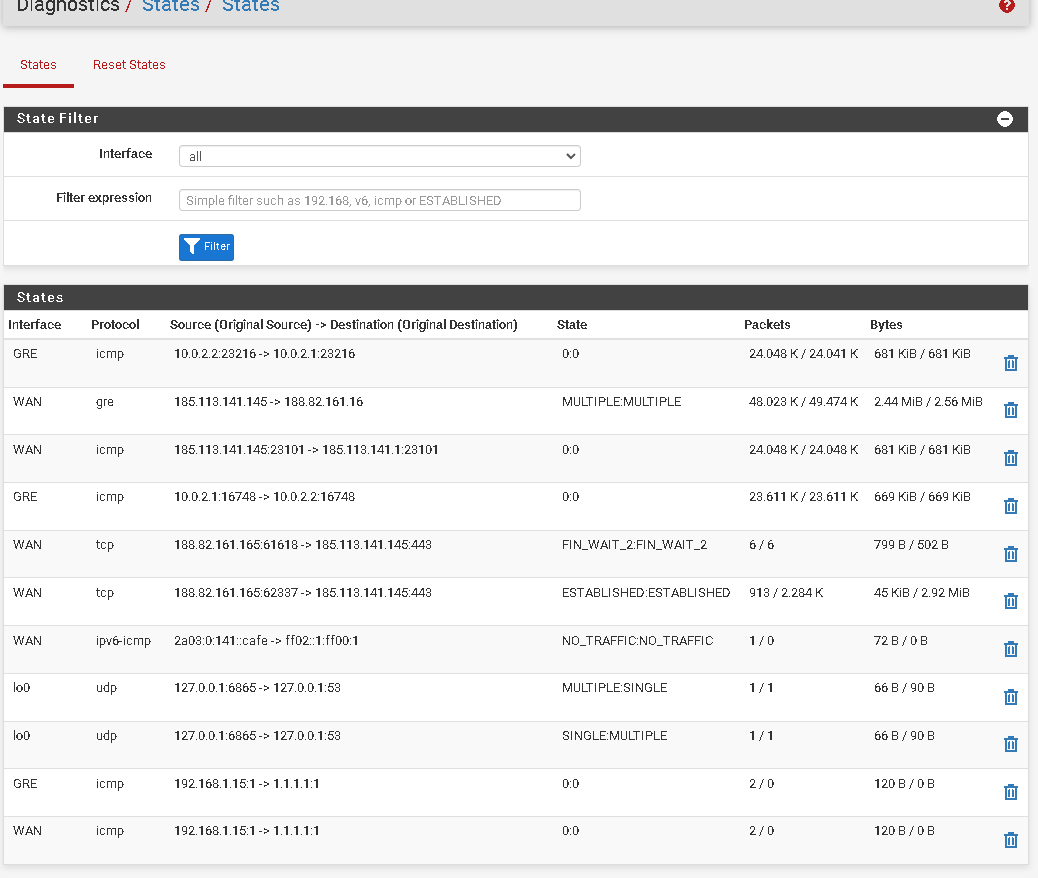
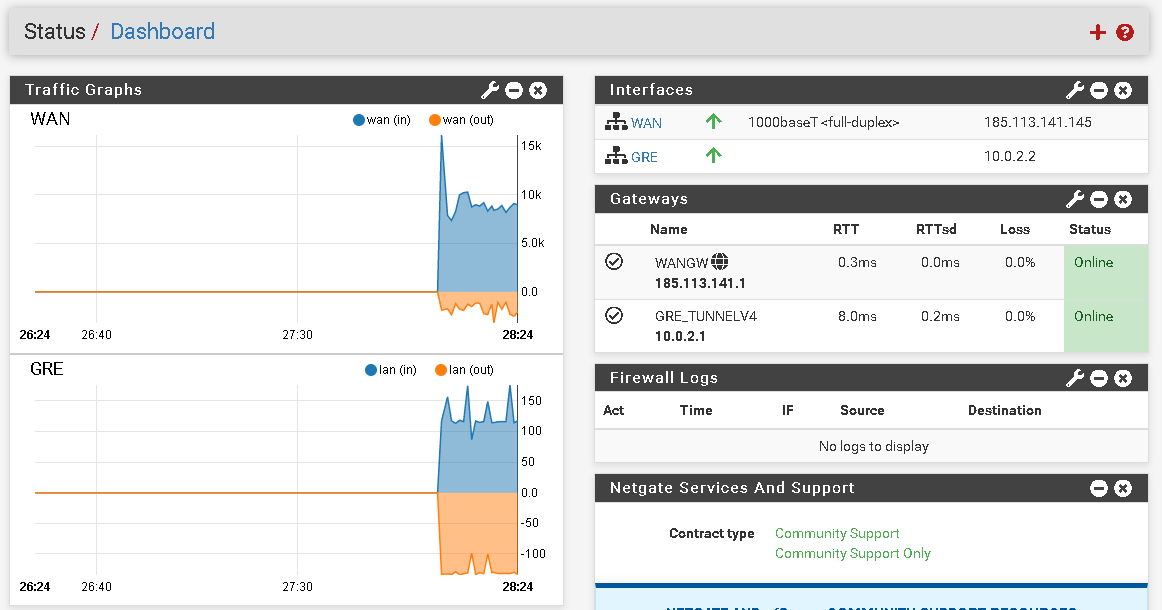
I'm constantly pinging from the windows machine to 1.1.1.1 and in the pfsense host states it is received like this

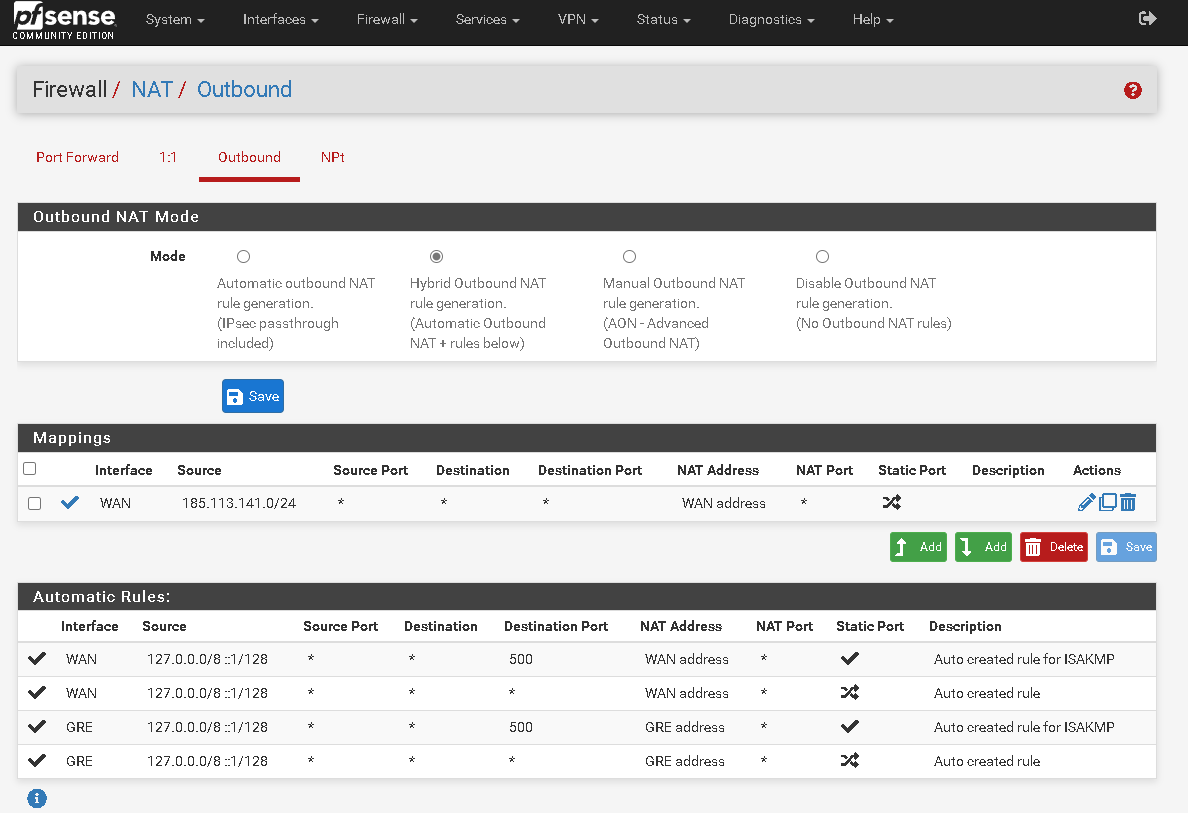
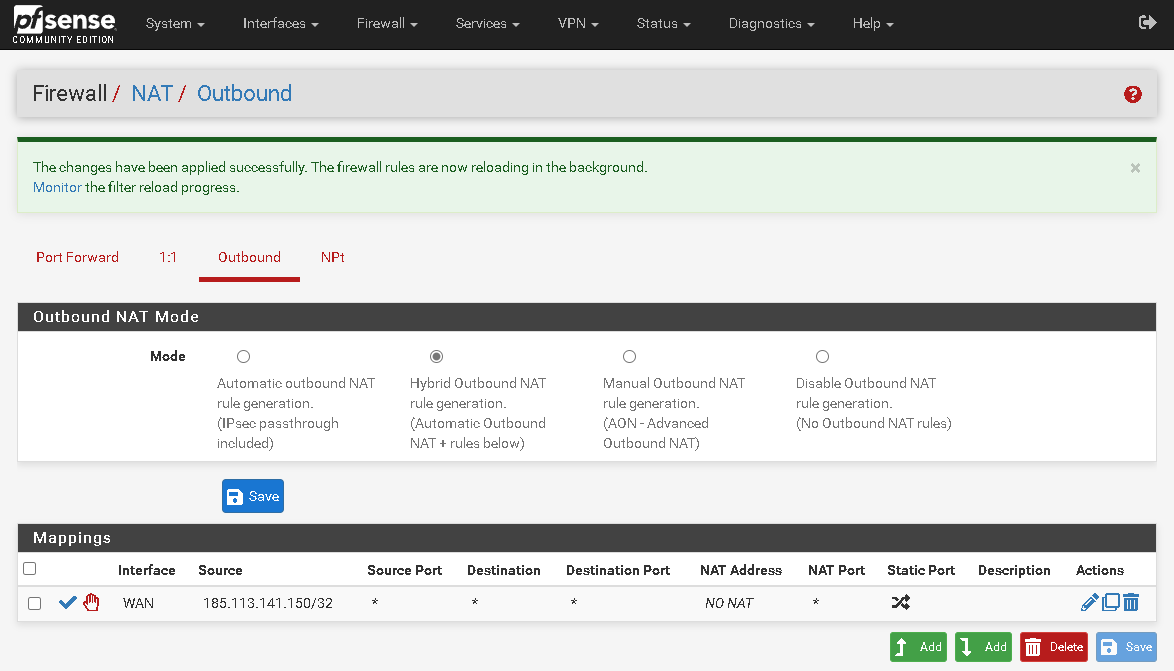
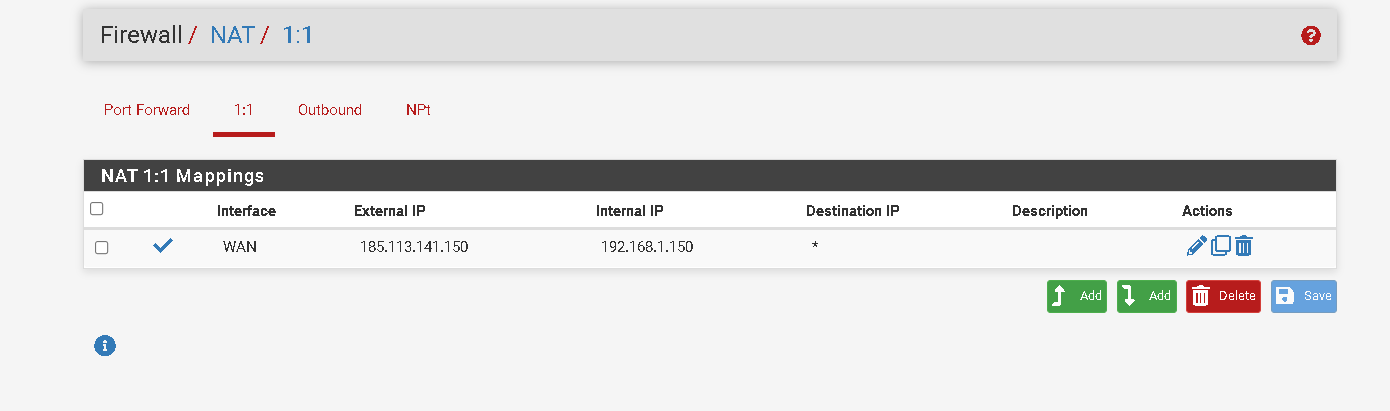
In the NAT part of the pfsense host I configured it like this ie the ip 185.113.141.145 is the ip wan of the pfsense host and I don't want to use it for anything else. And the ip 185.113.141.150 I want to be used in my virtual machine.
The only problem is that the machine is without internet for the ip 185.113.141.150
-
You can't use that IP directly on the client because that conflicts with the WAN subnet at the remote site.
Instead you need to add that as a VIP on the WAN at the remote site and then NAT the traffic to it.Steve
-
I already added the virtual ip.
To do the nat routing is as follows?
-
Which end is that rule on?
I expect to see the client using 192.168.1.15 and then that traffic to pass without NAT at the local pfSense. Then at the remote pfSense that IP should be NAT'd to the WAN IP or the VIP.
-
I liked to use the ip 185.113.141.150 on the windows machine is this not possible?
This rule was in remote pfsense. -
You can't use the public IP on the Windows machine directly unless it is bridged (layer 2) to the remote WAN somehow. You can't use a routed tunnel like you are now.
-
What other possibilities can I use?
-
@stephenw10 said in Gre tunnel to protect IP.:
I expect to see the client using 192.168.1.15 and then that traffic to pass without NAT at the local pfSense. Then at the remote pfSense that IP should be NAT'd to the WAN IP or the VIP.
Like I said ^.
-
Yes, I'm already doing that. Now I use NAT 1:1 or Outbound?
-
Is it working? Does the expected external IP show in test site?
-
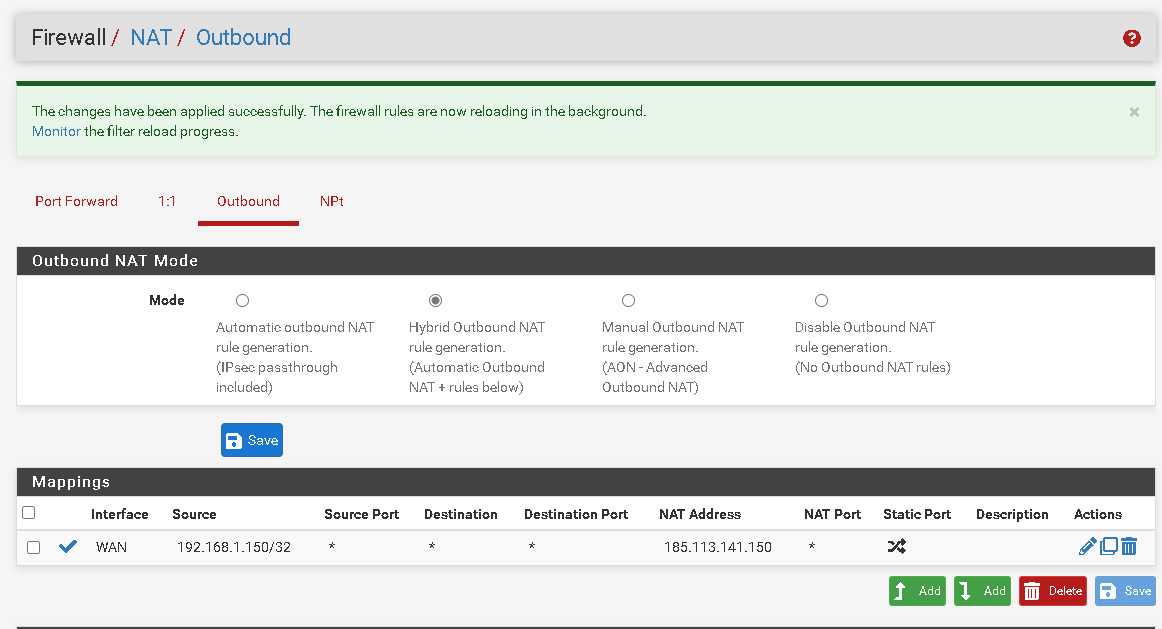
I created the rule like this and it worked.
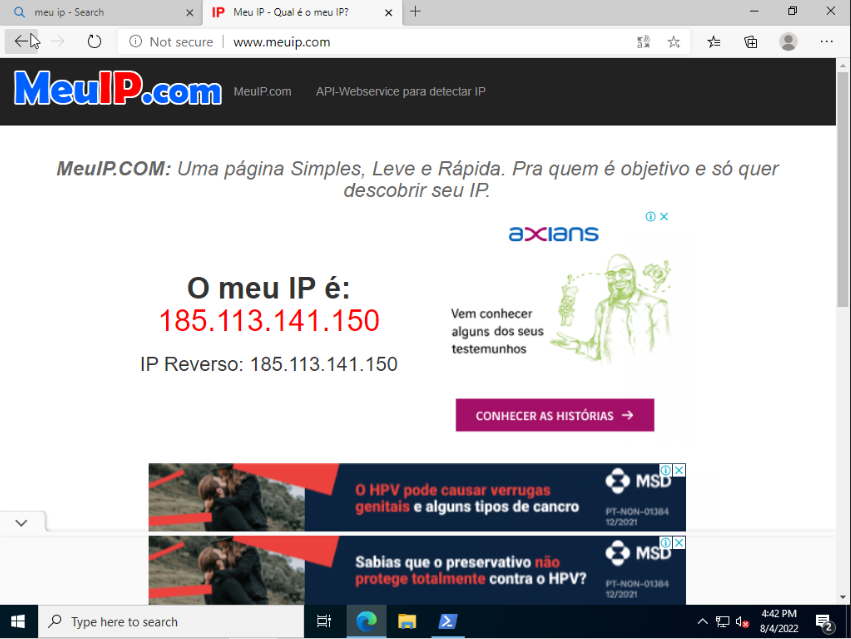
The only problem now is the ports are not working.
And they are open on the firewall. -
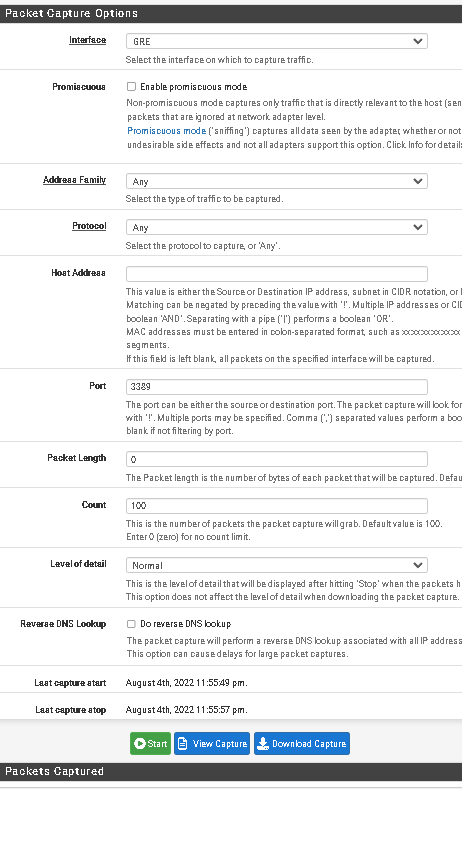
On remote host i recive the packets on wan interface.
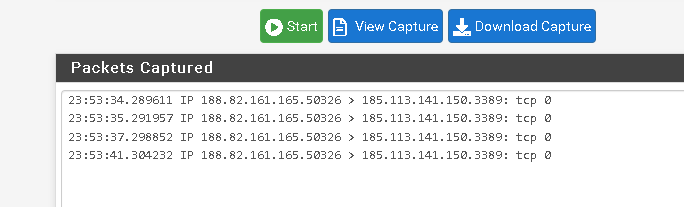
If i change for the gre interface the packets not are sended
-
Ah, you need traffic to work inbound as well?
You captured that on the GRE interface? That's surprising if so. I might expect to see that on the WAN...
Anyway if you need inbound and outbound traffic then I would use a 1:1 NAT rule at the remote side instead of the outbound NAT rule.
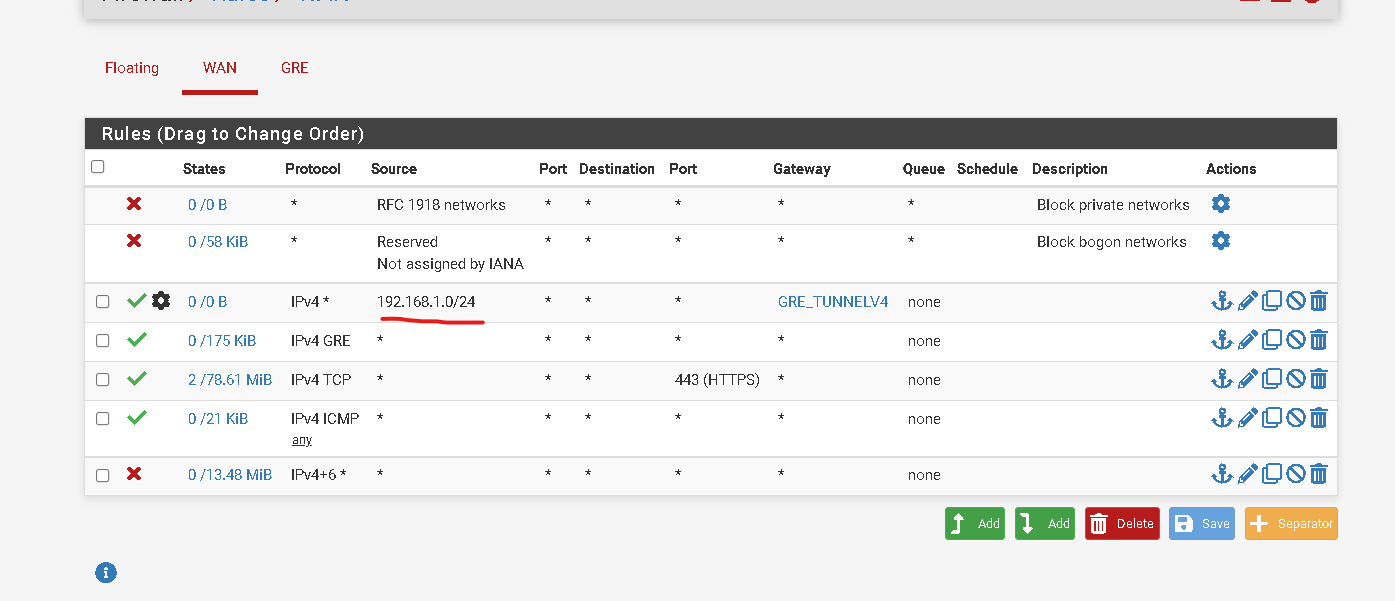
You will also need firewall rules on the WAN there to pass whatever traffic you need.
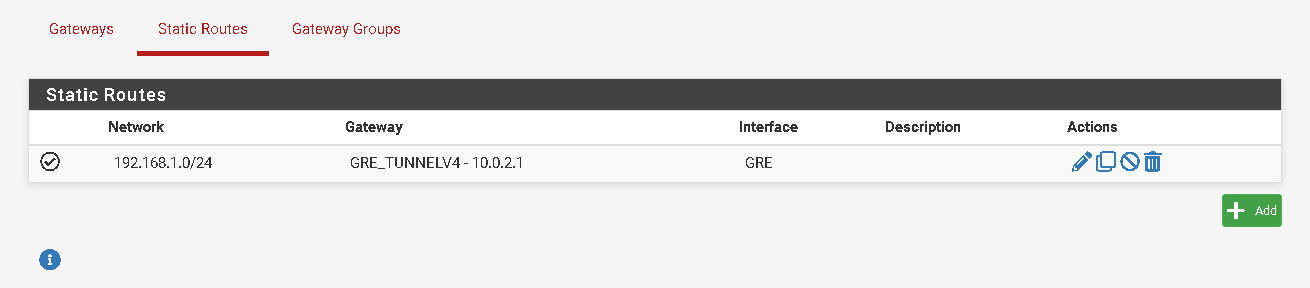
And you will need a static route to 192.168.1.0/24 via the GRE gateway so it knows where to send traffic.Steve
-
Yes I want to open ports on the machine and they are available for that ip.
I did this on the remote host but it still doesn't work. In packet capture I analyze the gree interface (remote host) and nothing gets there.
Is there a better way to do what I'm trying to do?
Thanks for the help
-
The WAN rule there needs to be:
Source: any
Destination: 192.168.1.150
Destination port: 3389 (or an alias of whatever ports you want to allow)Steve
-
It worked, thanks a lot for the help.
Is there any better way to do this? It will be for VPS use.
What I would really like to do is add the public IP directly to the VPS.
Thanks again for the help, I really appreciate it. -
To use a public IP directly you would need to have a small subnet that is routed to you that you can then use internally.
Either that or bridge the connections so it appears as one layer 2. You might be able to do that with OpenVPN in TAP mode instead of GRE but I would not recommend it.Steve