Unifi Network Controller & Pfsense
-
@stephenw10 I got it finally, I followed your suggestion on finding what changes with the VPN on.
Problem was Split Tunnel in the VPN app PIA. Works even if PIA app is not running.
If the VPN is not Online the programs on the Split Tunnel List can't talk to the internet. The Unifi Network was NOT one of the apps on the Split Tunnel list but I thought maybe its blocking ports that those apps on the list might share with Unifi Network, as Pfsense was ruled out.
So I turned off Split Tunnel completely & now the Unifi Network works perfectly without needing the VPN on.
-
Ah, good catch!
-
-
@dobby_ while some people are ok with doing that - I would suggest against doing such a thing. If you really want to run your unifi an pfsense on the same box - prob better to run them both as VM on some VM host.. I would not think it a good idea to introduce 3rd party packages into the pfsense OS.. Unless the 3rd party stuff has been given atleast an ok from the pfsense devs by allowing it into pfsense package system.
Now this is just a guess on my part, and my opinion could be biased towards my own setup. But I would "think" that most people that have the want/desire to run pfsense would also have something else they could run the controller on, a VM on a nas, a docker on some other box they have on their network, or some pi or some other box, etc. I would again just "guessing" here that people that have decided to run pfsense also have a few other toys in their toybox, so should have something other than their firewall to mess around with when running stuff like controller software for APs.. But maybe that is just me? ;)
-
Yup, I have to agree. It's impossible to recommend that. None of that is tested by us before release. Also... java.

-
@johnpoz said in Unifi Network Controller & Pfsense:
But maybe that is just me? ;)
+1
At the end of the month I'll have to fire up a VM to host that ynfi controller app, as I deploy my new AP's.
That is, if I really need that application, I'm not sure yet.
And if the VM isn't easy enough, I'll go for their box version. -
@gertjan I believe the unifi app is only required if your going to be doing something with vlans, or you want to run a captive portal sort of thing.There may be some other things not aware of - but those 2 come to mind.
if vlans - you can fire it up, set it an then turn it off - so that could be just run on your PC or laptop when you "need" to make a change.
I do like it running, just for insight on what is going on with all the wifi clients - what speeds are they connected at, what specific AP they are connected to (I have 3) 4 if you count flexHD that is on and off the network.
It doesn't require a lot of resources - it sits pretty much idle as a vm on my nas. To be honest I mostly use it to make sure clients are connected to the AP I want them to be connected to ;) After I do a rolling update of firmware - clients tend to have moved to a different AP, and don't always jump back to the one I think they should be on right away. So after a rolling update has completed I will look at all the clients, and for example some of my smart lights might be connected to the hallway AP vs the one in the kitchen where they are. Sending a simple reconnect for that client normally has them pop right up on the correct AP. Now if I let it sit long enough maybe they would move on their own at some point.
But the info it provides can be handy - and for sure is pretty eye candy ;)
-
@johnpoz hey there,
indeed, it is only needed for changing settings, setting up vlans, captive portal and such...
I handle it the same way: I got it running 24/7 anyways, cause it is nice to have that specific "extra" dashboard and possibilities.
And it does look quite nice :)I never bothered with vm or letting it run on a separate pc as many do, I went for the boxed version at once, lazy as I am. It does not need much power, runs well from day one and (knock on wood) did not break so far (around 3 years now).
Some of unifi's stuff is not really well implemented imho: using your own https/ssl certificate is rather complicated...moving away from default management vlan is a little tricky (it took some time to adopt my APs again).
As to the topic of this thread...no, I do not need it integrated in pfsense (not to say, it does not feel good to imagine that).
It is imho the same as with modern NAS...people tend to activate every single service just because it is possible...well. It is a storage after all, not a full server, but that's jm2c
:) -
@the-other said in Unifi Network Controller & Pfsense:
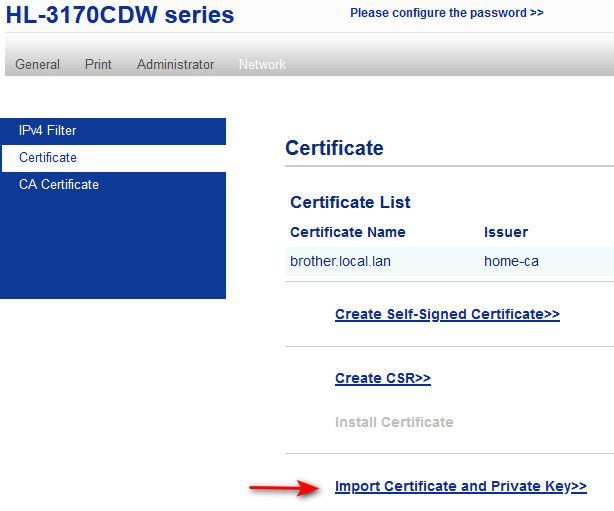
using your own https/ssl certificate is rather complicated
They for sure could make that easier - its sad really why they have not just added such a basic thing to the gui..
Setting up my printer to use a specific cert it easier than with the unifi controller..
-
@johnpoz
I actually gave up along the way and set an exception to my browser...lazy me.
:D -
@the-other its not all that hard, here I saved these instructions. But it is PITA
delete the old keystore and restart unifi to create an empty keystore: rm /var/lib/unifi/keystore service unifi restart openssl pkcs12 -export -in server.domain.net.cert.pem -inkey server.domain.net.key.pem -certfile ca.cert.pem -out unifi.p12 -name unifi -password pass:aircontrolenterprise keytool -importkeystore -srckeystore unifi.p12 -srcstoretype PKCS12 -srcstorepass aircontrolenterprise -destkeystore /usr/lib/unifi/data/keystore -storepass aircontrolenterprise service unifi restartJust use a ca in pfsense, and then download your cert and key file from your cert - but you have to join them all together with openssl, lets hope by next time I need to do this june of 2023 they have made it easier ;) but I doubt it.
-
@johnpoz
Wow, thank you.
:)
I do all my certs with good old cert manager and pfsense. Before I used openssl under ubuntu indeed, which is okay after some learning. Went well for all kinds of devices (switches, raspberries...well everything here using https). With cert manager it's even fun, well, kinda...just the darned unifi stuff!What I missed was to delete the default keystore...tried to put my own cert there, did not work, if I remember correctly...
Anyway, thanx for a new project for the time when the leaves are falling...
-
@the-other no problem, last time I didn't save instructions - and it was another PITA finding the instructions again, so this time I saved them off.
Now on the other hand, printer is just a gui you import the cert/key and ca with, etc.
But its only doing tls 1.0 so browser doesn't like that either and still warns that "not secure" ;)
Now if some crappy printer interface can have a gui for importing your cert, why can not the unifi controller do it..
Don't get me started on their behind the times busybox on their AP, and the antiquated sshd (dropbear v2020.81) on them. An update to securecrt broke access to them because securecrt had dropped support for old host keys.. And have to use a different library, that took a while to get sorted - but support from securecrt was great..
-
@johnpoz said in Unifi Network Controller & Pfsense:, so this time I saved them off.
I hear you...
... done and bookmarked :)Sorry btw for hijacking this thread @all
-
@the-other while true not actually pfsense related ;) lots of unifi users around here, hope someone else will find the info useful other than just you - hehe
-
@johnpoz said in Unifi Network Controller & Pfsense:
hope someone else will find the info useful other than just you - hehe
I am pretty sure a lot of ppl will...haha, true.
-
@tux4000 While your issue is solved, just wanted to add for those searching in the future that on all my customer sites, all unifi devices report to a digital ocean linux 'box' running the controller software. I have pfSense FWs and pfSense+ on netgate appliances, a varied mix. No tweaking of any kind ever needed on the firewall, as all traffic is outbound (from firewall's perspective).
The only exception was human error before I put the controller on DO when controller and device were on separate VLANs (w/out rules). After that, I no longer used local controllers.