reaching firewall itself via ipv6
-
@ddbnj said in reaching firewall itself via ipv6:
I just broke my dynamic DNS trying to point to the ipv6 address of the LAN
With many ISPs the IPv6 prefix is pretty much static, do you may not need dynamic DNS. Mine has survived replacing, at different times, both my modem and the computer I run pfSense on. I use a regular DNS server, for devices I want to be reachable from outside. As far as the outside world is concerned, there is no difference between your LAN interface and any other device on your LAN. They are all equally reachable, subject to firewall rules.
-
@ddbnj Depends on what they delegate to you. If it's a /56, take a /64 out of it and dedicate it to VIPs on the localhost interface. Then just tell OpenVPN to bind to that and pass the traffic to it into WAN.
-
Why assign a prefix to local host, when using the LAN address works?
-
Thank you for introducing me to some more tools.
Verizon provides a /56.
Never had the need to use VIPs before so that's something I'll have to read about tomorrow.
Can you bind any app to any VIP? Do I have to assign the VIP to an interface before I can bind openvpn to it? I don't think wireguard has a way to bind it to a specific interface. Too bad because that's the main site to site tunnel. Openvpn is a backup.
Take care,
Devan
-
@ddbnj said in reaching firewall itself via ipv6:
Since my ISP does not provide my WAN an IPv6 address,
Is that really the case? Do you have IPv6 working on LAN and don't have an address on WAN? Show it please, you have been wrong before.
-
I don't think you need to use a VIP for this. Just point the VPN server to your LAN interface. Any valid address on pfSense will work. In another thread, someone else mentioned my method worked for him.
-
@jknott Why not?
Nobody is saying your method will not work, but why not put services bound to addresses on the firewall in their own IPv6 interface "domain" disconnected from services off the firewall? One day you might want to, say, filter them differently. Maybe move that localhost /64 to another node.
So, Why not?
-
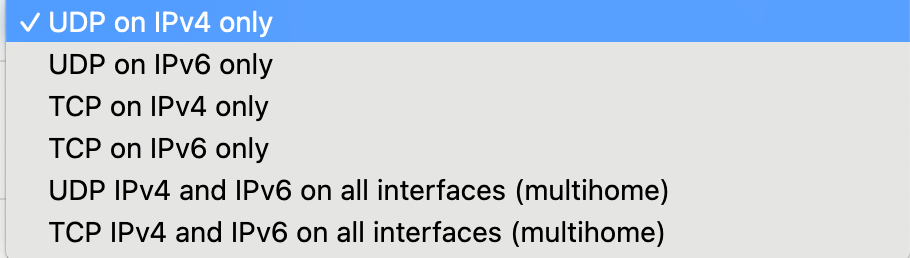
@ddbnj Well, with OpenVPN you have three choices:
Bind to a specific IPv4 interface address or IPv4 VIP
Bind to a specific IPv6 interface or IPv6 VIP
Bind to any address on the firewall.*The third method is the only way a single OpenVPN server can accept connections on both IPv4 and IPv6 addresses. So the 5th choice here...
-
@bob-dig said in reaching firewall itself via ipv6:
Is that really the case? Do you have IPv6 working on LAN and don't have an address on WAN? Show it please, you have been wrong before.
Yes, Verizon does not provide a global IPv6 address to the WAN interface. On their own routers, they use the "ff" prefix ID and assign a global address from that prefix to the WAN interface (usually ::1).
It had been thought that they might be using RFC 6603 (prefix exclude) for this, but a user in another forum with an OpenWRT router (which supports that RFC) said this doesn't appear to be the case, so we're not sure how they're picking that prefix for the purpose (might just be hard-coded in their routers).
I've basically done the same thing by putting a VIP on my WAN interface. It works, but if my prefix ever changes, I'll need to manually update the VIP with the new prefix.
-
@bob-dig said in reaching firewall itself via ipv6:
@ddbnj said in reaching firewall itself via ipv6:
Since my ISP does not provide my WAN an IPv6 address,
Is that really the case? Do you have IPv6 working on LAN and don't have an address on WAN? Show it please, you have been wrong before.
Thanks,
I didn't want to be wrong again.
Devan
-
@mikev7896 said in reaching firewall itself via ipv6:
On their own routers, they use the "ff" prefix ID and assign a global address from that prefix to the WAN interface (usually ::1).
ff00/8 is a multicast address and certainly not global, which starts with 2 or 3. Perhaps you meant fc or fd, which are unique local addresses and entirely suitable for network management.
-
@ddbnj said in reaching firewall itself via ipv6:
I didn't want to be wrong again.
I thought I was wrong once, but I was mistaken.

-
@jknott said in reaching firewall itself via ipv6:
@mikev7896 said in reaching firewall itself via ipv6:
On their own routers, they use the "ff" prefix ID and assign a global address from that prefix to the WAN interface (usually ::1).
ff00/8 is a multicast address and certainly not global, which starts with 2 or 3. Perhaps you meant fc or fd, which are unique local addresses and entirely suitable for network management.
I mean that they use prefix ID "ff" out of the /56 that was delegated... that would be xxxx:xxxx:xxxx:xxFF::
-
@ddbnj I'm on FIOS too (NYC) and spent just about the entire week messing around with and learning the ins and outs of Verizon's implementation. There are definitely some sharp edges but I'm pretty happy now with the way things are working.
You might want to check out my helper script to assign a routable IP (GUA) to your WAN from one of the delegated prefix subnets. Link below