Weird situation about accessing LAN to DMZ
-
@vincentemmanuel said in Weird situation about accessing LAN to DMZ:
Sniff on lan proofs that pfsense did deliver the icmp to dmz but it kinda lost somewhere between pfsense and dmz
What about a pcap on DMZ? Does that show the ping leaving the DMZ interface toward the servers but no reply?
Do you see the servers ARPing for the LAN clients maybe?
What subnets are in use here exactly?
LAN is 192.168.9.0/24?
DMZ is 192.168.3.0/24?
What is the VPN subnet?You could workaround this with an outbound NAT rule on DMZ but you absolutely shouldn't have to do that.
Steve
-
@stephenw10 said in Weird situation about accessing LAN to DMZ:
What about a pcap on DMZ?
That is where I told him to sniff from the get go, that is where he took the sniff I would of thought, taking it on lan is sure a valid check that pfsense is even seeing the ask for ping to dmz device. But the whole point was to validate pfsense is sending on the traffic.
Sniff on lan proofs that pfsense did deliver the icmp to dmz
But I can see how this could be misleading... Where exactly was the sniff taken? But his lan rules show no policy routing so its not like pfsense sending it out some gateway if sees it on lan, unless there is a floating rule that either blocks it or policy routes the traffic.
-
Indeed, I'd be surprised if it wasn't leaving the DMZ. It's almost certainly an issue at the target server.
But it could be some NAT rule or IPSec perhaps. -
Thanks guys! Let me try my best to provide the details
LAN 10.65.1.0/24
DMZ 172.16.65.0/24
VPN 10.5.5.0/24I have an IOT network at 10.65.2.0/24
I have 5 servers in the DMZ with IP ending 11 20 25 30.
NAT 1:1
Not multihomed.Things I have done.
Turning off DNS resolver so that LAN access server via public IP (failed)
Capture Packet from LAN interface (ICMP sent successfully from pfsense)
Capture Packet from DMZ interface (No ICMP traffic from my LAN host)Yesterday I did a test, I swop LAN with IOT and now everything works.
I am not sure what is the root problem but I can conclude it is not the end devices and probably the "LAN" on pfsense has some special thing going on.
-
@vincentemmanuel do you have some rules you didn't show us on the lan? Above that any rule? Do you have rules in floating.
Like maybe block rfc or bogon ;) Have seen that countless times.. That is why it is always best to show full rule sets, not just some specific rule. From the posting you have on your lan above - that would allow all traffic and not send it out some gateway.
But for all we know you have block rfc or some other rule policy routing traffic? Also do you have any rules in floating tab?
-
@johnpoz Well I didnt show the entire LAN ruleset because during troubleshooting I moved the any any rules to the top so the rest didn't really matters since everything passed thru that.
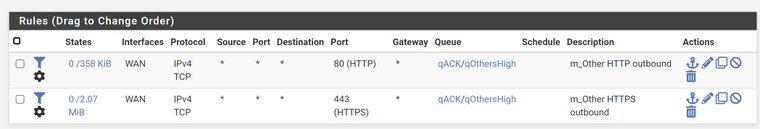
As for the floating rules, here it is
-
@vincentemmanuel well floating wouldn't have any issues. What other rules did you have on lan that you moved. If you had created a state, that say for example sent it out a vpn interface or something, that could cause the issue.
Here is the thing, if your rules allowed access on lan, and you were not forcing it out a gateway, there would be nothing stopping the traffic from going out the interface the destination IP was meant for. Basic routing, pfsense has routes for all the networks its directly attached to.
The only other thing that would stop it from sending on the traffic would be if it didn't know the mac address of the IP your trying to send to. Since its directly attached to that network.
-
@vincentemmanuel said in Weird situation about accessing LAN to DMZ:
Yesterday I did a test, I swop LAN with IOT and now everything works.
What exactly did you swap? The NIC assignment?
When traffic seems to disappear like that my prime suspect is always IPSec. Do you have any IPSec tunnels configured?
Steve
-
@stephenw10 yes. I swopped the nic assignment. I do have ipsec tunnel configured but how would that affect the lan traffic to Dmz?
-
If an IPSec P2 config is over-matching it will grab that traffic and send it across the tunnel so it never reaches the DMZ.
That affect it whatever the NIC assignment though. It only applies to subnets.Steve